Introduction
In the manufacturing sector, the increasing frequency of cyberattacks presents a critical challenge for organizations. With recent statistics revealing that manufacturing has become the most targeted industry for cyberattacks, the need for effective penetration testing devices is paramount. This article outlines best practices for selecting effective penetration testing tools, enabling manufacturers to strengthen their security posture and mitigate risks.
With so many options available, how can organizations select the right devices to meet their specific needs and protect against evolving threats?
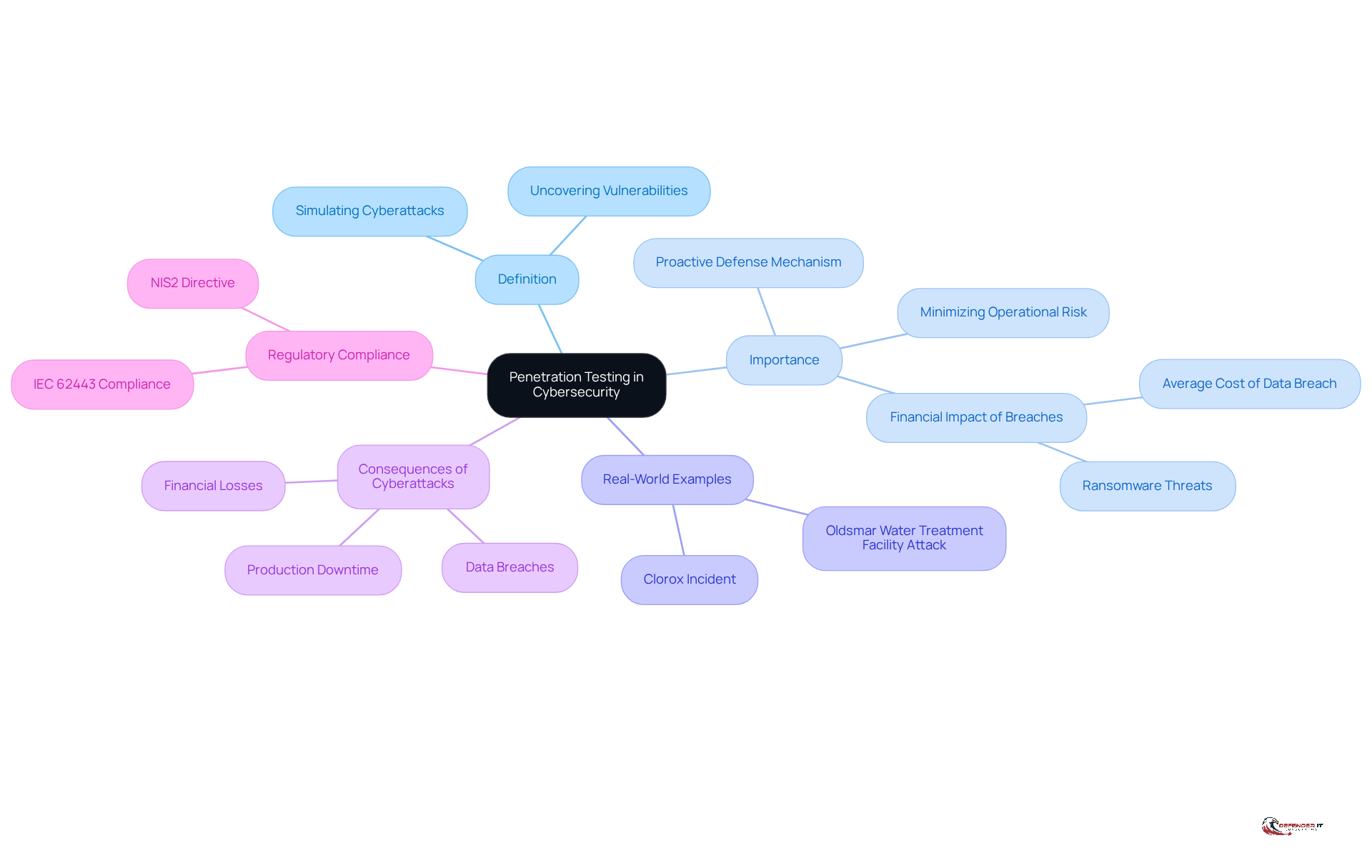
Define Penetration Testing and Its Importance in Cybersecurity
In an era where cyber threats are escalating, manufacturers have recognized that pen testing devices are a critical defense mechanism. Commonly referred to as ‘pen testing devices,’ this process involves simulating cyberattacks on computer systems, networks, or web applications to uncover vulnerabilities that malicious actors could exploit. In the manufacturing sector, where operational technology (OT) and information technology (IT) intersect, the implications of cyberattacks are particularly severe. Recent statistics indicate that manufacturing has become the most-attacked industry globally, surpassing finance, healthcare, and energy for three consecutive years. A successful cyberattack can result in significant production downtime, data breaches, and financial losses. The average cost of a data breach exceeds $4.44 million, and in the United States, this figure surpasses $10.22 million, underscoring the severe financial impact on manufacturers. Manufacturers frequently face pressure to pay ransoms swiftly to restore operations, which makes them attractive targets for ransomware attacks.
The impact of cyberattacks on manufacturing operations is profound. Disruptions can halt production lines, delay shipments, and jeopardize worker safety, leading to substantial revenue losses. For instance, an automotive assembly plant may lose hundreds of thousands of dollars for just one hour of downtime. This reality highlights the importance of security assessments, particularly through the use of pen testing devices, as a proactive approach to discover and address vulnerabilities before they can be exploited.
Consider real-world examples that highlight how security assessments play a vital role in protecting manufacturing assets:
- The 2021 Oldsmar water treatment facility attack, which took advantage of remote access weaknesses
- The 2023 Clorox incident, where compromised vendor credentials were utilized
These examples emphasize the urgent need for strong protective measures. Experts stress that security assessments not only reveal exploitable weaknesses but also assist organizations in prioritizing remediation actions, thus minimizing operational risk and improving overall security stance.
In conclusion, understanding the significance of penetration evaluation and the role of pen testing devices is essential for manufacturers aiming to safeguard their assets and maintain compliance with industry regulations, including the upcoming NIS2 Directive. Without a robust penetration evaluation strategy, manufacturers risk not only their assets but also their very operational viability in a competitive market.
Explore Types of Penetration Testing and Their Device Requirements
In the realm of manufacturing cybersecurity, penetration assessments play a critical role in identifying vulnerabilities and ensuring compliance with regulatory standards. Various methodologies exist, each tailored to specific environments and objectives. The primary types include:
- Black Box Testing: In this method, testers act like external attackers, diving in without any prior knowledge of the system. This approach is particularly useful for evaluating the overall safety stance and recognizing weaknesses that an outsider could exploit. According to the Cybersecurity Incident Reporting for Critical Infrastructure Act (CIRCIA), organizations must have documented protection programs with testing in place, making black box testing essential for compliance.
- White Box Testing: Here, testers possess complete knowledge of the system, allowing for a thorough examination of internal vulnerabilities. This method is ideal for uncovering weaknesses in proprietary systems and ensuring robust security measures are in place. Compliance frameworks such as PCI DSS and CMMC highlight the necessity for regular evaluations, which can be effectively addressed through white box methodologies.
- Gray Box Evaluation: This hybrid method merges aspects of both black and white box assessments, where evaluators have partial knowledge of the system. It allows for a balanced assessment, focusing on both external and internal threats, which is crucial for organizations looking to meet evolving compliance requirements.
- Network Penetration Testing: This type specifically targets weaknesses in network devices and configurations, crucial for maintaining the integrity of manufacturing operations. The NYDFS cybersecurity regulation clearly mandates annual penetration evaluations as part of its risk assessment, underscoring the significance of this methodology.
- Web Application Evaluation: Given the increasing reliance on online interfaces, this evaluation focuses on identifying vulnerabilities in web applications, which can be critical for manufacturers engaging with customers and suppliers online. Regular assessments are necessary to comply with standards like PCI DSS, which mandates testing for entities handling payment card data.
- Mobile Application Testing: This evaluates the safety of mobile applications utilized for operational management, ensuring that mobile interfaces do not introduce additional risks. As mobile applications become more prevalent, understanding their security posture is vital for compliance and risk management.
Different types of penetration evaluations require tailored methodologies and pen testing devices to effectively identify vulnerabilities. For instance, network tests often utilize vulnerability scanners, while web application assessments may require code analysis tools. Comprehending these requirements is crucial for manufacturers to choose the suitable tools that align with their particular assessment needs, thereby improving their cybersecurity posture. As noted by CyberGuard Advantage, “Our engagements emphasize scoping accuracy and reporting, ensuring that each test reflects realistic attack capabilities and produces findings that translate directly into a measurable reduction of risk.” Understanding the nuances of each penetration testing type is essential for manufacturers to effectively mitigate risks and enhance their cybersecurity frameworks by utilizing pen testing devices.
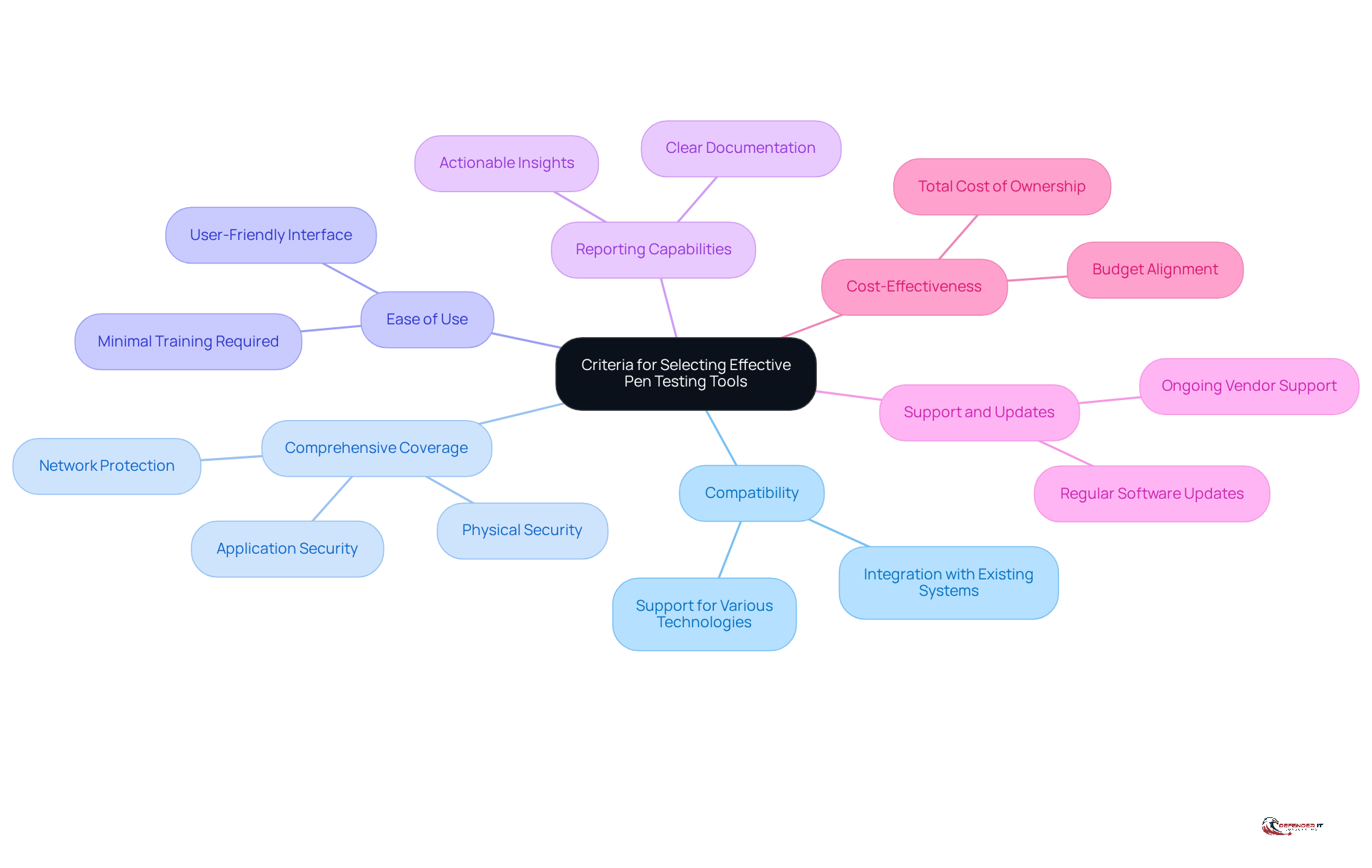
Establish Criteria for Selecting Effective Pen Testing Tools
In an era where cyber threats are increasingly sophisticated, manufacturers face the challenge of selecting the right pen testing devices to safeguard their operations. When selecting penetration testing tools, manufacturers should consider the following criteria:
- Compatibility: Ensure that the tools are compatible with existing systems and technologies used in the manufacturing environment.
- Comprehensive Coverage: Look for tools that provide extensive coverage across various attack vectors, including network, application, and physical protection.
- Ease of Use: Tools should be user-friendly, allowing security teams to operate them effectively without extensive training.
- Reporting Capabilities: Effective tools should generate clear, actionable reports that emphasize weaknesses and provide remediation guidance.
- Support and Updates: Choose tools from vendors that offer ongoing support and regular updates to address emerging threats.
- Cost-Effectiveness: Evaluate the total cost of ownership, including licensing, maintenance, and potential training costs, to ensure the investment aligns with the organization’s budget.
Without a structured approach to tool selection, manufacturers risk exposing their systems to significant vulnerabilities that could compromise their operations.
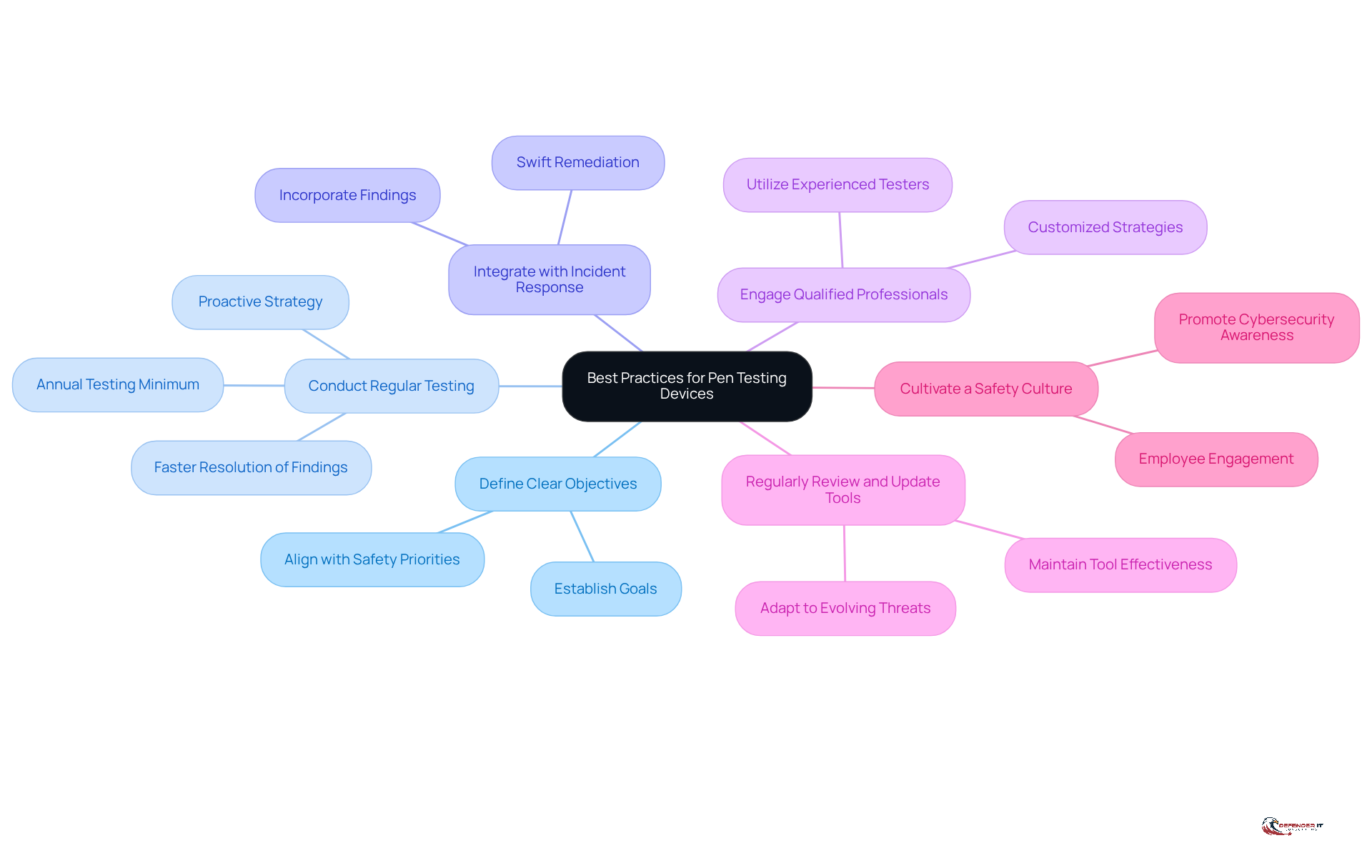
Implement Best Practices for Using Pen Testing Devices Effectively
To maximize the effectiveness of penetration testing devices, manufacturers must adopt a strategic approach that encompasses several best practices:
- Define Clear Objectives: Establishing clear goals and objectives before conducting tests is crucial. This guarantees that the evaluation process corresponds with organizational safety priorities and tackles specific weaknesses pertinent to the manufacturing environment.
- Conduct Regular Testing: Organizations that conduct tests at least annually resolve critical findings. The organization is evaluating the security of its systems using pen testing devices times faster-within three days or less-than those relying on ad-hoc teams. This proactive strategy greatly improves defenses against new threats and weaknesses.
- Integrate with Incident Response: Discoveries from security tests should be seamlessly incorporated into the incident response plan. This integration allows for swift remediation of identified vulnerabilities, ensuring that organizations can respond effectively to potential threats. Establishing a clear scope and objectives during security assessments is often a challenge for organizations, leading to incomplete evaluations and overlooked critical areas.
- Engage Qualified Professionals: Utilizing experienced penetration testers who understand the unique challenges of the manufacturing sector is vital. Their expertise can provide valuable insights and customized strategies that improve the effectiveness of evaluation efforts. As Gunter Ollmann states, “Security excellence is not a destination, but a continuous cycle of discovery and resolution.”
- Regularly Review and Update Tools: The organization is evaluating the security of its systems using pen testing devices. It’s crucial to regularly review and update pen testing devices to keep pace with evolving threats. As cyber threats become more sophisticated, manufacturers must adapt their tools and methodologies accordingly.
- Cultivate a Safety Culture: Promoting a culture of awareness regarding safety within the organization is essential. All employees should understand the importance of cybersecurity and their role in maintaining it, which can significantly bolster overall security efforts.
By adhering to these best practices, manufacturers not only strengthen their cybersecurity posture but also foster a proactive approach to emerging threats.
Conclusion
In the face of escalating cyber threats, the role of penetration testing devices in manufacturing operations is critical. These tools serve as a proactive measure, enabling manufacturers to identify and rectify vulnerabilities before they can be exploited by malicious actors. As the manufacturing sector continues to face unprecedented attacks, a strategic approach to selecting and utilizing pen testing devices is essential for maintaining operational integrity and compliance with industry standards.
The article outlined several key practices for choosing the right penetration testing tools, emphasizing the need for:
- Compatibility
- Comprehensive coverage
- Ease of use
- Robust reporting capabilities
Additionally, understanding the various types of penetration testing – such as black box, white box, and network testing – provides manufacturers with the insights necessary to tailor their cybersecurity strategies effectively. Regular testing, engaging qualified professionals, and fostering a culture of safety were also highlighted as best practices that can significantly enhance the overall security posture of manufacturing environments.
Manufacturers must prioritize integrating effective penetration testing devices into their security frameworks to navigate the complexities of cybersecurity. By adopting these best practices and remaining vigilant against evolving threats, organizations can not only protect their assets but also enhance their competitive edge in an increasingly digital landscape. Investing in robust penetration testing strategies is essential for safeguarding operations and reputations in an increasingly hostile cyber landscape.
Frequently Asked Questions
What is penetration testing?
Penetration testing, commonly referred to as pen testing, involves simulating cyberattacks on computer systems, networks, or web applications to identify vulnerabilities that could be exploited by malicious actors.
Why is penetration testing important in cybersecurity?
Penetration testing is crucial because it helps uncover vulnerabilities before they can be exploited, thereby protecting organizations from potential cyberattacks that can lead to significant production downtime, data breaches, and financial losses.
How has the manufacturing sector been affected by cyberattacks?
The manufacturing sector has become the most-attacked industry globally, facing severe implications from cyberattacks, including production halts, shipment delays, and jeopardized worker safety, resulting in substantial revenue losses.
What are the financial impacts of data breaches on manufacturers?
The average cost of a data breach exceeds $4.44 million, with this figure surpassing $10.22 million in the United States, highlighting the severe financial repercussions for manufacturers.
Can you provide examples of notable cyberattacks in the manufacturing sector?
Notable examples include the 2021 Oldsmar water treatment facility attack, which exploited remote access weaknesses, and the 2023 Clorox incident, where compromised vendor credentials were used.
How do security assessments benefit manufacturers?
Security assessments reveal exploitable weaknesses, assist organizations in prioritizing remediation actions, minimize operational risk, and improve the overall security posture of manufacturers.
What regulations should manufacturers be aware of regarding cybersecurity?
Manufacturers need to maintain compliance with industry regulations, including the upcoming NIS2 Directive, which emphasizes the importance of cybersecurity measures like penetration testing.
What are the consequences of not having a robust penetration evaluation strategy?
Without a strong penetration evaluation strategy, manufacturers risk their assets and operational viability, making them vulnerable in a competitive market.
List of Sources
- Define Penetration Testing and Its Importance in Cybersecurity
- Why Manufacturing Is the #1 Cyberattack Target in 2026 — And What to Do About It (https://blog.cybelesoft.com/manufacturing-cybersecurity-zero-trust-2026)
- 5 Key Takeaways from the 2026 State of Pentesting Report (https://cobalt.io/blog/5-key-takeaways-from-the-2026-state-of-pentesting-report)
- consilien.com (https://consilien.com/news/cybersecurity-threats-facing-manufacturers-in-2026)
- Why Penetration Testing is Important for Your Business in 2026 (https://brightdefense.com/resources/why-penetration-testing-is-important)
- 7 Key Manufacturing Cybersecurity Trends for 2026 | Huntress (https://huntress.com/blog/manufacturing-cybersecurity-trends)
- Explore Types of Penetration Testing and Their Device Requirements
- Best Penetration Testing Methods for Compliance (https://info.cgcompliance.com/blog/main-types-of-penetration-testing)
- 7 Types of Penetration Testing: Purpose & How to Choose (https://bitsight.com/blog/types-of-penetration-testing-which-is-right-for-your-business)
- Penetration Testing Requirement: What U.S. Rules Mandate It in 2026? (https://halock.com/penetration-testing-requirement-what-u-s-rules-mandate-it-in-2026)
- 8 Best Practices for Pen Testing in Manufacturing (https://manufacturing-journal.net/press-release/4588-8-best-practices-for-pen-testing-in-manufacturing)
- The Complete Guide to External Penetration Testing (2026) – Triaxiom Security (https://triaxiomsecurity.com/blog/the-complete-guide-to-external-penetration-testing-2026)
- Establish Criteria for Selecting Effective Pen Testing Tools
- Top 15 Penetration Testing Tools In 2026 | CloudSEK (https://cloudsek.com/knowledge-base/top-penetration-testing-tools)
- What type of penetration testing is required for compliance in 2026? (https://trustcloud.ai/risk-management/ultimate-guide-to-picking-the-right-type-of-penetration-testing)
- Top 6 Continuous Pentesting Tools in 2026 (https://aikido.dev/blog/top-6-continuous-pentesting-tools)
- 83 Penetration Testing Statistics: Key Facts and Figures (https://getastra.com/blog/penetration-testing/statistics)
- Top 7 Penetration Testing Tools for Enterprises in 2026 (https://cio.economictimes.indiatimes.com/tools/top-penetrating-test-tools/126140155)
- Implement Best Practices for Using Pen Testing Devices Effectively
- 5 Key Takeaways from the 2026 State of Pentesting Report (https://cobalt.io/blog/5-key-takeaways-from-the-2026-state-of-pentesting-report)
- 7 Key Manufacturing Cybersecurity Trends for 2026 | Huntress (https://huntress.com/blog/manufacturing-cybersecurity-trends)
- Penetration Testing Best Practices in 2026 | Iterasec (https://iterasec.com/blog/4-tips-to-maximize-application-pentest-value)
- Penetration Testing Requirement: What U.S. Rules Mandate It in 2026? (https://halock.com/penetration-testing-requirement-what-u-s-rules-mandate-it-in-2026)
- The New Rules of Manufacturing Cybersecurity: What to Know in 2026 – Decypher Technologies (https://decyphertech.com/the-new-rules-of-manufacturing-cybersecurity-what-to-know-in-2026)