Introduction
Internal vulnerability assessments are essential to an organization’s cybersecurity strategy, serving as the first line of defense by uncovering weaknesses that external scans may miss. These assessments go beyond mere compliance; they play a crucial role in protecting sensitive information and reducing the financial impact of data breaches, which can escalate into millions.
Given the rapidly changing threat landscape and the alarming increase in cyberattacks, organizations must ensure they effectively identify and address vulnerabilities before they can be exploited. This article explores best practices for conducting internal vulnerability assessments, providing a comprehensive roadmap for businesses to strengthen their security posture and navigate the complexities of modern cybersecurity challenges.
Define Internal Vulnerability Assessments and Their Importance
Internal vulnerability assessments are systematic reviews conducted within a company’s network to identify vulnerabilities that attackers could exploit. Internal vulnerability assessments involve scanning internal systems, applications, and configurations to uncover weaknesses that may not be visible through external scans. The importance of internal vulnerability assessments lies in their ability to proactively detect and address potential vulnerabilities before they can be exploited, thereby reducing the risk of data breaches and enhancing the organization’s overall security posture.
Regular internal vulnerability assessments are particularly crucial for companies in regulated sectors, where compliance with security standards is mandatory. In 2025, the average cost of a data breach reached $4.35 million, with the healthcare sector facing even higher costs at $10.1 million per breach. This underscores the financial ramifications of unassessed vulnerabilities. Additionally, 83% of organizations reported experiencing successful phishing attacks in 2023, which highlights the increasing frequency and severity of cyber threats and the urgent need for internal vulnerability assessments.
By conducting these evaluations on a regular basis, organizations can ensure compliance with industry regulations and effectively protect their sensitive information against evolving cyber threats.
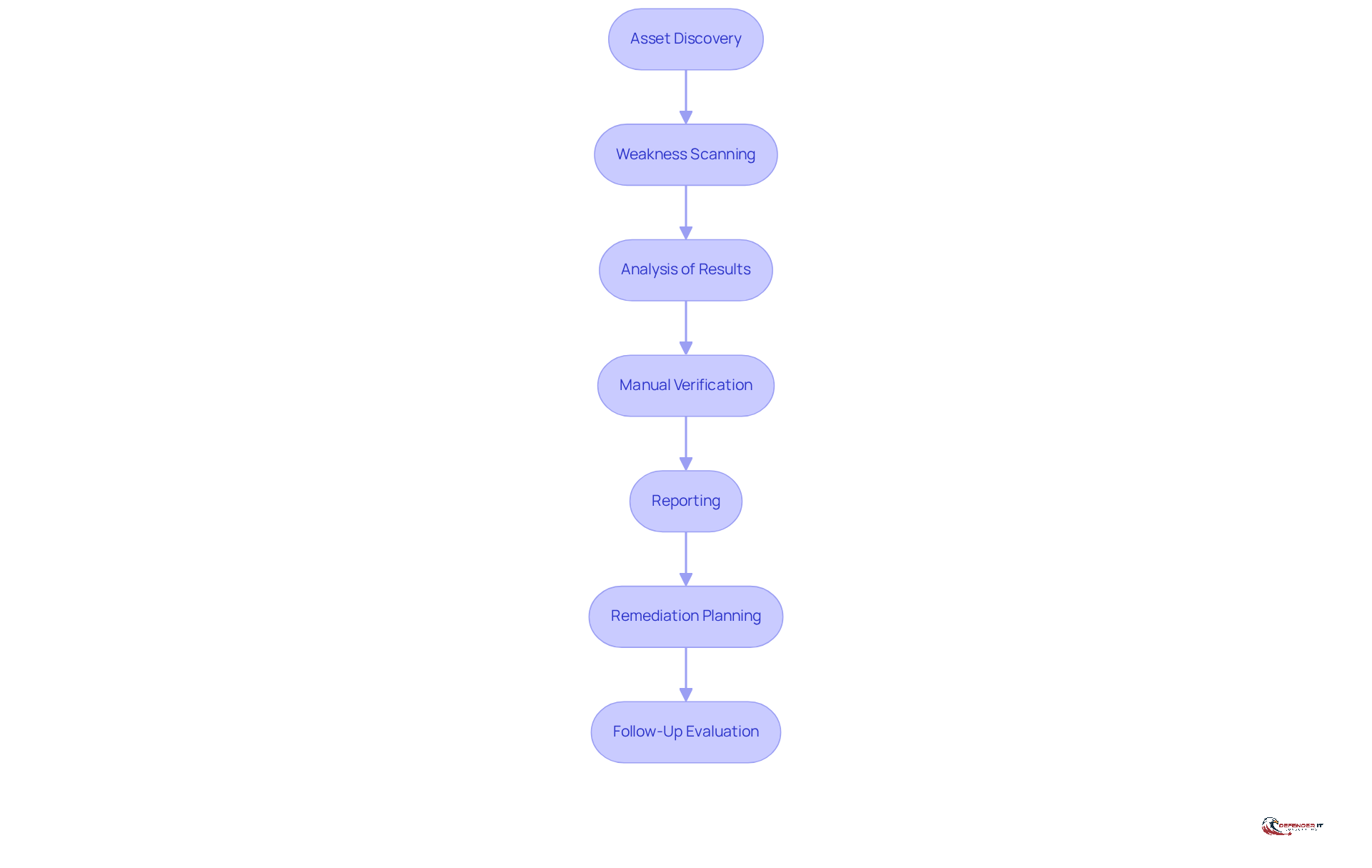
Outline the Step-by-Step Process for Conducting Assessments
- Asset Discovery: Start by identifying all assets within the network, including servers, workstations, and applications. This foundational step is crucial for establishing a comprehensive understanding of the evaluated environment, which is essential for effective risk management.
- Weakness Scanning: Employ automated tools such as Tenable, Qualys, and Rapid7 to assess the identified assets for known vulnerabilities. Regular scanning is imperative, as cybersecurity incidents now result in more downtime than mechanical failures, underscoring the urgency of proactive assessments. By 2026, a projected 21% increase in new vulnerabilities will necessitate that organizations stay ahead of potential threats.
- Analysis of Results: Examine the outcomes of the scans to pinpoint weaknesses, categorizing them by severity and potential impact on the organization. This analysis should translate technical risks into business implications, highlighting potential financial consequences, such as the average cost of a breach being $4.88 million, to support informed decision-making.
- Manual Verification: Conduct manual assessments on critical vulnerabilities to confirm their existence and evaluate their potential impact more accurately. This step is vital, as automated tools may yield false positives, leading to alert fatigue among security teams.
- Reporting: Prepare a comprehensive report detailing the findings, including identified vulnerabilities, their risk levels, and recommended remediation actions. Tailoring reports for different audiences-executives and IT teams-ensures that the information is both accessible and actionable.
- Remediation Planning: Develop a strategy to address the identified vulnerabilities, prioritizing them based on risk and potential effects on business operations. Effective corrective actions should focus on threats that pose the highest risk to the organization, with defined timelines for addressing critical vulnerabilities.
- Follow-Up Evaluation: Schedule follow-up evaluations to verify the success of remediation efforts and to identify any new vulnerabilities that may have emerged. Ongoing monitoring is essential, as the typical duration required for internal vulnerability assessments in businesses is decreasing, necessitating frequent updates to security protocols. Additionally, a clearly defined scope document is crucial for managing expectations and preventing scope creep during security evaluations.
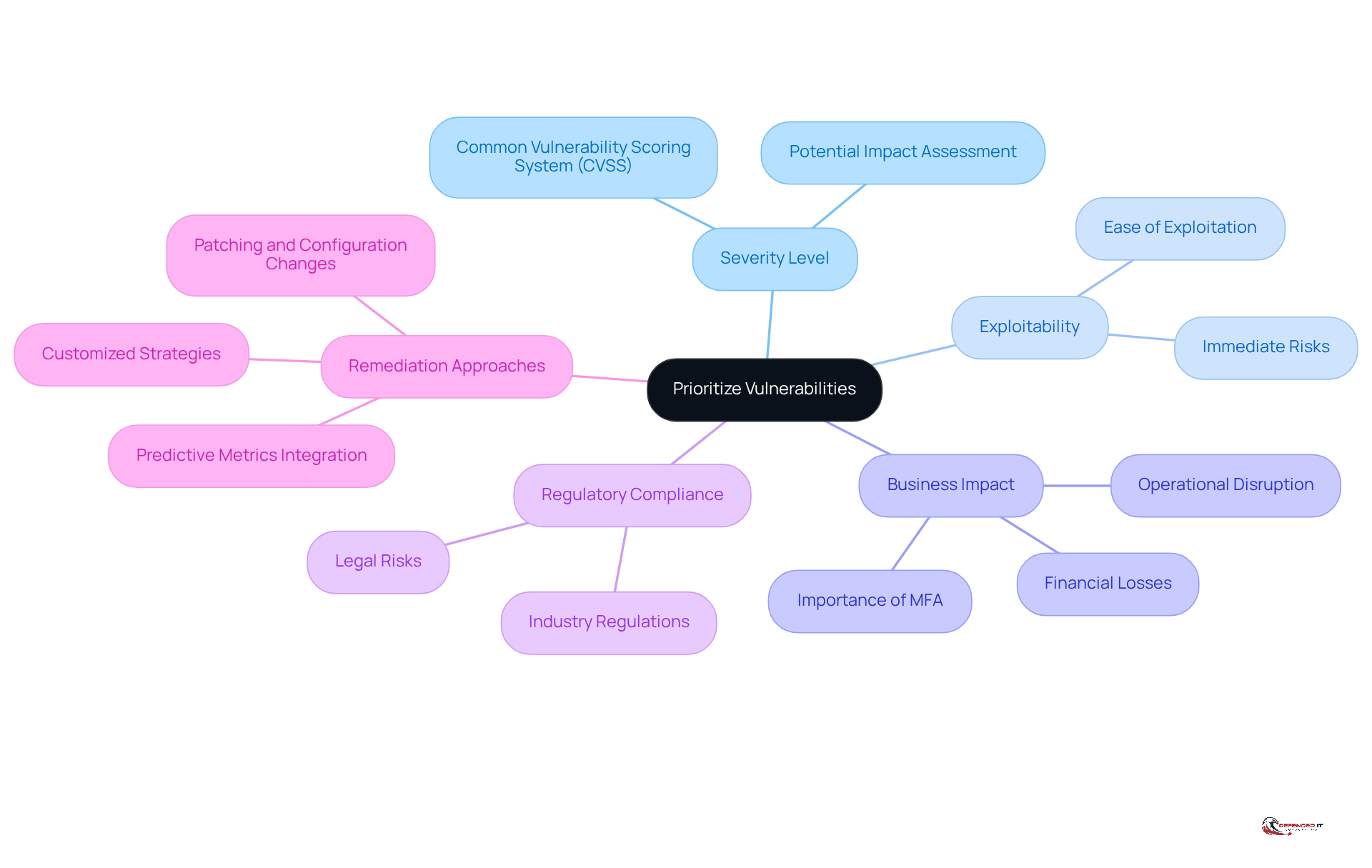
Prioritize Vulnerabilities and Develop Effective Remediation Strategies
To effectively prioritize vulnerabilities, organizations must consider several critical factors:
- Severity Level: The Common Vulnerability Scoring System (CVSS) should be utilized to assess the severity of each issue, determining its potential impact on the organization. This standardized scoring system aids in identifying which weaknesses pose the greatest risk.
- Exploitability: It is essential to assess how easily a weakness can be exploited by attackers. Vulnerabilities that are readily exploitable should be prioritized for remediation, as they present immediate risks to security.
- Business Impact: Organizations must evaluate the potential outcomes on business operations if a weakness were to be exploited. Focus should be on weaknesses that affect essential systems or sensitive information, as these can lead to significant operational disruptions and financial losses. For instance, organizations implementing phishing-resistant multi-factor authentication (MFA) and robust identity management practices have consistently experienced fewer credential-based incidents, underscoring the importance of addressing vulnerabilities that could lead to such incidents.
- Regulatory Compliance: Identifying weaknesses that could result in non-compliance with industry regulations is crucial. Prioritizing these vulnerabilities helps mitigate legal risks, particularly in regulated sectors where compliance failures can incur severe penalties. In 2025, North America accounted for 29% of all X-Force incident response cases, highlighting the urgency of addressing vulnerabilities in a region increasingly targeted by attackers.
- Remediation Approaches: Customized remediation strategies should be developed for each prioritized weakness. These strategies may encompass patching, configuration changes, or the implementation of additional security controls. It is vital to consistently assess and update these strategies to adapt to evolving threats and vulnerabilities. The integration of predictive metrics can enhance proactive decision-making, enabling organizations to identify weaknesses likely to be exploited in the near term. Notably, predictive metrics appear in only 17 studies, indicating a significant opportunity for improvement.
By focusing on these elements, companies can bolster their risk management procedures and enhance their overall security posture.
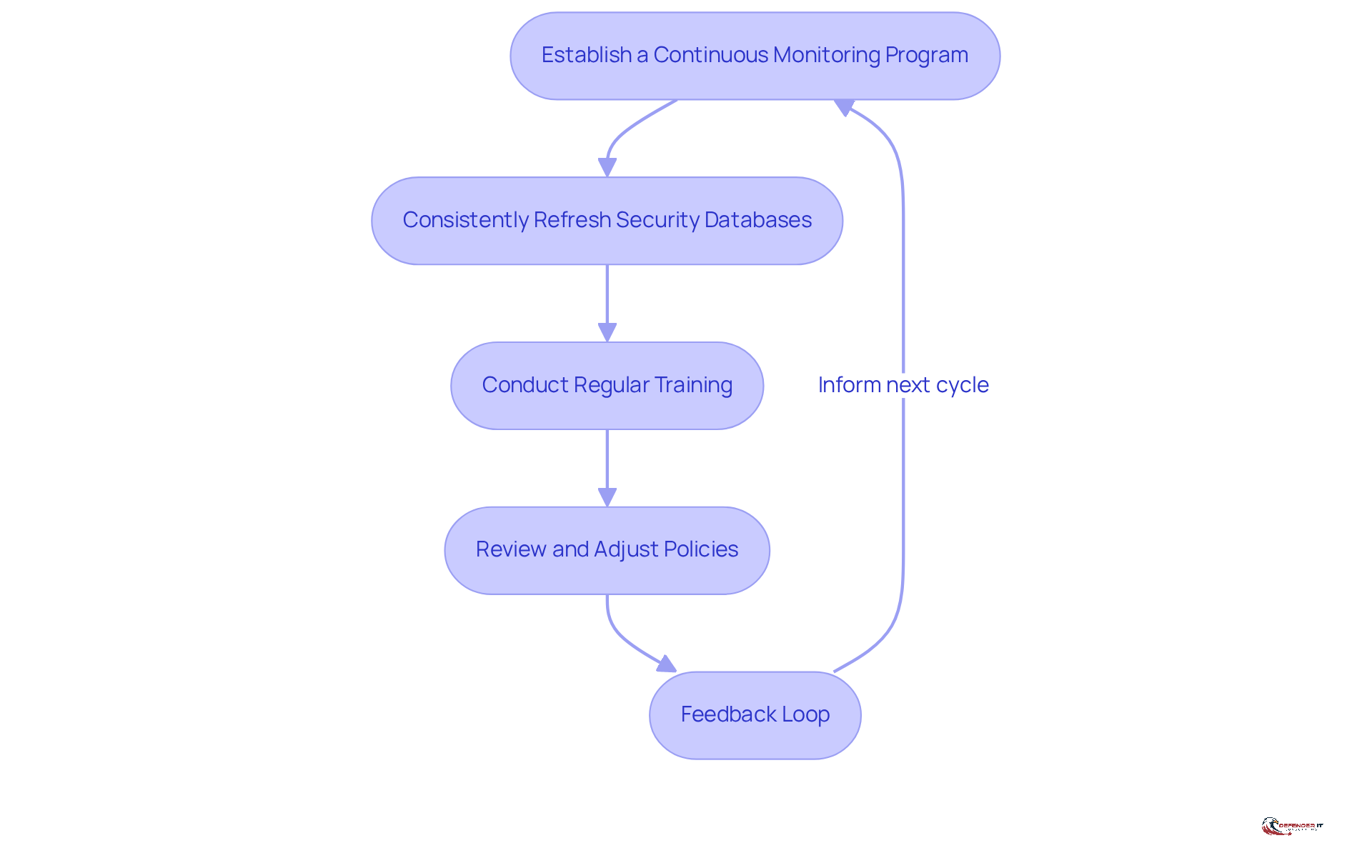
Implement Continuous Monitoring and Improvement Practices
- Establish a Continuous Monitoring Program: Implement tools and processes that facilitate real-time monitoring of networks and systems. This enables the identification of weaknesses as they arise, incorporating automated scanning and alerting mechanisms that provide immediate insights into potential threats. By 2026, continuous monitoring will be mandatory for entities subject to DFARS 252.204-7012, CMMC, NIST SP 800-53 Rev. 5, CDM, or FISMA, making it essential to adopt these practices now.
- Consistently Refresh Security Databases: Maintain current threat databases to include the latest risks and weaknesses. This practice is crucial for effective scanning and assessment, ensuring that organizations are prepared to address newly identified risks. Notably, 56% of nearly 40,000 weaknesses monitored in 2025 could be exploited without any form of authentication, underscoring the urgency of this task.
- Conduct Regular Training: Provide ongoing instruction for IT personnel and staff to keep them informed about the latest threats and best practices for maintaining safety. This proactive strategy enhances the organization’s capacity to address weaknesses effectively.
- Review and Adjust Policies: Regularly assess protection policies and procedures to ensure they remain effective and aligned with current best practices and regulatory requirements. This continuous improvement process is vital for adapting to the evolving threat landscape.
- Feedback Loop: Establish a feedback loop where lessons learned from past incidents and assessments inform future vulnerability management practices. As Patrick Sullivan noted, “for CISOs, continuous monitoring is ultimately a means of maintaining control: understanding current posture, managing exceptions, and making defensible decisions as the environment changes.” This iterative approach enables organizations to adapt to new threats and continuously enhance their overall security posture.
Conclusion
Internal vulnerability assessments are essential for maintaining robust cybersecurity within organizations. By systematically identifying and addressing vulnerabilities before they can be exploited, these assessments play a vital role in safeguarding sensitive information and ensuring compliance with regulatory standards. Their proactive nature not only helps mitigate potential data breaches but also reinforces the overall security posture of a company.
The article outlines the step-by-step process for conducting internal vulnerability assessments, highlighting key stages such as:
- Asset discovery
- Weakness scanning
- Remediation planning
It emphasizes the importance of prioritizing vulnerabilities based on severity, exploitability, and potential business impact. Furthermore, the necessity of continuous monitoring and improvement practices is underscored, ensuring that organizations remain vigilant against emerging threats.
Ultimately, the significance of internal vulnerability assessments cannot be overstated. Organizations must embrace these assessments as a fundamental component of their cybersecurity strategy, treating them not merely as a one-time task but as an ongoing commitment to security. By implementing these best practices and fostering a culture of continuous improvement, companies can effectively navigate the evolving threat landscape and protect their most valuable assets.
Frequently Asked Questions
What are internal vulnerability assessments?
Internal vulnerability assessments are systematic reviews conducted within a company’s network to identify vulnerabilities that attackers could exploit. They involve scanning internal systems, applications, and configurations to uncover weaknesses not visible through external scans.
Why are internal vulnerability assessments important?
They are important because they proactively detect and address potential vulnerabilities before they can be exploited, reducing the risk of data breaches and enhancing the organization’s overall security posture.
Who should conduct internal vulnerability assessments?
Regular internal vulnerability assessments are particularly crucial for companies in regulated sectors, where compliance with security standards is mandatory.
What are the financial implications of data breaches?
In 2025, the average cost of a data breach reached $4.35 million, with the healthcare sector facing even higher costs at $10.1 million per breach, highlighting the financial ramifications of unassessed vulnerabilities.
How prevalent are cyber threats?
In 2023, 83% of organizations reported experiencing successful phishing attacks, indicating the increasing frequency and severity of cyber threats and the urgent need for internal vulnerability assessments.
How can regular internal vulnerability assessments benefit organizations?
By conducting these evaluations regularly, organizations can ensure compliance with industry regulations and effectively protect their sensitive information against evolving cyber threats.
List of Sources
- Define Internal Vulnerability Assessments and Their Importance
- Cybersecurity Alerts & Advisories | CISA (https://cisa.gov/news-events/cybersecurity-advisories)
- Industrial Control System Vulnerabilities Hit Record Highs (https://infosecurity-magazine.com/news/industrial-control-system-vulns)
- Vulnerability — Latest News, Reports & Analysis | The Hacker News (https://thehackernews.com/search/label/Vulnerability)
- Why and How to Perform Cybersecurity Risk Assessments in 2026 (https://maddevs.io/blog/how-to-perform-cybersecurity-risk-assessments)
- Ultimate Guide to Vulnerability Assessment: What, Why & How (2026 Edition) (https://acronis.com/en/blog/posts/ultimate-guide-to-vulnerability-assessment-2026)
- Outline the Step-by-Step Process for Conducting Assessments
- Ultimate Guide to Vulnerability Assessment: What, Why & How (2026 Edition) (https://acronis.com/en/blog/posts/ultimate-guide-to-vulnerability-assessment-2026)
- Vulnerability Assessment in 2026: A Comprehensive Guide – Tolu Michael (https://blog.tolumichael.com/vulnerability-assessment-2026)
- Vulnerability Assessment Guide by Heights Consulting Group (https://heightscg.com/2025/12/16/how-to-conduct-vulnerability-assessment)
- Vulnerability Management Process: Step-by-Step Guide for 2026 (https://qualysec.com/vulnerability-management-process)
- 3 Best Practices for Effective Cyber Assessments in 2026 — Cyber Solutions Inc (https://discovercybersolutions.com/blog-posts/3-best-practices-for-effective-cyber-assessments-in-2026)
- Prioritize Vulnerabilities and Develop Effective Remediation Strategies
- Cyber Risk in 2026: What Security Leaders Need to Pay Attention to Now (https://directdefense.com/cyber-risk-in-2026-what-security-leaders-need-to-pay-attention-to-now)
- Forget Predictions: True 2026 Cybersecurity Priorities From Leaders (https://securityweek.com/forget-predictions-true-2026-cybersecurity-priorities-from-leaders)
- Cybersecurity Trends 2026 | IBM (https://ibm.com/think/insights/more-2026-cyberthreat-trends)
- A Survey on Vulnerability Prioritization: Taxonomy, Metrics, and Research Challenges (https://arxiv.org/html/2502.11070v1)
- Implement Continuous Monitoring and Improvement Practices
- Why CISOs are adopting continuous control monitoring 2026 (https://trustcloud.ai/security-assurance/why-cisos-should-prioritize-continuous-controls-monitoring-in-2026)
- Industry News 2026 The 6 Cybersecurity Trends That Will Shape 2026 (https://isaca.org/resources/news-and-trends/industry-news/2026/the-6-cybersecurity-trends-that-will-shape-2026)
- Why continuous monitoring matters for cybersecurity leaders (https://heightscg.com/2026/04/17/why-continuous-monitoring-matters-cybersecurity-leaders)
- Cybersecurity Trends 2026 | IBM (https://ibm.com/think/insights/more-2026-cyberthreat-trends)
- Continuous Monitoring in 2026: Best Practices for Regulated Industries (https://telos.com/blog/2026/04/14/continuous-monitoring-in-highly-regulated-industries-best-practices)