Introduction
In an era where cyber threats are increasingly prevalent, organizations encounter the significant challenge of establishing robust incident response capabilities. This article examines best practices that enable security leaders to effectively navigate the complexities of the incident response phase, encompassing preparation strategies and efficient recovery protocols. Notably, with nearly half of all organizations lacking a formal incident response plan, the question arises: how can they effectively mitigate risks and bolster their resilience against potential breaches? This exploration uncovers critical insights and actionable steps that can shift a reactive approach into a proactive defense strategy, ultimately safeguarding an organization’s reputation and assets.
Establish Comprehensive Preparation Strategies
To effectively prepare for potential , organizations should implement the following best practices:
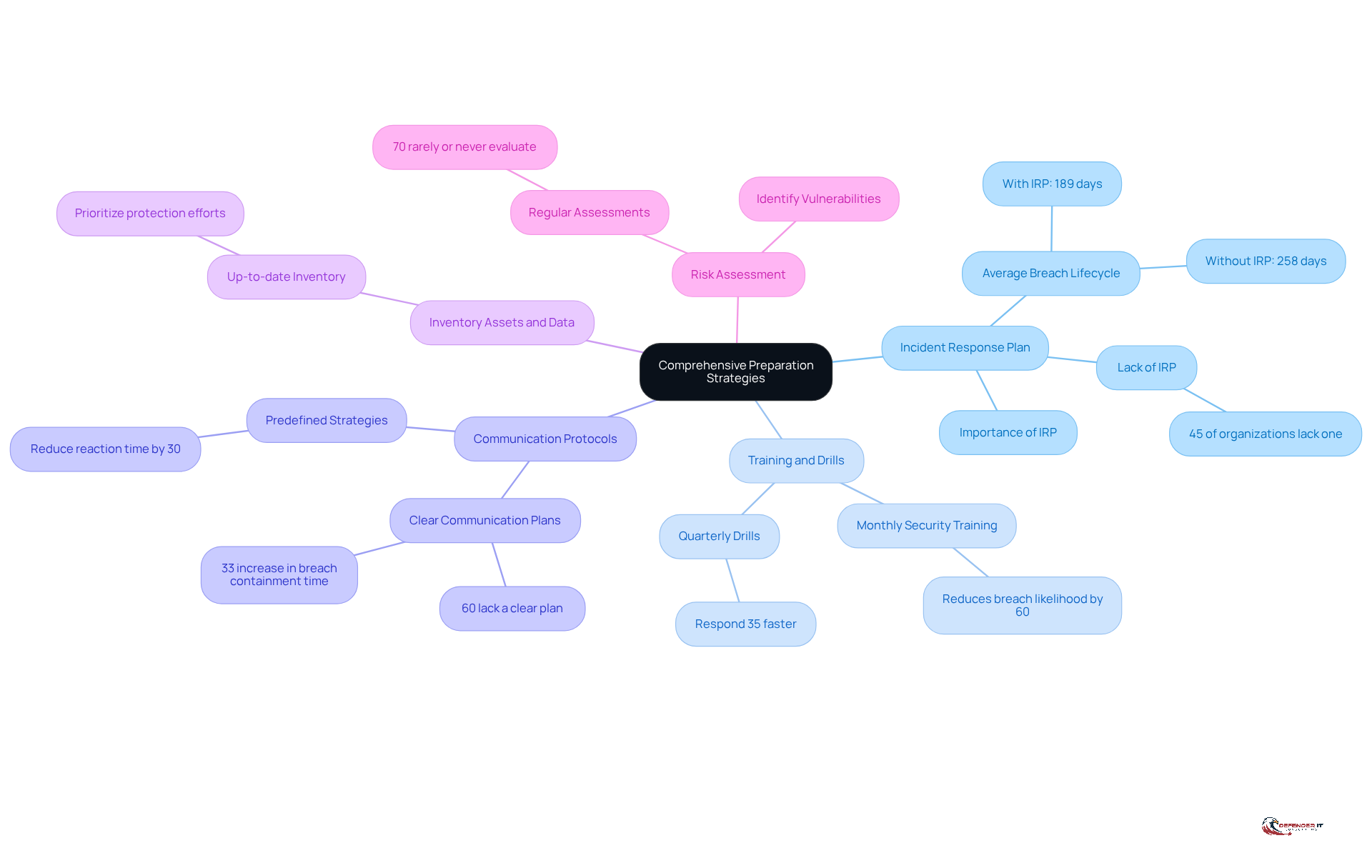
- Develop an : Establish a comprehensive IRP that clearly outlines roles, responsibilities, and procedures for responding to incidents. A documented plan is crucial, as approximately 45% of organizations lack one, leading to an average of 258 days compared to 189 days for those with a formal strategy. Regular updates and are essential to ensure its effectiveness. As noted by Unit 42, “Organizations without a formal plan face a 258-day average .”
- : Engage employees in consistent training sessions and tabletop exercises to familiarize them with the IRP. Organizations that conduct monthly security training can reduce breach likelihood by 60%. Moreover, companies conducting emergency drills at least once every three months react 35% quicker to situations. Routine exercises not only boost readiness but also clarify personal responsibilities during an event, greatly enhancing reaction times.
- Establish Communication Protocols: Define clear communication channels for both internal and external stakeholders. Effective are vital, as 60% of organizations lack a clear plan during , resulting in a 33% increase in breach containment time. Predefined can decrease reaction time by 30%.
- : Maintain an up-to-date inventory of all IT assets and sensitive data. Comprehending what requires protection is crucial for prioritizing action efforts and ensuring that critical systems are shielded from potential threats.
- : Conduct regular s to identify vulnerabilities and potential threats. This proactive method enables entities to customize their crisis management strategies to the particular threats they encounter, improving their overall security stance. Significantly, 70% of enterprises seldom or never evaluate their crisis management strategies, emphasizing a frequent mistake that companies should evade.
By implementing these strategies, entities can establish a strong foundation for their , ensuring they are well-prepared to tackle any cybersecurity challenges that may arise.
Implement Robust Detection and Analysis Mechanisms
To enhance , organizations should adopt the following practices:
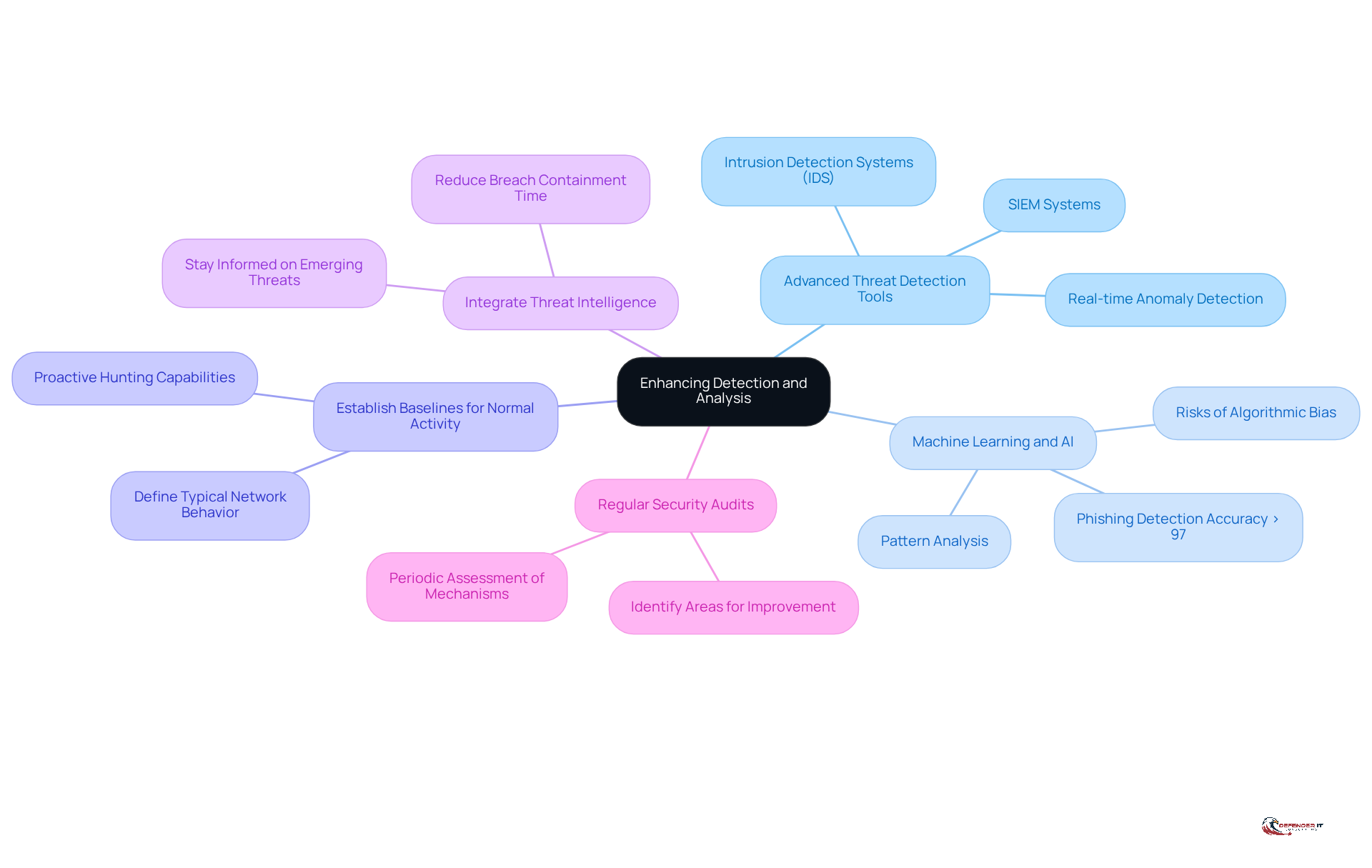
- Employ : Deploy information and event management (SIEM) systems and intrusion detection systems (IDS) to oversee network traffic and detect anomalies in real-time. These tools are evolving into decision engines, improving response times and reducing manual processes.
- Utilize : Leverage machine learning algorithms to analyze patterns and detect potential threats. These technologies significantly improve the ability to identify both known and unknown threats, with models achieving over 97% accuracy in detecting phishing attempts. As AI becomes integrated into protection tools, it accelerates detection and response capabilities, enhancing organizations’ resilience against evolving threats. However, organizations must also be aware of the potential risks associated with AI, such as algorithmic bias and overreliance on automation.
- : Define what constitutes typical network behavior to facilitate the identification of deviations that may suggest a breach. Organizations that establish behavioral baselines early will develop more mature proactive hunting capabilities, allowing for quicker anomaly detection.
- : Utilize threat intelligence feeds to stay informed about emerging threats and vulnerabilities. This proactive approach enhances the organization’s capacity to identify and respond to events, as timely information can significantly reduce the average duration to contain a breach, which currently stands at approximately 280 days.
- : Perform periodic audits of detection mechanisms to ensure they are functioning correctly and to identify areas for improvement. Ongoing assessment of protective measures is crucial, particularly as the digital environment becomes increasingly complex and fluid.
By implementing these detection and analysis methods, organizations can significantly enhance their ability to recognize events and respond to them swiftly during the incident response phase, thereby improving their overall security posture.
Develop Clear Containment and Recovery Protocols
To ensure effective containment and recovery during a , organizations should adopt several best practices:
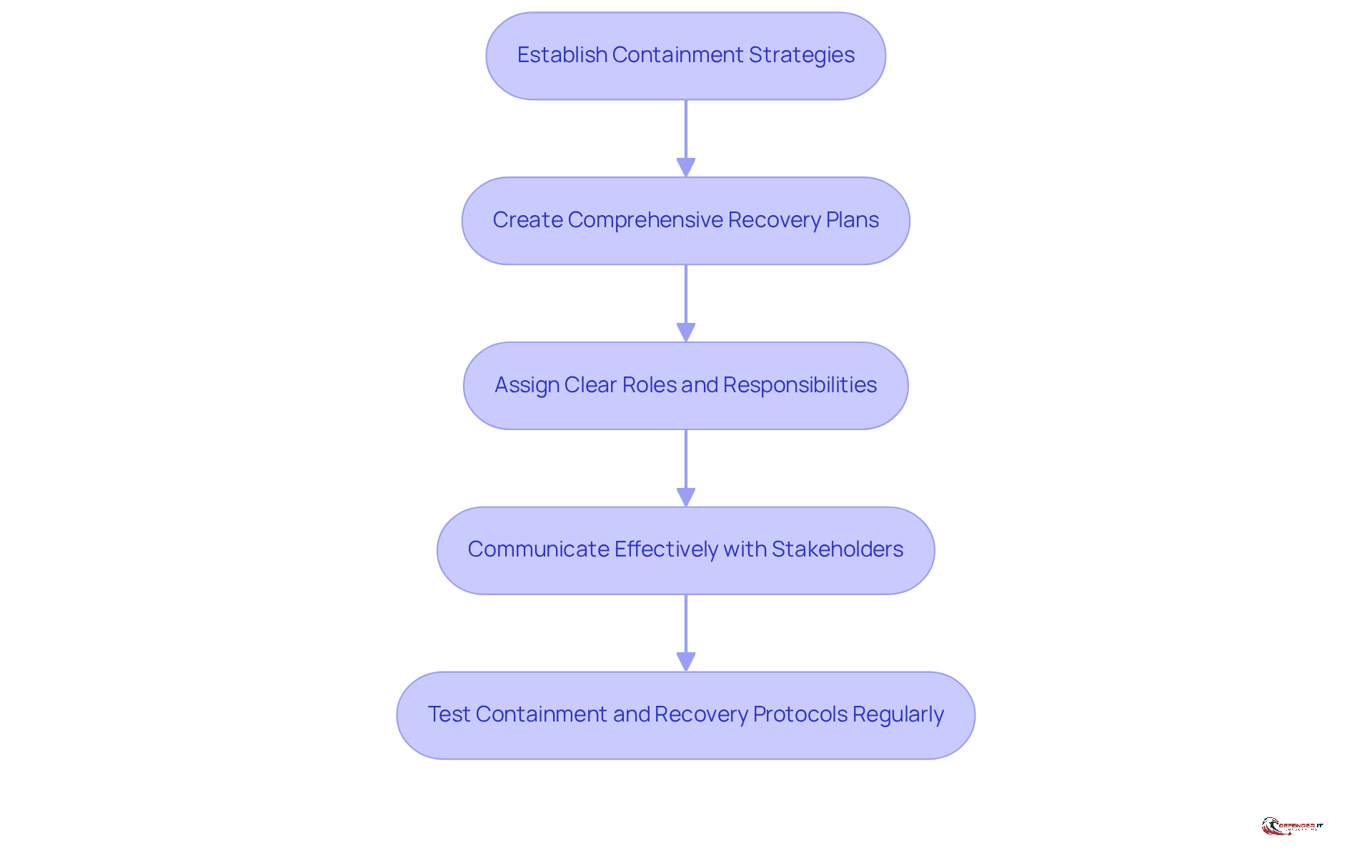
- Establish : Organizations must define specific tailored to various types of events. This may involve isolating affected systems, blocking malicious traffic, or disabling compromised accounts to prevent further damage.
- Create Comprehensive : It is essential to develop detailed that outline the necessary steps to restore systems and data post-incident. This should include data backups, system recovery procedures, and clear timelines for restoration, facilitating an organized approach.
- Assign : Clearly delineating roles and responsibilities for the response team during containment and is crucial. This clarity ensures that all team members understand their tasks, enabling swift and coordinated action.
- : Maintaining open lines of communication with stakeholders throughout the is vital. Frequent updates on the status of the situation and are essential for transparency and trust.
- : Conducting regular simulations to test containment and recovery protocols is necessary to ensure their effectiveness and that team members are well-acquainted with their roles. This proactive approach helps identify gaps and enhances overall preparedness.
By creating and executing these protocols in the , companies can significantly reduce the impact of incidents and ensure a swift recovery, thereby protecting their operations and reputation.
Conduct Post-Incident Reviews for Continuous Improvement
To drive continuous improvement in , organizations should adopt the following for post-incident reviews:
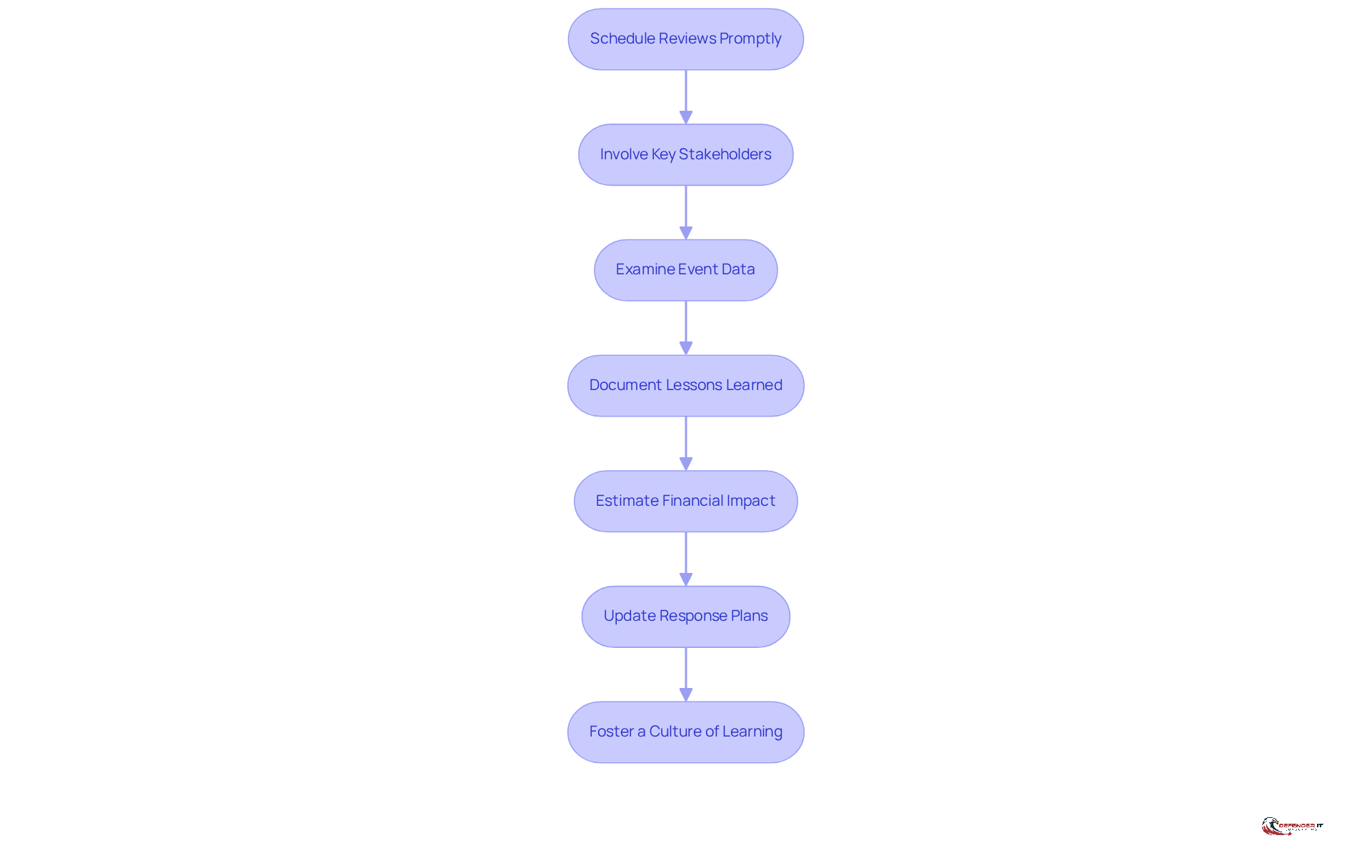
- : Conduct within 24 to 72 hours after an occurrence to ensure that details are fresh and accurately captured. Prompt evaluations assist in preserving a sense of urgency and clarity concerning the event timeline.
- Involve Key Stakeholders: Engage a diverse group of stakeholders in the review process, including IT staff, management, and external partners. This inclusive method promotes a thorough understanding of the event and links technical findings to wider organizational policies.
- Examine Event Data: Carefully assess all information associated with the event, such as detection logs and actions taken. This analysis should emphasize both strengths and weaknesses in the response, allowing organizations to identify previously unseen risks and areas for enhancement.
- : that records the findings from the review, including actionable lessons learned and suggestions for improving future event management efforts. This documentation serves as a valuable resource for enhancing response strategies.
- Estimate Financial Impact: Assess the overall , including direct losses and reputational damage. Understanding these costs is crucial for reporting to executive management and for .
- Update Response Plans: Utilize insights gained from the review to modify response plans and protocols. This ensures that the organization is better prepared to manage future situations, ultimately enhancing its .
- : Encourage a non-blame environment where team members can openly discuss what went well and what could be improved. This culture of learning enhances vigilance and strengthens the overall security program.
By implementing these , organizations can enhance their phase capabilities, turning past incidents into opportunities for resilience and improvement.
Conclusion
Establishing a robust incident response strategy is essential for organizations seeking to protect their digital assets from the constantly evolving landscape of cybersecurity threats. By implementing comprehensive preparation strategies, organizations can significantly enhance their readiness to respond effectively to incidents, thereby minimizing the impact on operations and reputation.
Key practices such as:
- Developing a detailed Incident Response Plan
- Conducting regular training and drills
- Establishing clear communication protocols
are vital components that contribute to a successful incident response phase. Furthermore, employing advanced detection mechanisms and creating effective containment and recovery protocols are crucial for swift action during a cybersecurity event. Regular post-incident reviews ensure that organizations learn from past experiences, fostering a culture of continuous improvement that strengthens their overall security posture.
In an environment where cyber threats are increasingly sophisticated, it is imperative for organizations to prioritize incident response preparation. By embracing these best practices, they can not only protect their assets but also build resilience against future incidents. Taking proactive steps today will lead to a more secure tomorrow, empowering organizations to navigate the complexities of cybersecurity with confidence and agility.
Frequently Asked Questions
What is an Incident Response Plan (IRP) and why is it important?
An Incident Response Plan (IRP) is a comprehensive document that outlines roles, responsibilities, and procedures for responding to cybersecurity incidents. It is crucial because organizations without a formal IRP experience an average breach lifecycle of 258 days, compared to 189 days for those with a plan.
How often should organizations conduct training and drills related to cybersecurity?
Organizations should engage employees in consistent training sessions and tabletop exercises. Conducting monthly security training can reduce the likelihood of breaches by 60%, while emergency drills at least once every three months can improve reaction times by 35%.
Why are communication protocols important during cyber incidents?
Clear communication protocols are vital as 60% of organizations lack a clear plan during cyber incidents, which can increase breach containment time by 33%. Predefined communication strategies can decrease reaction time by 30%.
What should organizations do to maintain an inventory of assets and data?
Organizations should keep an up-to-date inventory of all IT assets and sensitive data to prioritize protection efforts and ensure critical systems are shielded from potential threats.
How can regular risk assessments benefit an organization?
Regular risk assessments help identify vulnerabilities and potential threats, allowing organizations to customize their crisis management strategies. However, 70% of enterprises seldom or never evaluate their crisis management strategies, which is a common mistake.
What are the overall benefits of implementing comprehensive preparation strategies for cybersecurity?
Implementing comprehensive preparation strategies establishes a strong foundation for the incident response phase, ensuring organizations are well-prepared to tackle any cybersecurity challenges that may arise.