Introduction
Understanding the complexities of NIST 800-171 is essential for organizations aiming to protect Controlled Unclassified Information (CUI) and ensure compliance in a highly regulated environment. Mastering the 110 security requirements outlined in this framework not only strengthens cybersecurity measures but also enhances competitive positioning for federal contracts. However, the journey to compliance presents significant challenges.
How can organizations effectively implement these controls to mitigate risks and safeguard sensitive data?
Understand NIST 800-171 and Its Importance for Compliance
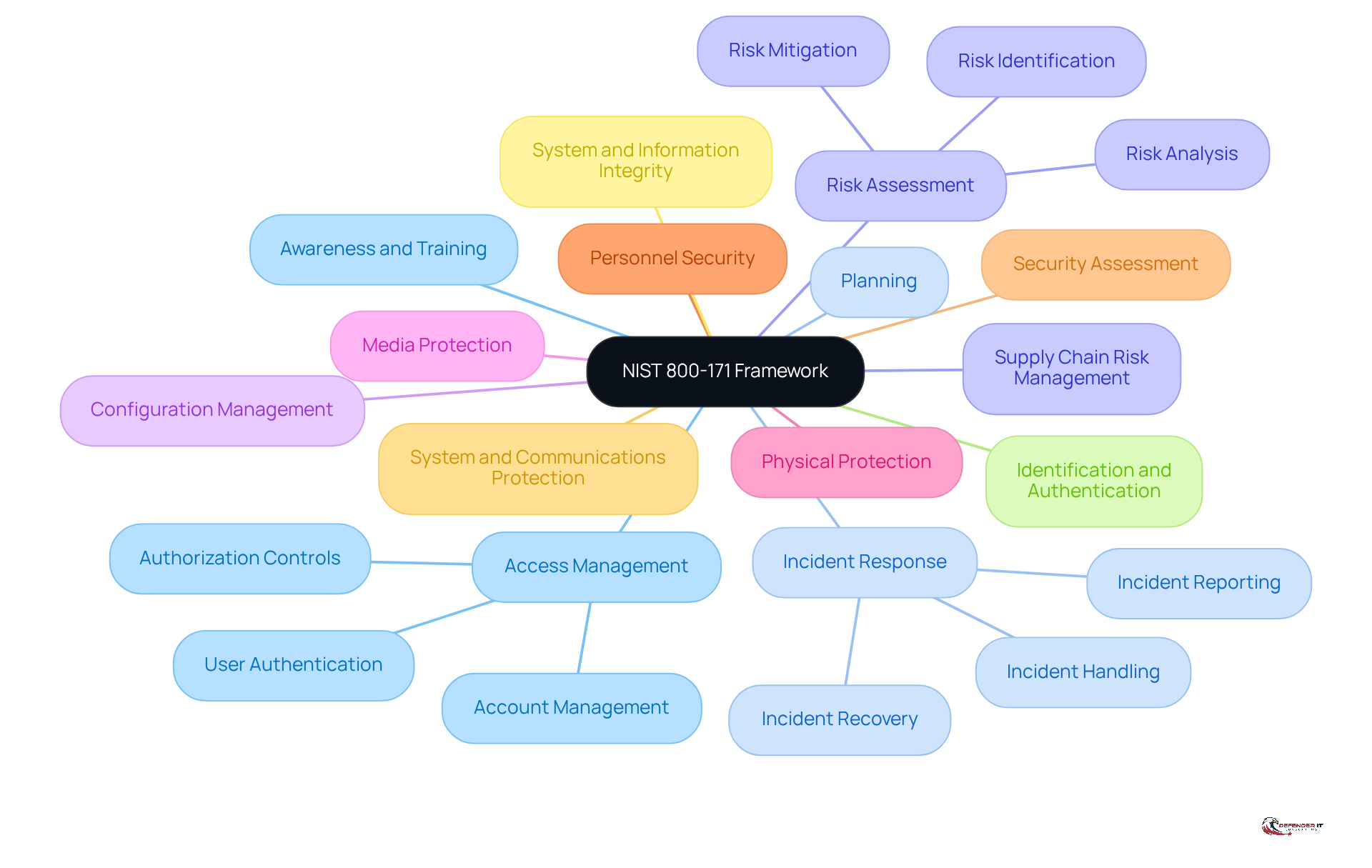
The NIST 800 171 controls serve as a vital framework established by the National Institute of Standards and Technology (NIST) to safeguard Controlled Unclassified Information (CUI) within non-federal systems. This framework delineates 110 security requirements organized into 14 categories, including:
- Access Management
- Incident Response
- Risk Assessment
Understanding the NIST 800 171 controls is essential for organizations, especially in sectors like finance and healthcare, where data breaches can result in [significant financial losses and damage to reputation](https://forbes.com/sites/emilsayegh/2026/02/07/a-quiet-policy-shift-just-redefined-entire-federal-cybersecurity-landscape). Compliance with the NIST 800 171 controls not only aids organizations in securing sensitive information but also positions them favorably for contracts with federal agencies, as adherence to these controls is often a prerequisite for engaging in business with the government.
By mastering the NIST 800 171 controls, organizations can significantly [enhance their cybersecurity posture](https://defenderit.consulting/master-medical-device-security-assessment-in-4-simple-steps/) and ensure compliance with regulatory requirements.
Identify and Implement NIST 800-171 Control Families
To achieve adherence to the NIST 800 171 controls, organizations must first recognize the relevant family of measures and implement the associated security requirements. The 14 control families are as follows:
- Access Control: Limit access to Controlled Unclassified Information (CUI) to authorized users only. This is critical, as failure to enforce access controls can lead to unauthorized data exposure. Cybersecurity specialists emphasize that implementing multi-factor authentication (MFA) is a best practice to enhance protection in this domain.
- Awareness and Training: Ensure all employees are educated on safety policies and procedures. Regular training mitigates risks associated with human error, often the weakest link in cybersecurity.
- Audit and Accountability: Implement logging and monitoring to track access and changes to CUI. This guarantees accountability and provides a path for forensic examination in the event of an incident.
- Configuration Management: Maintain secure configurations for information systems. Regular reviews and updates of configurations help prevent vulnerabilities from being exploited.
- Incident Response: Develop and implement an incident response plan. A well-defined plan enables organizations to respond swiftly to breaches, minimizing potential damage.
- Maintenance: Conduct routine upkeep on systems to ensure protection. This includes applying patches and updates to software and hardware components.
- Media Protection: Protect CUI stored on physical and digital media. Organizations must ensure that sensitive information is encrypted and securely stored.
- Physical Protection: Secure physical access to systems that process CUI. This involves establishing access controls to facilities and overseeing physical protection measures.
- Risk Assessment: Conduct regular risk assessments to identify vulnerabilities. Understanding possible threats enables organizations to prioritize their protective measures effectively.
- System and Communications Protection: Safeguard communications and data transmission. This includes using encryption protocols to protect data in transit.
- System and Information Integrity: Monitor systems for vulnerabilities and threats. Ongoing observation aids in identifying and addressing incidents proactively.
- Identification and Authentication: Ensure users are properly identified and authenticated. Implementing multi-factor authentication (MFA) is a best practice to improve protection.
- Planning: Create a strategy that details how measures will be applied. A comprehensive plan ensures that all aspects of safety are addressed systematically.
- Personnel Security: Ensure that personnel with access to CUI are trustworthy. Conducting background checks and implementing a structured screening process can help mitigate insider threats.
By methodically addressing each management category, organizations can establish a robust protective framework that not only fulfills regulatory needs but also enhances overall cybersecurity resilience. Current compliance rates with the NIST 800 171 controls vary across industries, highlighting the necessity for tailored approaches to meet specific regulatory demands. Organizations that effectively apply these measures frequently report enhanced protection levels and reduced risks linked to cyber threats. For instance, a recent case analysis revealed that a manufacturing company implementing these controls experienced a 40% decrease in incidents within the first year of execution. Furthermore, specialists underscore the importance of ongoing observation and routine updates to uphold regulations and adapt to evolving threats.
Conduct Comprehensive Security Assessments for NIST Compliance
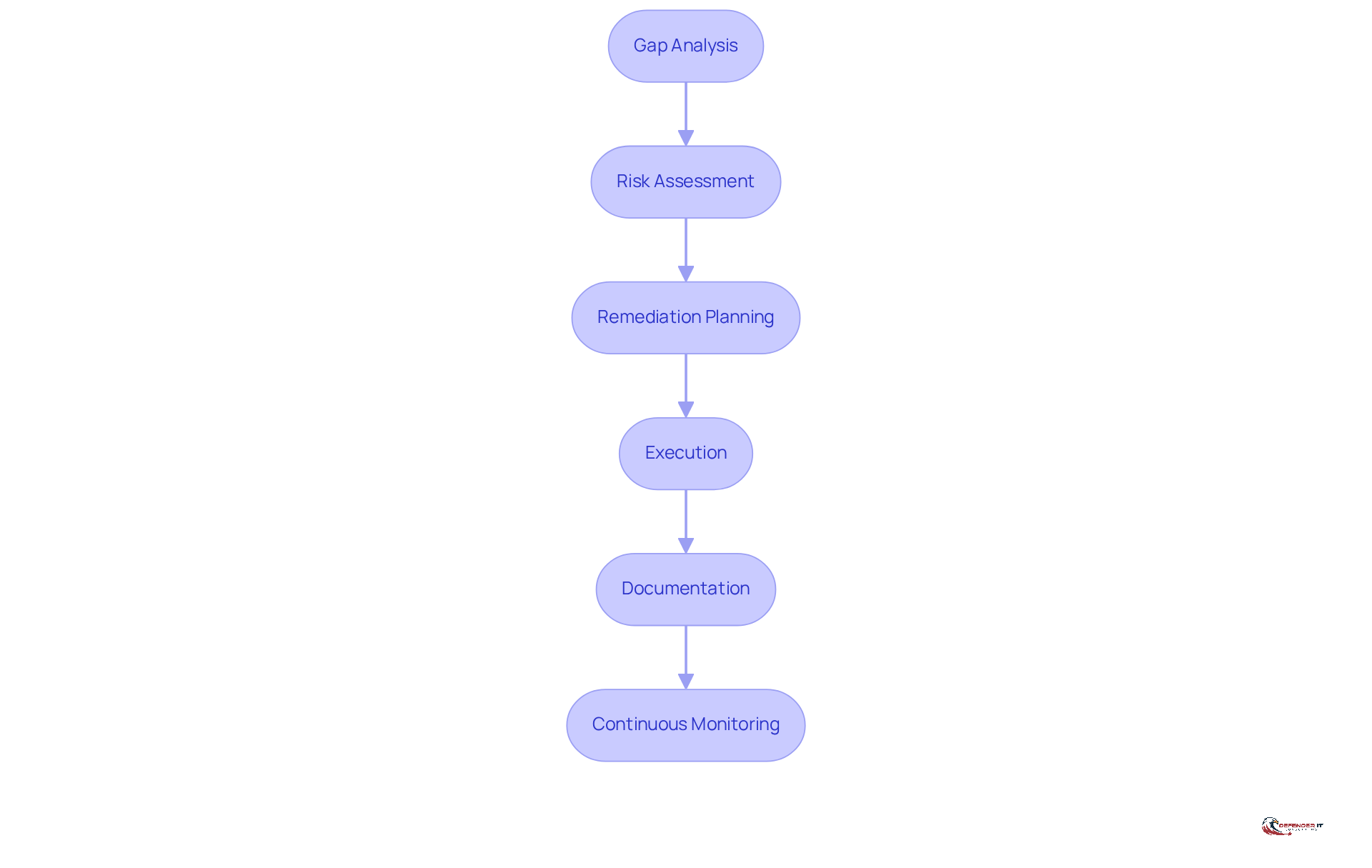
To achieve compliance with the NIST 800 171 controls, organizations must conduct thorough assessments regularly. This process includes several essential steps:
- Gap Analysis: The initial step involves comparing current protective practices against the NIST 800 171 controls to identify deficiencies. Organizations often discover common gaps, such as insufficient documentation of security measures and incomplete system boundary definitions during this analysis. Notably, VC3 clients are reported to be 70% towards compliance with NIST 800 171 controls on technical measures, providing a benchmark for entities evaluating their compliance status.
- Risk Assessment: After the gap analysis, organizations should assess the potential risks associated with the identified gaps. It is crucial to prioritize these risks based on their potential impact to facilitate effective remediation.
- Remediation Planning: Develop a comprehensive plan to address the identified gaps. This plan should outline specific timelines and designate responsible parties to ensure accountability.
- Execution: Implement the remediation strategy, ensuring that all essential protective measures are effectively established. This may involve adopting technologies such as FIPS 140-2 validated authenticators to enhance protective measures.
- Documentation: Maintain thorough documentation of all assessments, findings, and remediation efforts. This documentation is vital for demonstrating compliance and can be critical during audits.
- Continuous Monitoring: Establish a robust process for ongoing observation of security measures. This ensures that the controls remain effective over time and can adapt to evolving threats.
Given the recent agreements regarding contractors not meeting cybersecurity standards, as highlighted by Jerry Leishman, companies must recognize the urgency of adhering to regulations. By systematically performing these evaluations, entities not only achieve compliance with the NIST 800 171 controls but also strengthen their overall cybersecurity posture, thereby enhancing resilience against potential cyber threats. Regular assessments and updates are essential, as non-compliance can lead to significant financial and reputational damage.
Educate Employees on NIST 800-171 Compliance and Security Awareness
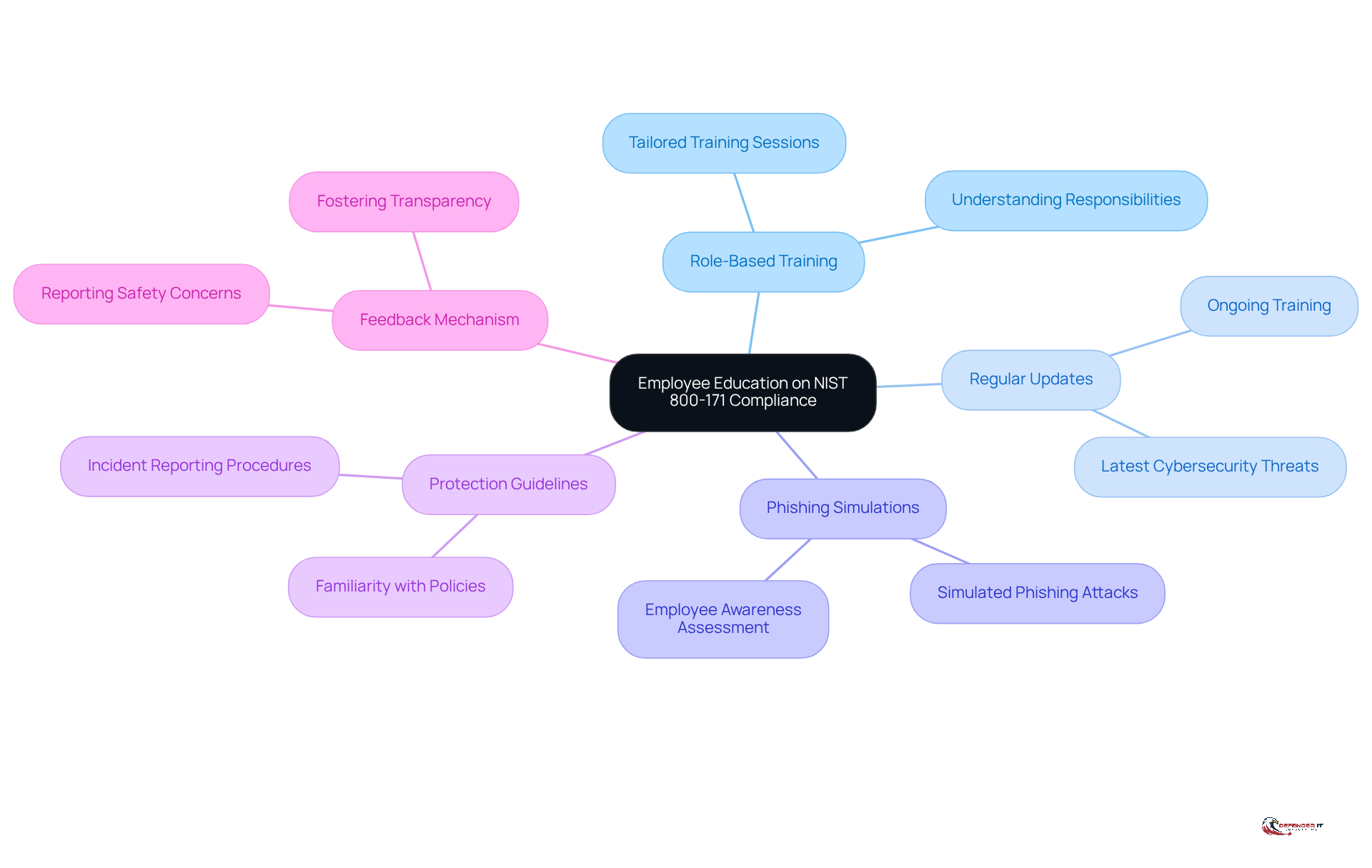
Employee education serves as a cornerstone for achieving NIST 800 171 controls compliance. Organizations must implement a comprehensive training program that encompasses several key components:
- Role-Based Training: Tailor training sessions to specific roles within the organization, ensuring employees understand their responsibilities regarding Controlled Unclassified Information (CUI).
- Regular Updates: Provide ongoing training to keep employees informed about the latest cybersecurity threats and best practices.
- Phishing Simulations: Conduct simulated phishing attacks to assess employee awareness and response to potential threats.
- Protection Guidelines: Ensure all staff are well-acquainted with the entity’s protection policies and procedures.
- Feedback Mechanism: Establish a system for employees to report safety concerns or incidents, fostering a culture of transparency and vigilance.
By prioritizing employee education, organizations can significantly mitigate the risk of human error, a leading cause of security breaches. A well-informed workforce is essential for maintaining compliance with the NIST 800 171 controls and safeguarding sensitive information.
Conclusion
Mastering the NIST 800-171 controls is not merely a regulatory obligation; it is a critical step in safeguarding Controlled Unclassified Information (CUI) and enhancing an organization’s overall cybersecurity posture. By understanding and implementing the 110 security requirements outlined in the NIST framework, organizations can effectively protect sensitive data while positioning themselves favorably for federal contracts. This proactive approach is essential in today’s landscape, where data breaches can lead to severe consequences.
The article emphasizes key practices for achieving compliance with NIST 800-171, including:
- Recognition of control families
- Conducting thorough security assessments
- Prioritizing employee education
Implementing access controls, performing regular risk assessments, and fostering a culture of security awareness are pivotal in mitigating risks associated with human error and cyber threats. Organizations that adopt these measures not only fulfill regulatory requirements but also significantly reduce their vulnerability to incidents, as demonstrated by success stories across various sectors.
Ultimately, the significance of NIST 800-171 compliance transcends mere adherence to regulations; it embodies a commitment to safeguarding sensitive information and enhancing organizational resilience against cyber threats. By prioritizing these best practices and fostering a culture of continuous improvement, organizations can achieve compliance while cultivating trust with clients and stakeholders. Taking decisive action today to master NIST 800-171 controls will pave the way for a more secure and compliant future.
Frequently Asked Questions
What is NIST 800-171?
NIST 800-171 is a framework established by the National Institute of Standards and Technology (NIST) that provides 110 security requirements for safeguarding Controlled Unclassified Information (CUI) within non-federal systems.
How many categories are the NIST 800-171 controls organized into?
The NIST 800-171 controls are organized into 14 categories.
What are some examples of categories included in NIST 800-171?
Examples of categories in NIST 800-171 include Access Management, Incident Response, and Risk Assessment.
Why is understanding NIST 800-171 important for organizations?
Understanding NIST 800-171 is crucial for organizations, particularly in sectors like finance and healthcare, as it helps secure sensitive information and prevents data breaches that can lead to financial losses and reputational damage.
How does compliance with NIST 800-171 benefit organizations?
Compliance with NIST 800-171 not only enhances an organization’s cybersecurity posture but also positions them favorably for federal contracts, as adherence to these controls is often a requirement for doing business with the government.
What is the overall goal of mastering the NIST 800-171 controls?
The overall goal of mastering the NIST 800-171 controls is to significantly improve cybersecurity measures and ensure compliance with regulatory requirements.
List of Sources
- Understand NIST 800-171 and Its Importance for Compliance
- NIST compliance in 2026: A complete implementation guide | UpGuard (https://upguard.com/blog/nist-compliance)
- A Quiet Policy Shift Just Redefined Entire Federal Cybersecurity Landscape (https://forbes.com/sites/emilsayegh/2026/02/07/a-quiet-policy-shift-just-redefined-entire-federal-cybersecurity-landscape)
- New GSA Guide Imposes Strict Cybersecurity Obligations on Government Contractors | Skadden, Arps, Slate, Meagher & Flom LLP (https://skadden.com/insights/publications/2026/03/new-gsa-guide-imposes-strict-cybersecurity-obligations-on-government-contractors)
- NIST 800-171 Compliance Guide for DoD Contractors (https://cmmcitsupport.us/nist-800-171-compliance-guide-for-dod-contractors-2026-update)
- #cmmc #cybersecurity #nist #compliance #defensecontracting #govcon | Agility Development Group (https://linkedin.com/posts/agility-development-group_cmmc-cybersecurity-nist-activity-7440486896868257792-o8Hd)
- Identify and Implement NIST 800-171 Control Families
- NIST compliance in 2026: A complete implementation guide | UpGuard (https://upguard.com/blog/nist-compliance)
- How to Meet GSA CUI Requirements | NIST 800-171 Guide (2026) (https://testpros.com/compliance/gsa-cui-compliance-guide-nist-requirements)
- GSA’s New CUI Requirements: What Government Contractors Need to Know | Insights | Holland & Knight (https://hklaw.com/en/insights/publications/2026/03/gsas-new-cui-security-requirements-what-government-contractors)
- How to Be NIST 800-171 Compliant: A Deep Dive for Defense Contractors (https://isidefense.com/blog/how-to-be-nist-800-171-compliant-defense-contractors)
- New GSA Guide Imposes Strict Cybersecurity Obligations on Government Contractors | Skadden, Arps, Slate, Meagher & Flom LLP (https://skadden.com/insights/publications/2026/03/new-gsa-guide-imposes-strict-cybersecurity-obligations-on-government-contractors)
- Conduct Comprehensive Security Assessments for NIST Compliance
- NIST 800-171 Compliance, Gap Analysis & Assessments | VC3 (https://vc3.com/services/compliance/nist-800-171-compliance)
- A Quiet Policy Shift Just Redefined Entire Federal Cybersecurity Landscape (https://forbes.com/sites/emilsayegh/2026/02/07/a-quiet-policy-shift-just-redefined-entire-federal-cybersecurity-landscape)
- How to Meet GSA CUI Requirements | NIST 800-171 Guide (2026) (https://testpros.com/compliance/gsa-cui-compliance-guide-nist-requirements)
- NIST compliance in 2026: A complete implementation guide | UpGuard (https://upguard.com/blog/nist-compliance)
- NIST 800-171 Compliance: How to Comply with the Latest Revision [+ Checklist] (https://secureframe.com/blog/nist-800-171-compliance)
- Educate Employees on NIST 800-171 Compliance and Security Awareness
- Cybersecurity Awareness Training for Employees in 2026 (https://uscsinstitute.org/cybersecurity-insights/resources/cybersecurity-awareness-training-for-employees-in-2026)
- Why Annual Security Training Isn’t Enough in 2026 | NINJIO (https://ninjio.com/blog/why-cisos-are-moving-beyond-annual-security-awareness-training)
- Effective Security Awareness Training | Elevate Cyber Defense in 2026 (https://trustcloud.ai/risk-management/how-effective-security-awareness-training-elevates-cybersecurity-in-your-organization)
- How to Implement a Role-Based Security Training Program to Meet NIST SP 800-171 REV.2 / CMMC 2.0 Level 2 – Control – AT.L2-3.2.2 (Step-by-Step Guide) (https://lakeridge.io/how-to-implement-a-role-based-security-training-program-to-meet-nist-sp-800-171-rev2-cmmc-20-level-2-control-atl2-322-step-by-step-guide)
- Why Cyber Security Awareness Training is Critical in 2026 (https://inspired-it.com.au/blog/why-cyber-security-awareness-training-is-critical-in-2026)