Introduction
As cyber threats escalate, manufacturers face unprecedented challenges that demand immediate attention to security risk management. The stakes are high, with ransomware attacks resulting in losses exceeding millions, while operational disruptions jeopardize both financial stability and corporate reputation. This article outlines ten essential security risk management services designed specifically for manufacturers, highlighting how these strategies can strengthen defenses in a complex digital environment.
What specific challenges hinder manufacturers from implementing these critical measures, and what strategies can they adopt to protect their operations in a competitive landscape?
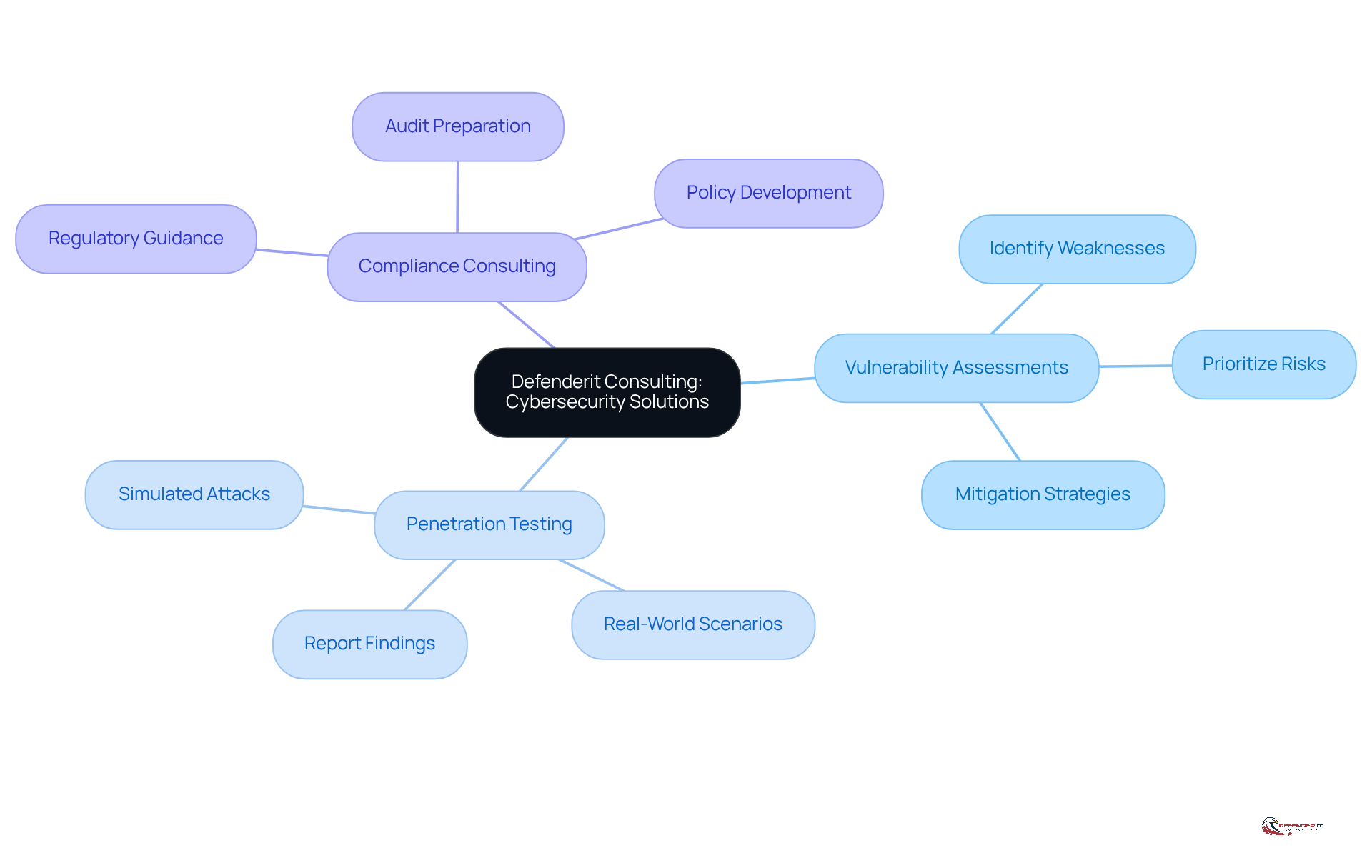
Defenderit Consulting: Comprehensive Cybersecurity Solutions
Producers are increasingly vulnerable to digital threats, necessitating tailored cybersecurity solutions to safeguard their operations. Defenderit Consulting focuses on providing customized security risk management services and cybersecurity solutions that tackle the specific challenges encountered by producers. With a focus on protecting digital assets, the firm offers a range of services including:
With their expertise, producers can effectively navigate the complex landscape of digital risks while maintaining operational integrity and compliance with industry regulations.
In 2026, the manufacturing sector faces substantial digital risks. Ransomware assaults are viewed as the most urgent peril. According to Siemens research, the average total cost of a ransomware incident in manufacturing reached approximately $8.7 million in 2024. Furthermore, 40% of reported operational technology (OT) incidents have caused disruptions, significantly higher than the industry target of less than 10%. Failure to implement robust cybersecurity measures could lead to devastating financial losses and reputational damage. By utilizing Defenderit Consulting’s expertise in security risk management services, producers can effectively manage the intricacies of digital risks while addressing stringent compliance challenges, ultimately safeguarding their operations and reputation. Without proactive measures, producers risk not only their financial stability but also their standing in a competitive market.
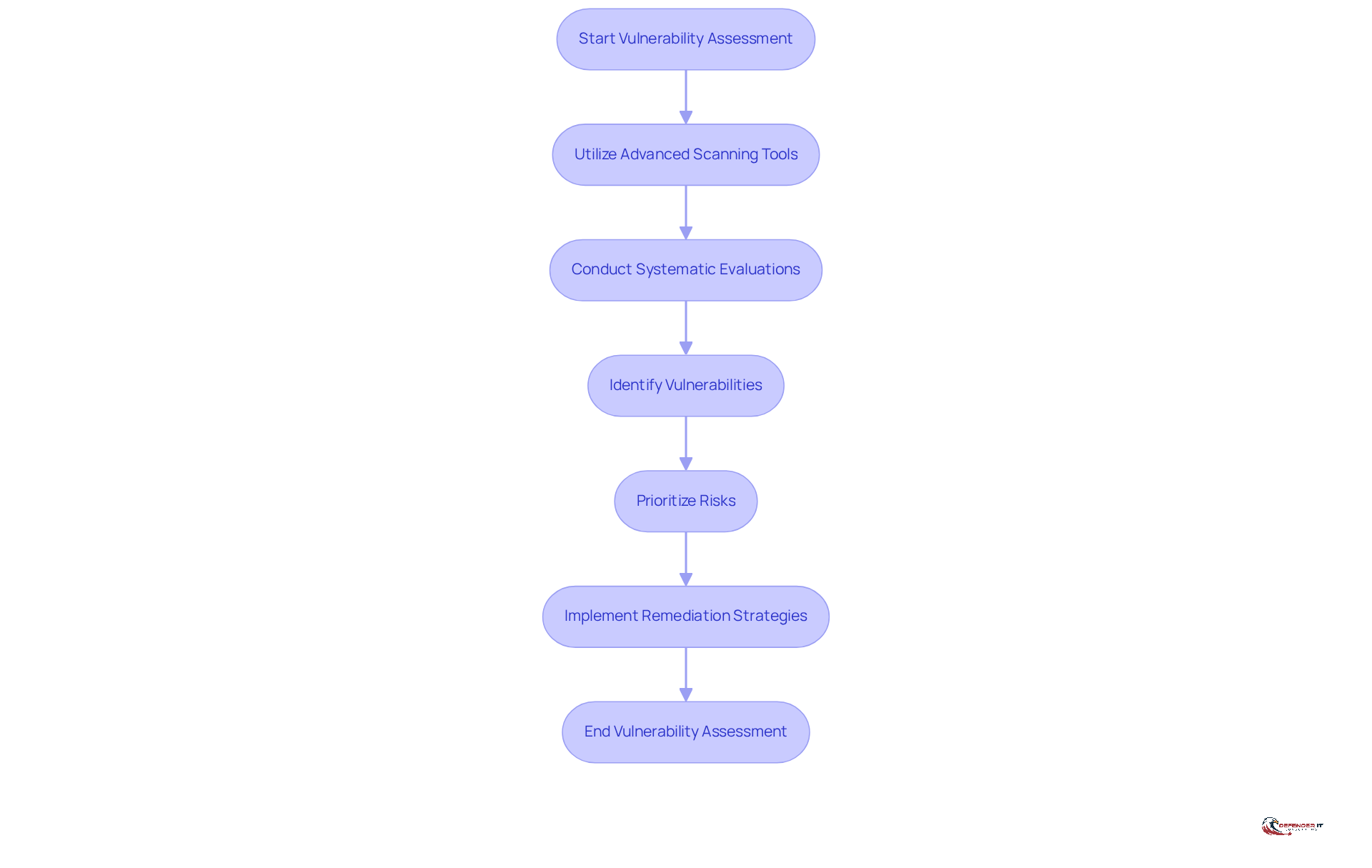
Vulnerability Assessments: Identifying Security Weaknesses
Producers face significant challenges in safeguarding their IT infrastructure against evolving digital threats. Vulnerability assessments are crucial, involving systematic evaluations to uncover potential security weaknesses. By utilizing advanced scanning tools and methodologies, organizations can identify vulnerabilities and prioritize risks for effective remediation.
In 2026, more than 40,000 vulnerabilities were recognized in 2024, indicating the industry’s increased susceptibility to digital risks. Regular evaluations not only help producers stay ahead of emerging threats, such as debilitating targeted cyberattacks, but also strengthen their systems against potential cyber attacks. The ongoing talent shortage complicates the implementation of robust cybersecurity measures.
This proactive approach not only mitigates risks but also enhances overall operational resilience. Ultimately, a robust vulnerability assessment strategy is essential for maintaining operational integrity and trust in an increasingly perilous digital landscape.
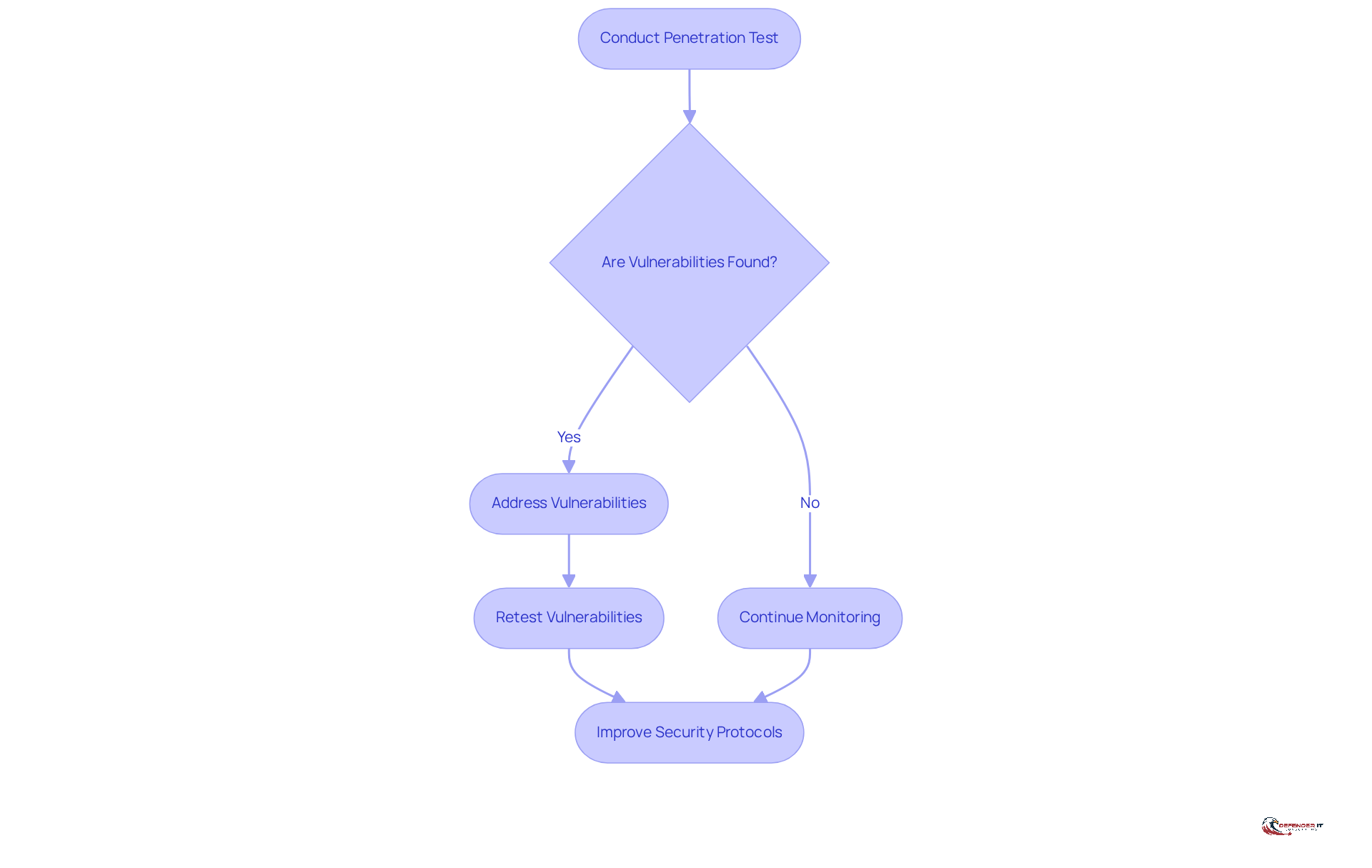
Penetration Testing: Simulating Attacks to Strengthen Security
Penetration testing is essential for identifying and addressing vulnerabilities in a producer’s systems before they can be exploited by cybercriminals. This proactive strategy enables organizations to uncover exploitable vulnerabilities, mitigating risks posed by malicious actors. In 2026, routine penetration tests proved crucial, with 84% of engagements revealing at least one exploitable vulnerability. This statistic underscores the essential need for producers to perform regular testing.
By implementing these tests, manufacturers not only strengthen their defenses but also align with compliance requirements, as many regulatory frameworks mandate regular testing. Moreover, organizations that performed penetration tests saved an average of $1.9 million per breach, highlighting the financial advantages of investing in proactive protective measures.
When manufacturers conduct successful penetration tests, they often see notable improvements in their security protocols, helping them stay resilient against evolving cyber threats. Additionally, establishing communication guidelines and escalation processes during penetration testing engagements is crucial for maximizing effectiveness. Retesting after vulnerabilities are addressed is essential to confirm that all issues have been resolved. Ultimately, neglecting penetration testing can result in severe financial repercussions and compromised security, making it a critical component of any robust cybersecurity strategy.
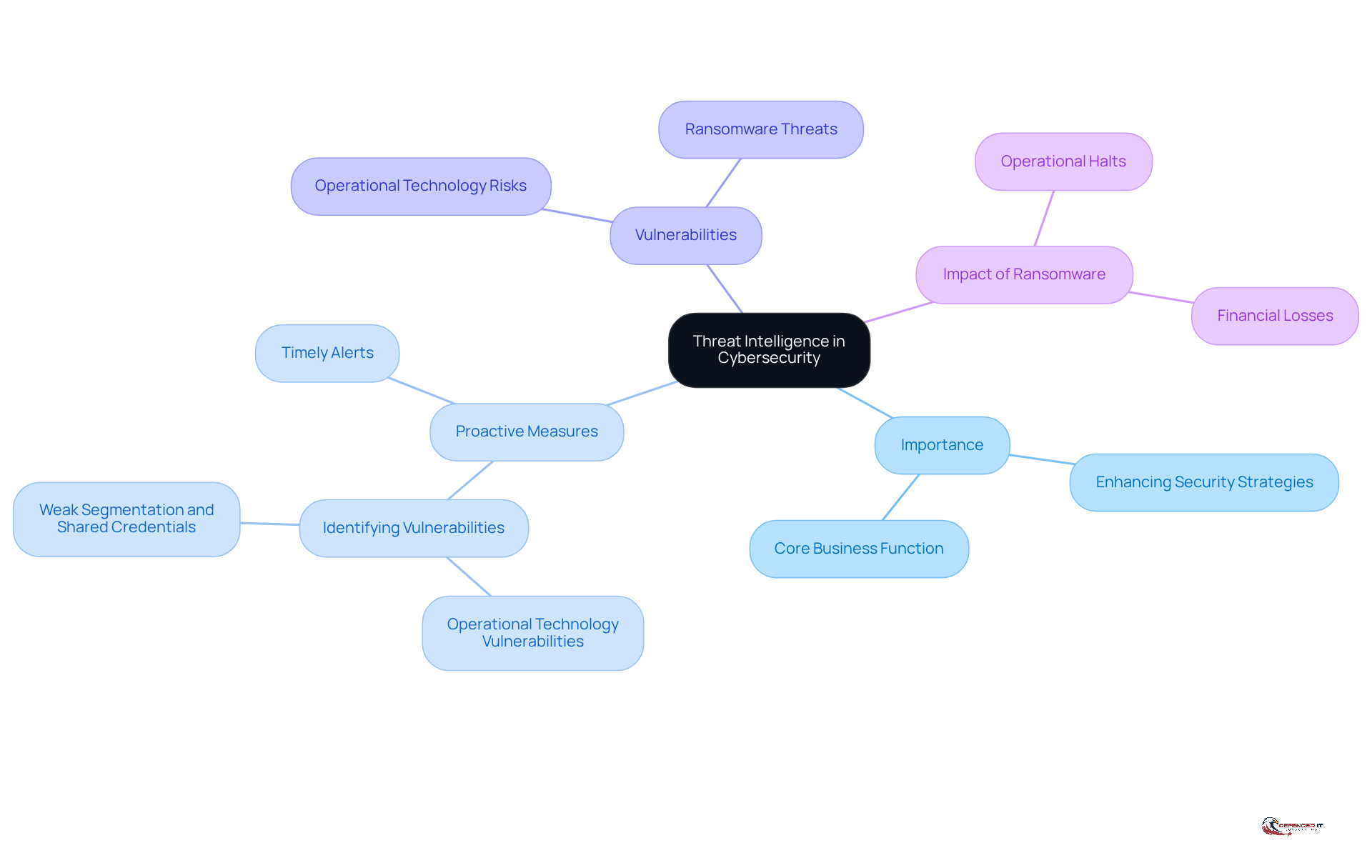
Threat Intelligence: Staying Ahead of Cyber Threats
In an era where cyber threats are increasingly sophisticated, threat intelligence has become indispensable for manufacturers navigating a perilous landscape. This systematic gathering and examination of information concerning potential cyber risks is essential for producers facing a dynamic environment of dangers. By effectively utilizing risk intelligence, manufacturers can gain valuable insights into emerging threats, allowing them to proactively implement preventive measures. For instance, organizations can utilize threat intelligence to identify vulnerabilities in their operational technology (OT) systems, which are increasingly targeted due to their critical role in production processes. This proactive approach not only enhances security strategies but also boosts resilience against digital threats.
Manufacturers face the risk of operational halts and significant financial losses due to ransomware attacks, which are recognized as the #1 cyber risk for manufacturing. Statistics indicate that these attacks can halt operations and lead to substantial financial losses, with costs potentially exceeding hundreds of thousands of dollars in lost revenue. This highlights the necessity for strong security risk management services capabilities. By incorporating risk intelligence into their cybersecurity systems, producers can more effectively foresee and reduce dangers, ensuring operational continuity and safety.
Furthermore, the effectiveness of intelligence in preventing cyber attacks is emphasized by its capacity to provide timely alerts about potential vulnerabilities and attack vectors. As producers increasingly depend on interconnected systems, comprehending the dynamics of these risks becomes essential. For instance, organizations that have adopted intelligence solutions report a significant enhancement in their capability to identify and react to incidents, thus minimizing downtime and protecting their reputation. A statement from industry specialists emphasizes that ‘cybersecurity is now a core business function, not a back-office IT activity,’ underscoring the essential role of risk intelligence in contemporary manufacturing.
As the landscape of cyber threats continues to evolve, producers must prioritize threat intelligence as a core component of their cybersecurity strategy. Without strong security intelligence, manufacturers risk severe operational disruptions, which can be mitigated by effective security risk management services. Prioritizing threat intelligence is not merely a defensive strategy; it is a proactive approach that can safeguard the future of manufacturing operations.
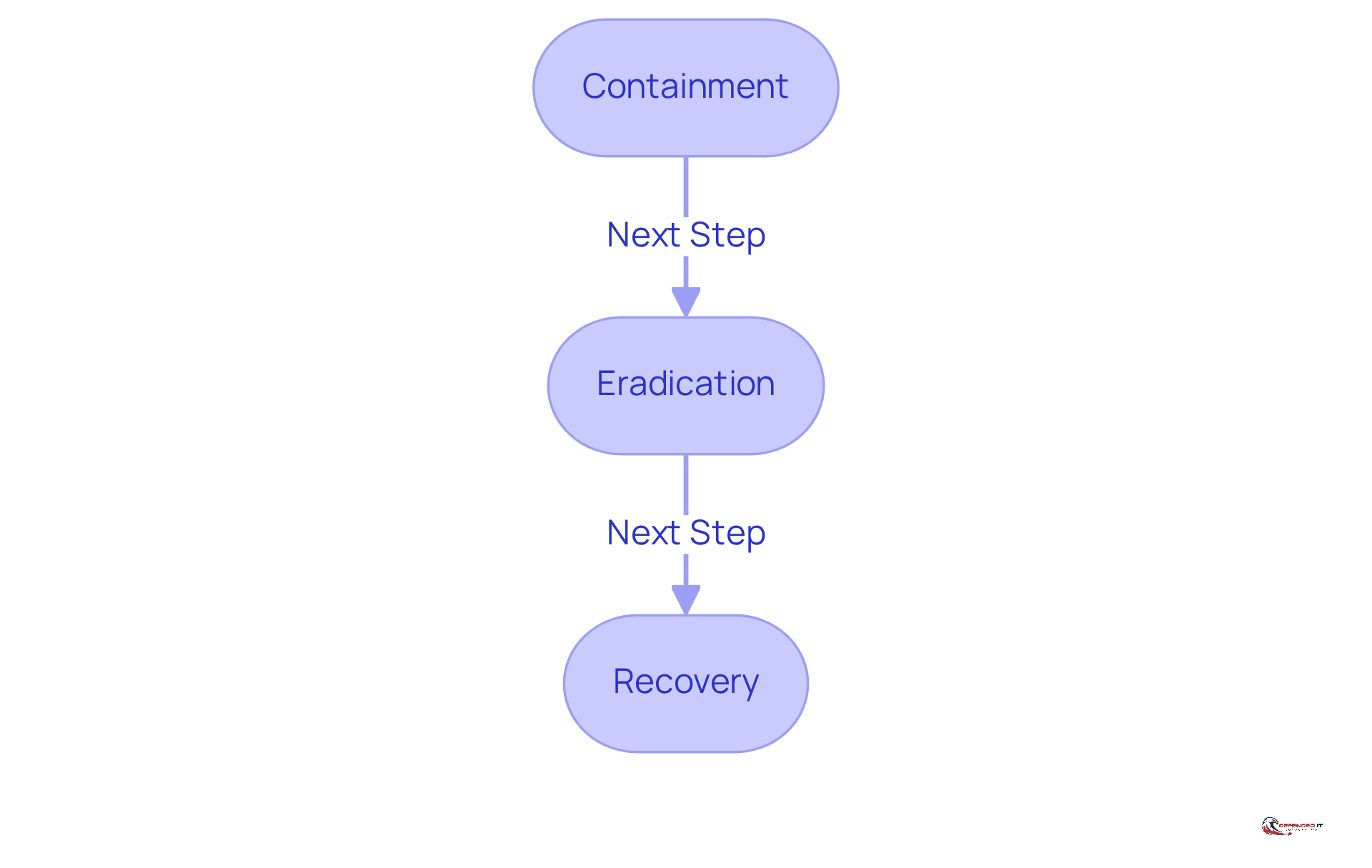
Incident Response: Effective Management of Security Breaches
In an era where cyber threats are increasingly prevalent, an effective incident response plan is essential for producers to navigate security breaches successfully. This plan delineates critical steps such as:
- Containment
- Eradication
- Recovery
Ensuring a structured approach to incident management. By preparing for potential incidents, producers can minimize damage, protect sensitive data, and ensure business continuity in the face of cyber threats. Ultimately, a robust incident response plan empowers producers to safeguard their operations and maintain trust with stakeholders.
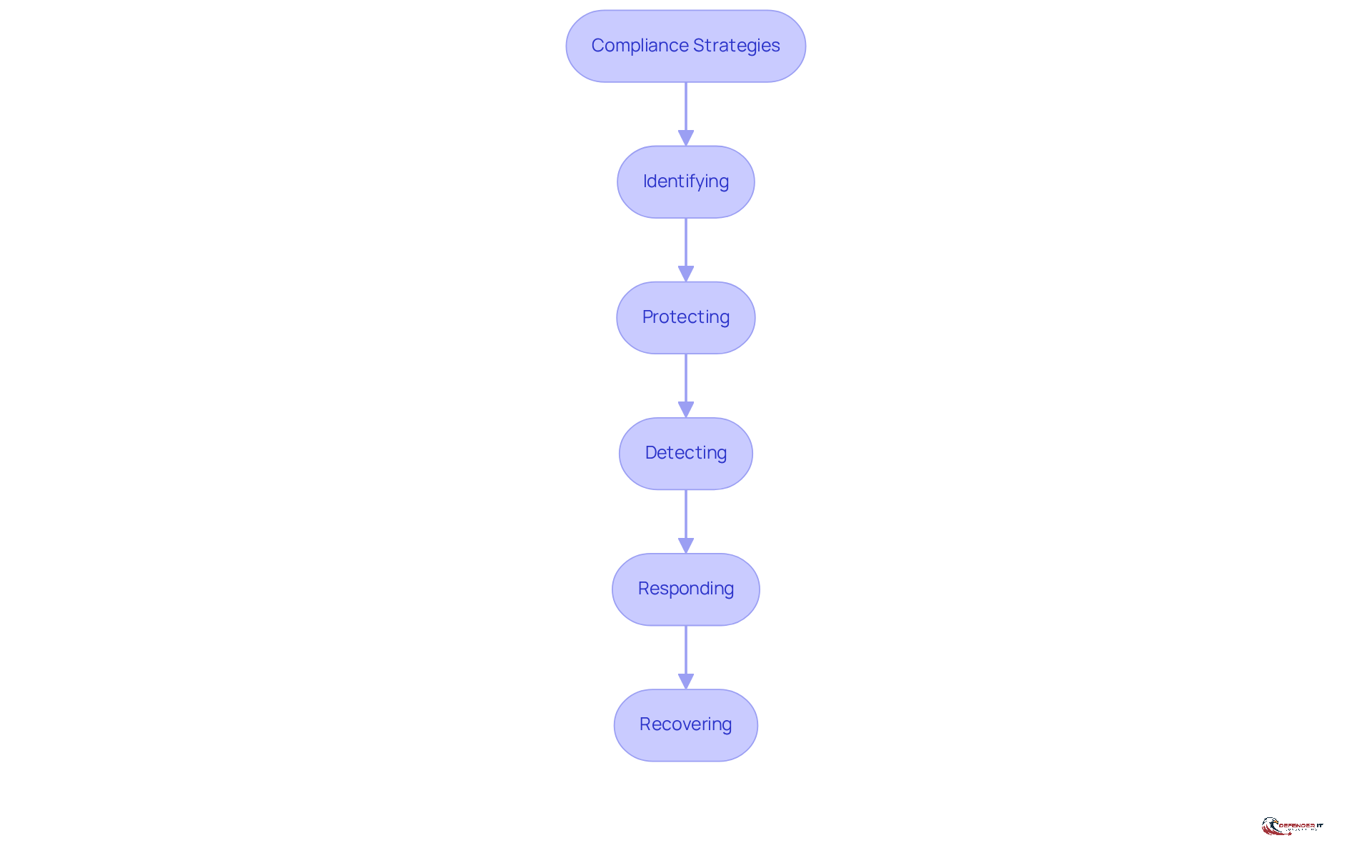
Compliance Consulting: Navigating Regulatory Requirements
Navigating the complex landscape of cybersecurity regulations is critical for producers, especially as compliance becomes increasingly stringent. In 2026, over 15% of producers are expected to face penalties for non-compliance, underscoring the urgency of adhering to these evolving standards. Engaging compliance consultants helps organizations avoid legal repercussions while enhancing their reputations. These specialists provide tailored advice on best practices, ensuring that producers implement necessary controls to safeguard sensitive data and maintain operational integrity.
Effective compliance strategies typically include comprehensive audits based on established frameworks. The NIST Cybersecurity Framework, for instance, highlights the critical steps of:
- Identifying
- Protecting
- Detecting
- Responding
- Recovering from cyber threats
Producers managing Controlled Unclassified Information (CUI) must implement all 110 NIST SP 800-171 controls. Furthermore, producers holding active DoD contracts must report incidents involving Covered Defense Information (CDI) within 72 hours. As regulatory oversight grows, the role of compliance consulting becomes ever more essential in assisting producers not only to fulfill legal requirements but also to improve their overall safety stance. As the regulatory landscape evolves, proactive compliance measures will not only safeguard data but also enhance organizational resilience against cyber threats.
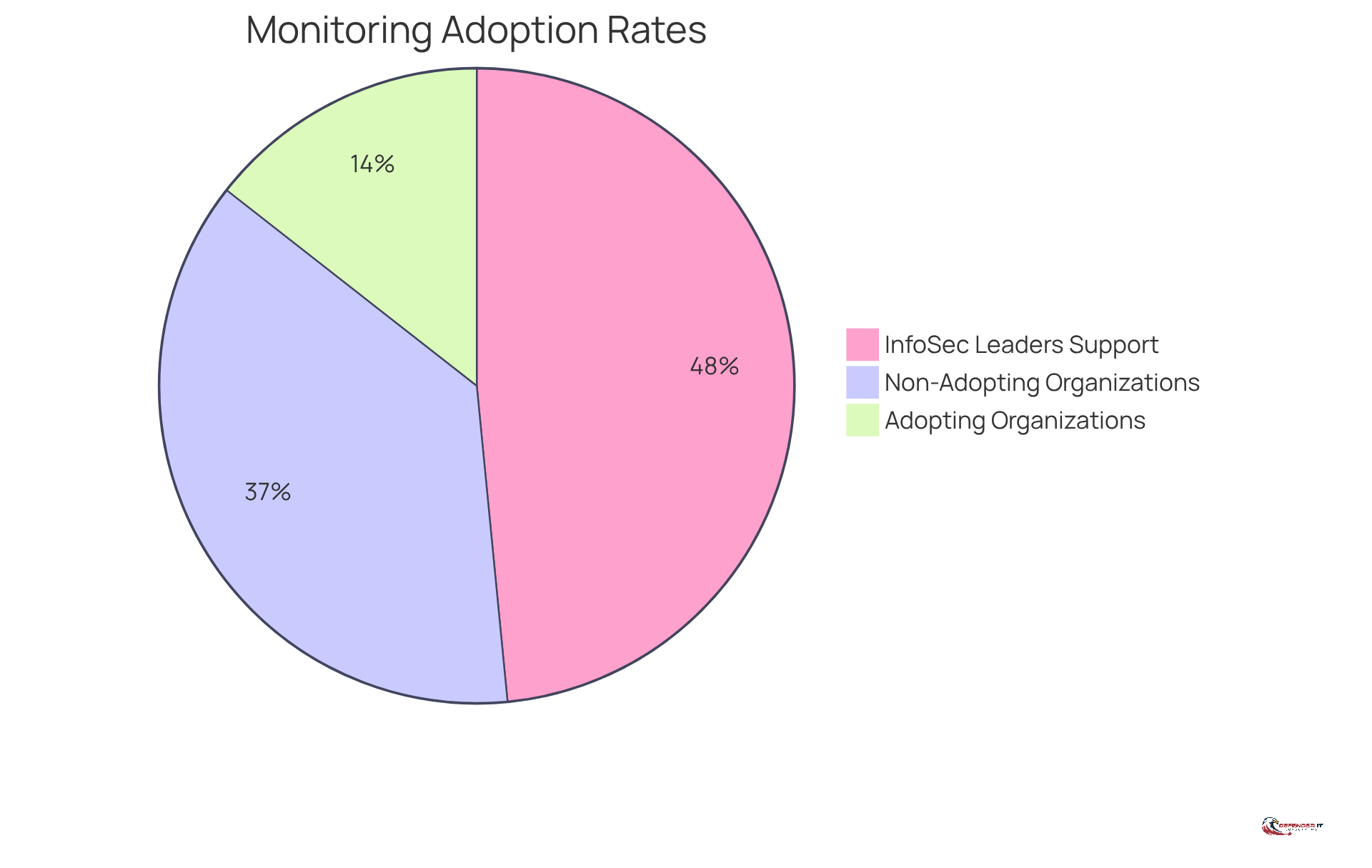
Continuous Monitoring: Adapting to Evolving Threats
Producers must prioritize constant observation to effectively manage risks in their IT environments. Constant observation is crucial for producers, involving the ongoing evaluation of IT environments to identify risks in real-time. By leveraging automated monitoring tools, organizations can swiftly identify vulnerabilities and respond to incidents as they occur. This proactive approach strengthens protections against emerging cyber risks. It also significantly improves the overall safety stance of manufacturing operations.
In 2026, 28% of organizations are expected to implement continuous monitoring solutions, reflecting a growing recognition of its importance. According to InfoSec leaders, “94% of InfoSec leaders said that Continuous Controls Monitoring will improve both compliance and security for 2025.” Organizations embracing these solutions have reported greater resilience and improved incident response, highlighting the effectiveness of real-time hazard detection.
Despite the benefits, producers encounter significant hurdles in adopting continuous monitoring solutions, such as resource limitations and resistance to change. Failure to overcome these obstacles could hinder the effectiveness of their monitoring efforts. As they face growing digital risks, the capacity to observe and react to dangers in real-time is becoming an essential part of their protection strategies.
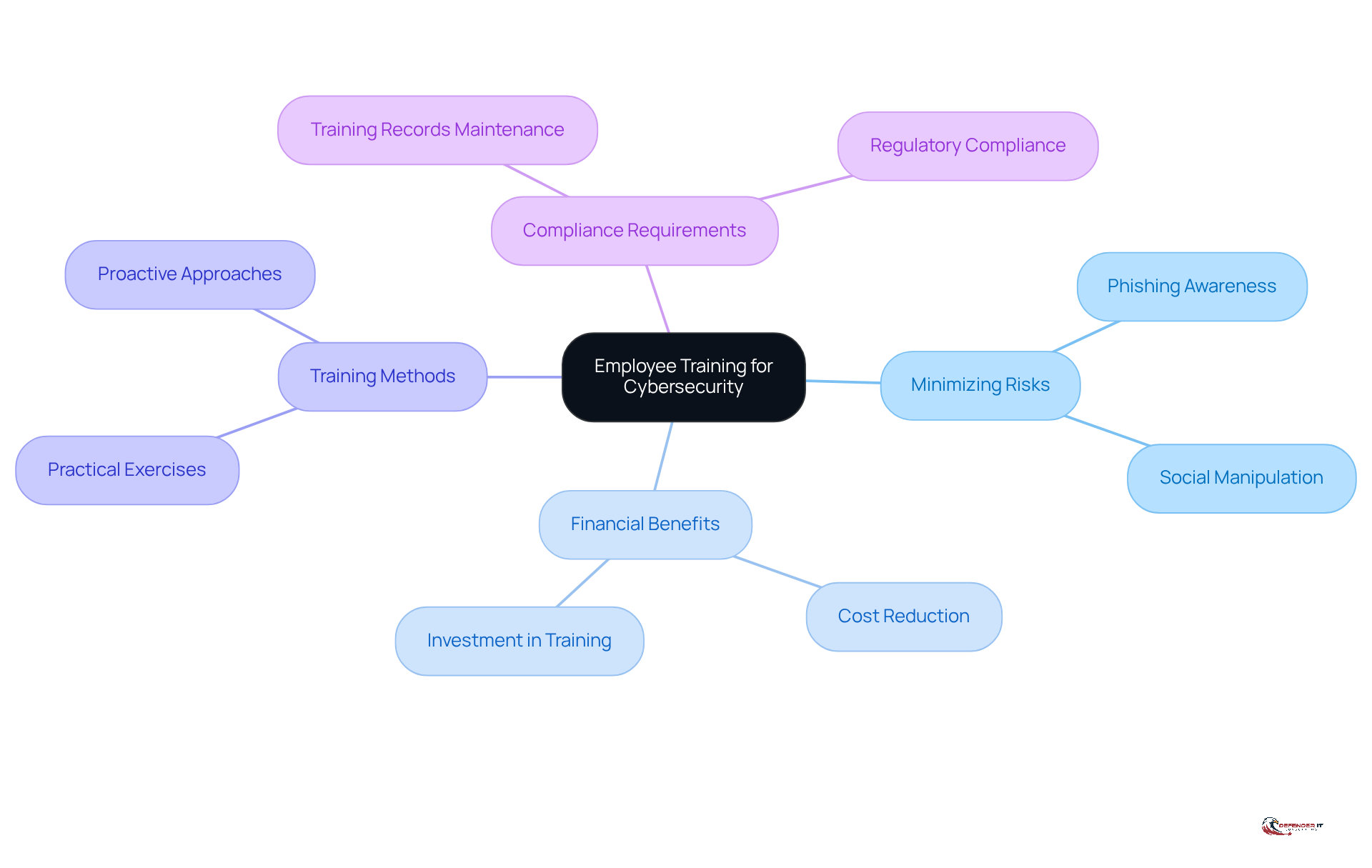
Employee Training: Empowering Staff to Enhance Security
Employee training is essential for minimizing cybersecurity risks in manufacturing environments. Informing employees about common online threats, like phishing and social manipulation, significantly reduces the chances of human error. Frequent training sessions enable employees to identify and respond to potential risks, fostering a culture of security awareness within the organization.
By 2026, 59% of organizations are expected to prioritize cybersecurity concerns, reflecting a significant shift in focus. Furthermore, the average cost of a data breach is projected to decrease to $4.4 million due to faster detection and containment, highlighting the financial advantages of investing in employee training. Additionally, 56% of organizations plan to enhance their workforce training to address skill gaps, indicating a broader trend in prioritizing cybersecurity education.
Manufacturing cybersecurity training programs frequently incorporate practical exercises that mimic real-world scenarios, allowing employees to practice their responses to cyber incidents. By fostering a proactive approach to cybersecurity, producers can significantly enhance their resilience against evolving threats and protect their operational integrity.
As Anna Ribeiro, an Industrial Cyber News Editor, notes, “Personnel who cannot receive cybersecurity training may access IT and/or OT systems only if they are physically accompanied or monitored by trained personnel.” This underscores the essential requirement for thorough training to ensure compliance with regulations. Without comprehensive training, organizations risk exposing themselves to significant vulnerabilities that could jeopardize their operational integrity.
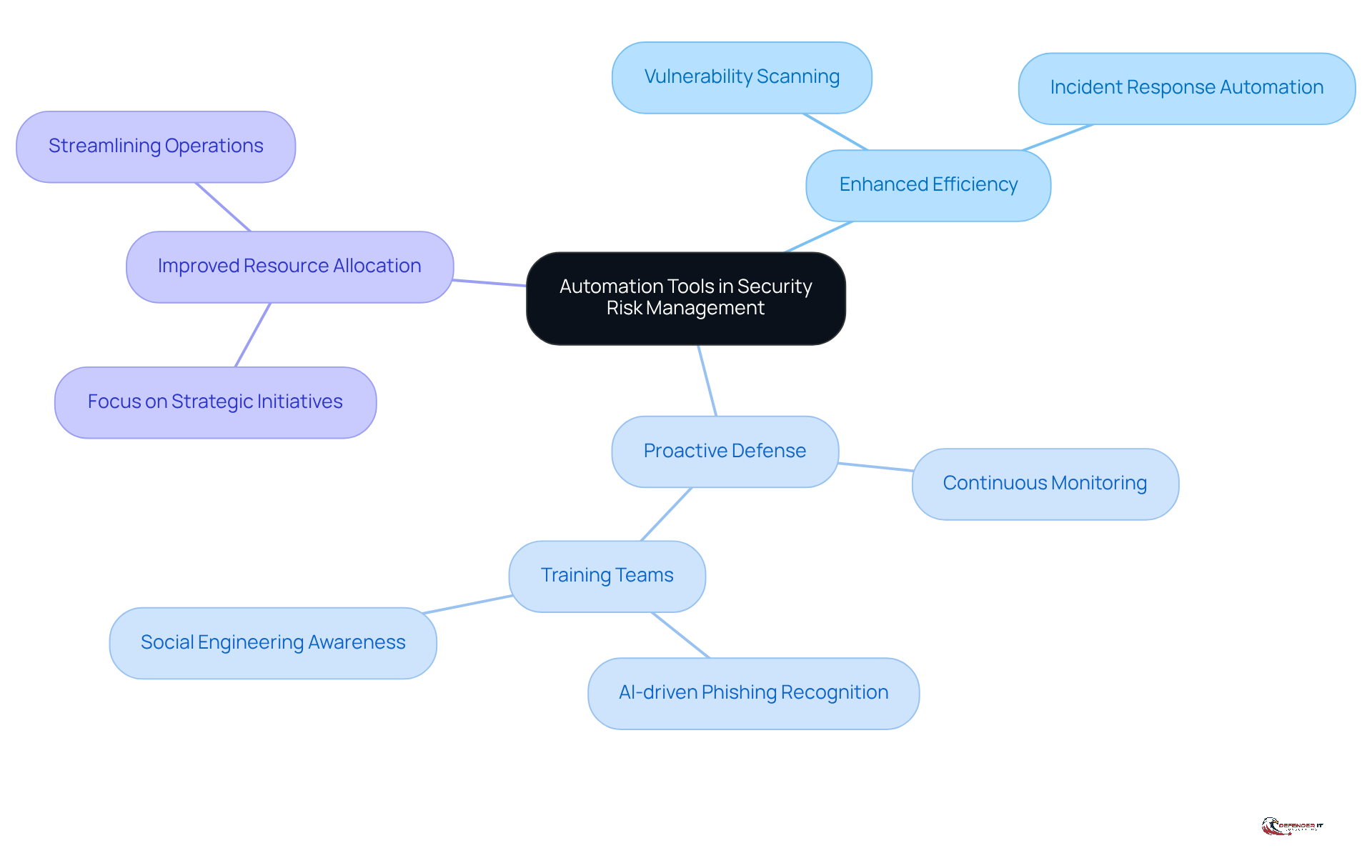
Automation Tools: Streamlining Security Risk Management
In an era where ransomware attacks on manufacturers have surged by 87% year-over-year, automation tools have become indispensable for enhancing security risk management services. By automating routine tasks such as vulnerability scanning and incident response, organizations can significantly improve efficiency and minimize human error. Continuous monitoring tools can identify anomalies in real-time, enabling swift containment of risks. As Gene Whaley notes, monitoring IoT assets and supply-chain partners in real time is essential to catch anomalies before they disrupt operations. Automation streamlines operations and frees up resources for strategic initiatives, ensuring essential measures like maintaining a clear inventory of assets are consistently enforced. Additionally, incorporating automation into security risk management services helps manufacturers stay ahead of emerging cyber threats, protecting both their operations and reputation in a digital-first world. By 2026, the adoption of automated solutions is expected to provide a competitive advantage, transforming cybersecurity into a strategic asset. Key benefits include:
- Enhanced efficiency in risk management
- Proactive defense against cyber threats
- Improved resource allocation for strategic initiatives
Moreover, training teams to identify AI-driven phishing and social engineering attacks is essential, further improving the effectiveness of automated protective measures.
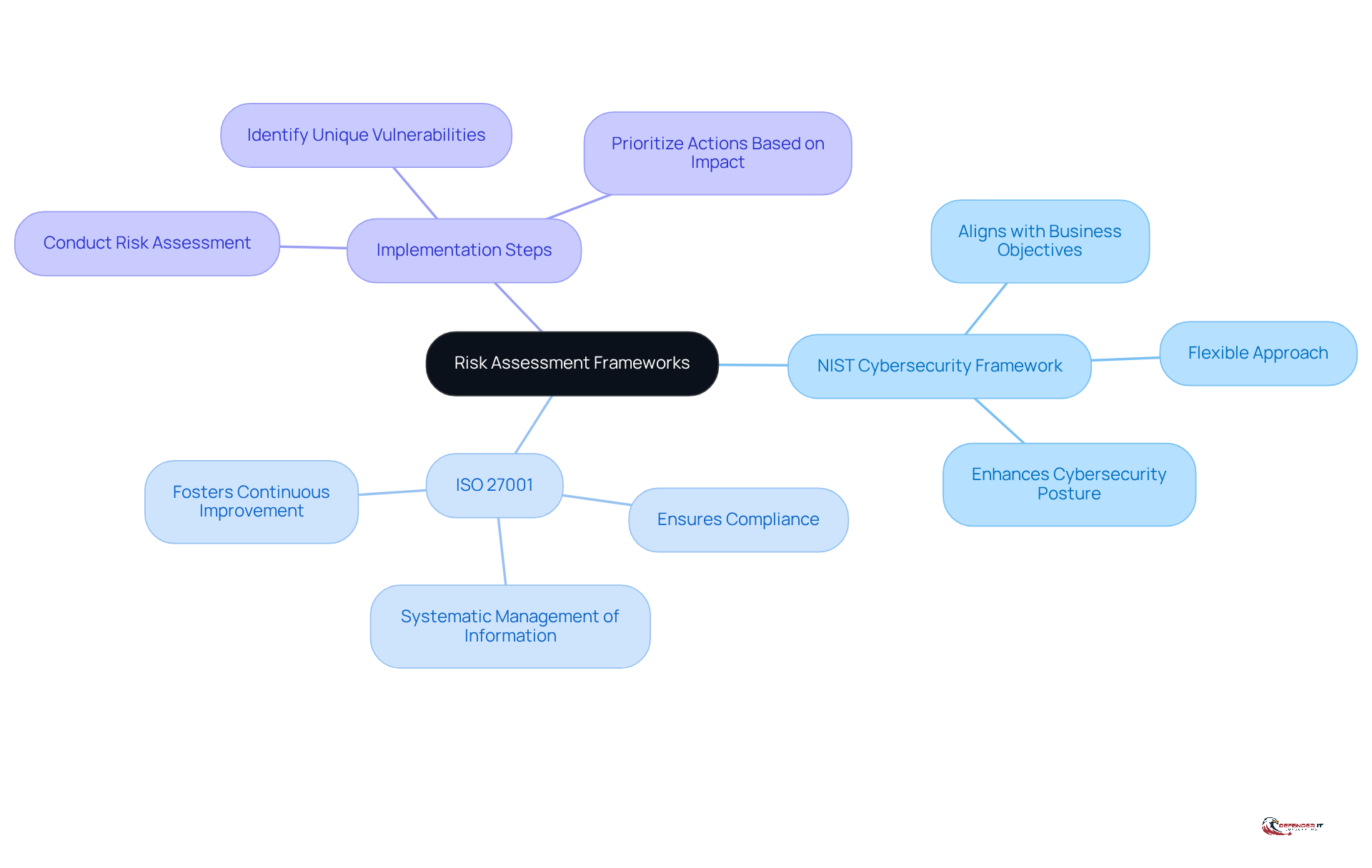
Risk Assessment Frameworks: Structuring Security Management
Producers face increasing threats in cybersecurity, making security risk management services essential for effective risk assessment frameworks. By adopting frameworks such as NIST and ISO standards, organizations can create a comprehensive strategy for security risk management services that not only assesses vulnerabilities but also prioritizes risks based on their potential impact. These frameworks provide a structured approach for producers to develop effective strategies that enhance their cybersecurity posture.
For instance, the NIST Cybersecurity Framework offers a flexible approach that aligns with business objectives, while ISO 27001 provides a systematic way to manage sensitive information, ensuring compliance with regulatory requirements. Implementing these standards not only strengthens security measures but also fosters a culture of continuous improvement in risk management practices, ultimately leading to greater resilience against cyber threats through effective security risk management services.
Given that manufacturing absorbs nearly 20% of cyber attacks, the need for robust cybersecurity measures is critical to prevent operational disruptions. To begin implementing these frameworks, manufacturers must conduct a thorough risk assessment to identify their unique vulnerabilities and prioritize actions based on the potential impact on their operations.
Conclusion
In an era marked by escalating digital threats, manufacturers must recognize the critical need for comprehensive security risk management services. The manufacturing sector faces unprecedented challenges from cyber attacks, necessitating proactive measures to safeguard operations and maintain a competitive edge. By leveraging tailored cybersecurity solutions, manufacturers can effectively mitigate risks and ensure operational integrity.
This article highlights several critical components of a robust security risk management strategy, including:
- Vulnerability assessments
- Penetration testing
- Threat intelligence
- Continuous monitoring
Each of these services plays a vital role in identifying weaknesses, preparing for potential incidents, and staying ahead of emerging threats. Furthermore, compliance consulting and employee training are essential elements for navigating regulatory landscapes and fostering a culture of cybersecurity awareness within organizations.
Ultimately, manufacturers are urged to prioritize their cybersecurity efforts by integrating these essential services into their operational frameworks. By doing so, they not only protect their assets and reputation but also contribute to a more resilient manufacturing industry capable of thriving amidst evolving digital challenges. Manufacturers must act decisively; embracing comprehensive security risk management is essential for safeguarding their future.
Frequently Asked Questions
What services does Defenderit Consulting provide to producers?
Defenderit Consulting offers customized security risk management services and cybersecurity solutions, including vulnerability assessments, penetration testing, and compliance consulting, specifically designed to tackle the challenges faced by producers.
Why are producers particularly vulnerable to digital threats?
Producers are increasingly vulnerable due to the rise of digital risks, such as ransomware attacks, which pose significant threats to their operations. The manufacturing sector faces substantial digital risks, with ransomware incidents costing an average of approximately $8.7 million in 2024.
What is the importance of vulnerability assessments for producers?
Vulnerability assessments are crucial for identifying potential security weaknesses in IT infrastructure. They involve systematic evaluations using advanced scanning tools to uncover vulnerabilities, helping producers prioritize risks and strengthen their systems against cyber threats.
How many vulnerabilities were recognized in the industry in 2024?
In 2024, more than 40,000 vulnerabilities were recognized, indicating an increased susceptibility to digital risks in the manufacturing sector.
What role does penetration testing play in cybersecurity for producers?
Penetration testing simulates attacks to identify and address vulnerabilities in a producer’s systems before they can be exploited. It is essential for strengthening defenses and aligning with compliance requirements, as many regulatory frameworks mandate regular testing.
What percentage of penetration testing engagements revealed exploitable vulnerabilities in 2026?
In 2026, 84% of penetration testing engagements revealed at least one exploitable vulnerability, highlighting the necessity of regular testing for producers.
What financial benefits can producers gain from conducting penetration tests?
Organizations that performed penetration tests saved an average of $1.9 million per breach, demonstrating the financial advantages of investing in proactive cybersecurity measures.
What are the consequences of neglecting penetration testing?
Neglecting penetration testing can lead to severe financial repercussions and compromised security, making it a critical component of a robust cybersecurity strategy for producers.
How can producers enhance their operational resilience against cyber threats?
By implementing regular vulnerability assessments and penetration testing, producers can mitigate risks, strengthen their security protocols, and maintain operational integrity in an increasingly perilous digital landscape.
List of Sources
- Defenderit Consulting: Comprehensive Cybersecurity Solutions
- consilien.com (https://consilien.com/news/cybersecurity-threats-facing-manufacturers-in-2026)
- Manufacturing Cyber Attack Statistics 2026: Data-Driven Insights on Industrial Security Threats (https://totalassure.com/blog/manufacturing-cyber-attack-statistics-2026-data-driven-insights-on-industrial-security-threats)
- 7 Key Manufacturing Cybersecurity Trends for 2026 | Huntress (https://huntress.com/blog/manufacturing-cybersecurity-trends)
- 2026 Will Be a Breakthrough Year for Cyberthreats: Four Predictions for Manufacturers (https://ien.com/redzone/blog/22958566/2026-will-be-a-breakthrough-year-for-cyberthreats-four-predictions-for-manufacturers)
- Cybersecurity 2026: AI, CISA, manufacturing sector all in the hot seat (https://cybersecuritydive.com/news/cyber-trends-outlook-2026/810708)
- Vulnerability Assessments: Identifying Security Weaknesses
- New Resilience Report Spotlights Manufacturing Cyberattack Severity and Ways to Reduce Cyber Risk (https://prnewswire.com/news-releases/new-resilience-report-spotlights-manufacturing-cyberattack-severity-and-ways-to-reduce-cyber-risk-302755350.html)
- Cybersecurity 2026: AI, CISA, manufacturing sector all in the hot seat (https://cybersecuritydive.com/news/cyber-trends-outlook-2026/810708)
- 7 Key Manufacturing Cybersecurity Trends for 2026 | Huntress (https://huntress.com/blog/manufacturing-cybersecurity-trends)
- Why manufacturing companies are most vulnerable to hacking | IBM (https://ibm.com/think/news/x-force-threat-intelligence-index-manufacturing-most-vulnerable-hacking)
- Ultimate Guide to Vulnerability Assessment: What, Why & How (2026 Edition) (https://acronis.com/en/blog/posts/ultimate-guide-to-vulnerability-assessment-2026)
- Penetration Testing: Simulating Attacks to Strengthen Security
- Why Penetration Testing is Important for Your Business in 2026 (https://brightdefense.com/resources/why-penetration-testing-is-important)
- 2026 Will Be a Breakthrough Year for Cyberthreats: Four Predictions for Manufacturers (https://ien.com/redzone/blog/22958566/2026-will-be-a-breakthrough-year-for-cyberthreats-four-predictions-for-manufacturers)
- Penetration Testing Requirement: What U.S. Rules Mandate It in 2026? (https://halock.com/penetration-testing-requirement-what-u-s-rules-mandate-it-in-2026)
- The 2026 State of Pentesting: How Modern Teams Manage and Deliver Results (https://thehackernews.com/expert-insights/2026/01/the-2026-state-of-pentesting-how-modern.html)
- Threat Intelligence: Staying Ahead of Cyber Threats
- consilien.com (https://consilien.com/news/cybersecurity-threats-facing-manufacturers-in-2026)
- 2026 Will Be a Breakthrough Year for Cyberthreats: Four Predictions for Manufacturers (https://ien.com/redzone/blog/22958566/2026-will-be-a-breakthrough-year-for-cyberthreats-four-predictions-for-manufacturers)
- Cybersecurity 2026: AI, CISA, manufacturing sector all in the hot seat (https://cybersecuritydive.com/news/cyber-trends-outlook-2026/810708)
- 7 Key Manufacturing Cybersecurity Trends for 2026 | Huntress (https://huntress.com/blog/manufacturing-cybersecurity-trends)
- New Resilience Report Spotlights Manufacturing Cyberattack Severity and Ways to Reduce Cyber Risk (https://prnewswire.com/news-releases/new-resilience-report-spotlights-manufacturing-cyberattack-severity-and-ways-to-reduce-cyber-risk-302755350.html)
- Incident Response: Effective Management of Security Breaches
- Mandatory Cyber Incident Reporting Arrives in 2026: What It Means for Businesses and How to Prepare – Device Authority (https://deviceauthority.com/mandatory-cyber-incident-reporting-arrives-in-2026-what-it-means-for-businesses-and-how-to-prepare)
- 7 Key Manufacturing Cybersecurity Trends for 2026 | Huntress (https://huntress.com/blog/manufacturing-cybersecurity-trends)
- Incident Response in 2026: A Complete Enterprise Guide (https://uscsinstitute.org/cybersecurity-insights/resources/incident-response-in-2026-a-complete-enterprise-guide)
- paloaltonetworks.com (https://paloaltonetworks.com/resources/research/unit-42-incident-response-report)
- 73% of CISOs Unprepared for the Next Big Cyber Attack, Incident Response Readiness Report Reveals (https://finance.yahoo.com/sectors/technology/articles/73-cisos-unprepared-next-big-120000695.html)
- Compliance Consulting: Navigating Regulatory Requirements
- 2026 Corporate Compliance, Litigation Outlook for Manufacturers » CBIA (https://cbia.com/news/manufacturing/2026-corporate-compliance-litigation-outlook-manufacturing)
- Navigating the 2026 FDA Cybersecurity Landscape: Lessons from the “Top Deficiencies”2026 FDA Cybersecurity Compliance: Avoiding Common Premarket Deficiencies (https://medcrypt.com/blog/navigating-the-2026-fda-cybersecurity-landscape-lessons-from-the-top-deficiencies)
- decyphertech.com (https://decyphertech.com/the-new-rules-of-manufacturing-cybersecurity-what-to-know-in-2026)
- What’s Trending in Compliance? March 2026 (https://complianceandrisks.com/blog/whats-trending-in-compliance-march-2026)
- Product Cybersecurity Regulations in 2026: Understanding the Global Compliance Shift (https://complianceandrisks.com/blog/product-cybersecurity-regulations-understanding-the-global-compliance-shift)
- Continuous Monitoring: Adapting to Evolving Threats
- 2026 State of Continuous Controls Monitoring Report | RegScale (https://regscale.com/resource-center/state-of-continuous-controls-monitoring-report)
- 2026 Will Be a Breakthrough Year for Cyberthreats: Four Predictions for Manufacturers (https://ien.com/redzone/blog/22958566/2026-will-be-a-breakthrough-year-for-cyberthreats-four-predictions-for-manufacturers)
- Cybersecurity 2026: AI, CISA, manufacturing sector all in the hot seat (https://cybersecuritydive.com/news/cyber-trends-outlook-2026/810708)
- telos.com (https://telos.com/blog/2026/04/14/continuous-monitoring-in-highly-regulated-industries-best-practices)
- Cyber threats to watch in 2026 – and other cybersecurity news (https://weforum.org/stories/2026/02/2026-cyberthreats-to-watch-and-other-cybersecurity-news)
- Employee Training: Empowering Staff to Enhance Security
- 2026 Will Be a Breakthrough Year for Cyberthreats: Four Predictions for Manufacturers (https://ien.com/redzone/blog/22958566/2026-will-be-a-breakthrough-year-for-cyberthreats-four-predictions-for-manufacturers)
- Cybersecurity 2026: AI, CISA, manufacturing sector all in the hot seat (https://cybersecuritydive.com/news/cyber-trends-outlook-2026/810708)
- Why Cybersecurity Training is the Smartest Investment for Organization in 2026 (https://uscsinstitute.org/cybersecurity-insights/blog/why-cybersecurity-training-is-the-smartest-investment-for-organization-in-2026)
- US Coast Guard mandates cybersecurity training for personnel with IT, OT access by January 2026 – Industrial Cyber (https://industrialcyber.co/training-development/ics-cyber-security-training/us-coast-guard-mandates-cybersecurity-training-for-personnel-with-it-ot-access-by-january-2026)
- Small Manufacturers at Risk: Boost Cybersecurity with Employee Training and Firewalls | TXI posted on the topic | LinkedIn (https://linkedin.com/posts/txidigital_cybersecurity-activity-7444468167747465216–HQc)
- Automation Tools: Streamlining Security Risk Management
- Cyber Threats in Smart Manufacturing | 2026 Outlook (https://keystonecorp.com/manufacturing/how-are-cyber-threats-evolving-in-smart-manufacturing)
- 7 Key Manufacturing Cybersecurity Trends for 2026 | Huntress (https://huntress.com/blog/manufacturing-cybersecurity-trends)
- 2026 Will Be a Breakthrough Year for Cyberthreats: Four Predictions for Manufacturers (https://ien.com/redzone/blog/22958566/2026-will-be-a-breakthrough-year-for-cyberthreats-four-predictions-for-manufacturers)
- 10 Hot New Cybersecurity Tools Announced At RSAC 2026 (https://crn.com/news/security/2026/10-hot-new-cybersecurity-tools-announced-at-rsac-2026)
- Risk Assessment Frameworks: Structuring Security Management
- What’s Old is New Again – 2026 Presents New and Enduring Challenges in Risk Assessment (https://navex.com/en-us/blog/article/whats-old-is-new-2026-presents-new-enduring-challenges-risk-assessment)
- Risk and Compliance in 2026: Six Key Themes Shaping Enforcement and Regulatory Scrutiny | Insights | Ropes & Gray LLP (https://ropesgray.com/en/insights/viewpoints/102me46/risk-and-compliance-in-2026-six-key-themes-shaping-enforcement-and-regulatory-sc)
- Manufacturing Cybersecurity – Standards, Regulation and Compliance – Industrial Cyber (https://industrialcyber.co/expert/manufacturing-cybersecurity-standards-regulation-and-compliance)
- Manufacturing Industry Trends 2026 (https://slalom.com/us/en/insights/manufacturing-outlook-2026)
- Stronger Cybersecurity, Stronger Business: NIST Celebrates 2026 National Small Business Week (https://nist.gov/blogs/cybersecurity-insights/stronger-cybersecurity-stronger-business-nist-celebrates-2026-national)