Introduction
The integrity of an organization’s digital landscape is increasingly threatened by evolving cyber risks, necessitating robust vulnerability assessments. This article outlines five key steps that can significantly enhance how organizations identify and tackle security weaknesses. Organizations often struggle to keep pace with the evolving landscape of cyber threats, leading to potential security gaps. Failure to prioritize and address these vulnerabilities can result in severe financial and reputational damage. Addressing these vulnerabilities is not just a technical necessity; it is a strategic imperative that can safeguard an organization’s future.
Identify Assets and Systems
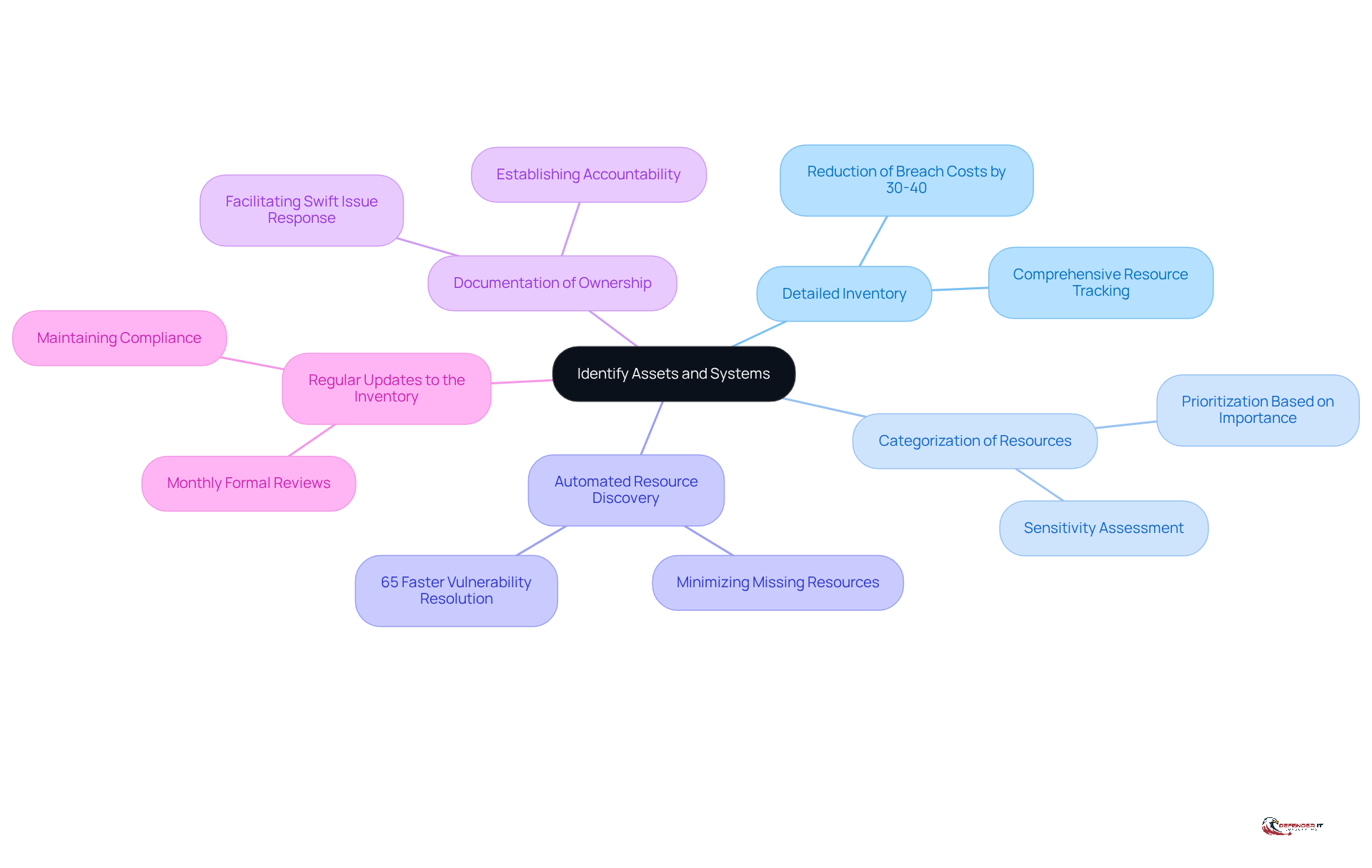
Creating a detailed inventory of all hardware, software, and data resources is essential for effective threat management and risk evaluation. By maintaining a comprehensive inventory of resources, organizations can reduce breach expenses by 30-40% compared to unmonitored resources.
Categorization of Resources: It is important to categorize resources based on their importance and sensitivity. This prioritization aids in directing vulnerability assessment cyber security evaluations toward the most significant areas. Understanding which resources are essential to operations enables organizations to allocate resources efficiently.
Automated Resource Discovery: Implementing automated tools for resource discovery is crucial for capturing all components within the IT environment. This approach minimizes the risk of missing resources, particularly in complex infrastructures where shadow IT may be present. Organizations that invest in proper resource monitoring can identify and resolve weaknesses 65% faster than those that do not.
Documentation of Ownership: Clearly documenting the location and ownership of each item establishes accountability. This practice not only facilitates better management but also enhances the ability to respond swiftly to issues identified during a vulnerability assessment in cyber security. The Equifax breach illustrates the risks associated with lacking ownership of resources, emphasizing the necessity for clear responsibility in resource management.
Regular Updates to the Inventory: It is crucial to regularly update the inventory to reflect changes in the IT landscape. Ongoing observation and revisions are vital for preserving a precise perspective of the resource landscape, which is crucial for prompt risk evaluations and adherence to regulatory obligations. Formal reviews of asset inventories should be conducted monthly for critical environments to ensure ongoing accuracy and accountability.
Conduct Vulnerability Scan
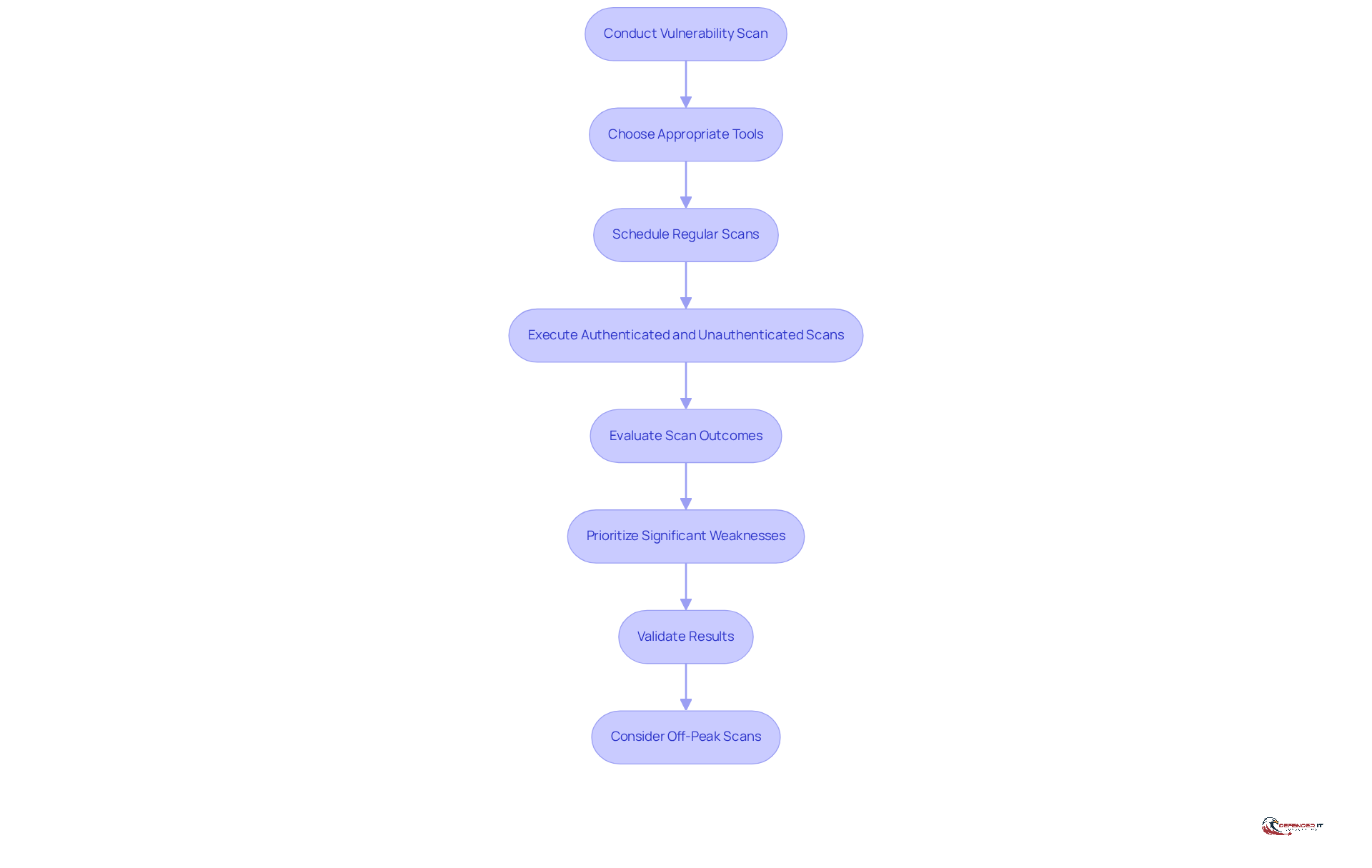
Choosing the appropriate tools for [[vulnerability assessment in cyber security](https://defenderit.consulting)](https://defenderit.consulting) is essential for maintaining a robust security posture in your organization. Choose tools tailored to your environment, such as network-based options like Nessus, Acunetix, and OpenVAS for infrastructure, along with web application scanners for online platforms.
It is advisable to schedule vulnerability assessment cyber security scans regularly, ideally on a monthly or quarterly basis, to ensure your security posture remains current and effective against evolving threats. Conducting a vulnerability assessment in cyber security through comprehensive scans is essential to ensure that all identified assets and systems are included, thereby preventing any critical areas from being overlooked.
Execute both authenticated and unauthenticated scans during a vulnerability assessment in cyber security to reveal a broad spectrum of security flaws, from configuration problems to access control weaknesses. It is important to carefully examine and evaluate scan outcomes during a vulnerability assessment in cyber security to prioritize and address significant weaknesses, concentrating on those that present the greatest threat to your organization. Furthermore, validate results and perform manual testing to confirm weaknesses, and consider arranging scans during off-peak hours to minimize disruption.
Prioritize Identified Risks
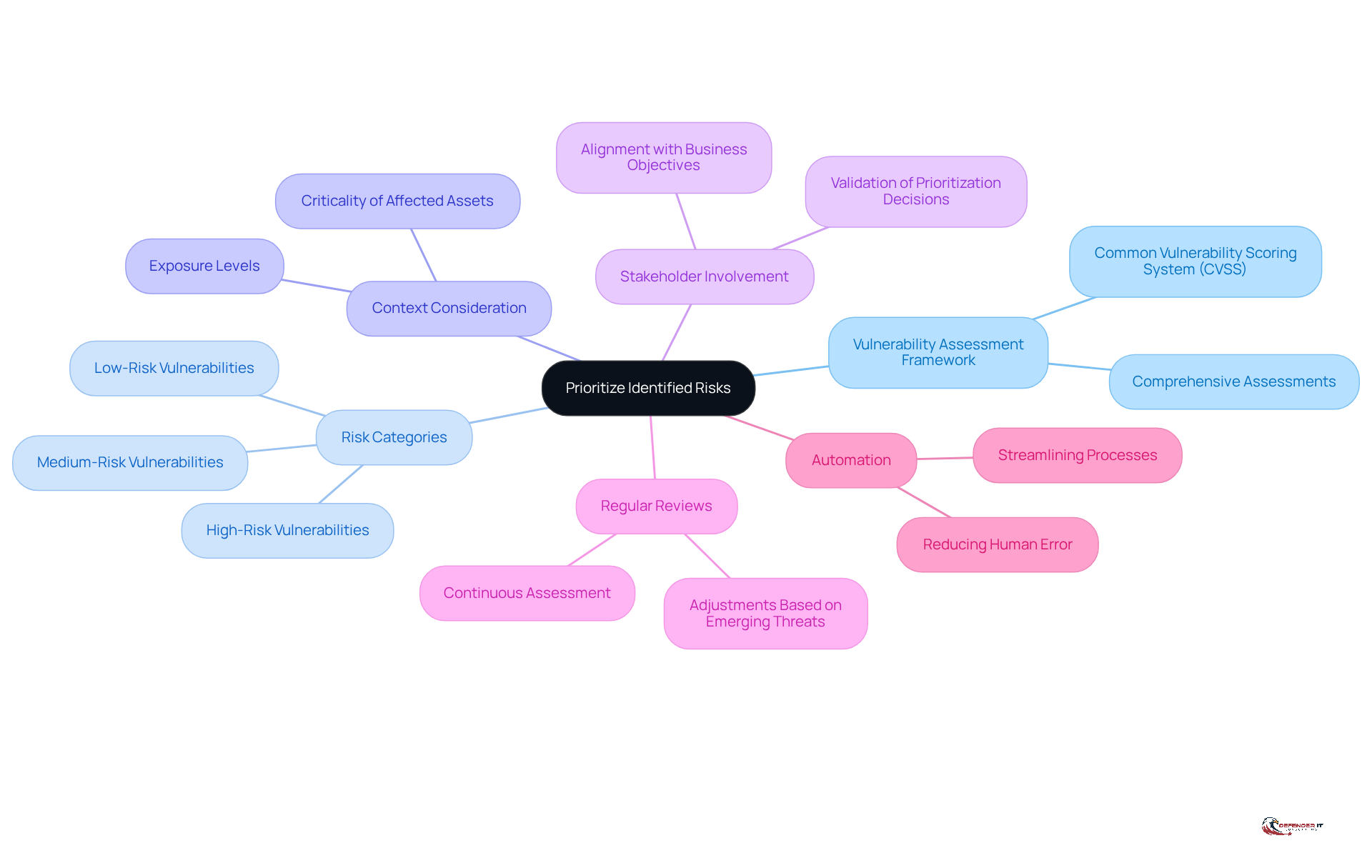
Establishing a robust framework for vulnerability assessment in cyber security is crucial for organizations to effectively evaluate and address cybersecurity weaknesses. One effective method for a vulnerability assessment in cyber security is the Common Vulnerability Scoring System (CVSS), which helps assess vulnerabilities based on their severity and potential impact on the organization.
Categorizing weaknesses into high, medium, and low-risk groups enables focused remediation actions, ensuring that the most critical issues are prioritized first. The incident affecting 20,000 users due to harmful Chrome extensions highlights the urgent need for a robust vulnerability assessment in cyber security framework to address and mitigate such vulnerabilities.
It’s essential to consider the context of each weakness, such as the criticality of affected assets and their exposure levels, to prioritize effectively. Involving key stakeholders in the validation of prioritization decisions ensures that cybersecurity efforts align with broader business objectives and risk management strategies. This alignment is particularly important in light of new SEC rules requiring C-level executives to disclose material cyber impacts in their reporting.
Regular reviews and adjustments of prioritization based on emerging threats and newly identified weaknesses are vital for maintaining an adaptive and proactive cybersecurity posture. Emphasizing automation can streamline this process, reducing human error and enhancing efficiency.
By fostering continuous assessment and collaboration, organizations can adapt to the evolving cybersecurity landscape and safeguard their assets against emerging threats.
Implement Security Fixes
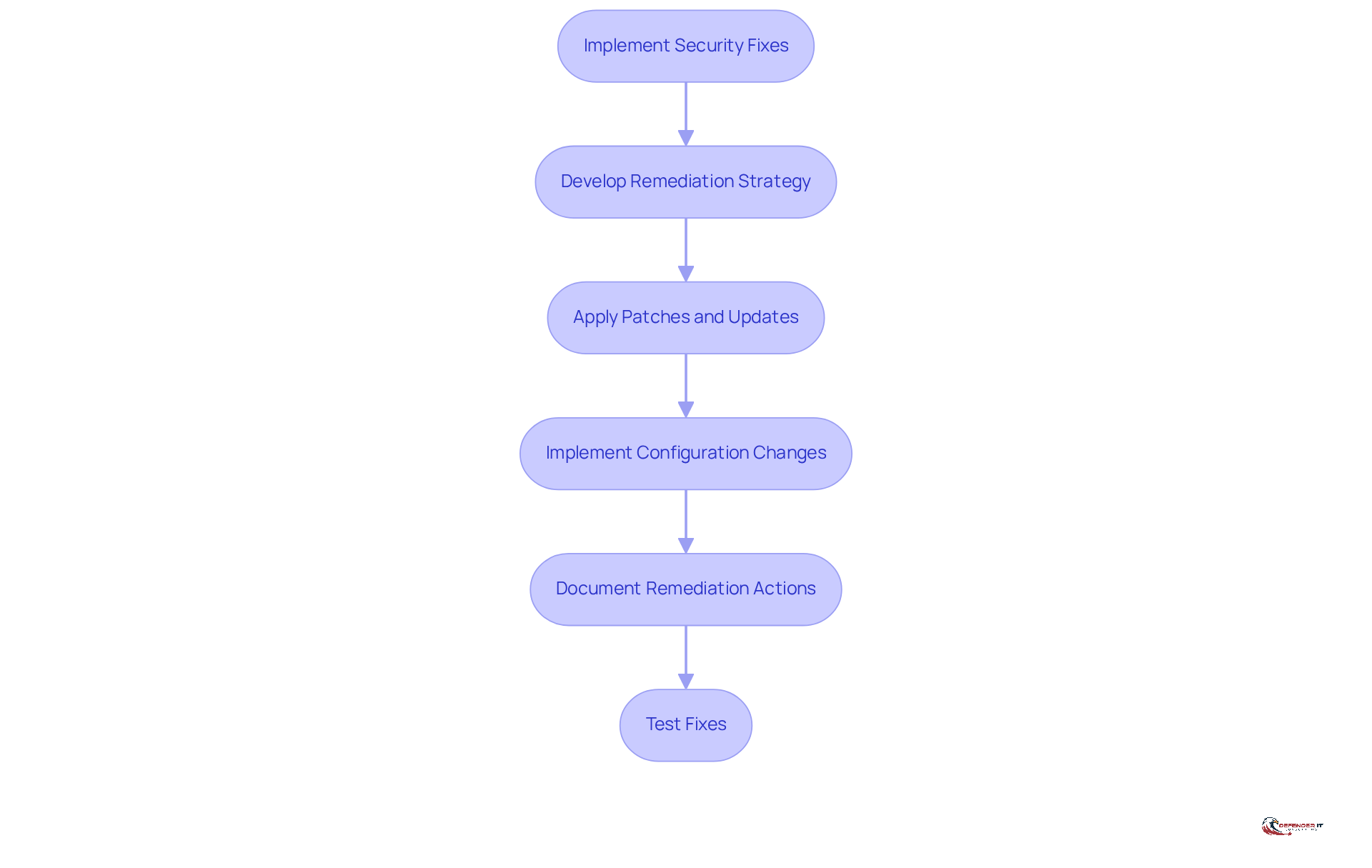
Addressing software weaknesses is critical to maintaining system integrity and security. Developing a comprehensive remediation strategy is essential for addressing each identified weakness effectively.
Timely application of patches and updates is crucial for mitigating software weaknesses and enhancing security. Implementing necessary configuration changes and protective measures is vital for strengthening system defenses.
Thorough documentation of all remediation actions is essential for accountability and serves as a reference for future actions. Testing fixes is critical to ensure that weaknesses are effectively mitigated while avoiding the introduction of new issues.
Failure to implement a robust remediation strategy can lead to significant vulnerabilities and potential breaches.
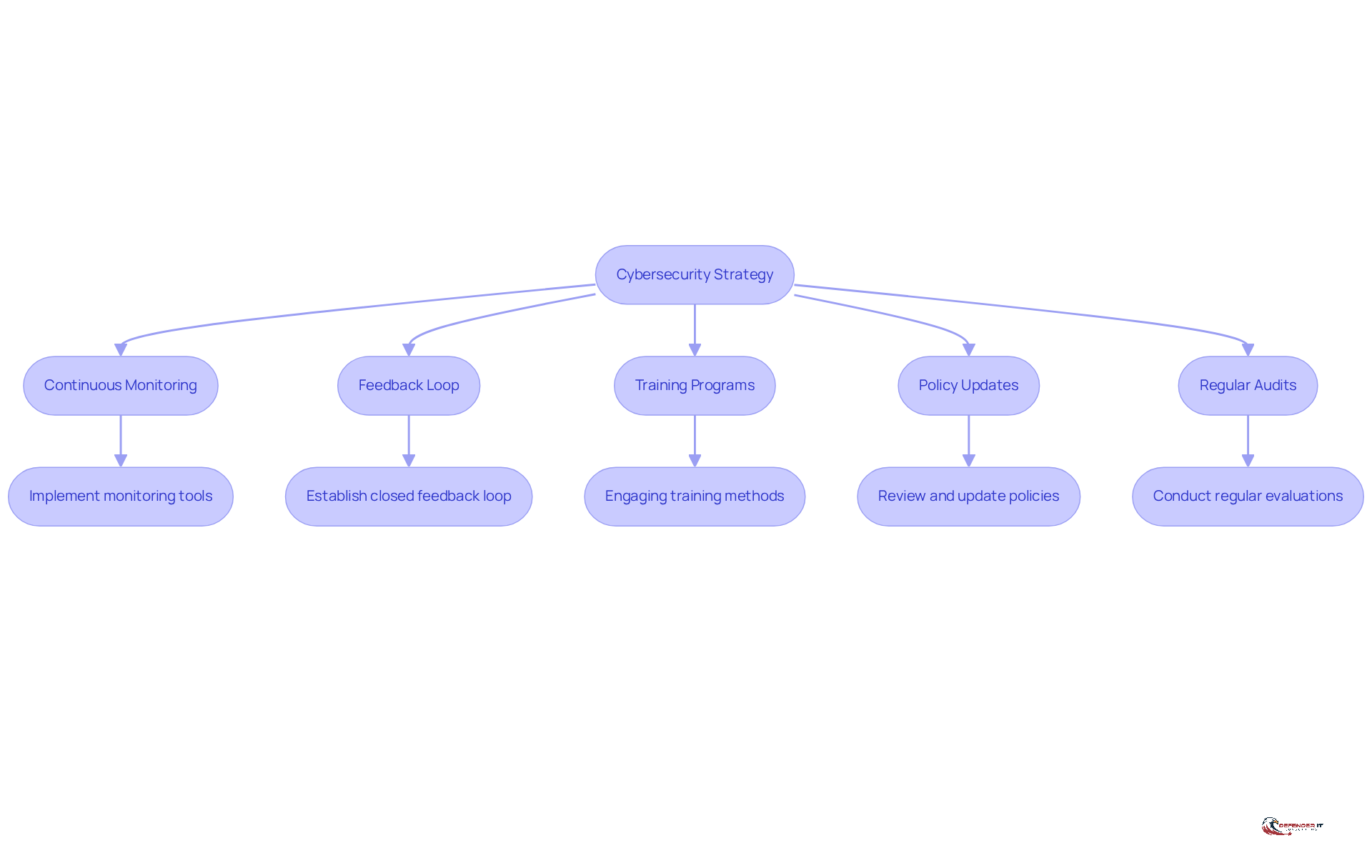
Ensure Continuous Monitoring and Improvement
In an era where cyber threats are increasingly sophisticated, organizations must adopt proactive measures to safeguard their assets. Implement continuous monitoring tools to detect vulnerabilities and threats in real-time, ensuring that response teams can act swiftly to emerging risks. Organizations that implement continuous exposure management significantly reduce their risk of breaches, being three times less likely to experience such incidents, underscoring the critical need for proactive measures in today’s threat landscape.
Establishing a feedback loop is crucial for learning from past incidents and enhancing future assessments. Without a closed feedback loop, the cybersecurity process stalls, making it essential to connect incident response with configuration baselines. This connection enables quick updates to detection signatures and improves overall effectiveness.
Regular training and awareness programs are essential for staff to effectively recognize and respond to threats. Statistics indicate that 79% of employees complete cybersecurity training due to mandatory compliance, yet only 12% are motivated by real-world examples. This gap emphasizes the necessity for engaging training that connects with employees, as effective training is vital for enhancing overall protective measures.
Regularly reviewing and updating security policies and procedures is vital to adapt to the evolving threat landscape. Ongoing monitoring tools offer real-time insight into misconfigurations and shadow IT risks, ensuring that policies stay pertinent and effective in addressing existing weaknesses.
Engaging in regular audits and evaluations is crucial for assessing the effectiveness of the risk management program. Routine vulnerability assessment cyber security helps organizations recognize flaws before intruders can exploit them, making it a vital component of a strong security strategy. Integrating vulnerability management with remediation plans allows for informed decision-making based on insights gained from a vulnerability assessment in cyber security regarding real-world risks. Ultimately, a robust risk management program is not just a regulatory requirement; it is essential for the survival of organizations in a perilous digital landscape.
Conclusion
In an era where cyber threats are increasingly sophisticated, effective vulnerability assessments are essential for safeguarding organizational assets. Organizations can significantly enhance their resilience against cyber threats by following essential steps:
- Identifying assets and systems
- Conducting vulnerability scans
- Prioritizing identified risks
- Implementing security fixes
- Ensuring continuous monitoring and improvement
The article emphasizes the importance of a comprehensive asset inventory, regular vulnerability scanning, and a structured approach to risk prioritization. Each step plays a critical role in identifying weaknesses, addressing them promptly, and adapting to the ever-evolving threat landscape. By implementing these best practices, organizations can mitigate risks and foster a culture of security awareness and proactive management.
The importance of a robust vulnerability assessment process is paramount in today’s digital landscape. It is not merely a compliance requirement; it is a foundational element for any organization striving to thrive in a digital environment fraught with risks. By prioritizing vulnerability assessments, organizations not only protect their assets but also position themselves for success in a digital landscape filled with challenges.
Frequently Asked Questions
Why is creating a detailed inventory of assets and systems important for organizations?
A detailed inventory of hardware, software, and data resources is essential for effective threat management and risk evaluation. It can reduce breach expenses by 30-40% compared to unmonitored resources.
How should resources be categorized for effective vulnerability assessment?
Resources should be categorized based on their importance and sensitivity. This prioritization helps direct vulnerability assessments towards the most significant areas, allowing for efficient resource allocation.
What role does automated resource discovery play in asset management?
Automated tools for resource discovery capture all components within the IT environment, minimizing the risk of missing resources, especially in complex infrastructures. Organizations that invest in proper resource monitoring can identify and resolve weaknesses 65% faster.
Why is documentation of ownership important in resource management?
Documenting the location and ownership of each item establishes accountability, facilitates better management, and enhances the ability to respond swiftly to issues identified during vulnerability assessments.
How often should organizations update their inventory of assets and systems?
Organizations should regularly update their inventory to reflect changes in the IT landscape. Formal reviews of asset inventories should be conducted monthly for critical environments to ensure ongoing accuracy and accountability.
What tools are recommended for conducting vulnerability assessments?
Recommended tools include network-based options like Nessus, Acunetix, and OpenVAS for infrastructure, as well as web application scanners for online platforms.
How often should vulnerability assessments be scheduled?
Vulnerability assessments should ideally be scheduled regularly, on a monthly or quarterly basis, to maintain an effective security posture against evolving threats.
What types of scans should be executed during a vulnerability assessment?
Both authenticated and unauthenticated scans should be executed to reveal a broad spectrum of security flaws, including configuration problems and access control weaknesses.
What should be done with the results of vulnerability scans?
Scan outcomes should be carefully examined and evaluated to prioritize and address significant weaknesses, concentrating on those that present the greatest threat. Results should also be validated through manual testing.
When is the best time to arrange vulnerability scans to minimize disruption?
It is advisable to arrange scans during off-peak hours to minimize disruption to organizational operations.
List of Sources
- Identify Assets and Systems
- Vulnerability Risk Assessment: The Role of Asset Management | Lansweeper (https://lansweeper.com/blog/cybersecurity/why-cybersecurity-asset-management-is-crucial-for-vulnerability-assessment)
- Asset inventory is foundational to security programs – runZero (https://runzero.com/blog/asset-inventory-is-foundational)
- CISA, partners release asset inventory guidance to protect OT systems from cyberattacks, bolster resilience – Industrial Cyber (https://industrialcyber.co/cisa/cisa-partners-release-asset-inventory-guidance-to-protect-ot-systems-from-cyberattacks-bolster-resilience)
- Asset Inventory Management: Key to Effective Vulnerability Management (https://armorcode.com/blog/asset-inventory-management-key-to-effective-vulnerability-management)
- Asset Inventory: The Strategic Foundation of Modern Vulnerability Management (https://linkedin.com/pulse/asset-inventory-strategic-foundation-modern-debra-anderson-lvh7c)
- Conduct Vulnerability Scan
- The Importance of Vulnerability Scanning for Cybersecurity: A Comprehensive Guide | Databank (https://databank.com/resources/blogs/the-importance-of-vulnerability-scanning-for-cybersecurity-a-comprehensive-guide)
- Continuous Vulnerability Assessment & Scanning | Why It Matters | Qualys (https://blog.qualys.com/product-tech/2025/04/18/the-importance-of-continuous-vulnerability-assessment-in-modern-it-environments)
- The Importance of Regular Vulnerability Scanning | Security Tower (https://security-tower.nl/en/the-importance-of-regular-vulnerability-scanning)
- 8 Reasons to Conduct Regular Vulnerability Scans (https://levelblue.com/blogs/levelblue-blog/8-reasons-to-conduct-regular-vulnerability-scans)
- Why Vulnerability Scans Matter in 2025 | Cybersecurity Essentials (https://hipaavault.com/resources/hipaa-compliant-hosting-insights/vulnerability-scans-cybersecurity)
- Prioritize Identified Risks
- Prioritizing cyber risk and centralizing response efforts are crucial for safeguarding critical infrastructure | Federal News Network (https://federalnewsnetwork.com/commentary/2025/06/prioritizing-cyber-risk-and-centralizing-response-efforts-are-crucial-for-safeguarding-critical-infrastructure)
- Cyber Security Risk Outlook 2026 | Threats, Resilience & Risk Insights | LRQA (https://lrqa.com/en-us/resources/cyber-security-risk-outlook-2026-cyber-risk-trends-report)
- 50+ Risk Management Statistics to Know in 2026 (https://secureframe.com/blog/risk-management-statistics)
- How To Prioritize Cyber Risk Management (https://forbes.com/councils/forbesbusinesscouncil/2024/07/16/cybersecurity-incidents-can-impact-a-companys-valuation-how-to-prioritize-cyber-risk-management)
- How to Prioritize Cybersecurity Spending: A Risk-Based Strategy for the Highest ROI (https://thehackernews.com/2024/02/why-risk-based-approach-to.html)
- Implement Security Fixes
- What is security patching? Best practices and importance (https://acronis.com/en/blog/posts/security-patching-complete-guide)
- Timely Patching Reduces System Compromises (https://cisecurity.org/insights/blog/timely-patching-reduces-system-compromises)
- Why Patching Cadence Matters for Cybersecurity Risk | Bitsight (https://bitsight.com/blog/why-patching-cadence-matters-cybersecurity-risk)
- Patching: A Necessity in a World of Ransomware (https://nlc.org/article/2023/11/29/patching-a-necessity-in-a-world-of-ransomware)
- Understanding Patches and Software Updates | CISA (https://cisa.gov/news-events/news/understanding-patches-and-software-updates)
- Ensure Continuous Monitoring and Improvement
- How Feedback Loops Strengthen Your Cyber Defenses (https://forbes.com/councils/forbestechcouncil/2024/03/26/how-feedback-loops-strengthen-your-cyber-defenses)
- Continuous Threat Exposure Management Trends & Evolution in 2026 (https://slcyber.io/blog/how-continuous-threat-exposure-management-is-evolving-in-2026)
- The Critical Role of Feedback Loops in the NIST Cybersecurity Framework (https://hoop.dev/blog/the-critical-role-of-feedback-loops-in-the-nist-cybersecurity-framework)
- Security Awareness Training: USA 2025 Statistics | Infrascale (https://infrascale.com/security-awareness-training-statistics-usa)
- 11 Benefits of Vulnerability Management | SentinelOne (https://sentinelone.com/cybersecurity-101/cybersecurity/benefits-of-vulnerability-management)