Introduction
In an era marked by a significant increase in cyber threats, manufacturing leaders face an urgent need for robust IT security services. This article explores ten essential cybersecurity services that enable production companies to protect their digital assets and uphold operational integrity. As the landscape of cyber risks evolves rapidly, organizations must ensure they are not only compliant but also resilient against increasingly sophisticated attacks.
Defenderit Consulting: Comprehensive Cybersecurity Solutions
Defenderit Consulting specializes in providing tailored cybersecurity solutions designed to protect production companies from emerging cyber threats. Their extensive range of services encompasses:
- Vulnerability assessments
- [[Penetration testing](https://defenderit.consulting/10-essential-external-penetration-testing-services-for-manufacturers/)](https://defenderit.consulting/10-essential-external-penetration-testing-services-for-manufacturers/)
- Threat intelligence
- Incident response
- Compliance consulting
By utilizing advanced technologies and methodologies, Defenderit empowers industry leaders to secure their digital assets and uphold operational integrity within a highly regulated landscape.
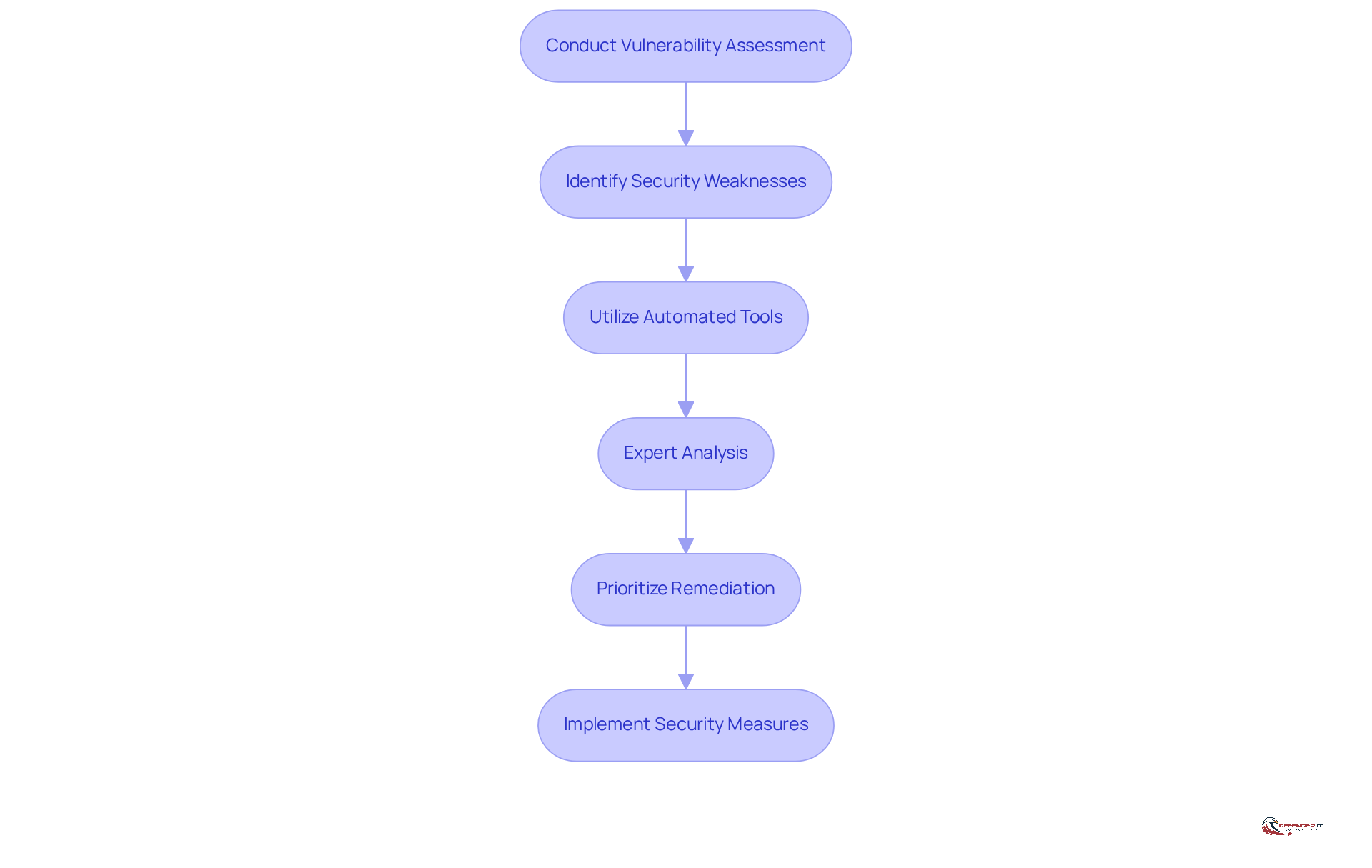
Vulnerability Assessments: Identifying Security Weaknesses
Vulnerability assessments serve as systematic evaluations of an organization’s IT infrastructure, aimed at identifying potential security weaknesses. For production leaders, these evaluations are essential in uncovering vulnerabilities in systems, applications, and networks before they can be exploited by cybercriminals. As the production sector faces a significant increase in cyber threats in 2026, regular evaluations become crucial for prioritizing remediation efforts and ensuring that critical vulnerabilities are addressed promptly.
The effectiveness of these assessments is enhanced through automated tools and expert analysis, enabling organizations to concentrate on the most pressing risks. Notably, the production sector has witnessed a 70% increase in successful ransomware attacks compared to other industries, highlighting the urgent need for robust security measures. By implementing comprehensive vulnerability assessments, manufacturers can markedly improve their cybersecurity posture, diminish the likelihood of breaches, and protect their operations against evolving threats.
[Defenderit Consulting](https://defenderit.consulting) specializes in delivering tailored vulnerability assessments that cater to the unique needs of the manufacturing sector. These evaluations not only aid in identifying weaknesses but also foster compliance with regulatory requirements, ensuring that organizations remain resilient in the face of escalating digital threats.
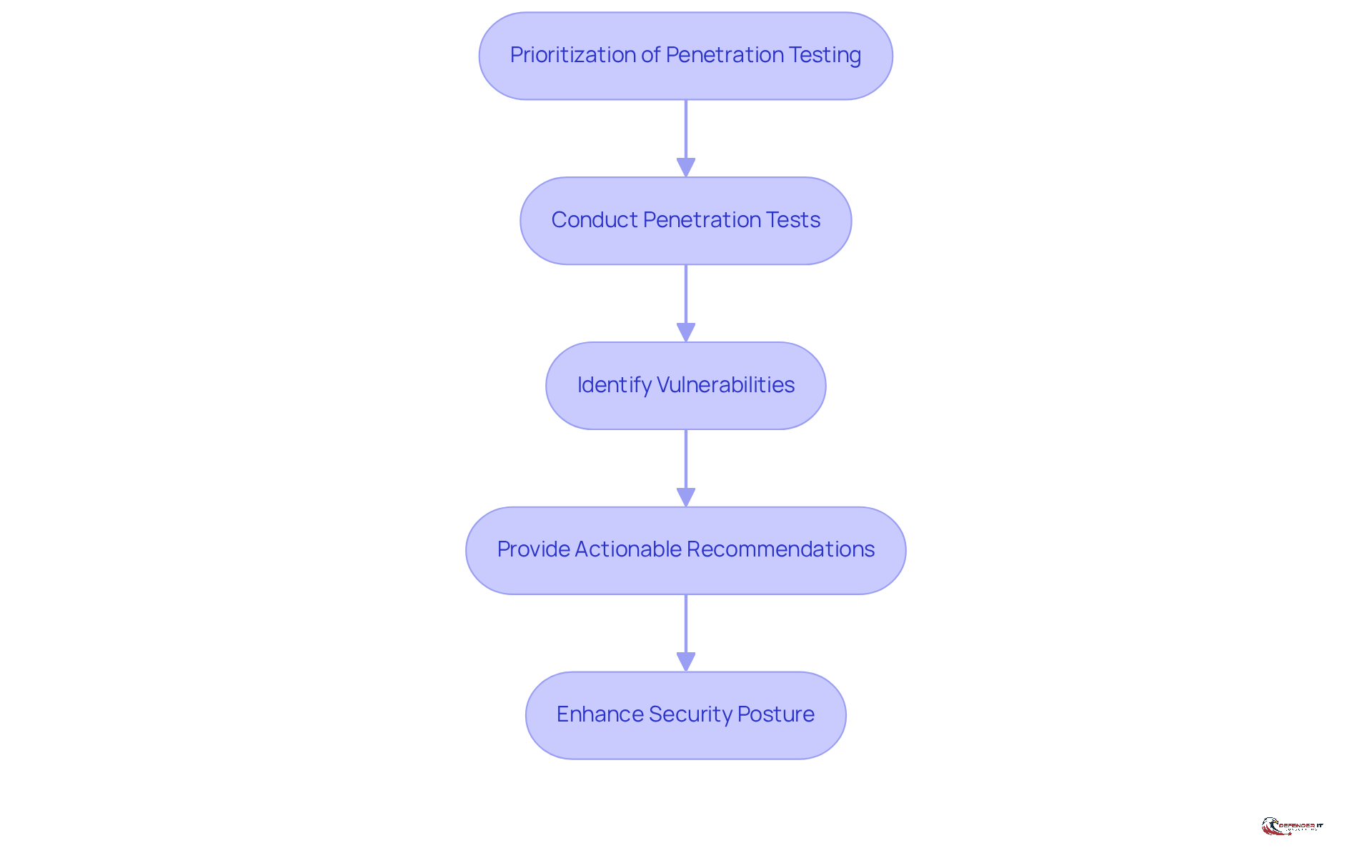
Penetration Testing: Simulating Cyber Attacks
Penetration testing, commonly referred to as ‘pen testing,’ is a critical practice that simulates cyber attacks on a company’s systems to uncover exploitable vulnerabilities. For leaders in manufacturing, this proactive approach is vital for assessing the robustness of their defenses against real-world threats. A recent study by Synack and Omdia indicates that by 2026, 95% of companies will prioritize penetration testing as a key security measure; however, only 32% of attack surfaces are actually tested, highlighting a significant gap in security practices.
Defenderit Consulting employs ethical hackers to perform thorough penetration tests, providing detailed reports that not only identify vulnerabilities but also offer actionable recommendations for remediation. This approach has proven effective; organizations that engage in regular penetration testing significantly enhance their security posture and reduce the risk of breaches. For example, the “Prioritization of Penetration Testing” case study illustrates that despite high prioritization, only a small fraction of attack surfaces are tested, underscoring a critical area for improvement.
Moreover, penetration testing replicates real-world digital assaults, allowing companies to understand how their systems would respond under genuine threat scenarios. This not only strengthens defenses but also builds trust among stakeholders regarding the organization’s ability to withstand potential digital risks. As the manufacturing sector faces increasing digital threats, integrating penetration testing into the cybersecurity strategy is essential for maintaining operational integrity and protecting sensitive information.
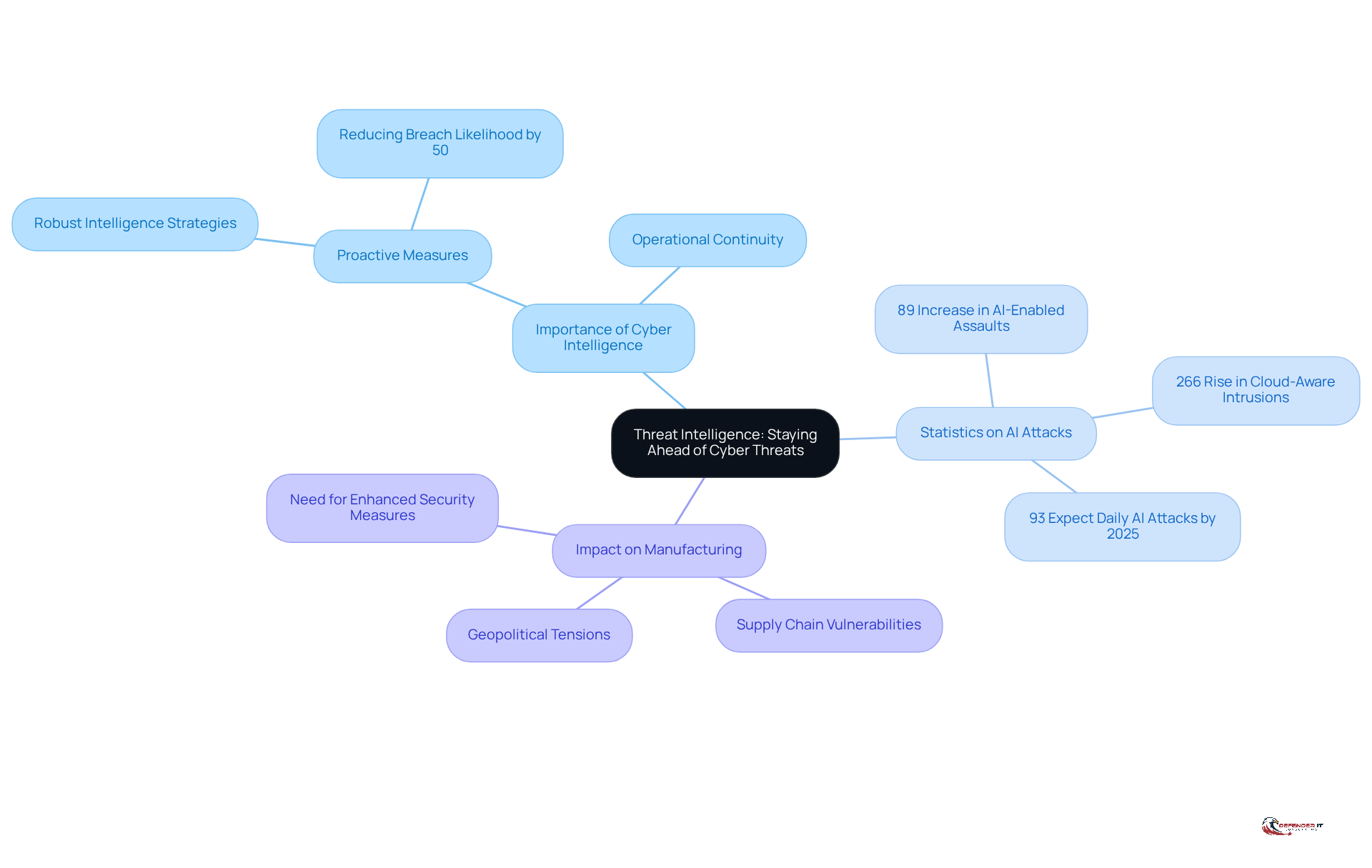
Threat Intelligence: Staying Ahead of Cyber Threats
Cyber intelligence plays a crucial role in the systematic collection and analysis of data related to potential cyber risks, enabling organizations to anticipate and effectively mitigate challenges. For manufacturing leaders, leveraging intelligence on risks is essential to understanding the evolving tactics, techniques, and procedures employed by cybercriminals. In 2026, the landscape of [[risk intelligence](https://defenderit.consulting/10-essential-mssp-cyber-security-services-for-manufacturing-leaders/)](https://defenderit.consulting/10-essential-mssp-cyber-security-services-for-manufacturing-leaders/) is marked by a notable increase in AI-enabled attacks, with adversaries integrating artificial intelligence into their operations. This has led to a staggering 266% rise in cloud-aware intrusions by state-linked malicious actors, as highlighted in CrowdStrike’s Virtual Risk Briefing. Additionally, the CrowdStrike 2026 Global Risk Report indicates an 89% increase in assaults by AI-enabled adversaries, underscoring the urgent need for manufacturers to adopt robust intelligence strategies. Furthermore, 93% of security leaders anticipate facing daily AI attacks by 2025, emphasizing the critical necessity for proactive measures.
[[Defenderit Consulting](https://defenderit.consulting)](https://defenderit.consulting) offers practical risk intelligence that empowers organizations to remain proactive against emerging threats. By incorporating this intelligence into their cybersecurity strategies, manufacturing firms can bolster their resilience against cyber attacks. Research shows that organizations effectively utilizing risk intelligence have experienced a significant improvement in their ability to prevent incidents, with studies indicating that proactive measures can reduce the likelihood of successful breaches by as much as 50%.
As manufacturers confront increasing threats from supply chain vulnerabilities and geopolitical tensions, the importance of risk intelligence becomes even more pronounced. By anticipating potential threats and comprehending the motivations behind cybercriminal activities, industry leaders can implement robust security measures that not only safeguard their digital assets but also ensure operational continuity in an increasingly complex threat landscape.
Incident Response: Managing Cyber Attack Consequences
Incident response is a structured approach that organizations implement to manage the aftermath of a [[cyber attack](https://defenderit.consulting/5-best-practices-for-mssp-security-in-regulated-industries/)](https://defenderit.consulting/5-best-practices-for-mssp-security-in-regulated-industries/). For production leaders, having a robust incident response plan is essential to minimize damage and ensure business continuity.
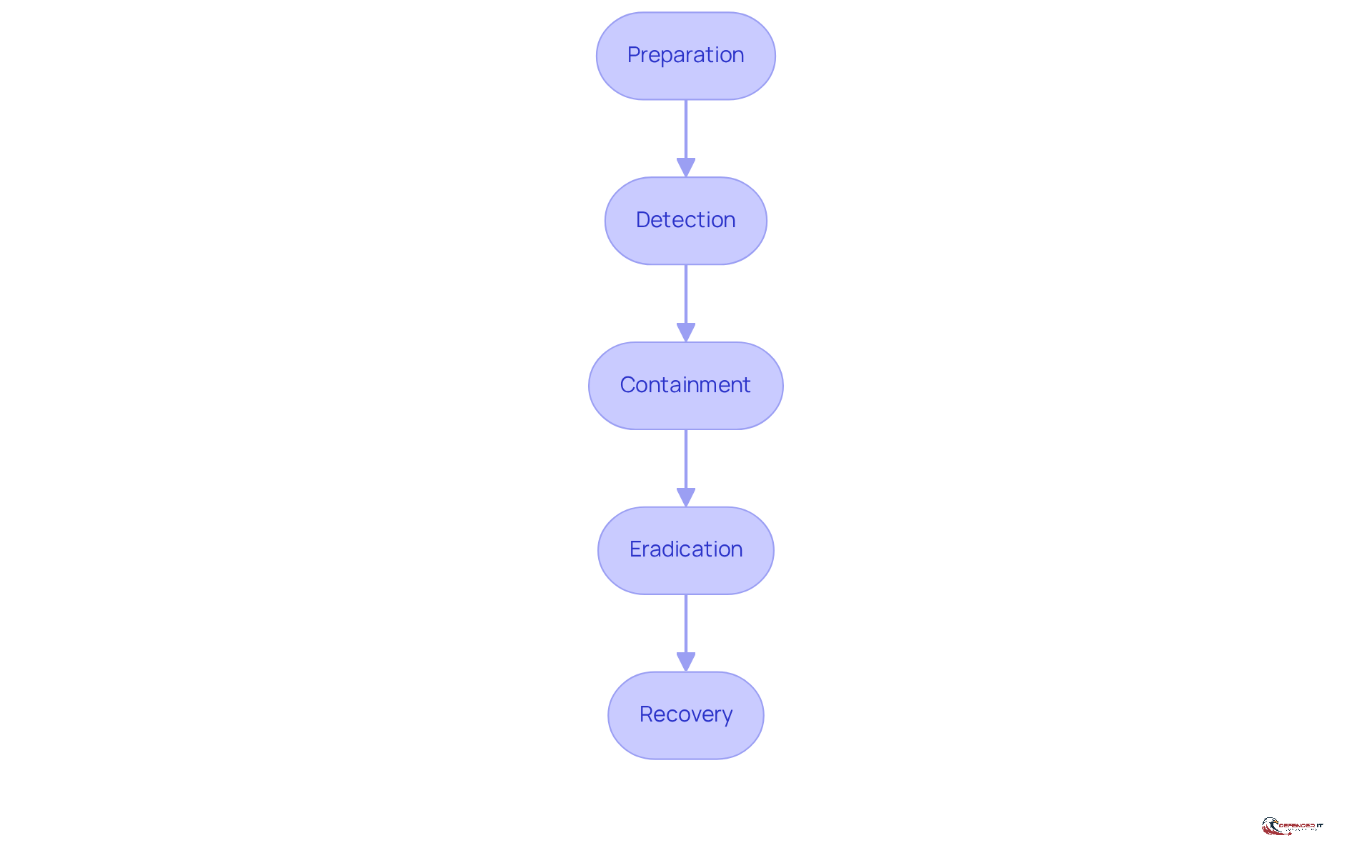
Defenderit Consulting assists organizations in developing and executing effective incident response strategies. These strategies encompass five critical phases:
- Preparation
- Detection
- Containment
- Eradication
- Recovery
By training teams and conducting simulations, companies can significantly enhance their readiness to respond to cyber incidents swiftly and effectively. This proactive approach not only mitigates potential losses but also reinforces the organization’s resilience against future threats.
Compliance Consulting: Navigating Regulatory Requirements
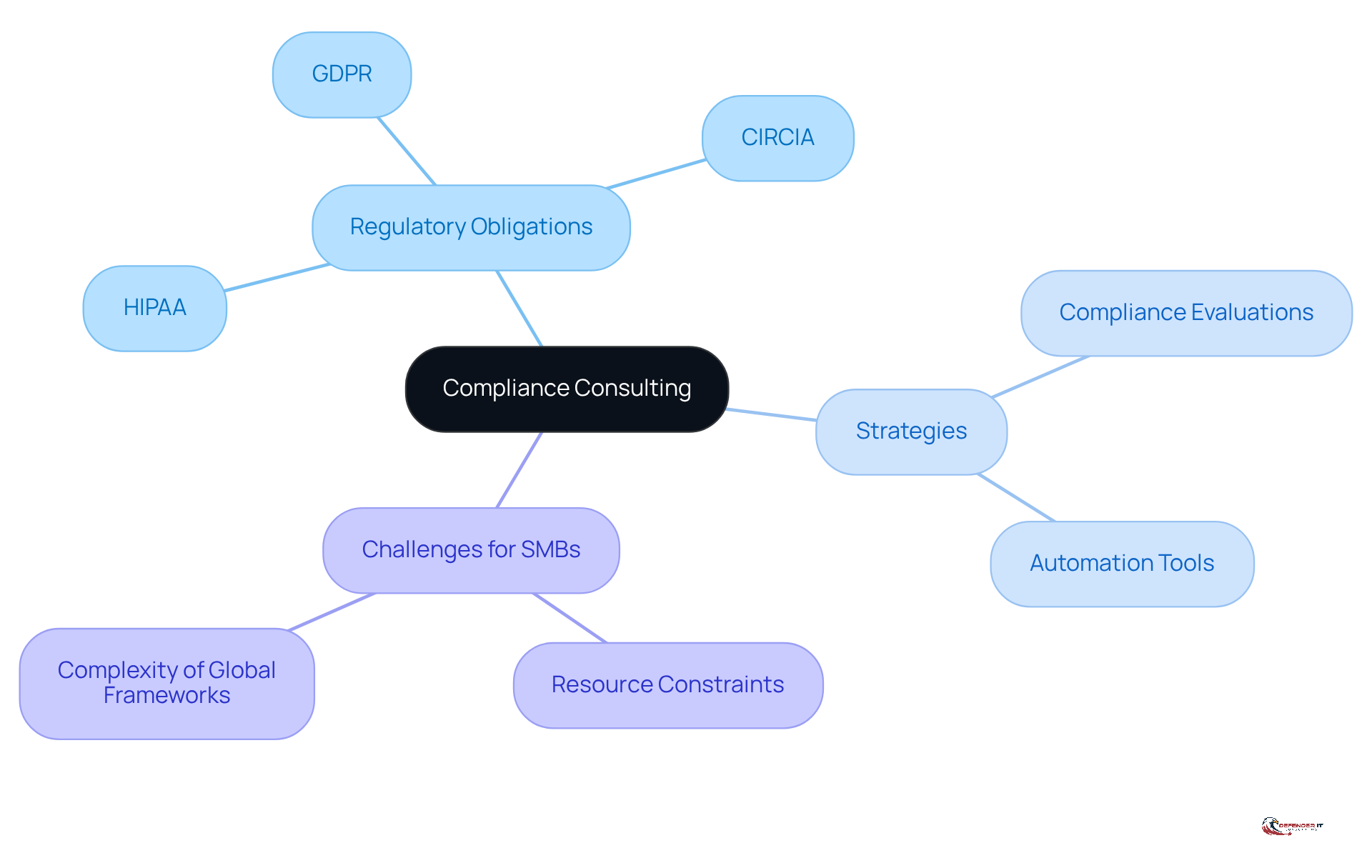
Compliance consulting is essential for production companies facing a multitude of regulatory obligations, such as GDPR, HIPAA, and industry-specific standards. Defenderit Consulting offers expert guidance to help these organizations navigate the intricate landscape of cybersecurity regulations. By performing comprehensive compliance evaluations and crafting tailored strategies, industry leaders can ensure they meet legal requirements while simultaneously bolstering their overall security posture. This proactive strategy not only reduces risks but also fosters trust among customers and stakeholders.
As of 2026, manufacturers will be subject to stringent regulations, with non-compliance potentially resulting in substantial fines-estimates indicate that penalties could amount to millions of dollars for serious infractions. For example, organizations that do not comply with the Cyber Incident Reporting for Critical Infrastructure Act (CIRCIA) face penalties and may lose eligibility for future contracts. Effective compliance strategies in regulated production sectors often involve continuous monitoring and adaptation to new regulations, ensuring that companies remain resilient against evolving digital threats.
Moreover, small and mid-sized businesses (SMBs) encounter distinct challenges in compliance management due to limited resources. Therefore, it is vital for them to implement compliance automation tools that streamline processes and enhance their capacity to meet regulatory demands.
Ongoing Support and Training: Sustaining Cybersecurity Efforts
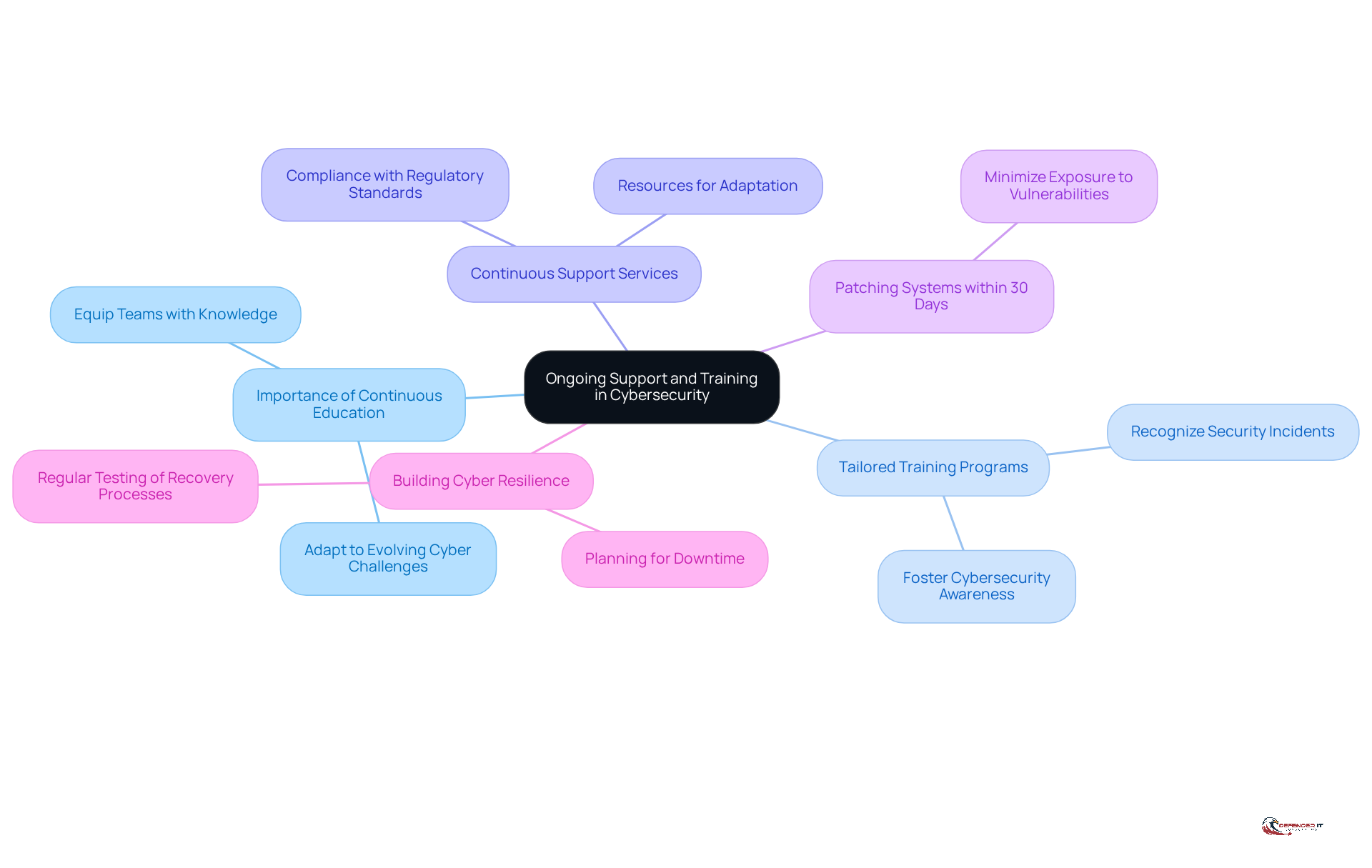
Continuous assistance and education are critical components of a comprehensive cybersecurity strategy, particularly for manufacturing leaders navigating an increasingly complex risk landscape. Ongoing education equips teams with the knowledge and skills necessary to identify and effectively address evolving cyber challenges. Tailored training programs from [[[Defenderit Consulting](https://defenderit.consulting)](https://defenderit.consulting)](https://defenderit.consulting) empower employees to recognize potential security incidents, thereby significantly reducing the likelihood of breaches.
Moreover, continuous support services ensure that organizations have the resources required to adapt to new challenges and comply with regulatory standards. Given that the manufacturing sector was the most targeted by hackers in 2025, the urgency of investing in cybersecurity training cannot be overstated. Additionally, manufacturers should prioritize:
- Patching systems with high or critical vulnerabilities within 30 days of updates becoming available to minimize exposure.
By fostering a culture of cybersecurity awareness and adapting training programs to address emerging threats, companies can substantially enhance their resilience and safeguard their digital assets against potential attacks.
Tailored Solutions: Customizing Cybersecurity for Your Business
Customized cybersecurity solutions are essential for addressing the unique challenges faced by production entities.
Defenderit Consulting collaborates closely with clients to formulate tailored strategies that align with their specific risk profiles and operational requirements.
Through comprehensive assessments and a deep understanding of each enterprise’s intricacies, Defenderit guarantees that organizations receive the most effective security measures.
This tailored approach not only enhances security but also optimizes resource allocation, allowing industry leaders to focus on their core operations while maintaining robust defenses.
Advanced Technologies: Enhancing Cybersecurity Measures
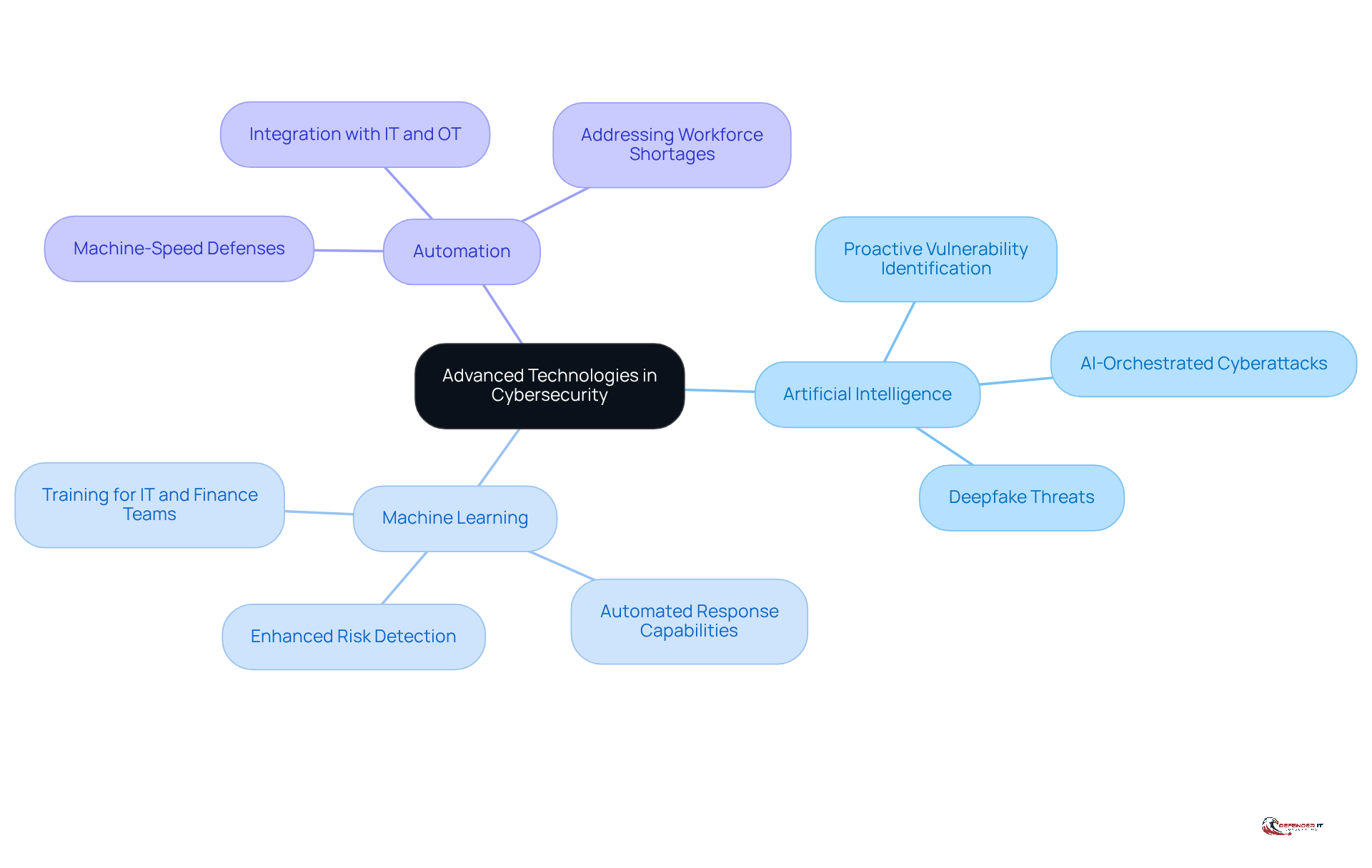
Advanced technologies are transforming the cybersecurity landscape, providing organizations with innovative tools to strengthen their defenses. For manufacturing leaders, integrating artificial intelligence (AI), machine learning, and automation is crucial for enhancing risk detection and response capabilities. By 2026, manufacturers will face increasingly sophisticated cyber challenges, including the emergence of fully AI-orchestrated cyberattacks. Leveraging AI-driven solutions will enable organizations to proactively identify vulnerabilities and respond to incidents with unmatched speed and accuracy, necessitating machine-speed defenses against these rapid threats.
[[Defenderit Consulting](https://defenderit.consulting)](https://defenderit.consulting) incorporates these advanced technologies into its IT security services, empowering production companies to bolster their security protocols and safeguard their digital assets from emerging risks. Furthermore, ongoing security awareness training for both IT and finance teams will be vital to maintaining resilience and compliance in a swiftly evolving environment.
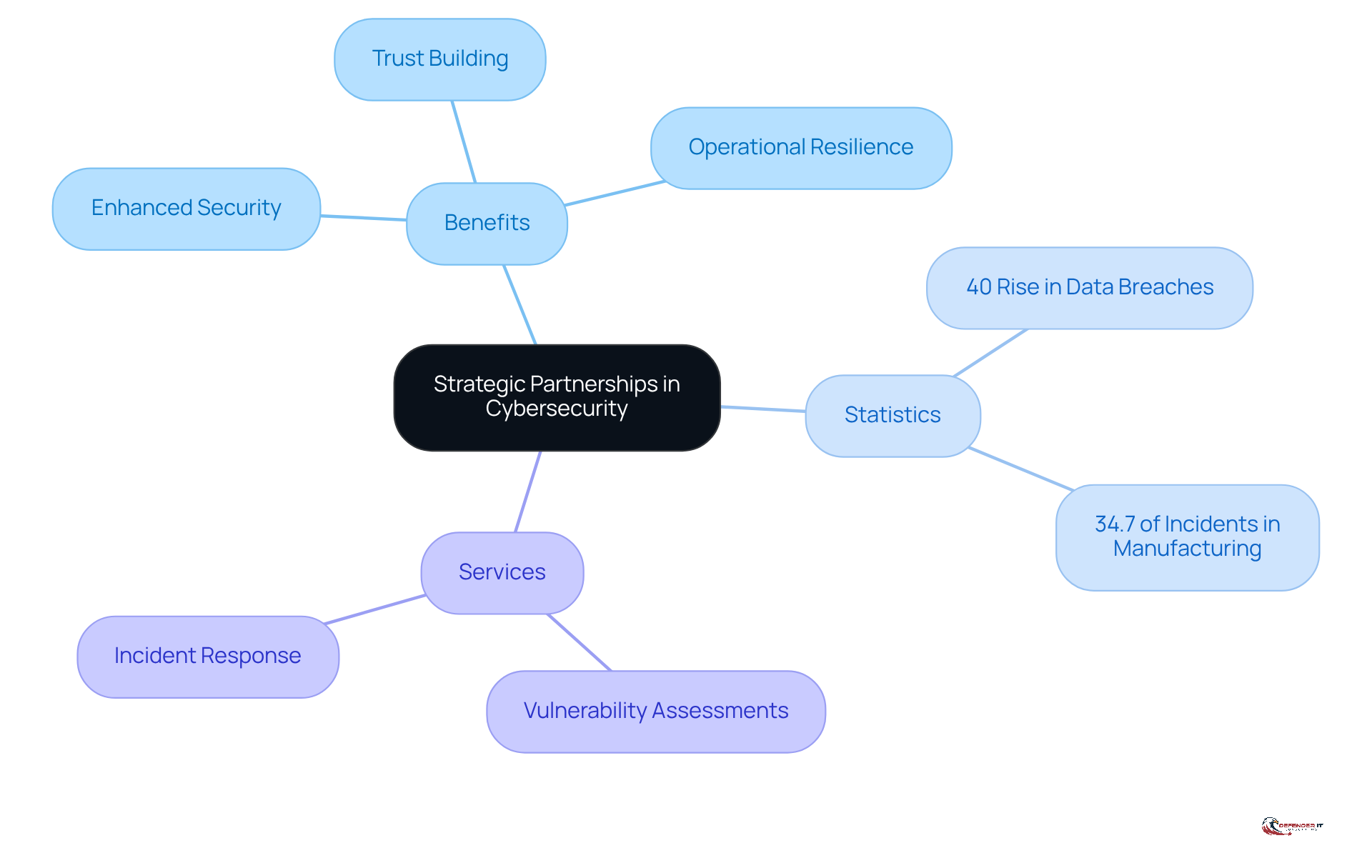
Strategic Partnerships: Building Trust in Cybersecurity
Strategic alliances play a vital role in enhancing cybersecurity initiatives within production companies. By partnering with reliable cybersecurity suppliers, these organizations can leverage advanced tools, risk intelligence, and expert advice tailored to their specific needs. In 2026, as digital risks continue to escalate-evidenced by a 40% rise in data breaches globally, with manufacturing accounting for 34.7% of all digital incidents–Defenderit Consulting underscores the necessity of forming robust alliances to establish a comprehensive security ecosystem.
Moreover, with cybersecurity spending projected to reach $240 billion in 2026, these collaborations not only bolster the effectiveness of cybersecurity measures but also foster trust among stakeholders. This trust enables organizations to adeptly navigate the complexities of the digital landscape. By cultivating these alliances, manufacturers can significantly enhance their resilience against cyber threats, ensuring a secure operational environment.
Additionally, services such as vulnerability assessments and incident response provided by Defenderit Consulting can be instrumental in operationalizing these partnerships.
Conclusion
In the rapidly evolving landscape of manufacturing, robust IT security services are essential. As production leaders confront increasing cyber threats, implementing comprehensive cybersecurity solutions is crucial for safeguarding operations and ensuring compliance with regulatory standards. By prioritizing tailored strategies, organizations can effectively protect their digital assets and maintain operational integrity.
This article outlines ten essential IT security services that manufacturing leaders should consider:
- Vulnerability assessments
- Penetration testing
- Threat intelligence
- Incident response
- Compliance consulting
Each service plays a critical role in identifying weaknesses, simulating potential attacks, and preparing organizations to respond effectively to incidents. Additionally, ongoing support and training, along with the integration of advanced technologies, enhance the overall cybersecurity posture of manufacturing firms, enabling them to stay ahead of emerging threats.
Ultimately, the call to action for manufacturing leaders is clear: investing in cybersecurity is not merely a protective measure but a strategic imperative. By fostering a culture of security awareness and collaborating with trusted partners like Defenderit Consulting, organizations can build resilient defenses against cyber threats, ensuring a secure and sustainable future in an increasingly digital world.
Frequently Asked Questions
What services does Defenderit Consulting provide?
Defenderit Consulting offers a range of tailored cybersecurity solutions including vulnerability assessments, penetration testing, threat intelligence, incident response, and compliance consulting to protect production companies from cyber threats.
What is the purpose of vulnerability assessments?
Vulnerability assessments systematically evaluate an organization’s IT infrastructure to identify potential security weaknesses in systems, applications, and networks, helping organizations prioritize remediation efforts and address critical vulnerabilities.
Why are vulnerability assessments particularly important for the production sector?
The production sector is facing a significant increase in cyber threats, with a 70% rise in successful ransomware attacks. Regular vulnerability assessments are crucial for improving cybersecurity posture and protecting operations against evolving threats.
How does Defenderit Consulting enhance vulnerability assessments?
Defenderit Consulting utilizes automated tools and expert analysis to enhance the effectiveness of vulnerability assessments, allowing organizations to focus on the most pressing risks while ensuring compliance with regulatory requirements.
What is penetration testing and why is it important?
Penetration testing, or ‘pen testing,’ simulates cyber attacks on a company’s systems to uncover exploitable vulnerabilities. It is important for assessing the robustness of defenses against real-world threats and is increasingly prioritized by companies as a key security measure.
What are the findings regarding penetration testing among companies?
A recent study indicated that while 95% of companies will prioritize penetration testing by 2026, only 32% of attack surfaces are actually tested, highlighting a significant gap in security practices.
How does Defenderit Consulting conduct penetration testing?
Defenderit Consulting employs ethical hackers to perform thorough penetration tests, providing detailed reports that identify vulnerabilities and offer actionable recommendations for remediation.
What are the benefits of regular penetration testing for organizations?
Regular penetration testing enhances security posture, reduces the risk of breaches, and helps organizations understand how their systems would respond to genuine threat scenarios, thereby building trust among stakeholders.
List of Sources
- Defenderit Consulting: Comprehensive Cybersecurity Solutions
- Manufacturing Cyber Attack Statistics 2026: Data-Driven Insights on Industrial Security Threats (https://totalassure.com/blog/manufacturing-cyber-attack-statistics-2026-data-driven-insights-on-industrial-security-threats)
- Why Manufacturing Is the #1 Cyberattack Target in 2026 — And What to Do About It (https://blog.cybelesoft.com/manufacturing-cybersecurity-zero-trust-2026)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- The New Rules of Manufacturing Cybersecurity: What to Know in 2026 – Decypher Technologies (https://decyphertech.com/the-new-rules-of-manufacturing-cybersecurity-what-to-know-in-2026)
- AI, Cybersecurity and Workforce Trends Shape Manufacturing in 2026 (https://ccat.us/news-insights/trends-shape-manufacturing-in-2026)
- Vulnerability Assessments: Identifying Security Weaknesses
- Cybersecurity 2026: AI, CISA, manufacturing sector all in the hot seat (https://cybersecuritydive.com/news/cyber-trends-outlook-2026/810708)
- Threat and Vulnerability Management in 2026 (https://recordedfuture.com/blog/threat-and-vulnerability-management)
- 9 Vulnerability Remediation Tools in 2026 | SentinelOne (https://sentinelone.com/cybersecurity-101/cybersecurity/vulnerability-remediation-tools)
- Ransomware Remains Top Cyber Risk for U.S. Manufacturers (https://advancedmanufacturing.org/news-desk/ransomware-remains-top-cyber-risk-for-u-s-manufacturers/article_31ebabd5-2acf-4a90-8eb4-7479fc7a94b8.html)
- Ultimate Guide to Vulnerability Assessment: What, Why & How (2026 Edition) (https://acronis.com/en/blog/posts/ultimate-guide-to-vulnerability-assessment-2026)
- Penetration Testing: Simulating Cyber Attacks
- 2026 GDPR Cybersecurity Requirements & Penetration Testing – Netragard (https://netragard.com/blog/gdpr-cybersecurity-requirements-and-penetration-testing)
- Outsourcing Penetration Testing in 2026: What Actually Works | Capture The Bug (https://capturethebug.xyz/Blogs/Why-Smart-Companies-Rethink-Outsourcing-Penetration-Testing-in-2026)
- The 2026 State of Pentesting: How Modern Teams Manage and Deliver Results (https://thehackernews.com/expert-insights/2026/01/the-2026-state-of-pentesting-how-modern.html)
- Penetration Testing Requirement: What U.S. Rules Mandate It in 2026? (https://halock.com/penetration-testing-requirement-what-u-s-rules-mandate-it-in-2026)
- 95% of Enterprises Prioritize Pentesting, Yet Only 32% of Attack Surfaces Are Tested, New Synack and Omdia Research Finds (https://prnewswire.com/news-releases/95-of-enterprises-prioritize-pentesting-yet-only-32-of-attack-surfaces-are-tested-new-synack-and-omdia-research-finds-302718985.html)
- Threat Intelligence: Staying Ahead of Cyber Threats
- U.S. Public Sector Under Siege: Threat Intelligence for Q1 2026 (https://trendmicro.com/en_us/research/26/d/us-public-sector-under-siege.html)
- 2026 Cyber Threat Trends & Outlook (https://intel471.com/resources/whitepapers/2026-cyber-threat-trends-and-outlook)
- 2026 Global Threat Report | Latest Cybersecurity Trends & Insights | CrowdStrike (https://crowdstrike.com/en-us/global-threat-report)
- 7 Key Manufacturing Cybersecurity Trends for 2026 | Huntress (https://huntress.com/blog/manufacturing-cybersecurity-trends)
- 2026 Will Be a Breakthrough Year for Cyberthreats: Four Predictions for Manufacturers (https://ien.com/redzone/blog/22958566/2026-will-be-a-breakthrough-year-for-cyberthreats-four-predictions-for-manufacturers)
- Incident Response: Managing Cyber Attack Consequences
- How to Build an Effective Cyber Incident Response Plan for 2026 (https://cm-alliance.com/cybersecurity-blog/how-to-build-an-effective-cyber-incident-response-plan)
- Manufacturing Cyber Attack Statistics 2026: Data-Driven Insights on Industrial Security Threats (https://totalassure.com/blog/manufacturing-cyber-attack-statistics-2026-data-driven-insights-on-industrial-security-threats)
- 70% of Manufacturers Experienced a Cyber Incident Last Year — Here’s Why This Is Now an Operations Issue (https://linkedin.com/pulse/70-manufacturers-experienced-cyber-incident-last-year-nook-oo97e)
- Cybersecurity 2026: AI, CISA, manufacturing sector all in the hot seat (https://cybersecuritydive.com/news/cyber-trends-outlook-2026/810708)
- 2026 Will Be a Breakthrough Year for Cyberthreats: Four Predictions for Manufacturers (https://ien.com/redzone/blog/22958566/2026-will-be-a-breakthrough-year-for-cyberthreats-four-predictions-for-manufacturers)
- Compliance Consulting: Navigating Regulatory Requirements
- Five Compliance Changes That Will Impact C&IP in 2026 | CBIZ (https://cbiz.com/insights/article/five-compliance-changes-that-will-impact-cip-in-2026)
- The New Rules of Manufacturing Cybersecurity: What to Know in 2026 – Decypher Technologies (https://decyphertech.com/the-new-rules-of-manufacturing-cybersecurity-what-to-know-in-2026)
- 2026 in manufacturing: Policy risks and opportunities | Grant Thornton (https://grantthornton.com/insights/articles/manufacturing/2026/2026-manufacturing-policy-risks-opportunities)
- Understanding IT Compliance: Key Regulations for 2026 | Prime Secured (https://primesecured.com/it-compliance-key-regulations-2026)
- New Federal Cybersecurity Reporting Rules are on Their Way: FAQs for Businesses About CIRCIA Regulations (https://fisherphillips.com/en/insights/insights/new-federal-cybersecurity-reporting-rules-are-on-their-way)
- Ongoing Support and Training: Sustaining Cybersecurity Efforts
- AI, Cybersecurity and Workforce Trends Shape Manufacturing in 2026 (https://ccat.us/news-insights/trends-shape-manufacturing-in-2026)
- 2026 Will Be a Breakthrough Year for Cyberthreats: Four Predictions for Manufacturers (https://ien.com/redzone/blog/22958566/2026-will-be-a-breakthrough-year-for-cyberthreats-four-predictions-for-manufacturers)
- Why 2026 Is the Year Cyber Training Stops Looking Like Training — Cloud Range (https://cloudrangecyber.com/news/why-2026-is-the-year-cyber-training-stops-looking-like-training)
- 5 ways to protect manufacturing from cyberattacks (https://manufacturingdive.com/news/how-to-protect-your-manufacturing-company-from-cyberattacks/814285)
- New Cybersecurity Courses for Continuous Learning (https://isc2.org/Insights/2026/04/staying-ahead-in-cybersecurity-new-courses)
- Tailored Solutions: Customizing Cybersecurity for Your Business
- 7 Key Manufacturing Cybersecurity Trends for 2026 | Huntress (https://huntress.com/blog/manufacturing-cybersecurity-trends)
- Manufacturers are making progress with AI, but barriers remain: Cisco (https://manufacturingdive.com/news/cybersecurity-top-barrier-expanding-ai-in-manufacturing-cisco/813751)
- Key Cyber Security Statistics for 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-statistics)
- Cybersecurity 2026: AI, CISA, manufacturing sector all in the hot seat (https://cybersecuritydive.com/news/cyber-trends-outlook-2026/810708)
- The New Rules of Manufacturing Cybersecurity: What to Know in 2026 – Decypher Technologies (https://decyphertech.com/the-new-rules-of-manufacturing-cybersecurity-what-to-know-in-2026)
- Advanced Technologies: Enhancing Cybersecurity Measures
- 2026 Will Be a Breakthrough Year for Cyberthreats: Four Predictions for Manufacturers (https://ien.com/redzone/blog/22958566/2026-will-be-a-breakthrough-year-for-cyberthreats-four-predictions-for-manufacturers)
- AI, Cybersecurity and Workforce Trends Shape Manufacturing in 2026 (https://ccat.us/news-insights/trends-shape-manufacturing-in-2026)
- Cybersecurity for Manufacturing in 2026 (https://linkedin.com/pulse/cybersecurity-manufacturing-2026-thriveon-l8xpc)
- Cybersecurity 2026: AI, CISA, manufacturing sector all in the hot seat (https://cybersecuritydive.com/news/cyber-trends-outlook-2026/810708)
- Top Cybersecurity Predictions For 2026 (https://forbes.com/councils/forbestechcouncil/2026/01/12/top-cybersecurity-predictions-for-2026)
- Strategic Partnerships: Building Trust in Cybersecurity
- From integration pain to partnership gain: How collaboration strengthens cybersecurity (https://cio.com/article/4111281/from-integration-pain-to-partnership-gain-how-collaboration-strengthens-cybersecurity.html)
- Strategic Priorities in the 2026 US Cyber Strategy and Cybercrime Executive Order | Weaver (https://weaver.com/resources/strategic-priorities-in-the-2026-us-cyber-strategy-and-cybercrime-executive-order)
- White House Announces The 2026 Cyber Strategy For America (https://forrester.com/blogs/white-house-announces-the-2026-cyber-strategy-for-america)
- Key Cyber Security Statistics for 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-statistics)
- US and allies collaborate on operational technology security guidance (https://cybersecuritydive.com/news/operational-technology-security-international-guidance/809851)