Introduction
A robust cybersecurity posture is now a necessity for organizations navigating an increasingly complex digital landscape. The cybersecurity maturity assessment serves as a critical tool, enabling companies to evaluate their security capabilities and align them with established standards. However, many organizations face challenges in effectively conducting these assessments, often leaving vulnerabilities unaddressed.
To systematically enhance their cybersecurity maturity and prepare for emerging threats, businesses must adopt a structured approach. This guide provides a step-by-step methodology for mastering cybersecurity maturity assessments, empowering organizations to strengthen their defenses and achieve compliance.
Define Cybersecurity Maturity Assessment
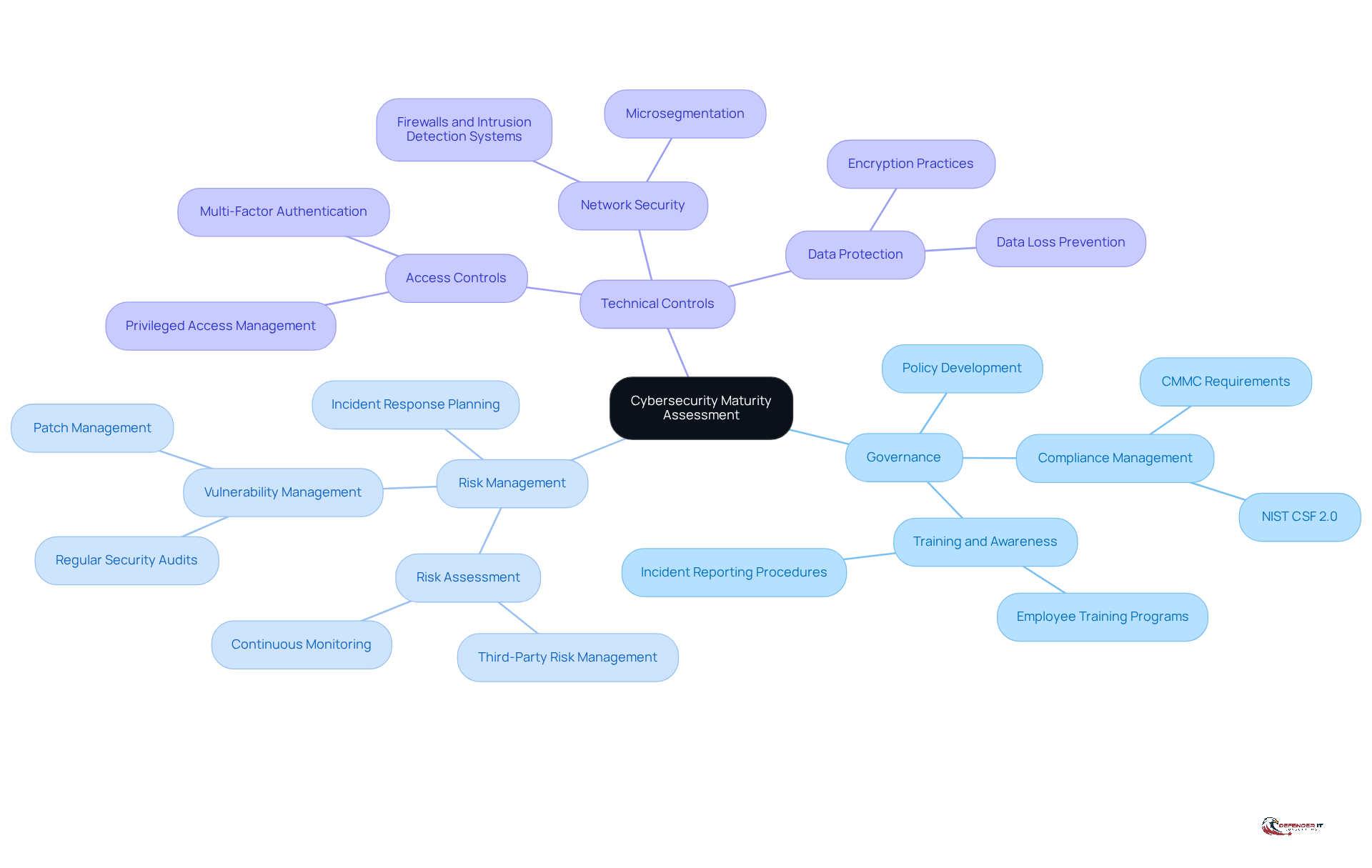
A Cybersecurity Maturity Assessment serves as a systematic review of a company’s security posture, assessing the alignment of its practices with established standards and frameworks. This evaluation primarily targets several critical areas, including:
- Governance
By scrutinizing these components, organizations can ascertain their maturity level, which ranges from ad-hoc practices to fully integrated and proactive security measures. Understanding this framework is essential for organizations aiming to improve their security posture and resilience against threats.
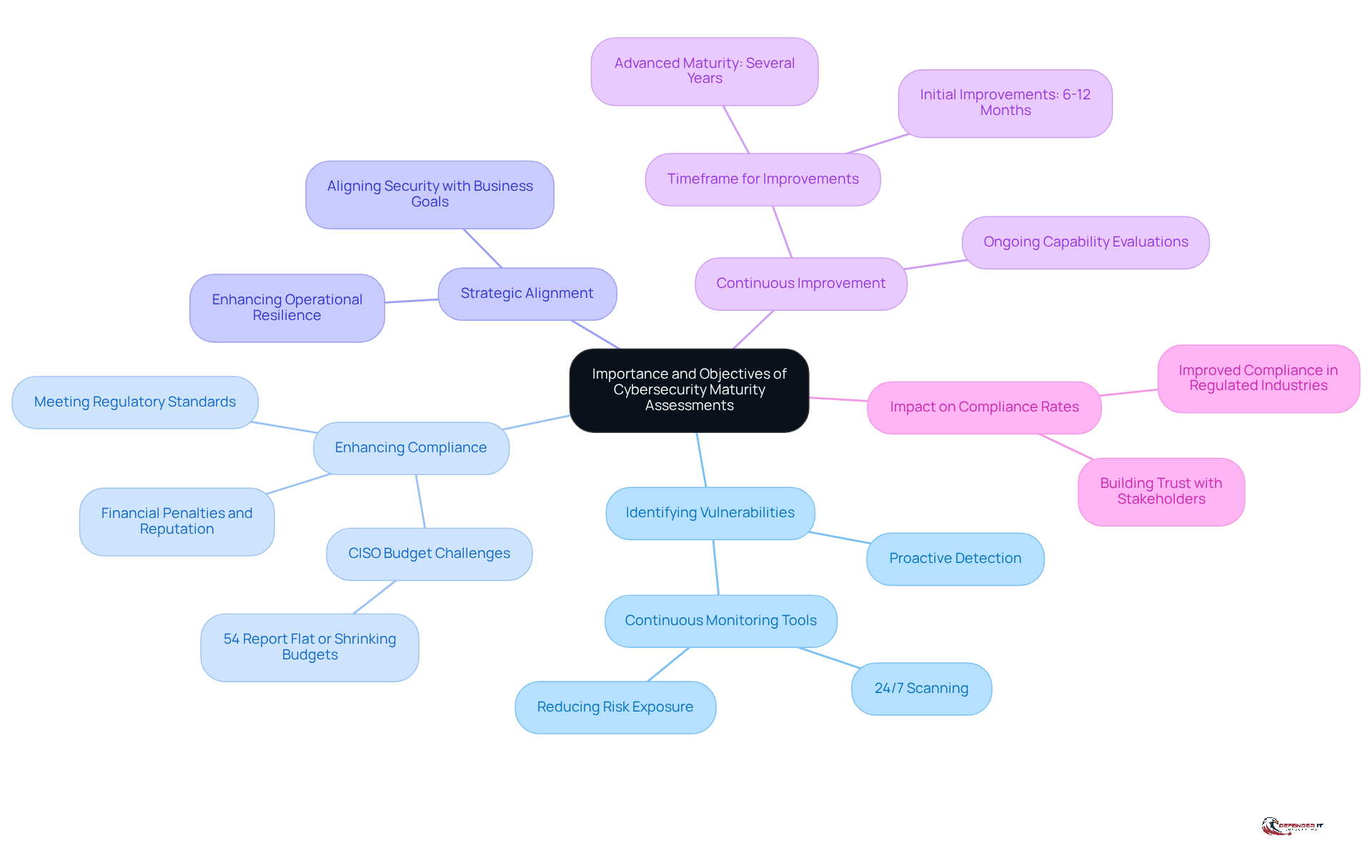
Understand the Importance and Objectives
are essential for organizations seeking to bolster their cybersecurity posture and manage risks effectively. The primary objectives of these assessments include:
- Vulnerability Identification: These evaluations play a critical role in revealing weaknesses within security controls, allowing organizations to proactively address gaps before they can be exploited by cyber threats. For instance, entities employing security monitoring can detect vulnerabilities and misconfigurations around the clock, significantly reducing their risk exposure. Continuous observation is a fundamental aspect of modern digital security strategies, helping organizations stay ahead of potential threats.
- Regulatory Compliance: Many sectors, particularly those under stringent regulations, have specific security development requirements. Conducting a cybersecurity maturity assessment ensures that organizations meet these regulatory standards, thereby minimizing the risk of non-compliance, which can lead to significant penalties. Notably, 54% of Chief Information Security Officers (CISOs) report static or declining budgets, highlighting the challenges organizations face in achieving compliance and enhancing their security posture.
- Strategic Alignment: Understanding their security maturity enables organizations to align their security strategies with broader business objectives. This alignment ensures that security measures not only safeguard assets but also support overall organizational goals, thereby enhancing operational efficiency.
- Continuous Improvement: Regular capability evaluations cultivate a culture of ongoing enhancement. Organizations that commit to continuous improvement can adapt to evolving threats and enhance their defenses over time. Initial improvements in digital security maturity may take 6-12 months, but reaching advanced status requires sustained effort over several years.
- Impact on Compliance Rates: Organizations that effectively assess their cybersecurity maturity often experience improved compliance rates, especially in regulated industries. This proactive approach not only aids in fulfilling compliance requirements but also fosters trust with stakeholders and clients, bolstering the organization’s reputation in the marketplace. As emphasized, developing sophistication in cybersecurity is an ongoing journey.
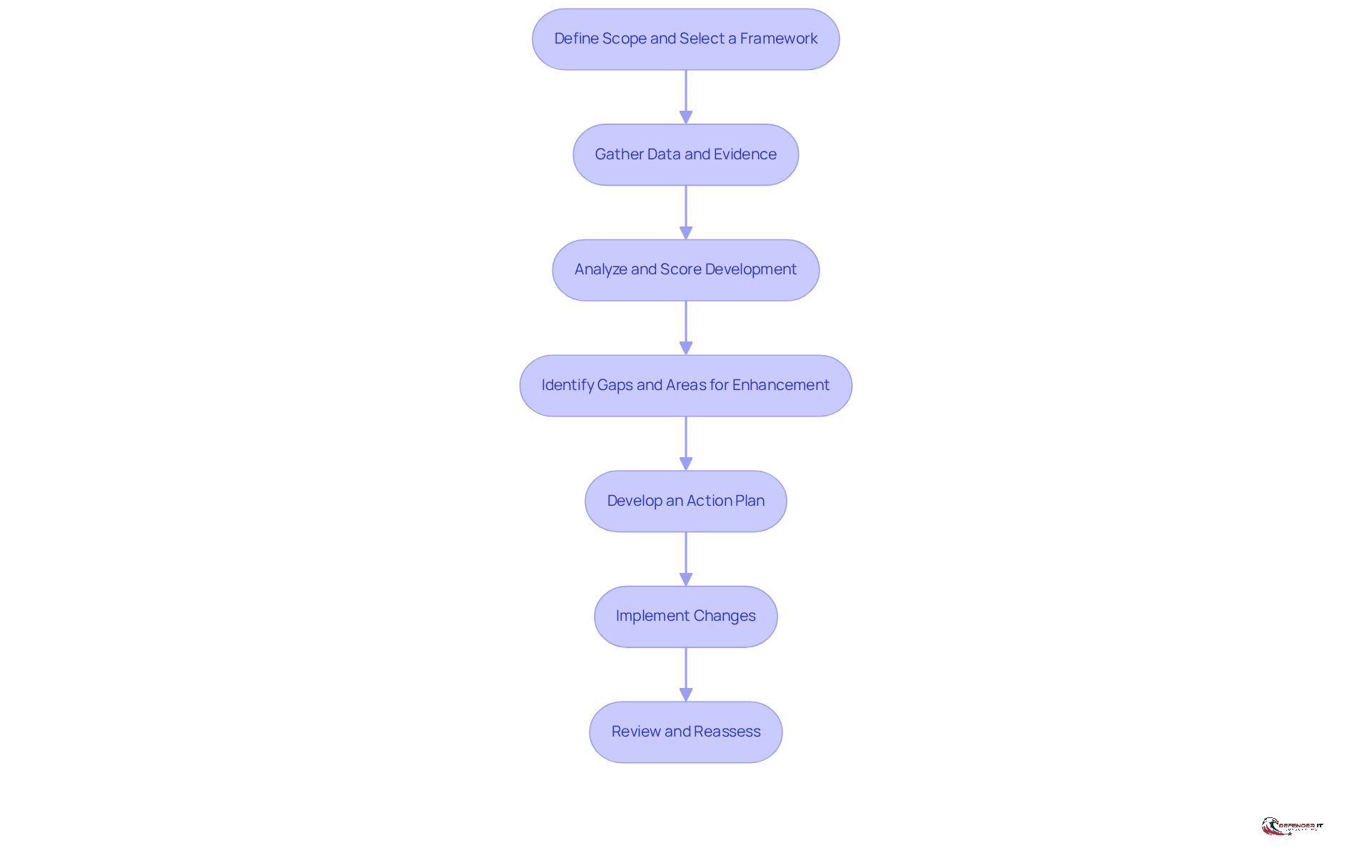
Follow the Step-by-Step Assessment Process
To conduct a cybersecurity maturity assessment effectively, follow these structured steps:
- Define Scope: Clearly outline the assessment’s scope and choose a framework that aligns with your entity’s objectives, such as NIST or ISO 27001. This selection should reflect the timeline, particularly considering the project running from November 2025 to November 2026.
- Gather Data and Evidence: Collect pertinent data through interviews, surveys, and documentation reviews. This comprehensive method assists in grasping current practices and controls, ensuring that all relevant aspects of the entity are considered.
- Analyze and Score Development: Evaluate the collected data against the chosen framework to ascertain the entity’s growth level across various domains. This scoring process provides a clear picture of where the entity stands in terms of its maturity.
- Identify Gaps: Pinpoint areas where the entity does not reach the desired development levels. Prioritize these gaps based on their associated risks, focusing on those that could significantly impact business continuity and compliance. For medium to large enterprises, the projected yearly expenses for reaching targeted development stages can exceed $100,000, making it crucial to address these deficiencies promptly.
- Create Roadmap: Create a detailed roadmap for addressing the identified gaps. This plan should include specific actions, timelines, and designated responsible parties to ensure accountability and progress.
- Implement Changes: Execute the action plan while keeping all stakeholders engaged and informed. Effective communication during this phase is crucial for fostering a culture of security awareness and collaboration. Continuous monitoring is vital to adapt to new threats and ensure the effectiveness of implemented changes.
- Review and Reassess: Regularly revisit the maturity evaluation process to track progress and adapt to emerging threats. Ongoing evaluation via a structured approach guarantees that the entity stays in accordance with changing security challenges and regulatory requirements. As specialists suggest, organizations should transition towards continuous improvement to maintain a robust security posture.
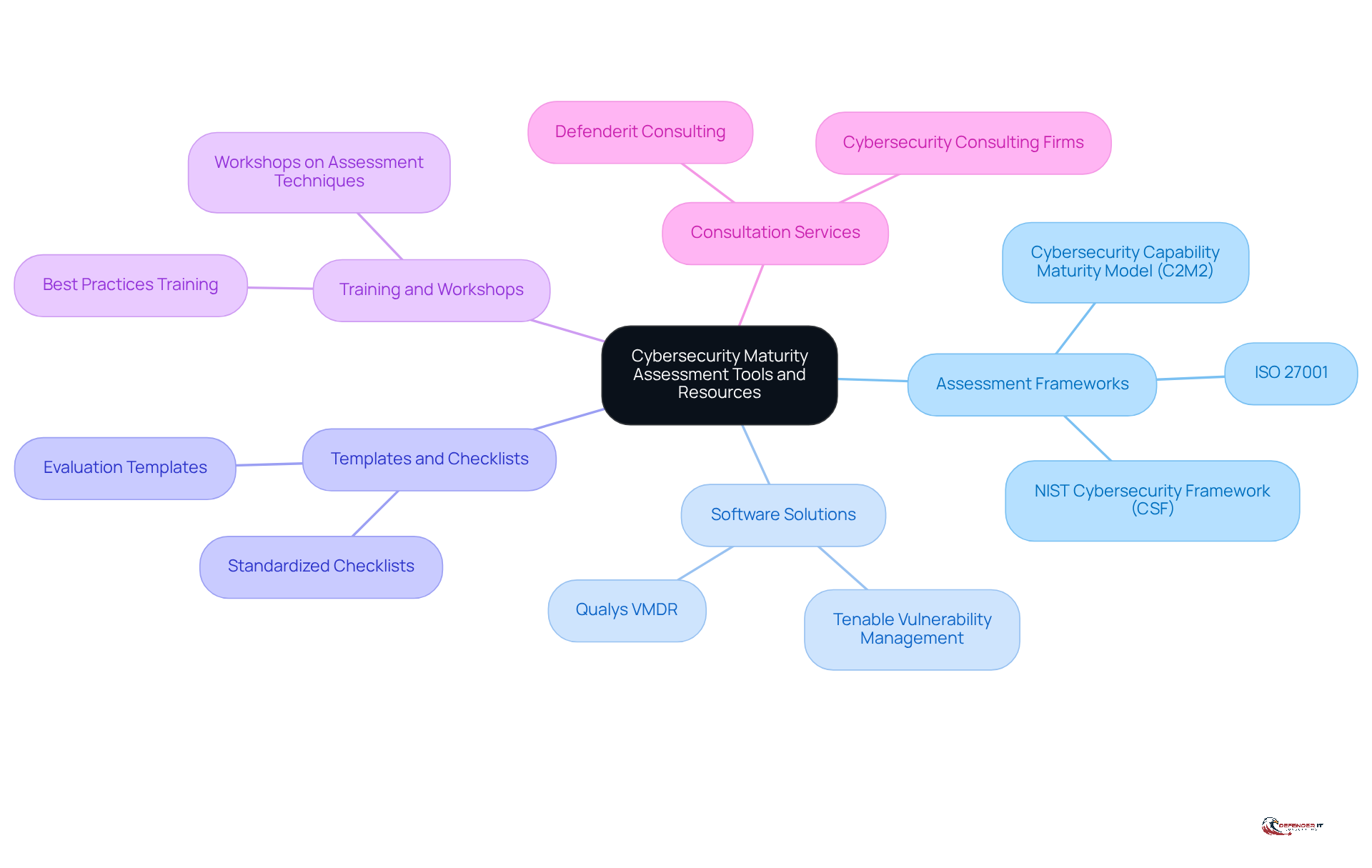
Utilize Tools and Resources for Effective Assessment
To enhance the effectiveness of your assessment, consider utilizing the following tools and resources:
- Frameworks: Leverage established frameworks such as the NIST Cybersecurity Framework, ISO 27001, and the Cybersecurity Capability Maturity Model (C2M2) to guide your assessment process. These frameworks offer organized methods to conduct a review and improve your security practices.
- Software solutions: Implement software solutions that automate data collection and analysis, streamlining the evaluation of your security posture. Tools like Tenable Vulnerability Management and Qualys VMDR continuously scan for vulnerabilities and prioritize them based on risk, enabling proactive defense. Given that over 1,000,000 files are left accessible to every employee, utilizing such tools is crucial to prevent vulnerabilities.
- Checklists: Utilize checklists to ensure comprehensive coverage of all evaluation components, minimizing the risk of oversight. These resources assist in standardizing the evaluation process for the organization and enable consistent appraisals.
- Training: Participate in training sessions or workshops to inform your team on best practices and interpreting results. This investment in knowledge improves the overall effectiveness of your security initiatives.
- Consultants: Partner with experts, such as Defenderit Consulting, to gain expert insights and support throughout the assessment process. Collaborating with specialists can provide tailored strategies and enhance your organization’s security posture. Given that the threat landscape is constantly evolving, this partnership can be invaluable in mitigating risks.
Conclusion
Conducting a cybersecurity maturity assessment is essential for organizations seeking to strengthen their defenses against an ever-evolving threat landscape. This systematic evaluation identifies vulnerabilities, enhances compliance, and aligns security strategies with broader business objectives. By understanding their current maturity level, organizations can foster a culture of continuous improvement, ensuring that their security measures remain effective and adaptive.
The article outlines a comprehensive step-by-step process for executing a cybersecurity maturity assessment. This includes:
- Defining the scope
- Gathering data
- Analyzing results
- Identifying gaps
- Developing actionable plans
It emphasizes the importance of utilizing established frameworks and tools to streamline the assessment process. Furthermore, leveraging expert insights and ongoing evaluations can significantly bolster an organization’s security posture, ultimately leading to improved compliance rates and increased stakeholder trust.
As organizations navigate the complexities of cybersecurity, prioritizing a maturity assessment is not merely a best practice; it is a strategic imperative. Embracing this proactive approach will enhance security measures and cultivate resilience in the face of emerging threats. Organizations must take charge of their cybersecurity journey, ensuring they are equipped to meet the challenges of today and tomorrow.
Frequently Asked Questions
What is a cybersecurity maturity assessment?
A cybersecurity maturity assessment is a systematic review of a company’s cybersecurity capabilities, focusing on how well its security practices align with established standards and frameworks.
What areas does a cybersecurity maturity assessment evaluate?
The assessment primarily targets three critical areas: governance, risk management, and technical controls.
Why is it important to understand cybersecurity maturity?
Understanding cybersecurity maturity is essential for organizations that want to improve their cybersecurity practices and enhance their resilience against emerging threats.
What stages can organizations be at in their cybersecurity maturity?
Organizations can be at various stages of maturity, ranging from ad-hoc practices to fully integrated and proactive security measures.
List of Sources
- Define Cybersecurity Maturity Assessment
- Get to Know the Cybersecurity Maturity Model Certification (https://gsa.gov/blog/2026/02/12/get-to-know-the-cybersecurity-maturity-model-certification)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Assessing Cybersecurity Maturity: How to Benchmark Your Defenses in 2026 (https://zeronetworks.com/blog/assessing-cybersecurity-maturity-how-to-benchmark-your-defenses-in-2026)
- 2026 Cybersecurity Outlook: A Maturity Reckoning (https://cybersecurity-insiders.com/2026-cybersecurity-outlook-a-maturity-reckoning)
- 210+ Cybersecurity Statistics to Inspire Action This Year [Updated Q4 2025] (https://secureframe.com/blog/cybersecurity-statistics)
- Understand the Importance and Objectives
- In 2026 organizational culture will define cybersecurity maturity (https://resilienceforward.com/in-2026-organizational-culture-will-define-cybersecurity-maturity)
- Get to Know the Cybersecurity Maturity Model Certification (https://gsa.gov/blog/2026/02/12/get-to-know-the-cybersecurity-maturity-model-certification)
- Understanding Cybersecurity Maturity Assessment In 2026 (https://gaminfo.com/cybersecurity-maturity-assessment)
- What a Year! Cybersecurity Recap and 2026 Forecast for Government Contractors | JD Supra (https://jdsupra.com/legalnews/what-a-year-cybersecurity-recap-and-9217321)
- 2026 Cybersecurity Outlook: A Maturity Reckoning (https://cybersecurity-insiders.com/2026-cybersecurity-outlook-a-maturity-reckoning)
- Follow the Step-by-Step Assessment Process
- Cybersecurity Maturity Assessment: 7 Step Framework – N-able (https://n-able.com/blog/cybersecurity-maturity-assessment)
- CMMC 2.0 in 2026: What’s New and What Organizations Must Know – Accorian (https://accorian.com/cmmc-2-0-in-2026-whats-new-and-what-organizations-must-know)
- Assessing Cybersecurity Maturity: How to Benchmark Your Defenses in 2026 (https://zeronetworks.com/blog/assessing-cybersecurity-maturity-how-to-benchmark-your-defenses-in-2026)
- Understanding Cybersecurity Maturity Assessment In 2026 (https://gaminfo.com/cybersecurity-maturity-assessment)
- Gartner Identifies the Top Cybersecurity Trends for 2026 (https://gartner.com/en/newsroom/press-releases/2026-02-05-gartner-identifies-the-top-cybersecurity-trends-for-2026)
- Utilize Tools and Resources for Effective Assessment
- Top 12 Cyber Security Risk Assessment Tools For 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-risk-assessment-tools)
- Top Cybersecurity Tools for 2026: The Age of Smart, Unified Defense (https://careerera.com/blog/top-cybersecurity-tools)
- Assessing Cybersecurity Maturity: How to Benchmark Your Defenses in 2026 (https://zeronetworks.com/blog/assessing-cybersecurity-maturity-how-to-benchmark-your-defenses-in-2026)
- Must-Have Cybersecurity Tools for 2026 (https://uscsinstitute.org/cybersecurity-insights/blog/must-have-cybersecurity-tools-for-2026)
- Cybersecurity Statistics 2025: Global Trends, Risks & Compliance Insights (https://sprinto.com/blog/list-of-cybersecurity-statistics)