Introduction
Manufacturers today face a complex landscape where the protection of Controlled Unclassified Information (CUI) is of utmost importance. As organizations increasingly depend on sensitive data to sustain competitive advantages, grasping the intricacies of CUI protection is essential for compliance and operational integrity. To effectively shield this critical information from cyber threats while ensuring compliance with evolving regulations, various strategies can be employed.
Define Controlled Unclassified Information (CUI) and Its Importance
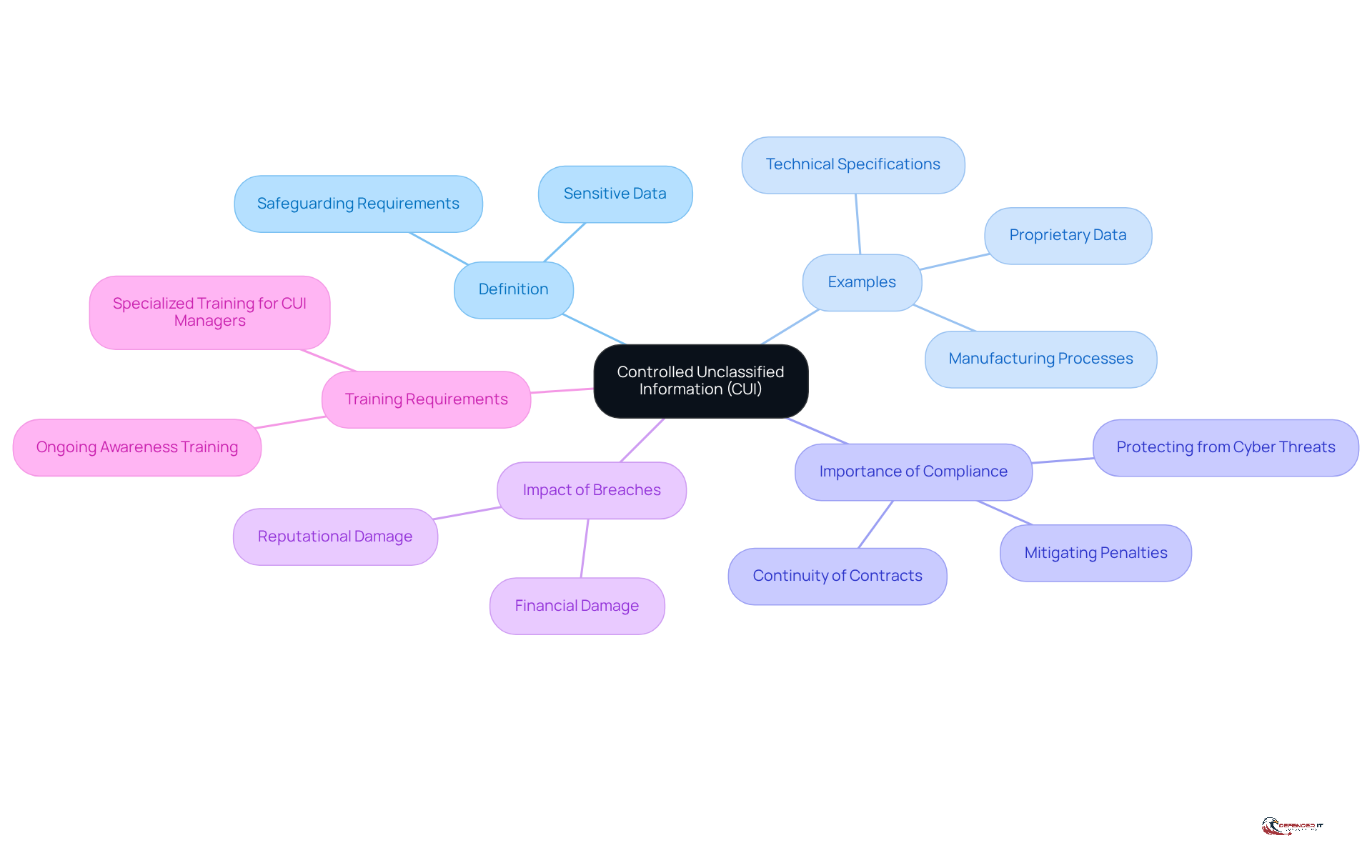
Controlled Unclassified Information (CUI) is sensitive data that, while not classified, requires specific safeguarding and dissemination controls as mandated by law, regulation, or government-wide policy. This category includes critical information such as:
- Technical specifications
- Manufacturing processes
- Proprietary data
If disclosed, this information could adversely affect national safety. For organizations in the manufacturing sector, especially those working with the Department of Defense, comprehending and managing CUI is vital.
Compliance with federal regulations is crucial for protecting CUI from cyber threats, while also ensuring the continuity of contracts and mitigating the risk of penalties. Recent developments in CUI regulations underscore the necessity of protecting CUI by implementing stringent protective measures, as breaches can lead to significant financial and reputational damage for manufacturers. Additionally, ongoing awareness training for employees regarding the CUI Program is essential, as it equips them with the knowledge to handle CUI appropriately.
The forthcoming Federal Acquisition Regulation (FAR) rule will require new contracts to incorporate CUI terminology and practices, further emphasizing the need for adherence. Established by Executive Order 13556, the CUI Program aims to standardize protections across federal agencies, making it imperative for manufacturers to remain informed about these regulations to avoid potential risks associated with non-compliance.
Differentiate Between CUI Basic and CUI Specified
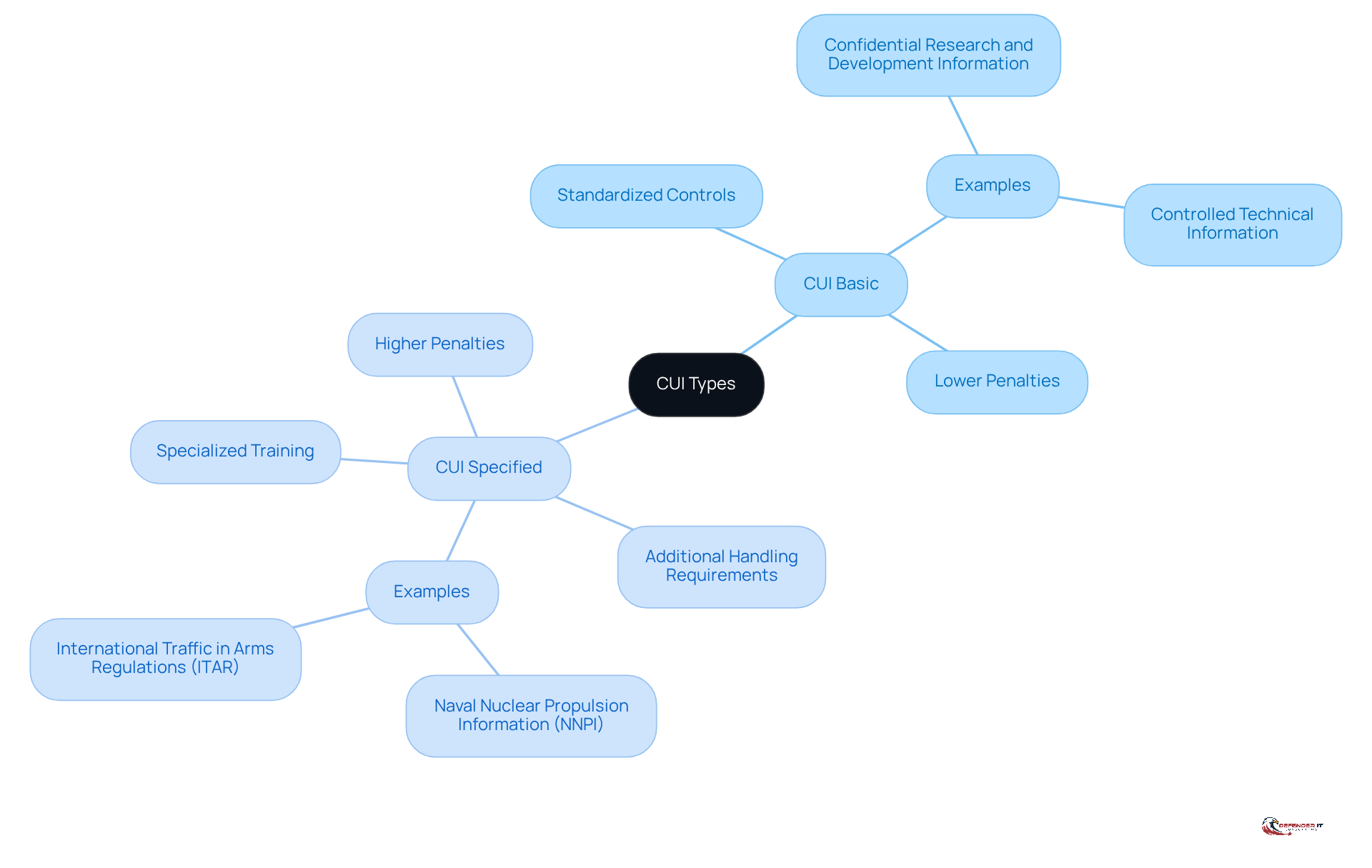
CUI is categorized into two primary types: CUI Basic and CUI Specified. CUI Basic follows a standardized set of controls as outlined in the CUI Registry. In contrast, CUI Specified imposes additional handling requirements dictated by specific laws or regulations. For example, CUI Specified may include sensitive information such as Naval Nuclear Propulsion Information (NNPI) and International Traffic in Arms Regulations (ITAR), which require enhanced access controls or advanced encryption protocols.
This distinction is crucial for organizations aiming to implement effective protective measures for protecting CUI and complying with federal mandates. Notably, the penalties for noncompliance with CUI Specified are significantly higher than those for CUI Basic, highlighting the urgency of adherence. Recent audits revealed that nearly 50% of examined documents lacked proper designation markers, underscoring ongoing regulatory challenges.
Moreover, specialized training for staff with access to CUI data is essential to ensure proper handling and security. Noncompliance can lead to severe legal and financial repercussions, particularly in manufacturing sectors where protecting CUI is vital for contract eligibility and operational integrity. Recent updates to CUI classification requirements have further clarified these distinctions, emphasizing the necessity for entities to remain informed and proactive in their compliance efforts.
Implement Best Practices for Identifying and Categorizing CUI
To effectively identify and categorize [Controlled Unclassified Information (CUI)](https://defenderit.consulting/master-managed-detection-response-essential-insights-for-security-leaders/), organizations must adopt several best practices:
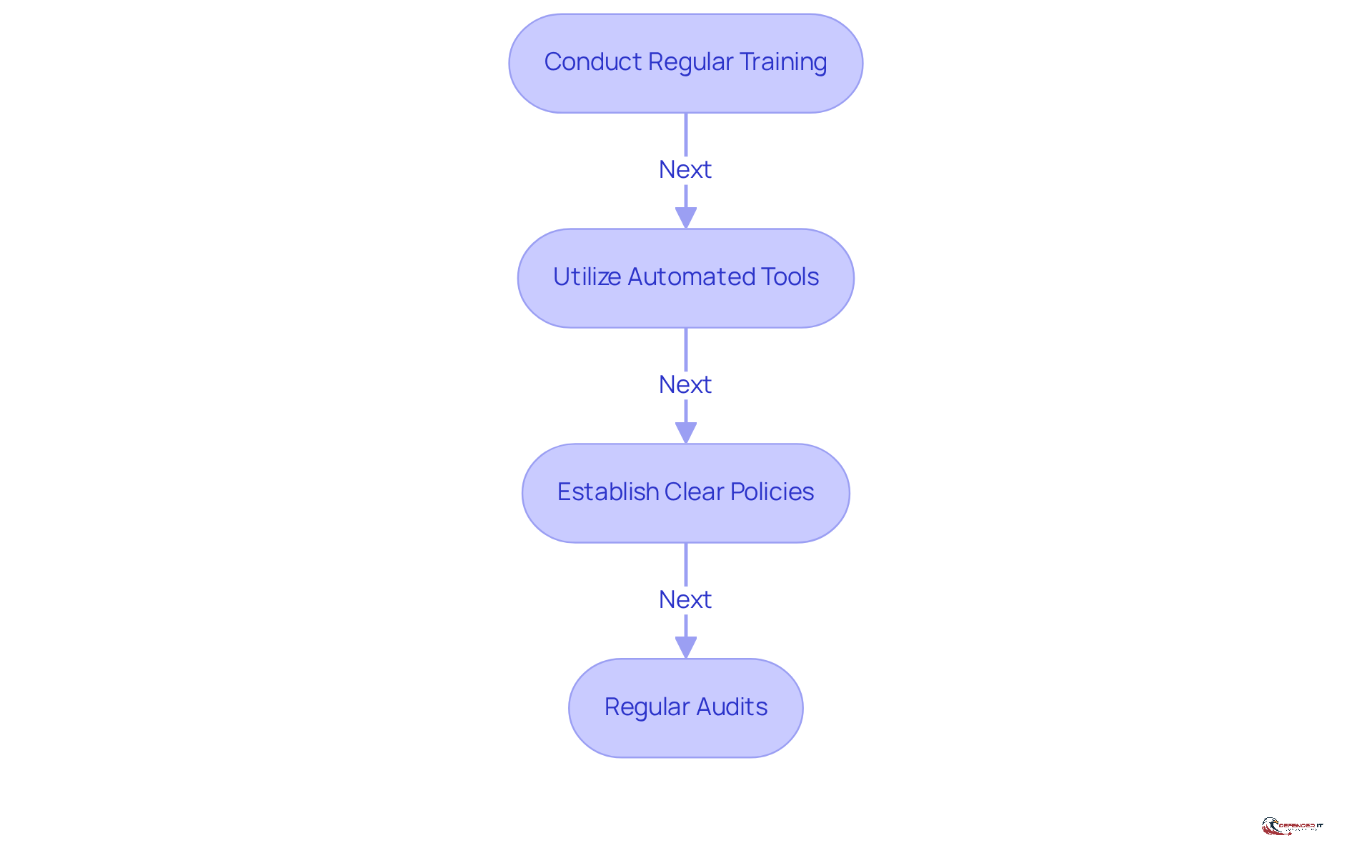
- Conduct Regular Training: All employees should understand what constitutes CUI and the importance of safeguarding it. Consistent training sessions foster a culture of awareness, ensuring that staff are equipped to recognize and manage sensitive information appropriately.
- Utilize Automated Tools: Implement machine learning and AI-driven tools to scan and classify data according to predefined CUI categories. These automated solutions enhance efficiency and accuracy in data management, thereby reducing the risk of human error in classification processes. The growing reliance on such tools reflects current trends in cybersecurity practices, making them essential for modern data management.
- Establish Clear Policies: Develop and disseminate comprehensive policies regarding the handling and categorization of CUI. Clear guidelines ensure that all employees align with organizational standards and regulatory requirements, particularly those outlined by the GSA based on NIST SP 800-171.
- Regular Audits: Conduct periodic audits to assess adherence to CUI identification protocols. These evaluations allow organizations to identify shortcomings in their processes and implement necessary changes to enhance their security posture. Notably, contractors must provide a Security Assessment Report (SAR) every three years, underscoring the importance of routine audits in ensuring compliance.
By adhering to these practices, organizations can significantly bolster their capacity to safeguard sensitive information and ensure compliance with federal regulations. It is also crucial to recognize common pitfalls, such as misclassifying data or neglecting to update training materials, which can undermine these efforts. Ultimately, implementing these best practices not only focuses on protecting CUI but also strengthens overall organizational resilience against cyber threats.
Adopt Security Measures for Protecting CUI
To effectively protect Controlled Unclassified Information (CUI), organizations should implement the following security measures:
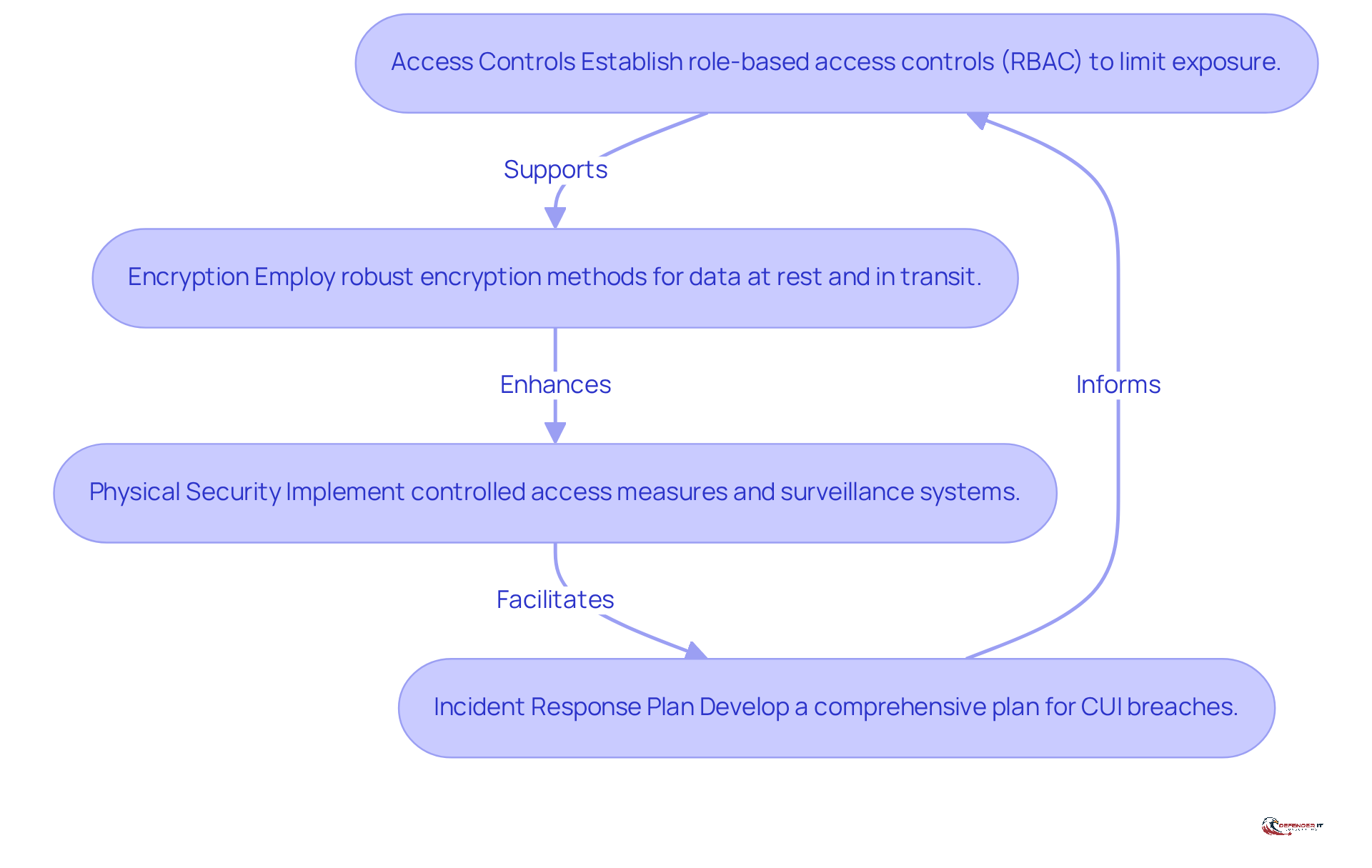
- Access Controls: Establish role-based access controls (RBAC) to ensure that only authorized personnel can access CUI. This approach limits exposure by assigning permissions based on the specific roles and responsibilities of employees, thereby minimizing the risk of unauthorized access.
- Encryption: Employ robust encryption methods for both data at rest and in transit. Utilizing encryption standards such as AES (Advanced Encryption Standard) is crucial for protecting CUI from unauthorized access, ensuring that even if data is intercepted, it remains unreadable without the appropriate decryption keys.
- Physical Security: Secure physical locations where CUI is stored by implementing controlled access measures and surveillance systems. This involves utilizing keycard access, biometric scanners, and surveillance cameras to oversee and limit access to sensitive zones. Furthermore, entities must record their protection and privacy needs as detailed in the GSA IT Security Procedural Guide to guarantee adherence.
- Incident Response Plan: Develop and maintain a comprehensive incident response plan tailored specifically for CUI breaches. This plan should detail procedures for identifying, responding to, and recovering from incidents, including the requirement for one-hour notification for suspected CUI occurrences. Guaranteeing that entities can operate quickly and efficiently to reduce possible harm is essential, particularly considering the urgency of adherence in regulated settings.
By implementing these measures, entities can greatly lower the risk of CUI exposure and improve their overall protective stance, which is essential for protecting CUI and aligning with changing federal expectations for cybersecurity regulations.
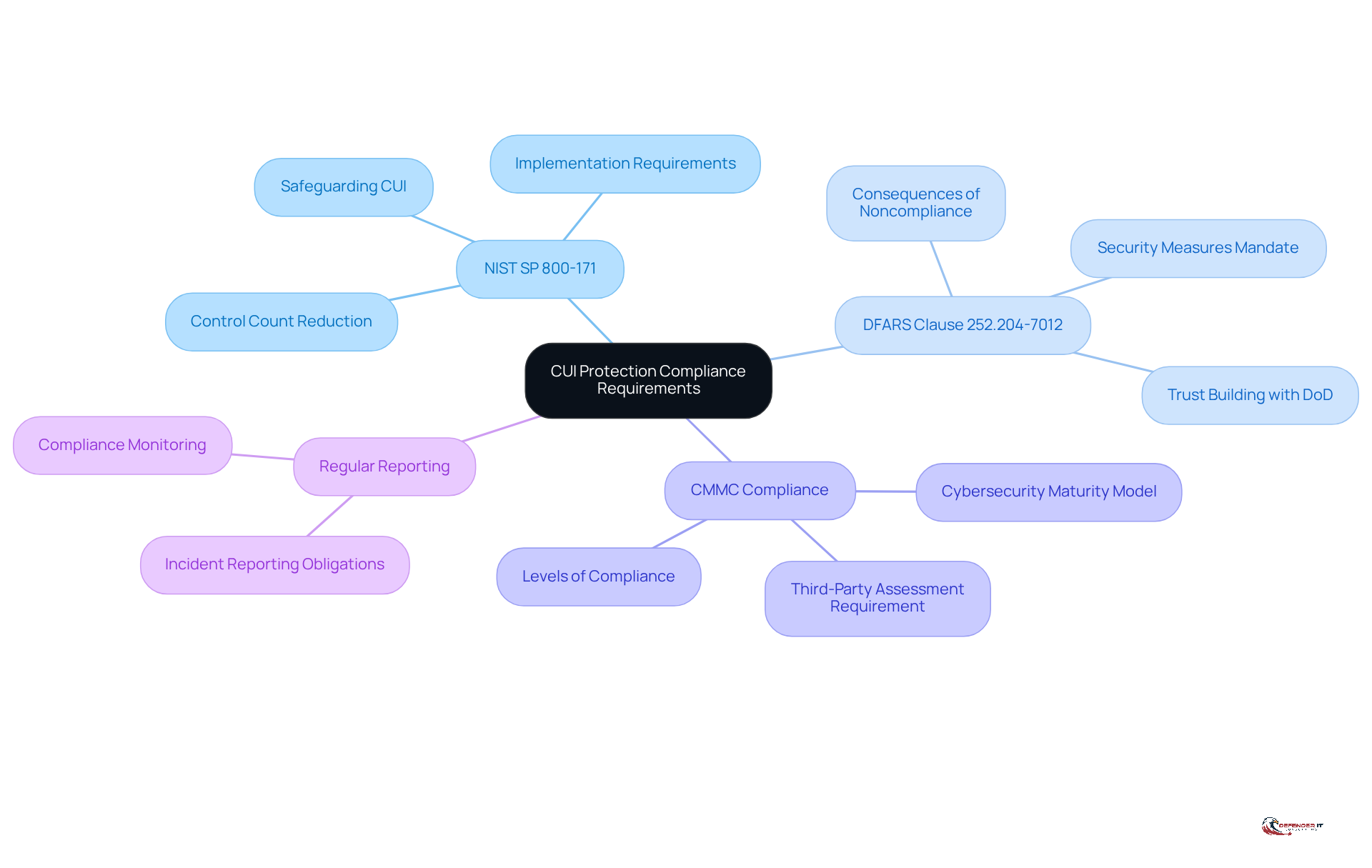
Understand Compliance Requirements for CUI Protection
Organizations must adhere to several compliance requirements for Controlled Unclassified Information (CUI) protection:
- [[NIST SP 800-171](https://defenderit.consulting)](https://defenderit.consulting): This standard outlines the requirements for safeguarding CUI in non-federal systems and entities.
- DFARS Clause 252.204-7012: This clause mandates that defense contractors implement adequate security measures to protect CUI. Noncompliance can lead to severe consequences, including contract termination and withholding of progress payments.
- CMMC Compliance: The Cybersecurity Maturity Model Certification (CMMC) requires entities to demonstrate their cybersecurity capabilities, particularly in protecting CUI. Notably, most Level 2 entities handling CUI must undergo a third-party assessment by a certified C3PAO, adding a verification component to the compliance process.
- [Regular Reporting](https://defenderit.consulting/5-best-practices-for-incident-detection-and-response-in-manufacturing/): Organizations are obligated to report any incidents involving CUI breaches to the appropriate authorities promptly.
By understanding and implementing these regulatory requirements, organizations can ensure they are protecting CUI and mitigating risks associated with non-adherence. Statistics reveal that over 60% of small businesses that experience a cyberattack close within six months, underscoring the urgency for robust cybersecurity measures. Additionally, more than 50% of defense contractors face challenges with CMMC compliance, highlighting the complexities involved in meeting these requirements. Compliance with DFARS 7012 not only fosters trust with the Department of Defense but also enhances competitive positioning within the defense contracting landscape.
Conclusion
Protecting Controlled Unclassified Information (CUI) is essential for organizations in the manufacturing sector. By prioritizing the safeguarding of sensitive data, manufacturers not only comply with federal regulations but also shield their operations from potential cyber threats. The significance of CUI is underscored by its role in maintaining national safety and organizational integrity.
Key practices include:
- Differentiating between CUI Basic and CUI Specified, which enables organizations to identify the necessary protective measures for each category.
- Regular training, automated tools for data classification, and clear policies are vital for ensuring employees handle CUI responsibly.
- Implementing robust security measures, such as access controls, encryption, and physical security, can significantly reduce risks associated with CUI exposure.
Ultimately, protecting CUI transcends regulatory compliance; it is crucial for maintaining trust and competitiveness in the manufacturing landscape. Organizations must remain vigilant and proactive in their compliance efforts to effectively safeguard sensitive information. By embracing these best practices, manufacturers will not only enhance data security but also strengthen the overall resilience of their operations against evolving cyber threats.
Frequently Asked Questions
What is Controlled Unclassified Information (CUI)?
Controlled Unclassified Information (CUI) is sensitive data that, while not classified, requires specific safeguarding and dissemination controls as mandated by law, regulation, or government-wide policy. It includes critical information such as technical specifications, manufacturing processes, and proprietary data.
Why is CUI important?
CUI is important because its unauthorized disclosure could adversely affect national safety. For organizations, especially in the manufacturing sector working with the Department of Defense, understanding and managing CUI is vital for compliance with federal regulations and to protect against cyber threats.
What are the consequences of non-compliance with CUI regulations?
Non-compliance with CUI regulations can lead to significant financial and reputational damage for manufacturers, potential penalties, and disruptions in contract continuity.
What is the difference between CUI Basic and CUI Specified?
CUI is categorized into CUI Basic and CUI Specified. CUI Basic follows standardized controls as outlined in the CUI Registry, while CUI Specified has additional handling requirements dictated by specific laws or regulations, such as Naval Nuclear Propulsion Information (NNPI) and International Traffic in Arms Regulations (ITAR).
What are the penalties for non-compliance with CUI Specified?
The penalties for non-compliance with CUI Specified are significantly higher than those for CUI Basic, emphasizing the urgency of adherence to these regulations.
What recent developments have occurred regarding CUI regulations?
Recent developments in CUI regulations highlight the need for stringent protective measures, with a forthcoming Federal Acquisition Regulation (FAR) rule requiring new contracts to incorporate CUI terminology and practices.
How can organizations ensure compliance with CUI regulations?
Organizations can ensure compliance by implementing protective measures, conducting ongoing awareness training for employees about the CUI Program, and staying informed about updates to CUI classification requirements.
Why is specialized training important for staff handling CUI?
Specialized training is essential for staff with access to CUI data to ensure proper handling and security, thereby reducing the risk of non-compliance and its associated legal and financial repercussions.
List of Sources
- Define Controlled Unclassified Information (CUI) and Its Importance
- What Is CUI And Why Should You Care? – CMMC Compliance (https://cmmccompliance.us/what-is-cui-and-why-should-you-care)
- Controlled Unclassified Information (CUI) (https://gsa.gov/reference/controlled-unclassified-information)
- GSA’s New CUI Requirements: What Government Contractors Need to Know | Insights | Holland & Knight (https://hklaw.com/en/insights/publications/2026/03/gsas-new-cui-security-requirements-what-government-contractors)
- Controlled Unclassified Information (CUI) And Why It Matters! – NASA (https://nasa.gov/controlled-unclassified-information-cui-and-why-it-matters)
- Differentiate Between CUI Basic and CUI Specified
- DoD still failing to properly mark CUI data years after initial audit | Federal News Network (https://federalnewsnetwork.com/defense-news/2026/04/dod-still-failing-to-properly-mark-cui-data-years-after-initial-audit)
- What’s the difference between CUI Basic And CUI Specified? (https://kelsercorp.com/blog/difference-cui-basic-cui-specified)
- Government Proposes New CUI Rules for all Federal Contractors (https://hivesystems.com/blog/cuiproposedrule)
- Implement Best Practices for Identifying and Categorizing CUI
- GSA Introduces a New Framework for Protecting CUI in Contractor Systems (https://natlawreview.com/article/gsa-introduces-new-framework-protecting-cui-contractor-systems)
- GSA Updates Guide for Protecting CUI in Nonfederal Systems (https://executivegov.com/articles/gsa-guide-cui-protection-nonfederal-systems)
- GSA’s New CUI Requirements: What Government Contractors Need to Know | Insights | Holland & Knight (https://hklaw.com/en/insights/publications/2026/03/gsas-new-cui-security-requirements-what-government-contractors)
- Government Proposes New CUI Rules for all Federal Contractors (https://hivesystems.com/blog/cuiproposedrule)
- Adopt Security Measures for Protecting CUI
- GSA Updates Guide for Protecting CUI in Nonfederal Systems (https://executivegov.com/articles/gsa-guide-cui-protection-nonfederal-systems)
- GSA’s New CUI Requirements: What Government Contractors Need to Know | Insights | Holland & Knight (https://hklaw.com/en/insights/publications/2026/03/gsas-new-cui-security-requirements-what-government-contractors)
- GSA Introduces a New Framework for Protecting CUI in Contractor Systems (https://natlawreview.com/article/gsa-introduces-new-framework-protecting-cui-contractor-systems)
- Understand Compliance Requirements for CUI Protection
- How to Comply with NIST SP 800-171 Revision 3 in 2026 | UpGuard (https://upguard.com/blog/nist-800-171-rev3)
- How High a Hurdle is CMMC Compliance for Today’s DoD Suppliers? (https://pivotpointsecurity.com/how-high-a-hurdle-is-cmmc-compliance-for-todays-dod-suppliers)
- Cybersecurity Facts and Stats as of 2026 (https://preveil.com/blog/cybersecurity-statistics)
- NIST 800-171 Rev 2 vs Rev 3: What Changed and What It Means for CMMC (https://secureframe.com/blog/nist-800-171-rev2-vs-rev3)
- What is the DFARS 7012 Clause and Why Should DIB Orgs Care? (https://pivotpointsecurity.com/what-is-the-defense-federal-acquisition-regulation-supplement-dfars-7012-clause)