Introduction
In an era marked by increasingly sophisticated cyber threats, the importance of incident response service providers has reached unprecedented levels. Organizations that effectively engage these experts can significantly bolster their resilience against breaches, often resulting in substantial savings in potential damages.
However, many organizations still face challenges in establishing robust communication and clear expectations with these providers. To ensure preparedness for incidents and an effective response when they occur, organizations must adopt strategic approaches to collaboration with incident response experts.
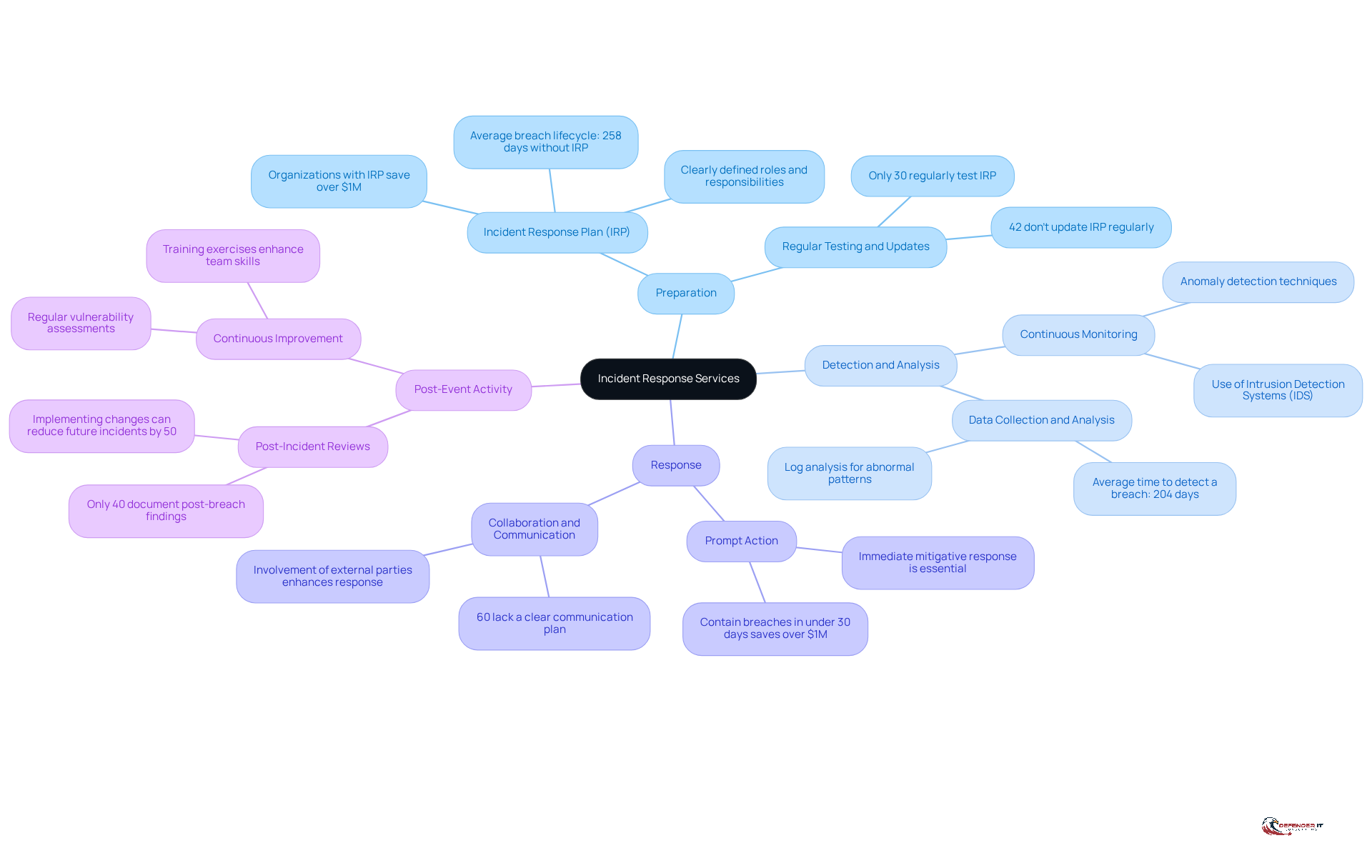
Define Incident Response Services
offer that encompass a comprehensive range of activities essential for preparing for, identifying, addressing, and recovering from incidents. The key components include:
- Preparation: Developing and implementing a robust incident response plan is crucial. Such a plan should clearly outline roles, responsibilities, and procedures. Organizations that utilize incident response plans can detect and recover from breaches significantly faster, often saving over $1 million compared to those without such plans. Furthermore, organizations lacking a response strategy face an average breach lifecycle of 258 days, in contrast to 189 days for those with a formal approach. This underscores the importance of having such plans.
- Detection and analysis by security teams is vital for proactively identifying potential security events through continuous monitoring and evaluation of security alerts. Efficient tools, such as intrusion detection systems (IDS), assist entities in recognizing irregularities that could indicate a breach.
- Response teams emphasize that containment, eliminating threats, and restoring systems to normal operations. Swift action minimizes harm and prevents further compromise, with entities that manage breaches in under 30 days saving over $1 million compared to those closer to the typical resolution time.
- Post-Event Activity: Conducting comprehensive evaluations of incidents with the assistance of incident response experts allows organizations to gain insights from their experiences and improve their strategies for addressing future situations. However, only 40% of organizations document lessons learned. Recording these insights enhances reaction speed and accuracy, highlighting a significant area for improvement.
In 2026, the importance of incident response planning cannot be overstated, as cyber threats continue to evolve. Currently, only 45% of entities have a plan for managing emergencies, indicating a substantial shortfall in preparedness. As Andrew Evers stated, “Preparedness is not built in the moment. It is earned through repetition, review, and refinement.” As the cybersecurity landscape becomes increasingly complex, incident response services are vital for maintaining resilience and safeguarding digital assets.
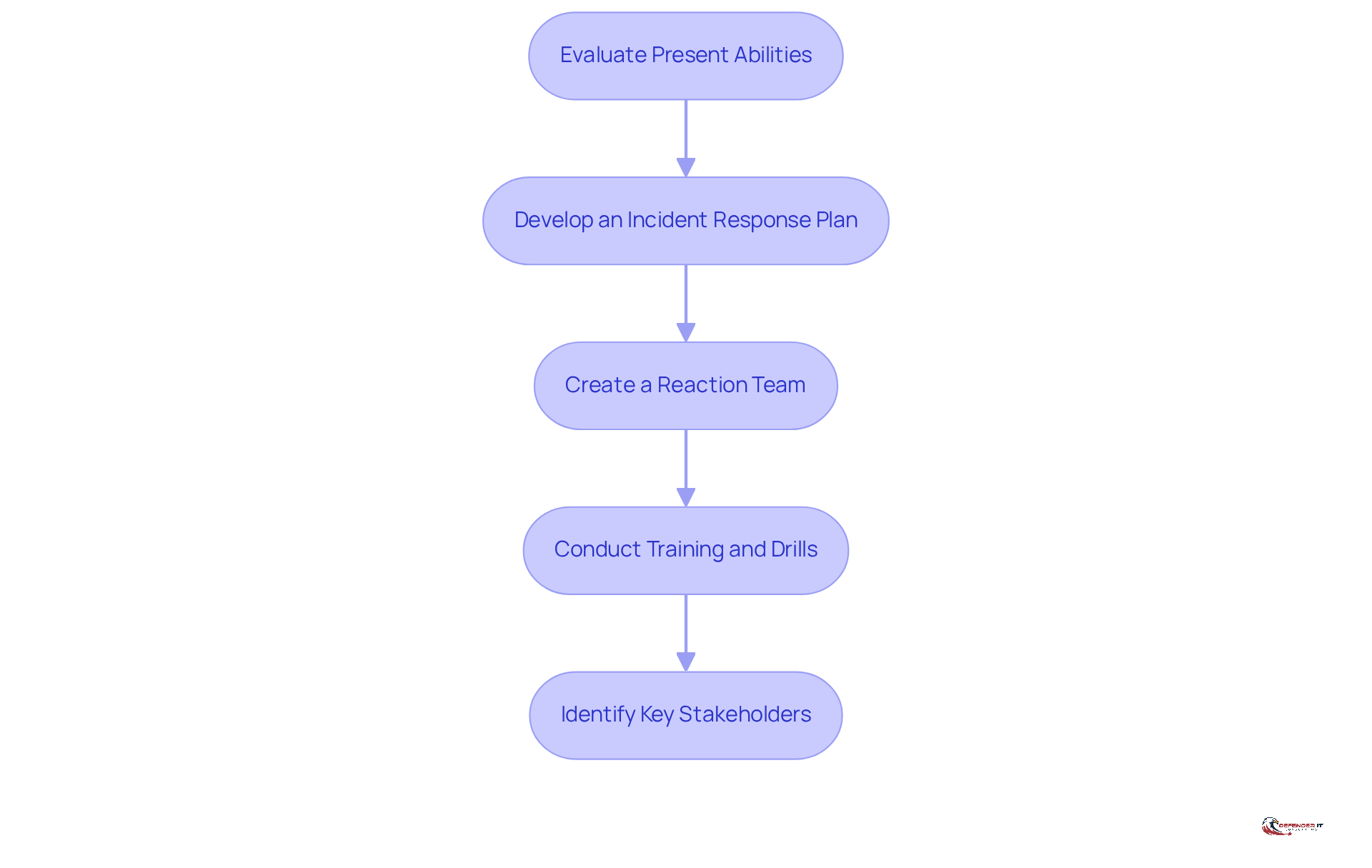
Prepare for Incident Response Engagement
Preparation for incident response involves several critical steps that can significantly enhance an organization’s security posture:
- Evaluate Present Abilities: Begin by assessing your organization’s current capability to handle incidents. This includes [security assessments](https://defenderit.consulting/10-essential-mssp-cyber-security-services-for-manufacturing-leaders/), which serve as a cybersecurity equivalent of a health scan, to identify vulnerabilities and gaps in your existing processes. Notably, only 55% of organizations had a fully documented [incident response plan](https://frsecure.com/blog/incident-response-statistics-how-do-you-compare) (IRP) for unexpected events as of 2025, and merely 45% of companies possess an IRP. This underscores the necessity for a comprehensive strategy.
- Develop an Incident Response Plan: Create or update your IRP to ensure it reflects current threats and organizational needs. Regular review is vital, as having a validated IRP is critical for faster recovery and damage reduction during incidents.
- Create a Reaction Team: Assemble a dedicated incident response team with clearly defined roles and responsibilities. Efficient handling of incidents necessitates distinct role differentiation among team members. The most skilled individual should not automatically assume the position of commander, as this can lead to inefficiencies.
- Conduct Training: Regularly train your team on the IRP and conduct simulation exercises to test their readiness. Engaging in tabletop exercises and red/blue team drills can help identify gaps and enhance coordination, ensuring that all stakeholders understand their roles during incidents.
- Identify Key Stakeholders: Determine who within your organization will participate in the incident response. Ensure that these stakeholders are informed and prepared, as their involvement is critical for effective communication and decision-making during an incident.
By implementing these preparatory actions, organizations can improve their readiness and foster a more effective partnership with incident response service providers, ultimately leading to a more resilient organization.
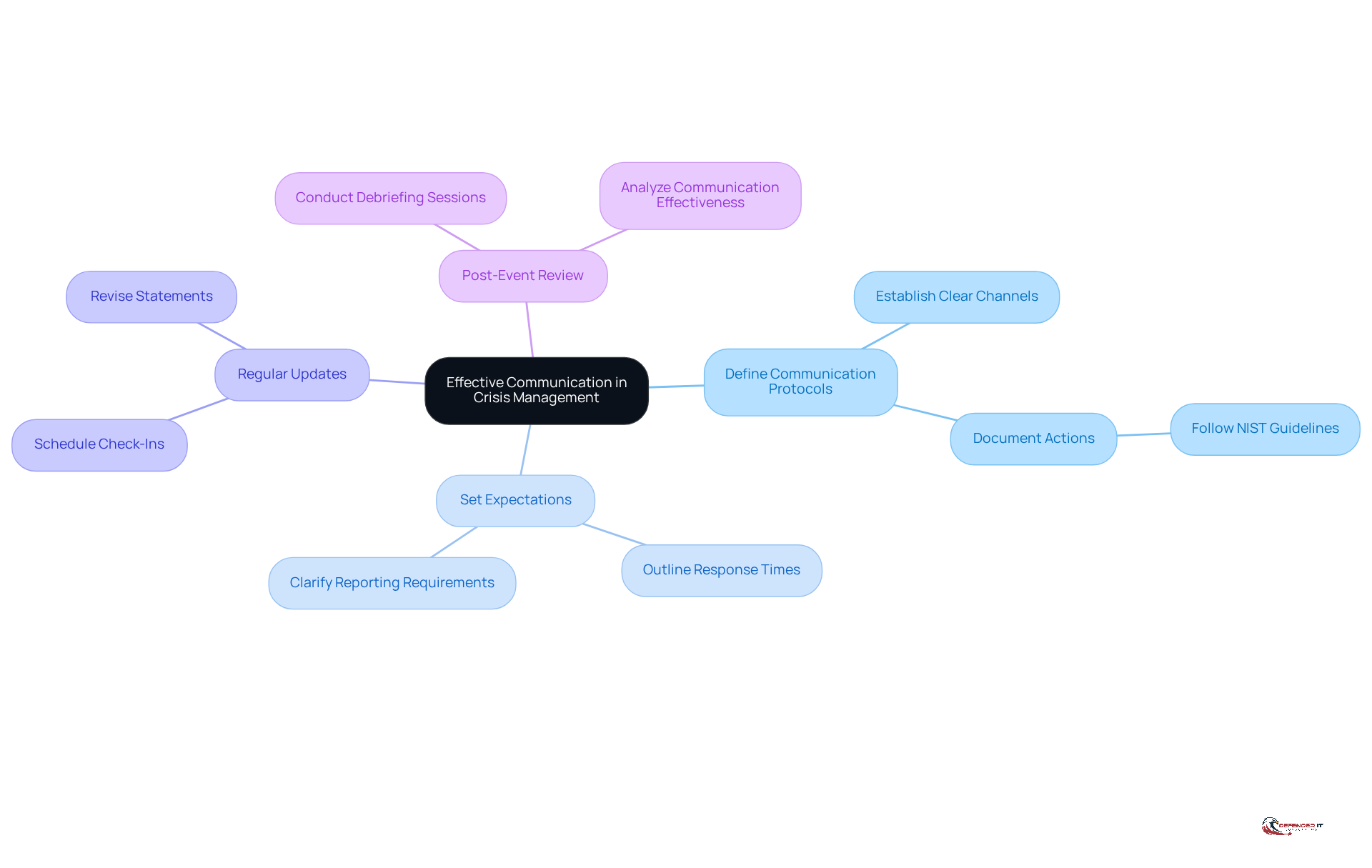
Establish Clear Communication and Expectations
Effective communication is fundamental to successful crisis management. It is essential.
It is crucial to establish clear channels for communication between your organization and the provider. This includes specifying who will communicate what information and when. The National Institute of Standards and Technology (NIST) emphasizes the importance of documenting and sharing actions during a cybersecurity threat in the Respond function of the Cybersecurity Framework. Clearly outline what your organization expects from the service provider regarding response times, reporting, and updates. With 83% of organizations experiencing one or more incidents, setting these expectations is vital for efficient event management.
Regular Updates: Schedule regular check-ins during an event to ensure all parties are aligned and informed about the situation, highlighting the financial consequences of inadequate communication during such events. After an incident, conduct a debriefing session to discuss what worked well and what could be improved in terms of communication. The Tylenol event in 1982 serves as a powerful example of how organizations can effectively manage crises.
By prioritizing communication, organizations can foster a collaborative environment that enhances the efficiency of crisis management efforts, ultimately leading to better outcomes and shorter recovery periods.
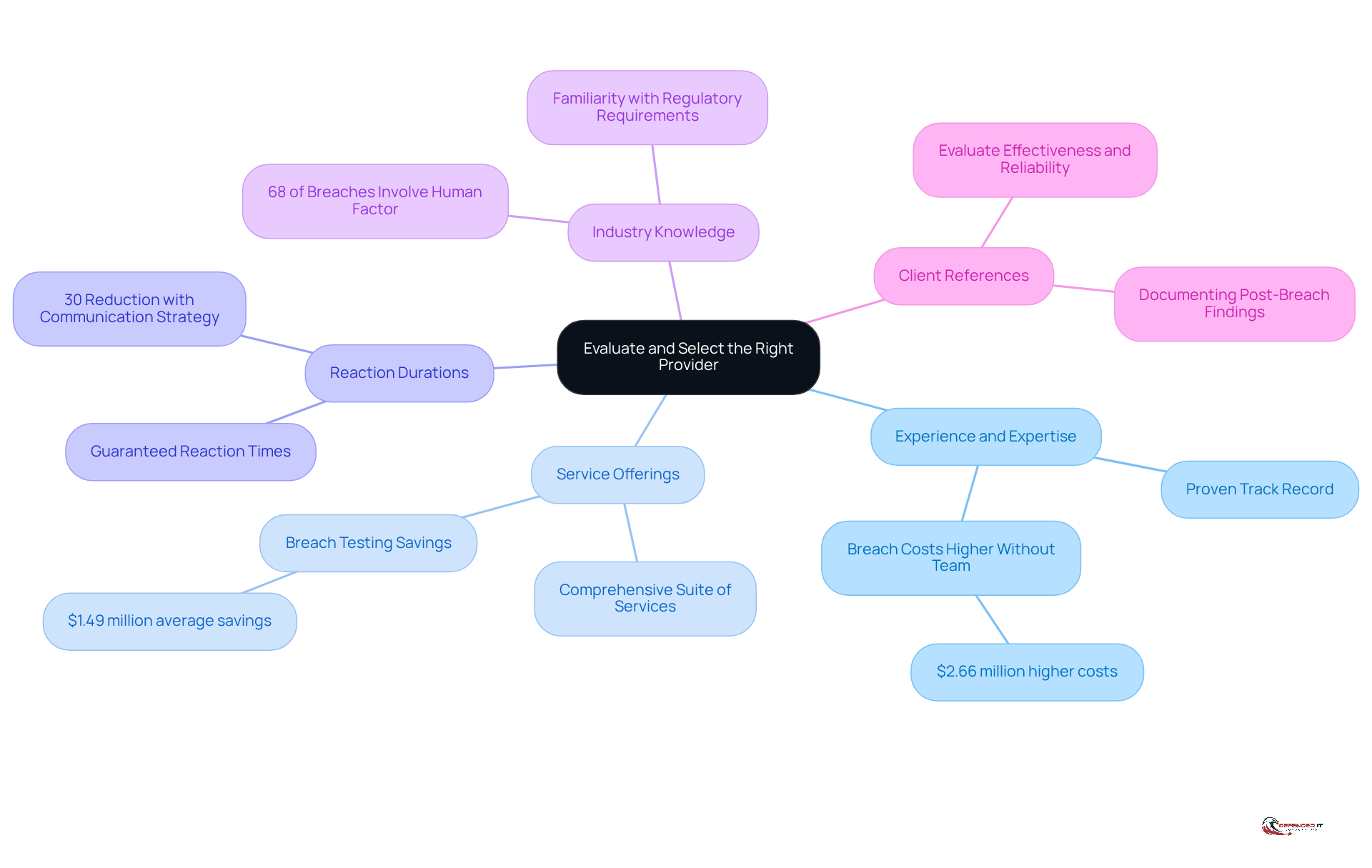
Evaluate and Select the Right Provider
Choosing the right provider for effective event management is essential. Organizations should prioritize the following criteria:
- Experience and Expertise: It is vital to select suppliers with a proven track record in managing incidents similar to those your organization may encounter. Research indicates that organizations lacking a response plan incur costs that are $2.66 million higher than those with established protocols, underscoring the importance of skilled suppliers.
- Service Offerings: Ensure that the supplier provides a comprehensive service package, including forensic analysis, containment, and recovery. Organizations that conduct breach testing at least twice a year can reduce costs by an average of $1.49 million, highlighting the necessity of a thorough strategy.
- Reaction Durations: Assess the supplier’s guaranteed response times and their ability to mobilize quickly during an incident. Organizations with established emergency communication strategies can decrease reaction time by 30%, emphasizing the critical nature of prompt action in crisis situations.
- Industry Knowledge: Opt for a supplier familiar with your industry’s regulatory requirements and specific challenges. Given that 68% of breaches involve a human factor, understanding these challenges is crucial for effective incident management.
- References: Request references from previous clients to evaluate the supplier’s effectiveness and reliability. Organizations that document their post-breach findings can significantly enhance their response speed and accuracy, turning client feedback into a valuable asset.
By thoroughly evaluating potential suppliers based on these criteria, organizations can make informed decisions that enhance their capabilities and better protect their assets.
Review and Improve Incident Response Strategies
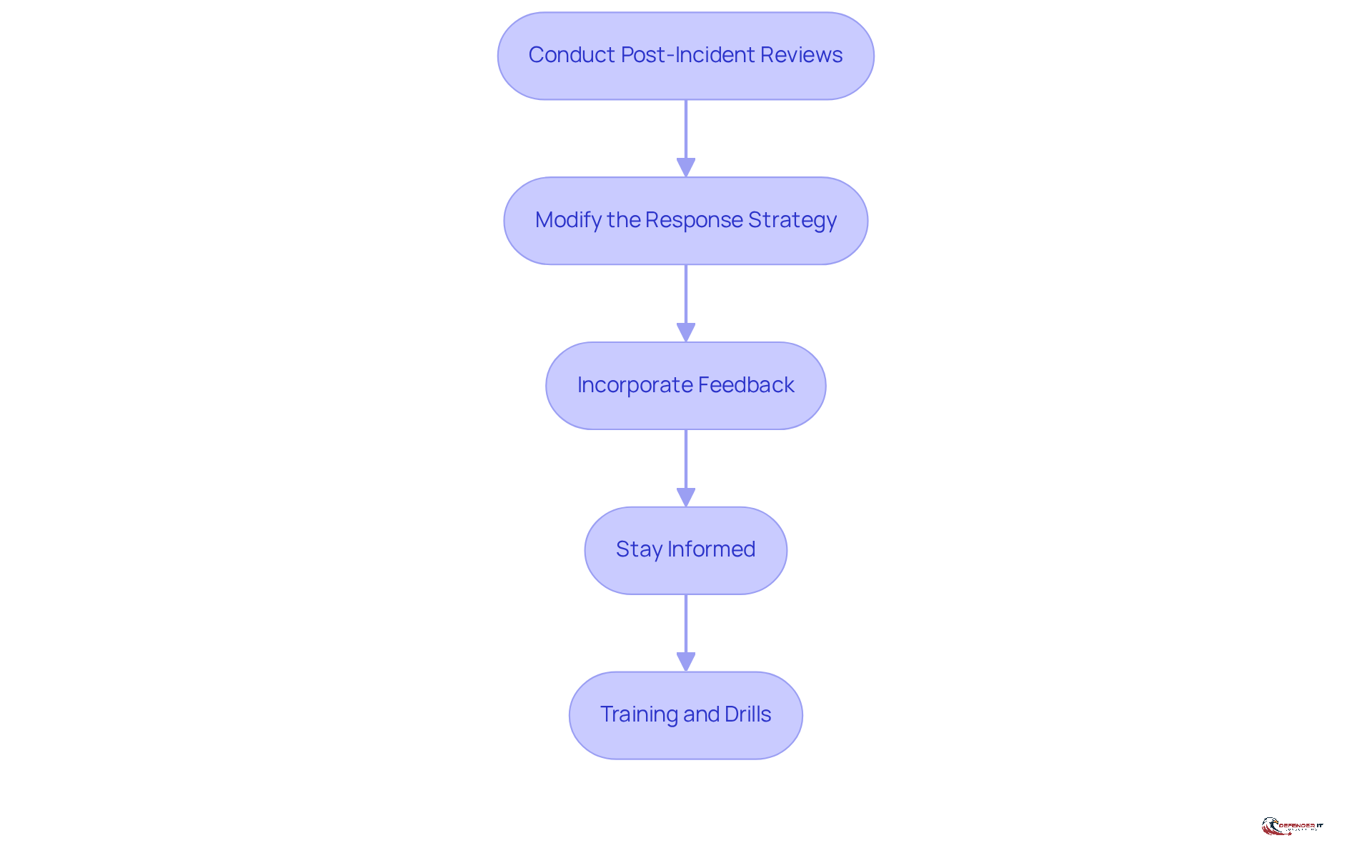
Ongoing enhancement is essential for effective situation management. Organizations must regularly refine their strategies by:
- Conducting Analysis: After each incident, it is vital to analyze the response to identify strengths and weaknesses. This practice is crucial, as companies that significantly improve their response time and accuracy. In fact, organizations that conduct incident response testing at least twice a year reduce breach costs by an average of $1.49 million.
- Updating Plans: It is important to revise the incident response plan based on lessons learned from events and shifts in the threat landscape. Currently, only 45% of organizations have a documented incident response plan, and 70% of businesses rarely or never test their IR plans. This highlights the critical need for regular updates to ensure preparedness.
- Incorporating Feedback: Gathering perspectives from all parties involved in the incident management process is essential to identify areas for improvement. Effective internal communication protocols can prevent 21% more secondary breaches caused by poorly managed efforts.
- Staying Informed: Organizations should remain updated on the latest threats to ensure their strategies are relevant. Those that conduct crisis management exercises at least once per quarter respond 35% faster to incidents, underscoring the importance of continuous learning. Notably, only 35% of businesses engage in training, revealing a gap between practice and recommended actions.
- Providing Education: It is crucial to consistently educate teams on revised procedures and conduct exercises to evaluate new tactics. Companies that provide monthly security training reduce the likelihood of breaches by 60%, emphasizing the importance of ongoing education. As W. Edwards Deming stated, “Learning is not compulsory; it’s voluntary. Improvement is not compulsory; it’s voluntary. But to survive, we must learn.”
By committing to ongoing review and improvement, organizations can enhance their incident response capabilities through service providers and better safeguard their digital assets.
Conclusion
Engaging effectively with incident response service providers is critical in today’s cybersecurity landscape. Organizations must recognize that a proactive approach, characterized by well-defined incident response plans and clear communication strategies, not only enhances preparedness but also significantly reduces the financial impact of security breaches. The importance of collaboration with these service providers cannot be overstated, as they play a pivotal role in ensuring swift detection, response, and recovery from incidents.
Key practices highlighted throughout this article include:
- The necessity of preparing an incident response plan
- Establishing clear communication channels
- Selecting the right provider based on experience and expertise
Additionally, ongoing evaluation and refinement of incident response strategies are essential to adapt to evolving threats. Collectively, these steps contribute to a more resilient cybersecurity posture, equipping organizations to handle crises more effectively.
Ultimately, organizations must commit to continuous improvement in their incident response capabilities. By fostering a culture of preparedness and collaboration with incident response service providers, businesses can mitigate risks and enhance their overall security framework. This proactive stance is vital for safeguarding digital assets and ensuring long-term success in an increasingly complex cyber environment.
Frequently Asked Questions
What are incident response services?
Incident response services are crisis management services that help organizations prepare for, identify, address, and recover from cybersecurity events. They include preparation, detection and analysis, prompt action during incidents, and post-event evaluations.
Why is preparation important in incident response?
Preparation is crucial because it involves developing a robust incident response plan (IRP) that outlines roles, responsibilities, and procedures. Organizations with an IRP can detect and recover from breaches faster, potentially saving over $1 million compared to those without a plan.
How do incident response service providers help in detection and analysis?
They proactively identify potential security events through continuous monitoring and evaluation of security alerts, utilizing efficient anomaly detection methods like intrusion detection systems (IDS) to recognize irregularities that may indicate a breach.
What is the significance of prompt action during a cybersecurity incident?
Prompt action is essential for managing incidents effectively, eliminating threats, and restoring systems to normal operations. Organizations that manage breaches in under 30 days can save over $1 million compared to those that take longer.
What should organizations do after a cybersecurity incident?
Organizations should conduct comprehensive evaluations of incidents with the help of incident response service providers to gain insights and improve their strategies for future incidents. However, only 40% of organizations currently document post-breach findings.
What is the current state of preparedness among organizations for cybersecurity incidents?
As of 2026, only 45% of organizations have a plan for managing emergencies, indicating a significant shortfall in preparedness. This highlights the importance of incident response service providers in enhancing crisis management.
What are the critical steps to prepare for engaging with incident response service providers?
Key steps include evaluating current capabilities, developing or updating an incident response plan, creating a reaction team with defined roles, conducting training and drills, and identifying key stakeholders for the incident handling process.
Why is it important to conduct training and drills for the incident management team?
Regular training and simulation exercises help test the team’s readiness, identify gaps, and enhance coordination, ensuring that all stakeholders understand their roles during incidents.
How can organizations improve their cybersecurity posture through incident response preparation?
By implementing preparatory actions such as assessing vulnerabilities, developing a validated incident response plan, and fostering effective partnerships with incident response service providers, organizations can enhance their readiness and resilience against cyber threats.
List of Sources
- Define Incident Response Services
- Incident Response: Importance of an Effective Incident Response Team in Cybersecurity | CyberMaxx (https://cybermaxx.com/incident-response-importance)
- Incident Response Statistics to Know in 2025 (https://jumpcloud.com/blog/incident-response-statistics)
- Incident Response Statistics: USA | Infrascale (https://infrascale.com/incident-response-statistics-usa-2025)
- 139 Cybersecurity Statistics and Trends [updated 2025] (https://varonis.com/blog/cybersecurity-statistics)
- Incident Response Statistics: How Do You Compare? | FRSecure (https://frsecure.com/blog/incident-response-statistics-how-do-you-compare)
- Prepare for Incident Response Engagement
- Incident Response Statistics: How Do You Compare? | FRSecure (https://frsecure.com/blog/incident-response-statistics-how-do-you-compare)
- thenewstack.io (https://thenewstack.io/5-incident-management-lessons-to-carry-into-2026)
- Incident Response Readiness (IRR): Ready for 2026 Threats? (https://halock.com/incident-response-readiness-irr-ready-for-2026-threats)
- Best Incident Response Tools for 2026 Security Needs (https://vmray.com/best-incident-response-tools-comprehensive-guide-2026)
- Cyber Resilience and Incident Response in 2026: Why Preparation Matters More Than Prevention (https://bitlyft.com/resources/cyber-resilience-and-incident-response-in-2026-why-preparation-matters-more-than-prevention)
- Establish Clear Communication and Expectations
- Keep the Conversation Going: Communication in Incident Response (https://compassmsp.com/resources/communication-in-incident-response)
- solutionsreview.com (https://solutionsreview.com/cybersecurity-awareness-month-quotes-and-commentary-from-industry-experts-in-2025)
- Poor Communication During a Data Breach Can Cost You — Here’s How to Avoid It | IBM (https://ibm.com/think/x-force/poor-communication-data-breach-cost-how-to-avoid)
- Case Studies in Crisis Management: Analyzing Corporate Responses to Public Relations Failures (https://socialtargeter.com/blogs/case-studies-in-crisis-management-analyzing-corporate-responses-to-public-relations-failures)
- 5 Quotes About the Growing Importance of Internal Communications – Weber Associates (https://weberassoc.com/internal-communications-quotes)
- Evaluate and Select the Right Provider
- Incident Response Statistics to Know in 2025 (https://jumpcloud.com/blog/incident-response-statistics)
- Incident Response Statistics: How Do You Compare? | FRSecure (https://frsecure.com/blog/incident-response-statistics-how-do-you-compare)
- Incident Response Statistics: USA | Infrascale (https://infrascale.com/incident-response-statistics-usa-2025)
- paloaltonetworks.com (https://paloaltonetworks.com/blog/2024/08/incident-response-by-the-numbers)
- Review and Improve Incident Response Strategies
- Incident Response Statistics to Know in 2025 (https://jumpcloud.com/blog/incident-response-statistics)
- 85 Quotes – Operational Excellence and Continuous Improvement | Rever (https://reverscore.com/85-quotes-operational-excellence-and-continuous-improvement)
- Why cybersecurity resilience should be your focus in 2026 (https://insights.integrity360.com/why-cybersecurity-resilience-should-be-your-focus-in-2026)
- Incident Response Statistics: How Do You Compare? | FRSecure (https://frsecure.com/blog/incident-response-statistics-how-do-you-compare)
- Top 8 Incident Response Metrics To Know | Splunk (https://splunk.com/en_us/blog/learn/incident-response-metrics.html)