Introduction
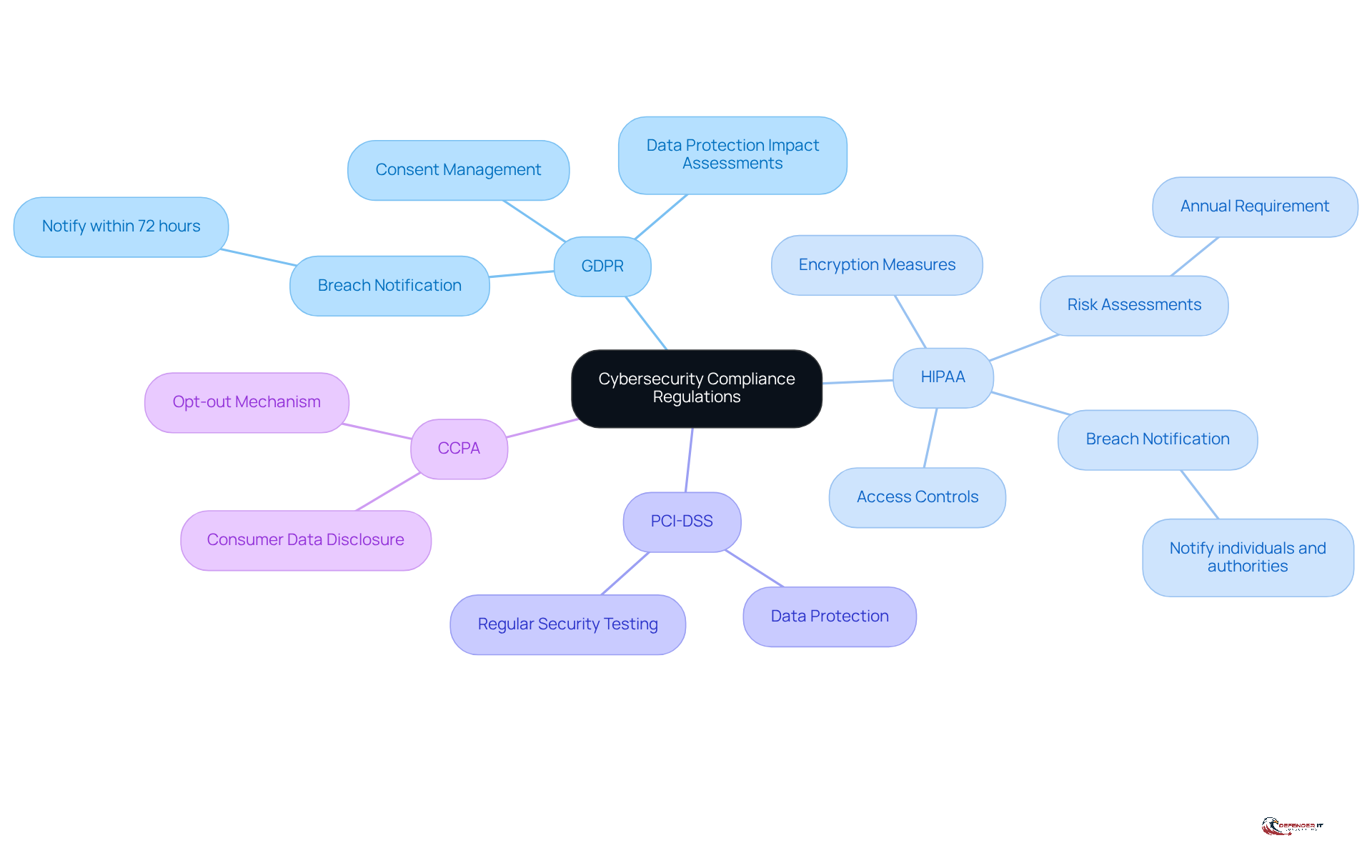
Navigating the complex landscape of cybersecurity compliance presents significant challenges for organizations today. With numerous regulations such as GDPR, HIPAA, and PCI-DSS impacting businesses, it is crucial to understand and implement the appropriate compliance services to protect sensitive data and mitigate risks. As regulations evolve and new challenges arise, organizations must consider how to maintain compliance while simultaneously enhancing their cybersecurity posture. This article explores five essential cybersecurity compliance services that not only fulfill regulatory requirements but also strengthen an organization’s defenses against the ever-evolving landscape of cyber threats.
Understand Regulatory Requirements for Cybersecurity Compliance
Organizations must have a comprehensive understanding of various cybersecurity regulations, such as GDPR, HIPAA, and PCI-DSS, as each regulation presents distinct requirements for data protection, breach notification, and risk management. For example, GDPR mandates that companies report data breaches within 72 hours, while HIPAA requires healthcare entities to implement stringent access controls and encryption measures.
Looking ahead to 2026, significant updates to HIPAA regulations will further underscore the necessity for thorough risk assessments and incident response capabilities, including mandatory penetration testing and vulnerability scans. The reinstatement of the HIPAA Audit Program in 2025 will ensure ongoing scrutiny of organizations regarding compliance with these regulations. Additionally, modifications to the California Consumer Privacy Act (CCPA) and other state laws set to take effect in 2026 will introduce further challenges for compliance.
To effectively navigate these complex regulatory landscapes, businesses should conduct a detailed analysis of their operational environments to identify the relevant . Engaging with legal specialists or regulatory advisors can provide essential insights into cyber security compliance services, ensuring that organizations fulfill their legal obligations while enhancing their overall security posture. This proactive approach is crucial, as entities that prioritize compliance are better positioned to mitigate risks and bolster their resilience against cyber threats.
Conduct Comprehensive Vulnerability Assessments
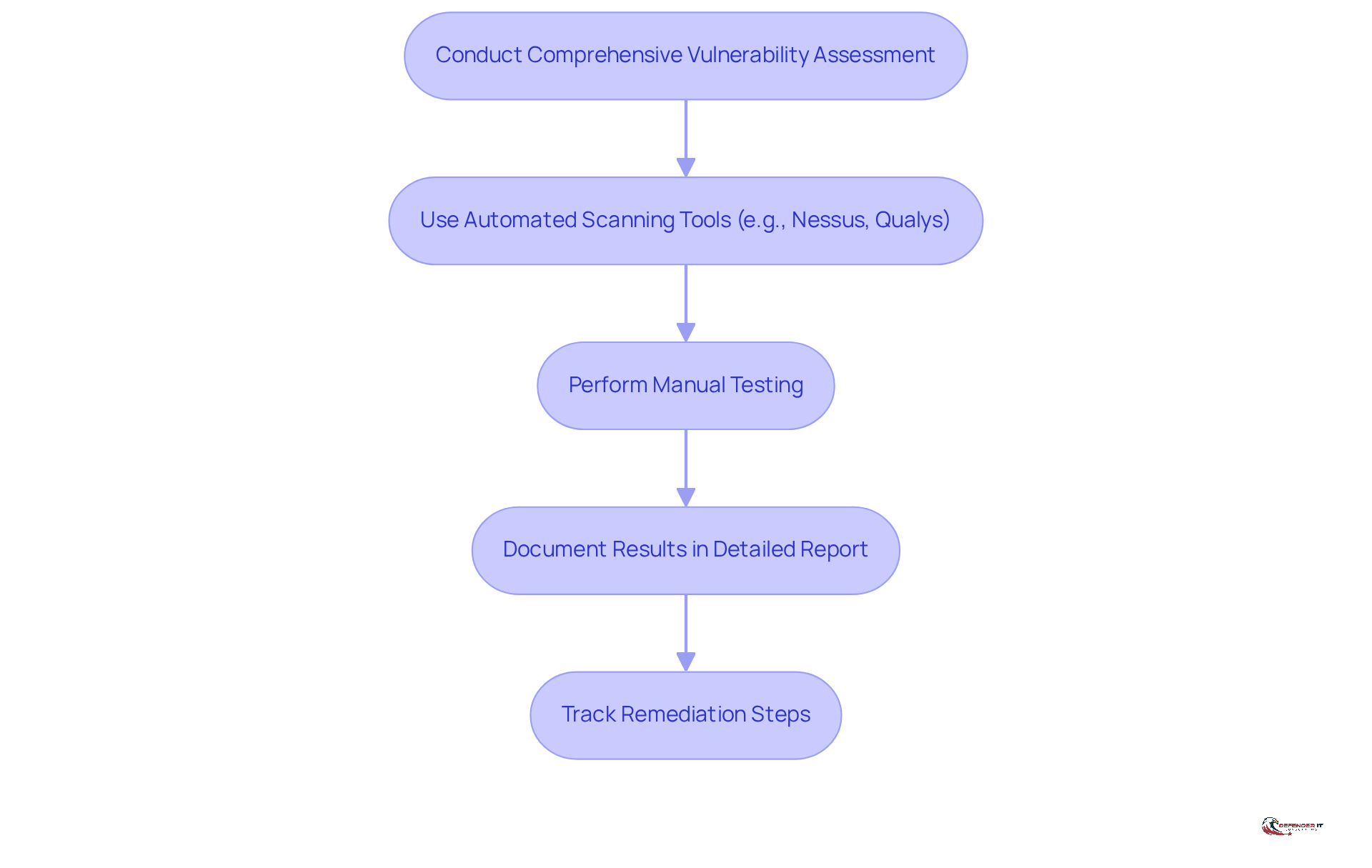
A comprehensive [vulnerability assessment](https://deepstrike.io/blog/vulnerability-statistics-2025) is essential for identifying, classifying, and prioritizing vulnerabilities within a company’s IT infrastructure. This process must incorporate both and manual testing to guarantee thorough coverage. Organizations should conduct these assessments regularly – at least quarterly – and after any significant changes to their systems.
For instance, a financial institution may employ tools such as Nessus or Qualys to scan for vulnerabilities, followed by manual penetration testing to exploit identified weaknesses. The results of these assessments should be documented in a detailed report that outlines remediation steps, which can then be tracked to ensure timely resolution.
This proactive approach not only aids in achieving cyber security compliance services but also significantly enhances the organization’s overall security framework.
Implement Tailored Cybersecurity Training Programs
Organizations must prioritize the creation and execution of customized cybersecurity training programs that specifically address the unique risks and regulatory requirements of their industry. For example, in the healthcare sector, training should emphasize adherence to HIPAA and the critical importance of protecting patient information. Engaging training sessions should cover essential topics such as:
These sessions should incorporate real-world scenarios to enhance relevance and retention.
Research indicates that by 2026, 51% of employees will be aware of phishing risks, underscoring the need for effective training. Furthermore, gamification has been shown to increase engagement by 60%, making interactive training methods particularly effective. Regular refresher courses are crucial to keep employees informed about the latest threats and compliance updates, especially given that 88% of businesses experienced at least one ransomware attack in the previous year.
By fostering a culture of security awareness, organizations can significantly reduce the risk of human error, which accounts for a substantial percentage of security breaches. Successful case studies demonstrate that organizations implementing have experienced a marked decrease in breaches, illustrating the effectiveness of such initiatives in enhancing overall cybersecurity resilience.
Establish an Effective Incident Response Plan
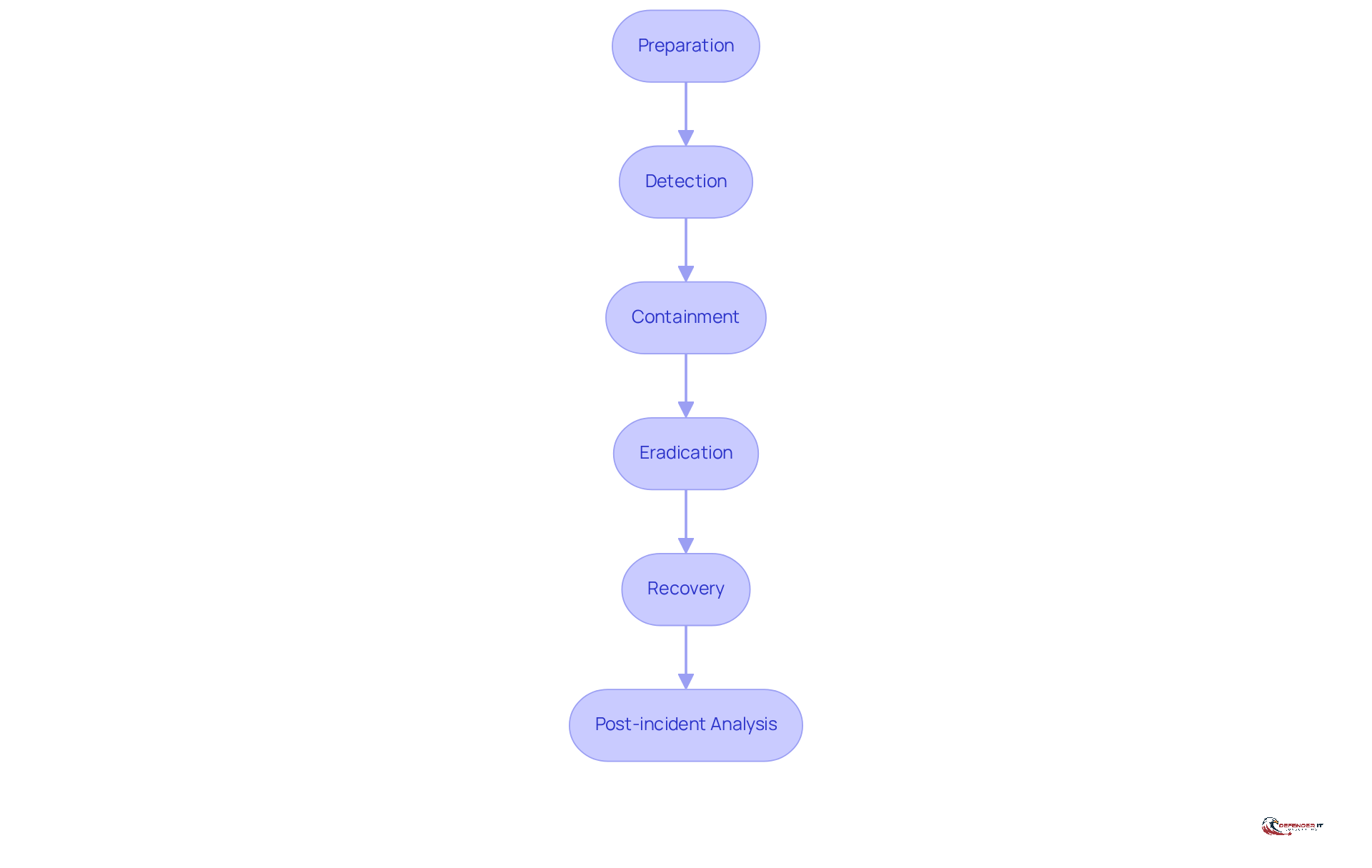
An effective incident response plan (IRP) is essential for organizations confronting cybersecurity incidents. It outlines critical steps such as:
- Preparation
- Detection
- Containment
- Eradication
- Recovery
- Post-incident analysis
Establishing a dedicated incident response team with clearly defined roles and responsibilities is crucial. For example, financial institutions frequently conduct simulations of data breach scenarios to assess the effectiveness of their IRP. This practice enables teams to identify weaknesses and .
Statistics reveal that the average cyberattack takes approximately 277 days to control, underscoring the necessity for organizations to continuously enhance their IRPs. Regular updates are vital for cyber security compliance services to adapt to evolving threats and regulatory requirements. By implementing a well-structured IRP, organizations can significantly reduce damage, improve compliance with reporting obligations, and cultivate a culture of preparedness that is essential in today’s dynamic cybersecurity landscape.
Ensure Continuous Monitoring and Improvement of Cybersecurity Practices
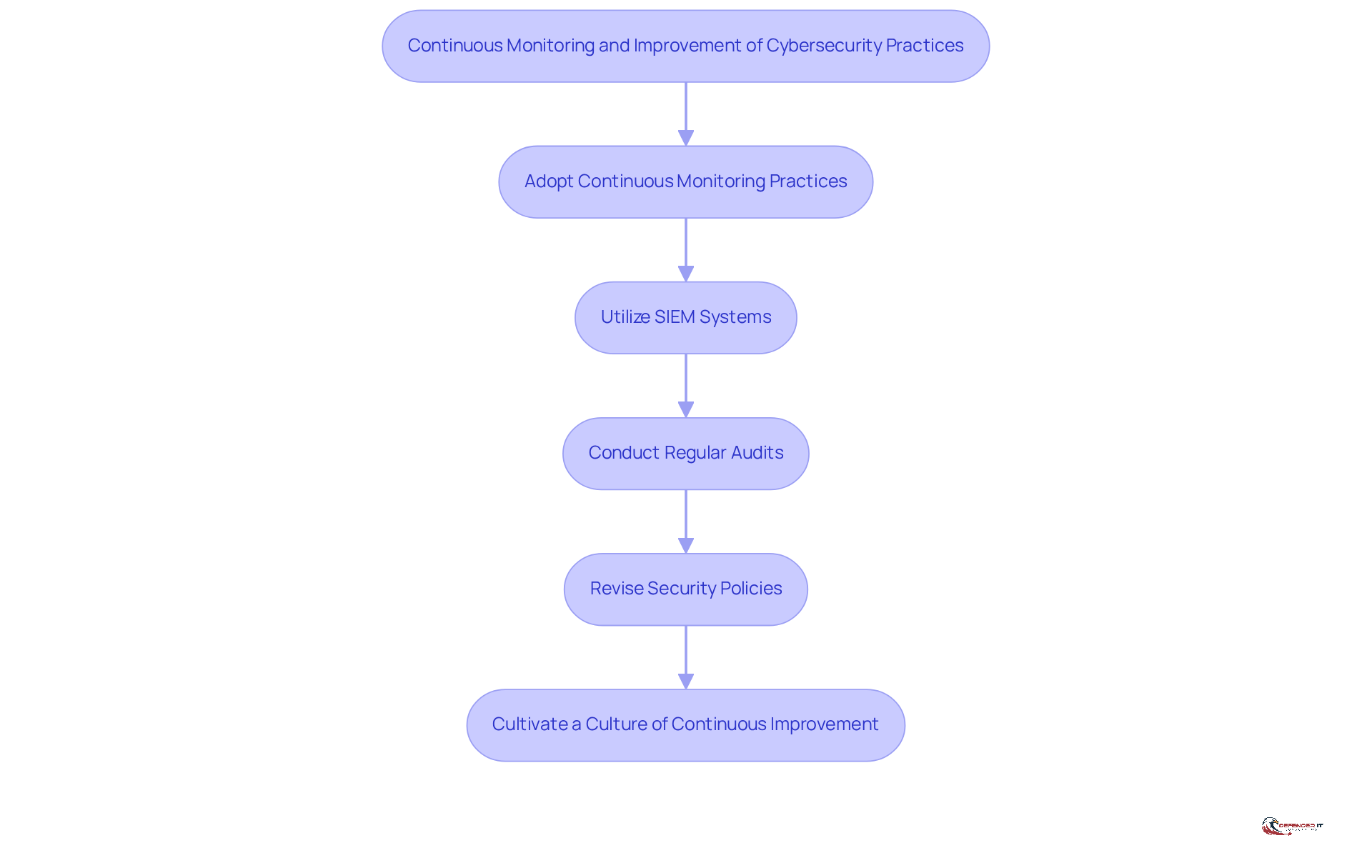
Organizations must adopt [continuous monitoring practices](https://linkedin.com/posts/gerry-blass-917a482_continuousmonitoring-cybersecurity-2026standards-activity-7426626399626514432-LSFE) to effectively identify and address threats in real-time. This approach necessitates the utilization of , which analyze logs to detect anomalies. Furthermore, regular audits and evaluations are essential to assess the effectiveness of existing protective measures and ensure alignment with cyber security compliance services. For example, a healthcare organization may implement automated tools to monitor access to sensitive patient data, generating alerts for any unauthorized attempts.
Ongoing enhancement should be a core principle, with organizations routinely revising their security policies and practices in response to the latest risk information and regulatory updates. By cultivating a culture of continuous improvement, organizations can bolster their resilience against cyber threats while ensuring the effectiveness of their cyber security compliance services.
Conclusion
In conclusion, understanding and implementing essential cybersecurity compliance services is vital for organizations that seek to protect their data and meet regulatory requirements. As regulations evolve and become increasingly stringent, businesses must engage proactively in strategies that not only fulfill compliance obligations but also enhance their overall security posture.
This article has highlighted five key services:
- Understanding regulatory requirements
- Conducting comprehensive vulnerability assessments
- Implementing tailored training programs
- Establishing effective incident response plans
- Ensuring continuous monitoring and improvement
Each of these components plays a crucial role in building a robust cybersecurity framework, enabling organizations to mitigate risks, respond effectively to incidents, and foster a culture of security awareness among employees.
In today’s complex digital landscape, the necessity for effective cybersecurity compliance services is paramount. Organizations must prioritize these practices to safeguard their assets and maintain trust with clients and stakeholders. By adopting a proactive approach to compliance, businesses not only protect themselves from potential threats but also position themselves for long-term success in a rapidly evolving regulatory environment.
Frequently Asked Questions
What are the key cybersecurity regulations organizations should understand?
Organizations should understand regulations such as GDPR, HIPAA, and PCI-DSS, as each has distinct requirements for data protection, breach notification, and risk management.
What does GDPR require regarding data breaches?
GDPR mandates that companies report data breaches within 72 hours.
What are the requirements for healthcare entities under HIPAA?
HIPAA requires healthcare entities to implement stringent access controls and encryption measures.
What significant updates to HIPAA regulations are expected by 2026?
Significant updates will include mandatory penetration testing and vulnerability scans, along with a focus on thorough risk assessments and incident response capabilities.
What is the HIPAA Audit Program, and when will it be reinstated?
The HIPAA Audit Program ensures ongoing scrutiny of organizations regarding compliance with HIPAA regulations and will be reinstated in 2025.
How will changes to the California Consumer Privacy Act (CCPA) affect compliance?
Modifications to the CCPA and other state laws set to take effect in 2026 will introduce further challenges for compliance.
How can businesses effectively navigate regulatory compliance for cybersecurity?
Businesses should conduct a detailed analysis of their operational environments to identify relevant regulatory frameworks and may benefit from engaging with legal specialists or regulatory advisors.
What is the importance of conducting comprehensive vulnerability assessments?
Comprehensive vulnerability assessments help identify, classify, and prioritize vulnerabilities within a company’s IT infrastructure, enhancing overall security and aiding in compliance.
How often should organizations conduct vulnerability assessments?
Organizations should conduct vulnerability assessments regularly, at least quarterly, and after any significant changes to their systems.
What tools can be used for vulnerability assessments?
Tools such as Nessus or Qualys can be employed for automated scanning, followed by manual penetration testing to exploit identified weaknesses.
What should be included in the documentation of vulnerability assessments?
The results should be documented in a detailed report that outlines remediation steps, which can then be tracked to ensure timely resolution.