Introduction
In today’s rapidly evolving landscape of cyber threats, organizations encounter a critical challenge: safeguarding sensitive data within enclave environments. Effective enclave security transcends mere technical necessity; it stands as a strategic imperative that can significantly mitigate the risk of costly breaches and compliance failures. Organizations must ask themselves: how can they ensure compliance with regulatory standards while also building resilience against the increasingly sophisticated nature of cyber attacks? This article explores essential practices for enhancing enclave security, compliance measures, and risk management strategies that empower organizations to protect their most valuable assets.
Establish Core Security Practices for Enclave Environments
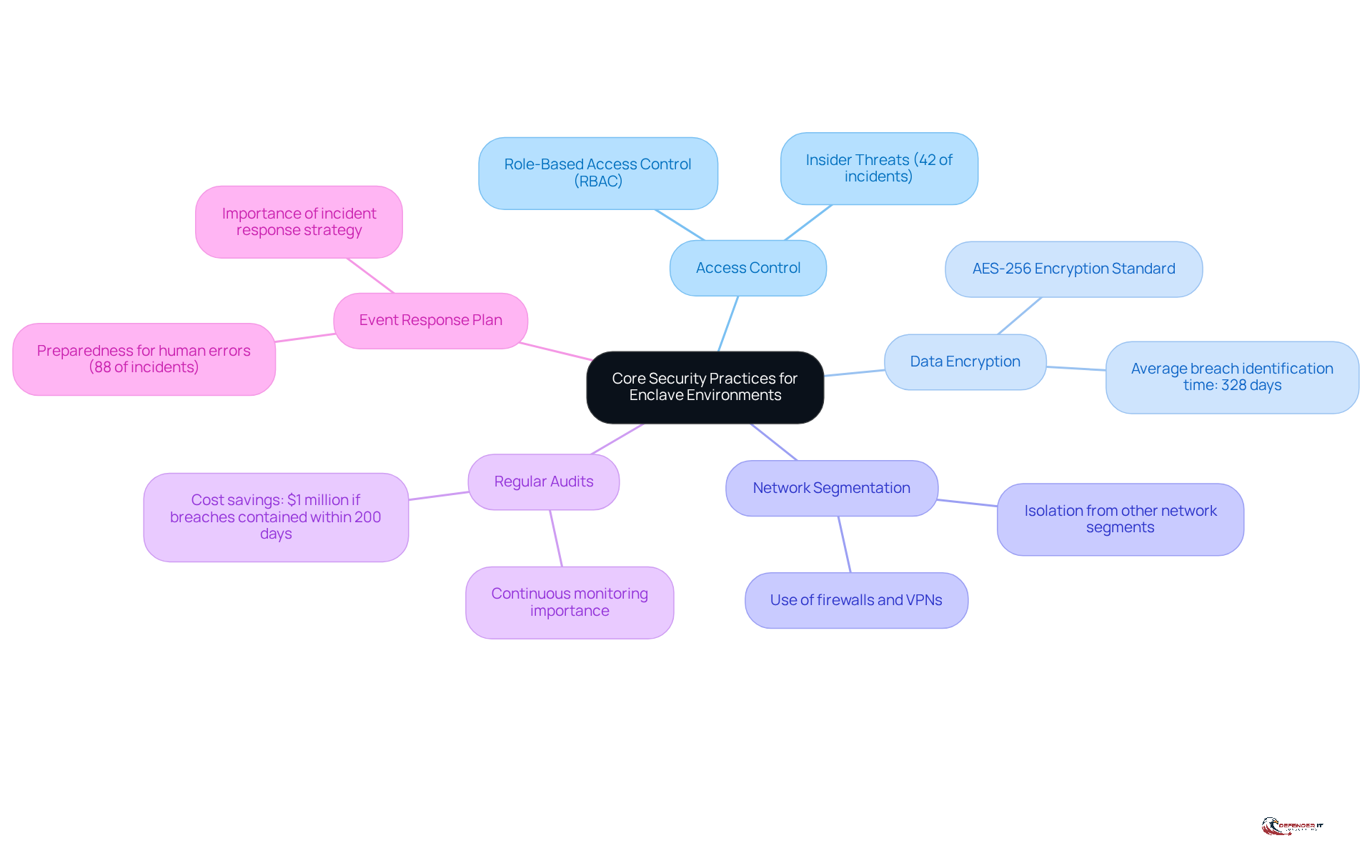
To enhance enclave security, organizations should implement the following core practices:
- Access Controls: Establish strict protocols to limit who can enter the enclave. Employing these measures ensures that only authorized personnel can access sensitive information, significantly reducing the likelihood of insider threats, which account for 42% of incidents. This underscores the critical role of access controls in mitigating risks associated with unauthorized access.
- Data Encryption: Encrypt data both at rest and in transit using robust encryption standards such as AES-256. This is essential, as breaches involving lost or stolen credentials take an average of 328 days to identify and contain, highlighting the necessity for encryption to protect data from unauthorized access. Effective encryption practices can notably decrease the time and costs associated with data breaches.
- Network Segmentation: Isolate the enclave from other network segments to minimize exposure to potential threats. This can be achieved through firewalls and virtual private networks (VPNs), which help establish enclave security around sensitive data, thereby enhancing overall protection.
- Regular audits should be conducted to assess safety and vulnerability in order to identify and remediate potential weaknesses in the enclave security measures. Continuous monitoring is vital, as organizations that identify and contain breaches within 200 days save approximately $1 million compared to those that take longer. This financial incentive emphasizes the importance of proactive protective measures.
- Incident Response: Develop and maintain a response plan that outlines procedures for detecting, addressing, and recovering from security events within the enclave. This proactive strategy is crucial for enclave security, given that 88% of all cyber incidents are attributed to human errors, which underscores the need for preparedness. The Colonial Pipeline ransomware attack serves as a cautionary example, illustrating the critical importance of having a well-defined response plan.
By implementing these practices, organizations can create a secure environment that protects sensitive data and complies with regulatory requirements, ultimately enhancing their resilience against evolving cyber threats.
Implement Compliance Measures for Regulatory Standards
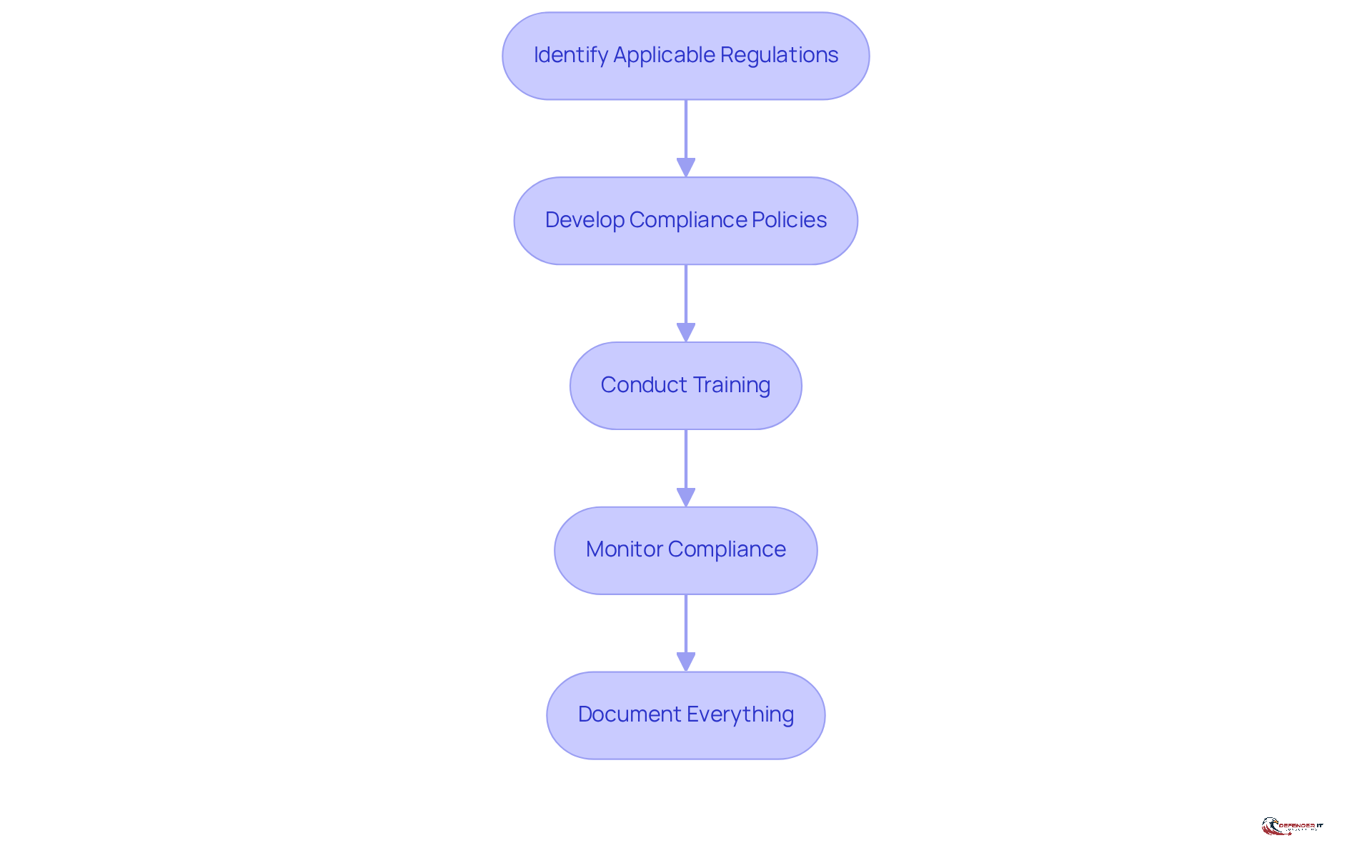
Organizations must implement compliance measures to effectively align with regulatory standards. This is crucial for fulfilling obligations and minimizing the risk of penalties. Key steps include:
- Identify Applicable Regulations: Determine which regulations pertain to your entity, such as GDPR, based on the nature of your business and the data you handle.
- Develop Policies: Create comprehensive policies that detail how your entity will comply with these regulations. Ensure that these policies are communicated to all employees.
- Provide Training: Provide regular training sessions for employees on compliance requirements and best practices. This helps to nurture a culture of compliance within the entity.
- Monitor Compliance: Implement monitoring procedures with compliance tools. This can include automated compliance checks and regular audits.
- Maintain Documentation: Keep thorough documentation, including policies, training records, and audit results. This documentation is essential for demonstrating compliance during audits.
By adhering to these steps, entities can guarantee they fulfill regulatory obligations and minimize the chance of non-compliance penalties.
Adopt Risk Mitigation Strategies for Enhanced Security
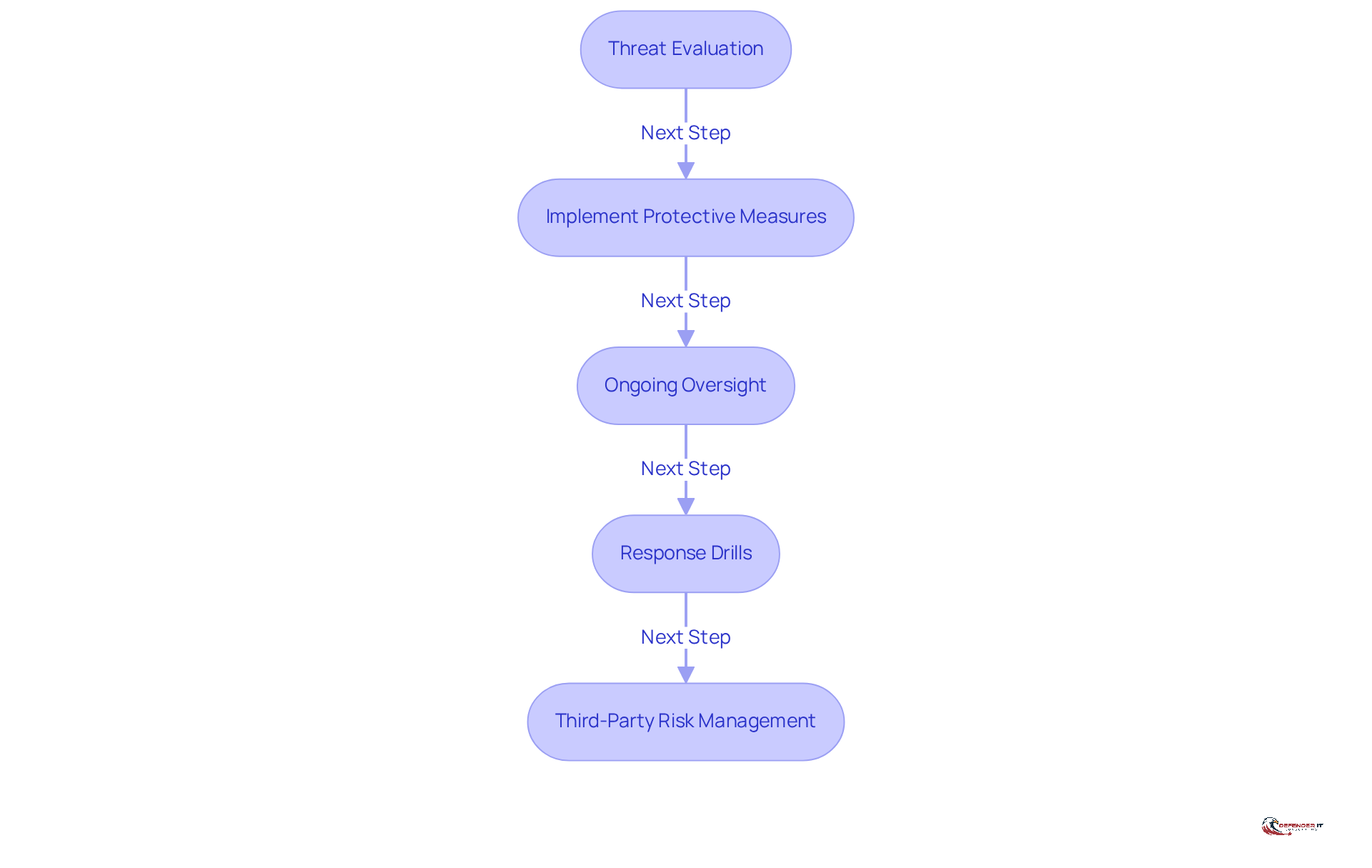
To effectively mitigate risks in 2026, organizations should adopt the following strategies:
- Threat Evaluation: Identify threats and dangers to the enclave security, including both internal and external challenges. This proactive strategy is crucial, as 57% of organizations indicate that new challenges are arising more quickly than they can be managed.
- Implement Protective Measures: Based on the findings from risk assessments, implement robust firewalls, intrusion detection systems (IDS), and endpoint protection solutions. Effective layered detection, including cloud-based protective tools, is essential for safeguarding against evolving threats, particularly as technology advances.
- Ongoing Oversight: Establish continuous monitoring. Utilizing information and event management (SIEM) systems can enhance visibility and enable faster risk detection, which 80% of respondents believe provides a competitive advantage.
- Response Drills: Regularly conduct training exercises to react effectively to security events. This practice minimizes the impact of breaches, as organizations that contained insider incidents within 31 days incurred significantly lower costs-averaging $10.6 million compared to $18.7 million for those taking longer.
- Vendor Management: Assess and manage risks associated with third-party vendors who may have access to the enclave. Ensure that these vendors adhere to your safety standards and compliance requirements. With 71% of entities prioritizing safety, health, and wellbeing standards, it is vital to maintain strict oversight to reduce potential vulnerabilities.
By embracing these tactics, companies can significantly diminish their risk exposure and enhance their overall protective stance, ensuring resilience in an increasingly complex threat environment.
Foster Continuous Training and Awareness for Security Personnel
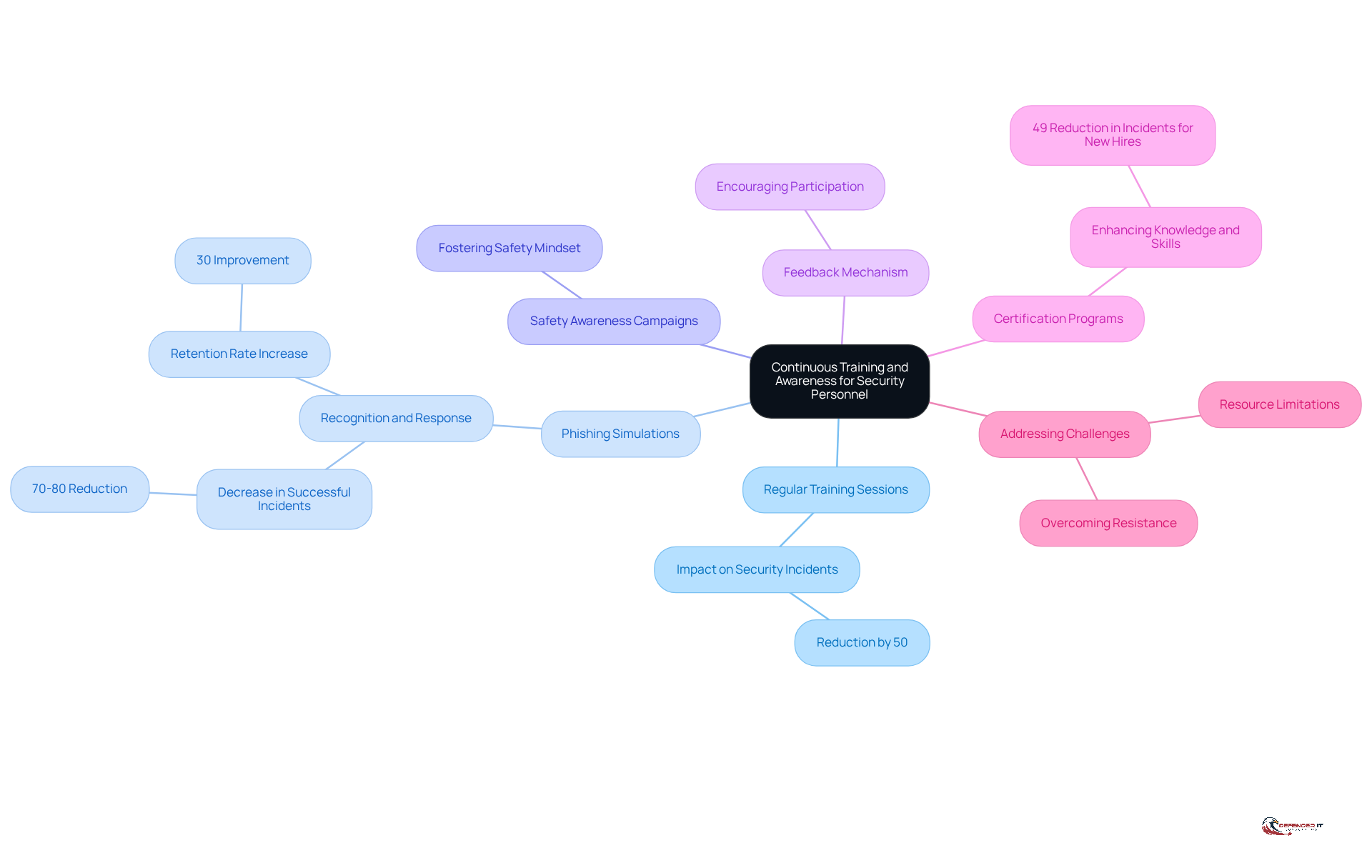
To cultivate a robust culture of security awareness, organizations should prioritize the following training initiatives:
- Training Sessions: Frequent training sessions are essential for personnel to stay informed about the latest and effective mitigation strategies. Research indicates that companies with comprehensive training programs can reduce incidents by as much as 50%.
- Phishing Simulations: Implementing phishing simulations allows organizations to assess employees’ ability to recognize and respond to phishing attempts. These simulations should mirror real-world tactics and adapt over time. Organizations that utilize interactive training report a 30% increase in retention rates. Furthermore, simulations can decrease successful phishing incidents by 70 to 80%, particularly when combined with regular reinforcement drills.
- Awareness Campaigns: Launching campaigns that emphasize essential safety practices fosters a culture of safety among employees. Engaging content and consistent updates are crucial for maintaining awareness of relevant safety issues.
- Feedback Systems: Establishing a feedback system empowers employees to report safety concerns or suggest improvements. This approach encourages active participation and accountability within the safety culture, highlighting the importance of shared awareness.
- Certification Programs: Encouraging personnel to pursue certification enhances their cybersecurity knowledge and skills. Organizations that integrate safety training into their onboarding process experience a 49% reduction in incidents involving new hires.
- Implementation Challenges: It is vital to recognize potential challenges in implementing training initiatives, such as employee resistance or resource limitations, which may impede the effectiveness of training programs. By anticipating these challenges, organizations can devise strategies to address them.
By prioritizing continuous training and awareness, organizations empower their security personnel to effectively combat threats and maintain a resilient security posture.
Conclusion
Enhancing enclave security is paramount for organizations aiming to protect sensitive data and comply with regulatory standards. A comprehensive approach that integrates core security practices, compliance measures, and risk mitigation strategies is essential. This multifaceted framework not only safeguards data but also fortifies organizations against evolving cyber threats.
Key practices include:
- Implementing strict access controls
- Robust data encryption
- Conducting regular audits to identify vulnerabilities
Furthermore, developing compliance policies and providing ongoing training for personnel are vital steps in fostering a culture of security awareness. By addressing both internal and external risks through continuous oversight and proactive measures, organizations can significantly reduce their exposure to potential threats.
The significance of enhancing enclave security cannot be overstated. As cyber threats grow increasingly sophisticated, organizations must prioritize these best practices to protect sensitive information and maintain compliance with regulatory requirements. By investing in a strong security posture and cultivating a culture of awareness, organizations will not only shield themselves but also build resilience against future challenges in the ever-evolving landscape of cybersecurity.
Frequently Asked Questions
What are the core security practices recommended for enclave environments?
The core security practices for enclave environments include access control, data encryption, network segmentation, regular audits, and developing an event response plan.
How does access control enhance enclave security?
Access control limits who can enter the enclave by employing role-based access control (RBAC), ensuring only authorized personnel access sensitive information, which reduces the likelihood of insider threats.
Why is data encryption important in enclave environments?
Data encryption protects sensitive information by encrypting data both at rest and in transit, using robust standards like AES-256. It helps safeguard against unauthorized access and can reduce the time and costs associated with data breaches.
What role does network segmentation play in enclave security?
Network segmentation isolates the enclave from other network segments, minimizing exposure to potential threats through the use of firewalls and virtual private networks (VPNs).
Why are regular audits necessary for enclave security?
Regular audits assess safety and vulnerability, helping organizations identify and remediate potential weaknesses in security measures. Continuous monitoring is crucial to quickly identify and contain breaches, which can save significant costs.
What should an event response plan include for enclave environments?
An event response plan should outline procedures for detecting, addressing, and recovering from security events within the enclave. This preparedness is essential due to the high percentage of cyber incidents attributed to human error.
How can implementing these practices benefit organizations?
Implementing these practices creates a secure environment that protects sensitive data, complies with regulatory requirements, and enhances resilience against evolving cyber threats.
List of Sources
- Establish Core Security Practices for Enclave Environments
- Protecting Sensitive Data with Secure Data Enclaves | Digital Government: Research and Practice (https://dl.acm.org/doi/10.1145/3643686)
- Cyber Security Best Practices for 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-best-practices)
- 2026 DoD Secure Enclave Guidance Validates Data-Centric Security for CMMC (https://virtru.com/blog/compliance/cmmc/secure-enclaves-dod-guidance)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Key Cyber Security Statistics for 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-statistics)
- Implement Compliance Measures for Regulatory Standards
- Compliance News & Updates | HIPAA, GDPR, PCI DSS, SOC 2 | PoliWriter (https://poliwriter.com/news?framework=nist-csf)
- Cybersecurity Compliance by Industry | HIPAA, PCI DSS and GDPR (https://bitlyft.com/resources/cybersecurity-compliance-by-industry-choosing-a-framework-that-fits)
- Global Privacy Trends and Best Practices for Compliance in 2026 | Schellman (https://schellman.com/blog/privacy/global-privacy-compliance-trends-in-2026)
- Understanding IT Compliance: Key Regulations for 2026 | Prime Secured (https://primesecured.com/it-compliance-key-regulations-2026)
- SEC’s new cyber-security rules put boards on the hook | Governance Intelligence (https://governance-intelligence.com/regulatory-compliance/secs-new-cyber-security-rules-put-boards-hook)
- Adopt Risk Mitigation Strategies for Enhanced Security
- Cyber Risk Trends for 2026: Building Resilience, Not Just Defenses (https://securityforum.org/in-the-news/cyber-risk-trends-for-2026)
- 50+ Risk Management Statistics to Know in 2026 (https://secureframe.com/blog/risk-management-statistics)
- Key Risk Management Statistics and Insights for 2026 (https://continuity2.com/blog/risk-management-statistics)
- The Top Cybersecurity Threats in 2026 & How to Prevent Them | Prime Secured (https://primesecured.com/top-cybersecurity-threats-2026-and-prevention)
- Foster Continuous Training and Awareness for Security Personnel
- Industry News 2026 Crafting Better Phishing Simulations A Call for Innovation in Cybersecurity (https://isaca.org/resources/news-and-trends/industry-news/2026/crafting-better-phishing-simulations-a-call-for-innovation-in-cybersecurity)
- Effective Security Awareness Training | Elevate Cyber Defense in 2026 (https://trustcloud.ai/risk-management/how-effective-security-awareness-training-elevates-cybersecurity-in-your-organization)
- What Every Company Needs To Know About Cybersecurity In 2026 (https://forbes.com/sites/chuckbrooks/2025/12/31/what-every-company-needs-to-know-about-cybersecurity-in-2026)
- Why Cybersecurity Training is the Smartest Investment for Organization in 2026 (https://uscsinstitute.org/cybersecurity-insights/blog/why-cybersecurity-training-is-the-smartest-investment-for-organization-in-2026)