Introduction
Manufacturers are increasingly navigating a complex landscape of cybersecurity regulations, where compliance is not merely a necessity but a strategic advantage. Understanding and implementing essential cybersecurity compliance services can significantly enhance operational resilience and mitigate risks. As the regulatory environment evolves, it is crucial for manufacturers to ensure they are not only meeting compliance requirements but also effectively safeguarding their assets against the ever-evolving cyber threats. With the looming compliance deadline of 2026, the urgency to address these challenges has never been greater.
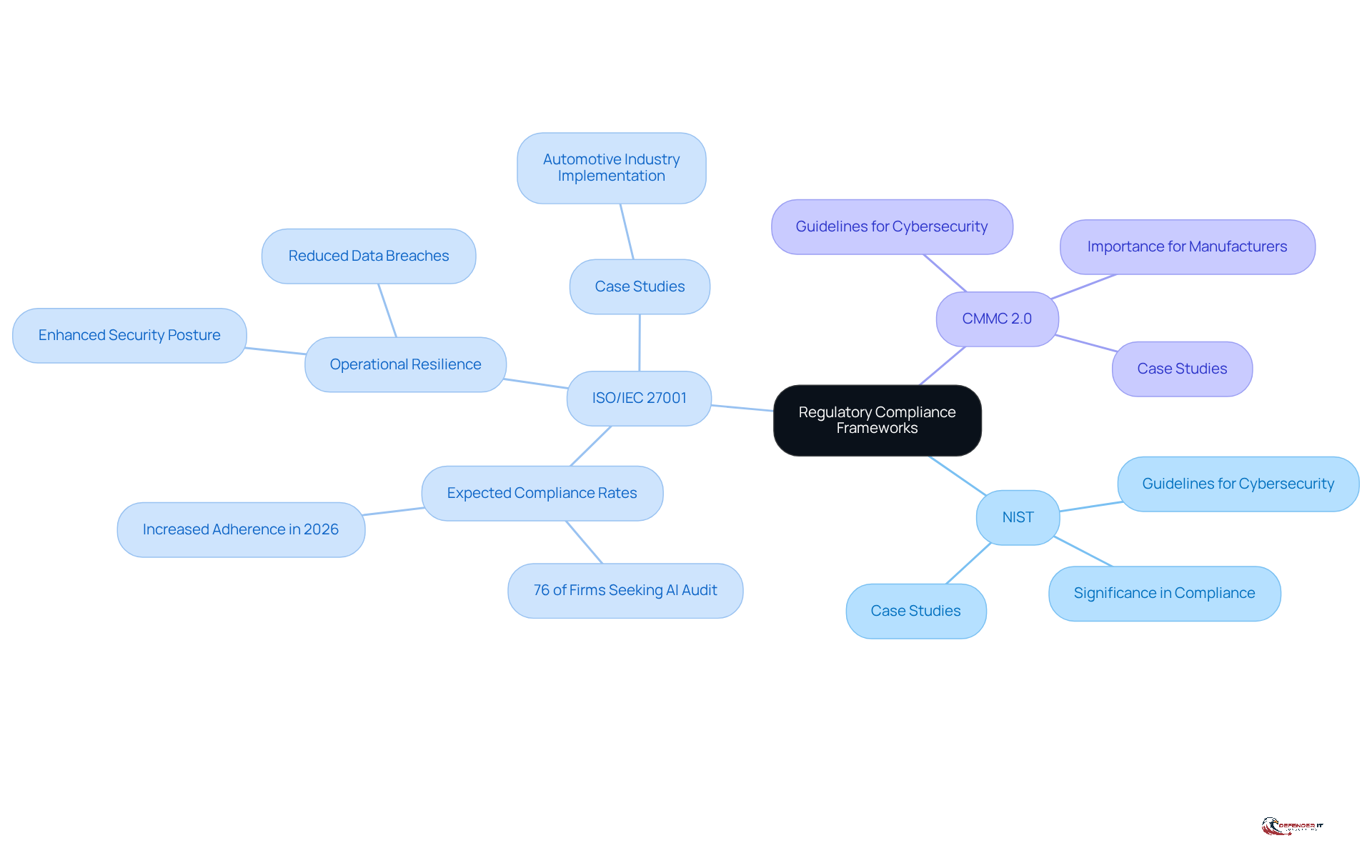
Understand Regulatory Compliance Frameworks
Manufacturers must familiarize themselves with essential regulatory frameworks such as NIST, ISO 27001, and CMMC 2.0. These frameworks provide guidelines for managing and ensuring adherence to industry standards. Notably, the NIST Cybersecurity Framework offers a comprehensive approach to identifying, assessing, and mitigating risks.
In 2026, adherence rates for cybersecurity compliance in the manufacturing sector are expected to increase substantially. A significant 76% of firms intend to seek an AI audit or certification within the next two years, indicating a rising acknowledgment of its significance in enhancing security. Companies that have successfully implemented compliance measures, particularly in the automotive and aerospace industries, demonstrate improved resilience.
For instance, a case study on the automotive industry reveals that entities implementing cybersecurity frameworks have improved their regulatory stance and diminished occurrences of data breaches. As organizations prepare for audits and regulatory inspections, understanding these frameworks not only strengthens their security posture but also emphasizes the role of compliance in minimizing the risk of non-compliance penalties.
Experts emphasize that aligning with these frameworks is crucial for manufacturers to navigate the increasingly complex regulatory landscape effectively, especially in light of the anticipated changes.
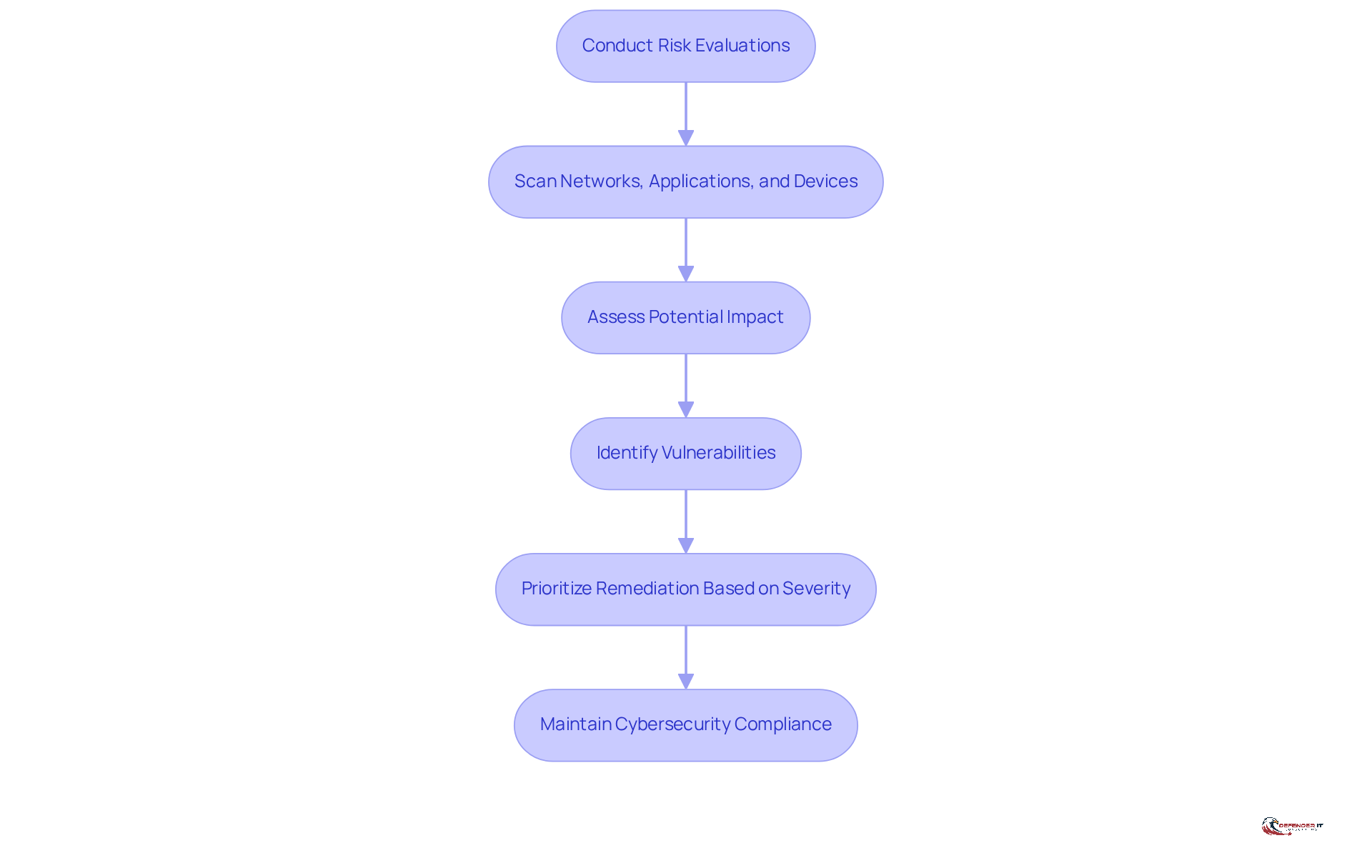
Conduct Regular Vulnerability Assessments
Producers must establish a procedure for conducting assessments to identify potential security weaknesses within their systems. This essential process begins with scanning software, applications, and devices for known vulnerabilities and assessing their potential impact. Notably, in 2026, the average number of cyberattacks is projected to increase significantly, with the anticipated market value to reach $24.08 billion by 2030. This projection underscores the urgency for proactive measures in cybersecurity.
Tools such as Nessus and Qualys play a vital role in vulnerability management, facilitating timely detection of vulnerabilities. Cybersecurity experts advocate for these tools due to their efficiency in identifying weaknesses and streamlining remediation efforts. Following evaluations, manufacturers should prioritize remediation of the identified vulnerabilities, ensuring that critical risks are addressed promptly. This method not only aids in maintaining compliance but also protects sensitive data, thereby reinforcing the overall security posture of the organization.
Furthermore, with 73% of respondents indicating that someone in their network was personally affected by a data breach in 2025, the necessity for cybersecurity measures has never been more critical.
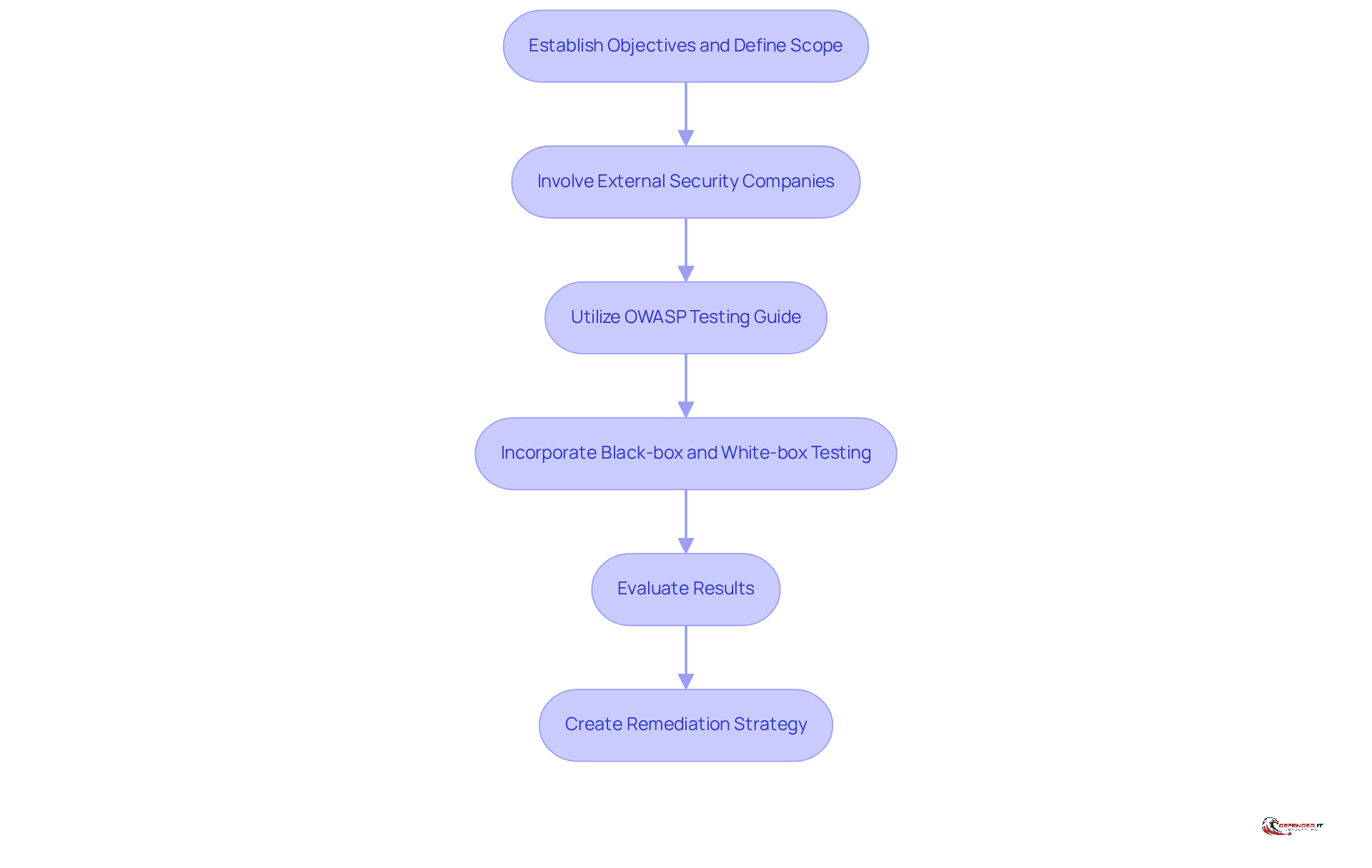
Implement Effective Penetration Testing Strategies
To implement effective penetration testing strategies, manufacturers must first establish clear objectives and define the scope for each assessment. This foundational step is crucial for ensuring that the testing process is both comprehensive and targeted. Involving cybersecurity experts offers an objective viewpoint on weaknesses, which is essential for a successful assessment. Furthermore, utilizing the OWASP Testing Guide provides a framework, ensuring that all critical areas are covered.
Manufacturers should incorporate both automated tools and manual testing to address a broad spectrum of potential attack vectors. This dual approach allows for a more robust evaluation of security vulnerabilities. After the testing phase, it is crucial to thoroughly evaluate the results and create a remediation plan to tackle identified weaknesses. Such a proactive approach not only enhances the overall security stance of the organization but also significantly improves its compliance posture.
Statistics indicate that entities utilizing third-party services encounter a greater rate of issue resolution, underscoring the effectiveness of external expertise in identifying and addressing risks. In fact, the median time to resolve all vulnerabilities is approximately 67 days, with 31% of serious issues remaining unpatched after reporting. This highlights the critical need for engaging qualified external firms to ensure timely and effective remediation.
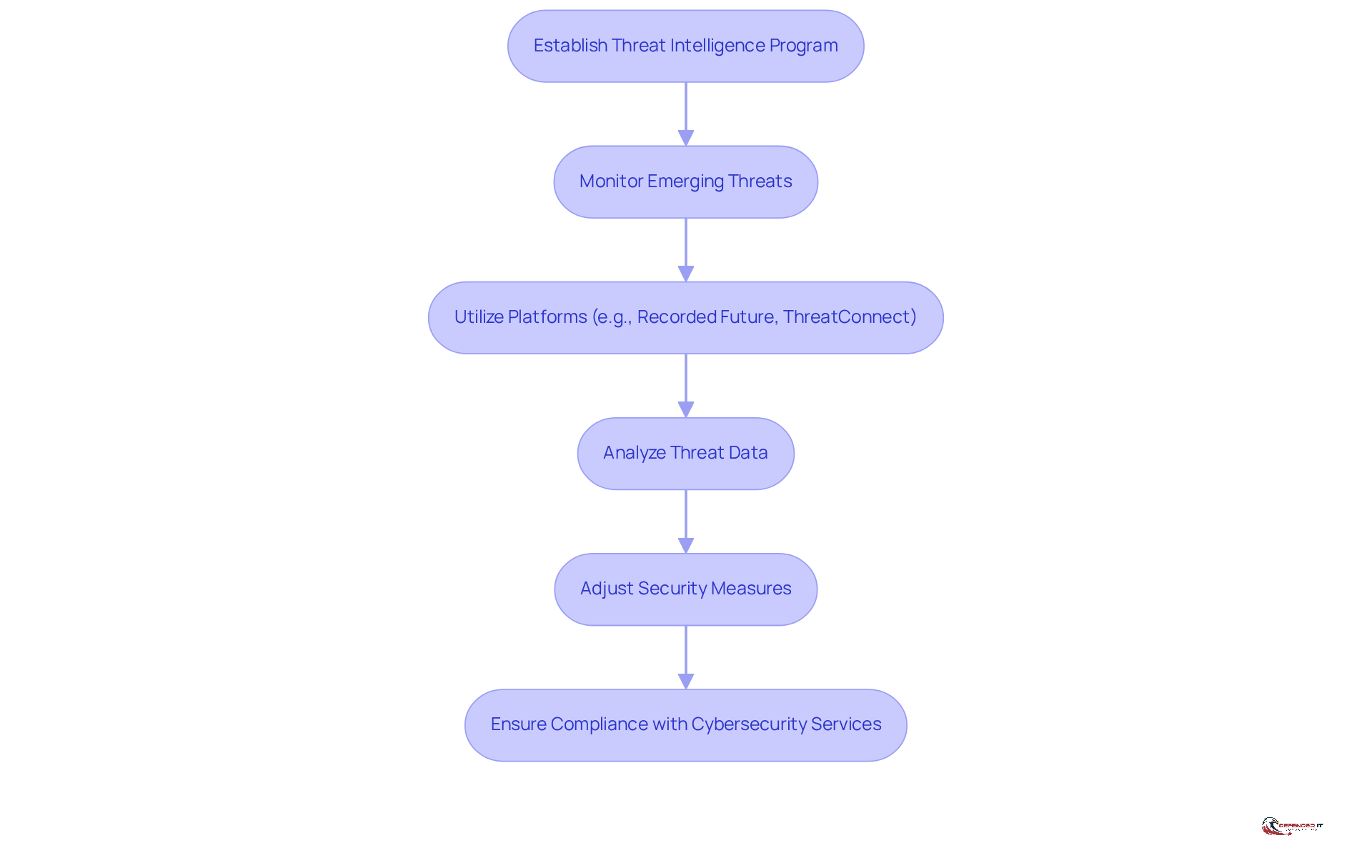
Leverage Threat Intelligence for Compliance
Manufacturers must establish a robust threat intelligence program that continuously monitors threats relevant to their industry. By utilizing platforms such as Recorded Future or ThreatConnect, organizations can gain actionable insights into vulnerabilities and attack vectors. As noted by Team Cyware, “CTI will become proactive instead of reactive, predictive instead of descriptive, and automated instead of manual” by 2026. This underscores the imperative for manufacturers to adopt a proactive approach.
By analyzing threat data, manufacturers can proactively adjust their security measures, ensuring they are in line with regulations that require compliance. For example, when a new vulnerability is identified in widely used software, manufacturers can prioritize their patching efforts to mitigate the risk of exploitation. This not only enhances security but also incorporates best practices to align with industry standards, ultimately safeguarding the organization’s operational integrity.
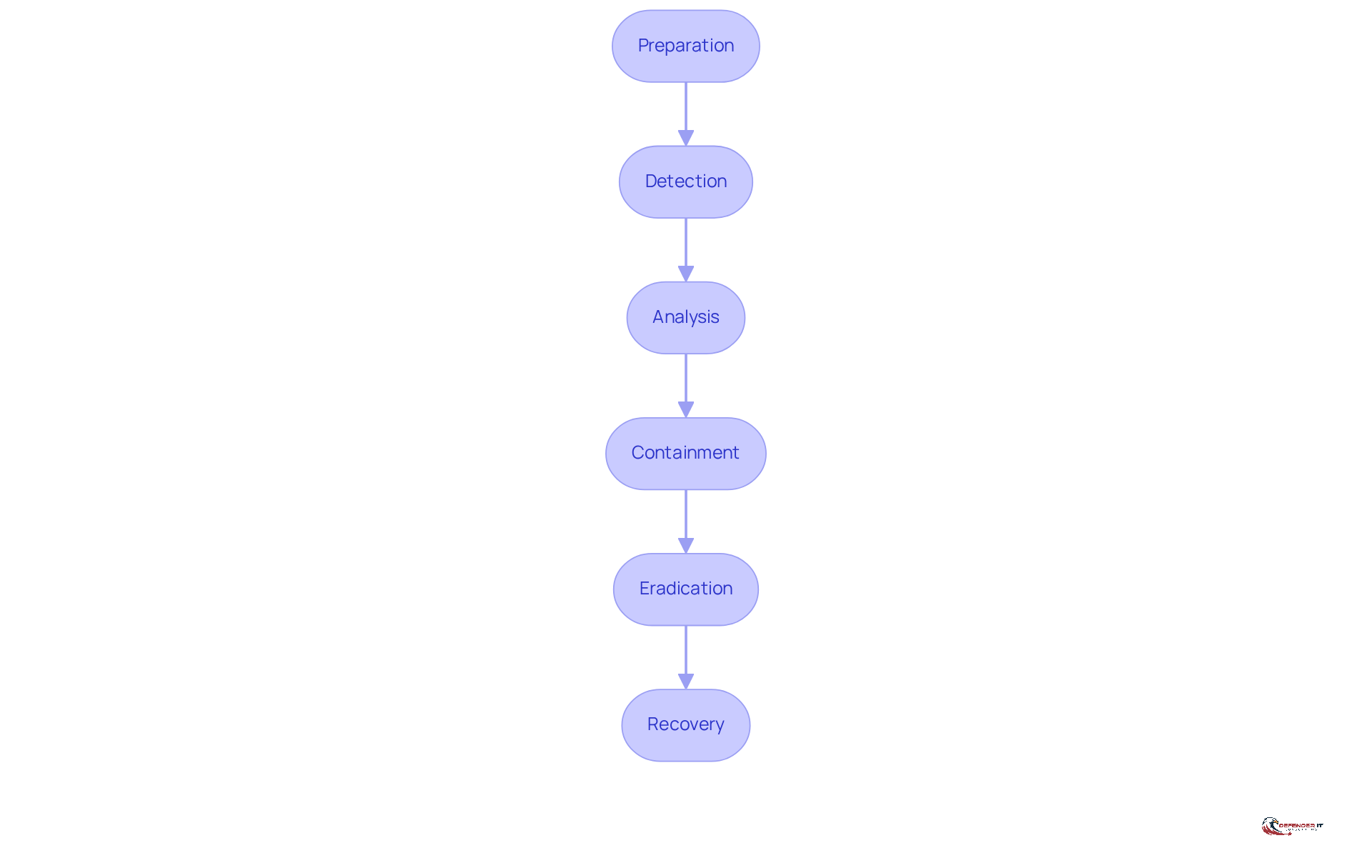
Develop a Robust Incident Response Plan
Manufacturers must develop a plan that clearly defines roles, responsibilities, and procedures for managing cybersecurity events. This plan should encompass activities such as preparation, detection, analysis, containment, eradication, and recovery. Regular testing of the plan through exercises is vital for identifying gaps and improving response times. For instance, simulating a ransomware attack enables manufacturers to evaluate the effectiveness of their response strategies and implement necessary adjustments.
A robust response strategy not only ensures compliance with regulatory standards but also significantly mitigates the impact of security events by utilizing best practices. Organizations with a well-established response strategy can reduce breach costs by up to 58% and resume operations 2.5 times faster. As the manufacturing sector confronts escalating threats, these strategies are crucial for protecting operations and maintaining resilience.
The recent Bridgestone incident underscores the importance of a comprehensive response plan, as even minor disruptions can lead to substantial operational and reputational damage. Moreover, with incidents occurring in approximately 50% of cases, it is essential for manufacturers to incorporate external parties into their response planning.
Additionally, the projected growth in cybersecurity spending in manufacturing by 2026 highlights the urgency of implementing effective plans.
Conclusion
Manufacturers are increasingly recognizing the critical importance of cybersecurity compliance services to navigate the complex regulatory landscape and protect their operations. Understanding and implementing essential frameworks such as NIST, ISO/IEC 27001, and CMMC 2.0 is vital for establishing robust security measures and minimizing the risk of non-compliance. As the manufacturing sector faces growing cyber threats, these frameworks serve as foundational guidelines for managing risks effectively.
The five key compliance services that manufacturers must prioritize include:
- Understanding regulatory compliance frameworks
- Conducting regular vulnerability assessments
- Implementing effective penetration testing strategies
- Leveraging threat intelligence
- Developing a robust incident response plan
Each of these components plays a crucial role in enhancing security posture, addressing vulnerabilities, and ensuring adherence to industry standards. With the anticipated compliance crunch in 2026, proactive measures are essential for safeguarding sensitive data and maintaining operational integrity.
In light of the evolving cybersecurity landscape, manufacturers are urged to take decisive action by investing in these compliance services. By doing so, they not only protect their assets and reputation but also position themselves for success in an increasingly regulated environment. Embracing these best practices will ultimately contribute to a more resilient manufacturing sector, capable of withstanding the challenges posed by cyber threats while ensuring compliance with essential regulatory requirements.
Frequently Asked Questions
What are some essential regulatory compliance frameworks for manufacturers?
Manufacturers should familiarize themselves with frameworks such as NIST, ISO/IEC 27001, and CMMC 2.0, which provide structured guidelines for managing cybersecurity risks and adhering to industry standards.
How does the NIST Cybersecurity Framework (NIST CSF) assist manufacturers?
The NIST CSF offers a comprehensive approach to identifying, assessing, and mitigating cybersecurity risks, helping manufacturers improve their security posture.
What is the expected trend for ISO/IEC 27001 adherence in the manufacturing sector by 2026?
By 2026, adherence rates for ISO/IEC 27001 in the manufacturing sector are expected to increase substantially, with 76% of firms planning to seek an AI audit or certification within the next two years.
What benefits have companies experienced from implementing ISO/IEC 27001?
Companies, especially in the automotive and aerospace industries, have demonstrated enhanced operational resilience and reduced risk exposure after successfully implementing ISO/IEC 27001.
Why is it important for manufacturers to understand regulatory frameworks?
Understanding these frameworks strengthens security posture and emphasizes the importance of cybersecurity compliance services in minimizing the risk of non-compliance penalties.
What is the significance of conducting regular vulnerability assessments for producers?
Regular vulnerability assessments help identify potential security weaknesses, allowing manufacturers to address risks proactively and maintain cybersecurity compliance.
What tools can assist in the vulnerability assessment process?
Tools like Nessus and Qualys are vital for automating the scanning process and facilitating timely detection of vulnerabilities.
How should manufacturers prioritize remediation after vulnerability assessments?
Manufacturers should prioritize remediation based on the severity of identified vulnerabilities, ensuring that critical risks are addressed promptly.
What alarming statistic highlights the necessity for regular risk assessments?
In 2025, 73% of respondents indicated that someone in their network was personally affected by cyber-enabled fraud, underscoring the urgency for regular risk assessments.
List of Sources
- Understand Regulatory Compliance Frameworks
- NIST compliance in 2026: A complete implementation guide | UpGuard (https://upguard.com/blog/nist-compliance)
- One moment, please… (https://isms.online/information-security/five-security-and-compliance-trends-to-look-out-for-in-2026)
- nextgov.com (https://nextgov.com/cybersecurity/2026/01/nist-releases-new-draft-cybersecurity-framework-systems-never-stop-moving/411074)
- Cyber Insights 2026: Regulations and the Tangled Mess of Compliance Requirements (https://securityweek.com/cyber-insights-2026-regulations-and-the-tangled-mess-of-compliance-requirements)
- 130+ Compliance Statistics & Trends to Know for 2026 (https://secureframe.com/blog/compliance-statistics)
- Conduct Regular Vulnerability Assessments
- Cyber threats to watch in 2026 – and other cybersecurity news (https://weforum.org/stories/2026/02/2026-cyberthreats-to-watch-and-other-cybersecurity-news)
- Cybersecurity 2026: AI, CISA, manufacturing sector all in the hot seat (https://cybersecuritydive.com/news/cyber-trends-outlook-2026/810708)
- Vulnerability Management Market: 2026 Edition (https://finance.yahoo.com/news/vulnerability-management-market-2026-edition-090500436.html)
- Why and How to Perform Cybersecurity Risk Assessments in 2026 (https://maddevs.io/blog/how-to-perform-cybersecurity-risk-assessments)
- Implement Effective Penetration Testing Strategies
- Penetration Testing Market Set for Explosive Growth to US$ 11.8 Billion by 2033, Led by North America’s 35.1% Market Share (https://openpr.com/news/4420209/penetration-testing-market-set-for-explosive-growth-to-us-11-8)
- The 2026 State of Pentesting: How Modern Teams Manage and Deliver Results (https://thehackernews.com/expert-insights/2026/01/the-2026-state-of-pentesting-how-modern.html)
- Sprocket Security | The Cyber Threats That Will Define 2026 (And Why… (https://sprocketsecurity.com/blog/the-cyber-threats-that-will-define-2026-and-why-point-in-time-testing-keeps-missing-them)
- Penetration Testing Companies To Consider In 2026 (https://blazeinfosec.com/post/penetration-testing-companies)
- Why Penetration Testing is Important for Your Business in 2026 (https://brightdefense.com/resources/why-penetration-testing-is-important)
- Leverage Threat Intelligence for Compliance
- 2026: The Year When Cyber Threat Intelligence Evolves Into Proactive AI-Driven Cyber Defense (https://cyware.com/blog/2026-the-year-when-cyber-threat-intelligence-evolves-into-proactive-ai)
- Key Cybersecurity Statistics and Emerging Trends for 2026 (https://cdnetworks.com/blog/cloud-security/cybersecurity-statistics-and-trends-2026)
- Cybersecurity 2026: AI, CISA, manufacturing sector all in the hot seat (https://cybersecuritydive.com/news/cyber-trends-outlook-2026/810708)
- 2026 Will Be a Breakthrough Year for Cyberthreats: Four Predictions for Manufacturers (https://ien.com/redzone/blog/22958566/2026-will-be-a-breakthrough-year-for-cyberthreats-four-predictions-for-manufacturers)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Develop a Robust Incident Response Plan
- Every business needs an Incident Response Plan in 2026 – csg[it] (https://csgrp.co.uk/blog/every-business-needs-incident-response-plan-2026)
- sundayguardianlive.com (https://sundayguardianlive.com/trending/incident-response-plans-evolve-into-battle-tested-drills-as-stricter-2026-cybersecurity-rules-take-effect-everything-you-need-to-know-168935)
- 7 Incident Response Metrics and How to Use Them (https://securityscorecard.com/blog/how-to-use-incident-response-metrics)
- Bridgestone Incident Highlights Growing Cyber Risks to Manufacturing | Radiflow (https://radiflow.com/blog/bridgestone-incident-growing-cyber-risks-manufacturing)
- Incident Response Statistics to Know in 2025 (https://jumpcloud.com/blog/incident-response-statistics)