Introduction
In today’s interconnected landscape, ensuring the security of network infrastructures is crucial for organizations, especially those operating in regulated sectors such as finance and healthcare. Managed network security services (MNSS) present a strategic solution, delivering expert oversight and advanced technologies to safeguard sensitive data while enabling businesses to focus on their core operations.
As cyber threats continue to evolve and compliance requirements grow more stringent, organizations must consider how to ensure that their managed services are not only effective but also aligned with the latest industry standards.
This article explores key strategies for optimizing the effectiveness of managed network security services, addressing compliance challenges, and promoting a culture of continuous improvement.
Define Managed Network Security Services
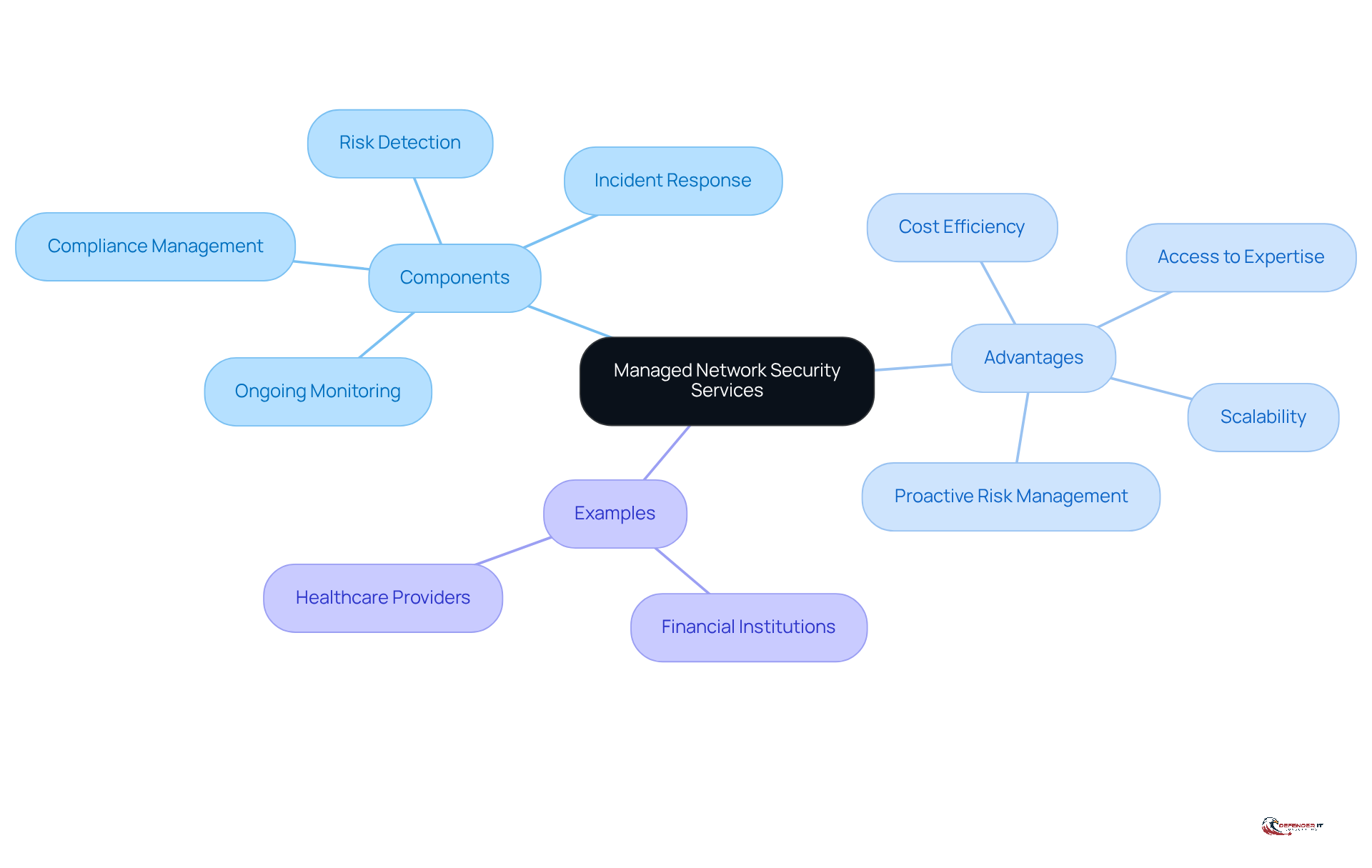
Managed network security service represents a comprehensive suite of cybersecurity solutions offered by specialized firms to safeguard a company’s network infrastructure. These services typically include ongoing monitoring, risk detection, incident response, and compliance management. By outsourcing these functions to experts, organizations can leverage advanced technologies and methodologies to protect their digital assets against evolving cyber threats. The managed network security service not only enhances security posture but also enables businesses to focus on their core operations without the complexities of managing intricate security protocols internally. For instance, a financial institution may utilize MNSS to ensure compliance with stringent regulations while effectively mitigating risks associated with data breaches.
The advantages of the managed network security service (MNSS) are particularly significant for businesses operating in highly regulated sectors, such as finance and healthcare. Financial institutions, for example, often depend on managed network security service to ensure adherence to strict regulations while simultaneously addressing risks linked to data breaches. This approach not only strengthens their security stance but also enables them to focus on core operations without the challenges of managing complex protective protocols internally.
Outsourcing network security services provides several key advantages:
- Cost Efficiency: Organizations can achieve a higher level of security at a lower cost compared to maintaining in-house teams, as outsourced providers benefit from economies of scale.
- Access to Expertise: Collaborating with managed service providers grants access to specialized skills and knowledge that may be lacking internally, particularly in areas such as incident response and compliance.
- Scalability: As businesses expand, their cybersecurity needs evolve. MNSS can easily scale to meet these changing requirements, ensuring that security measures remain robust without significant additional investment.
- Proactive Risk Management: With 24/7 monitoring and response capabilities, outsourced services can identify and address threats in real-time, significantly reducing the potential impact of cyber incidents.
In summary, a managed network security service not only strengthens an organization’s defenses against cyber threats but also enables businesses to operate more efficiently by allowing them to focus on their primary objectives.
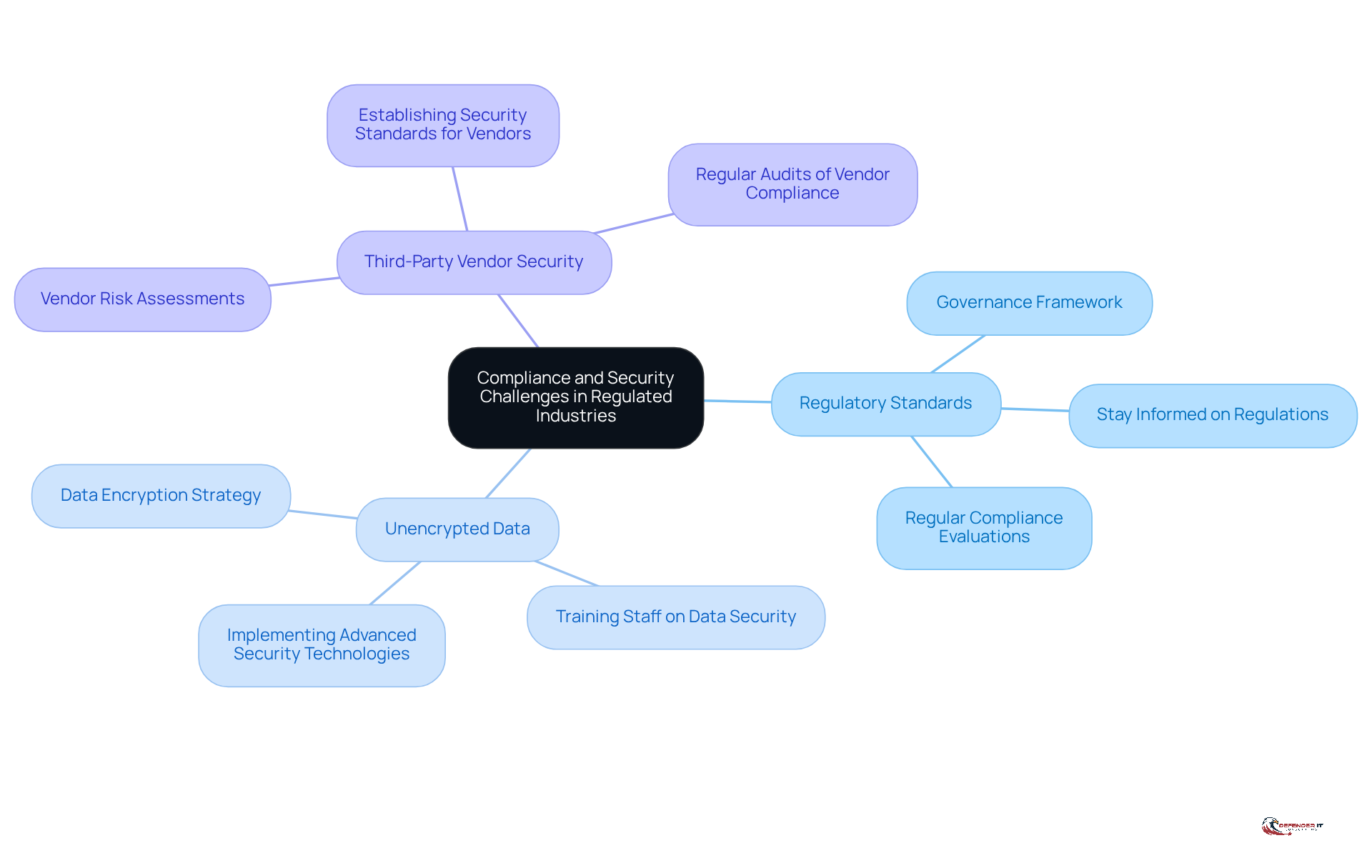
Address Compliance and Security Challenges in Regulated Industries
Organizations operating in regulated sectors like finance and healthcare encounter stringent regulatory demands that complicate their cybersecurity initiatives. The primary challenges include:
- Navigating a complex array of regulatory standards
- Managing unencrypted data
- Ensuring the security of third-party vendors
Additionally, the evolving regulatory landscape, shaped by advancements in AI and digital innovation, further complicates these issues.
To effectively tackle these challenges, organizations should establish a comprehensive governance framework that aligns protective measures with regulatory requirements. For example, healthcare providers can adopt a robust data encryption strategy to protect patient information while complying with HIPAA regulations. Regular evaluations and reviews are also crucial for identifying compliance and protection gaps, enabling organizations to proactively mitigate potential vulnerabilities.
Given that the average healthcare data breach costs approximately $9.77 million, with operational downtime averaging $1.47 million per incident, this proactive approach not only enhances security but also fosters resilience against emerging cyber threats. Furthermore, organizations must stay informed about upcoming regulations, such as the Health Infrastructure Security and Accountability Act, to ensure readiness for future compliance obligations.
Implement Best Practices for Effective Managed Network Security
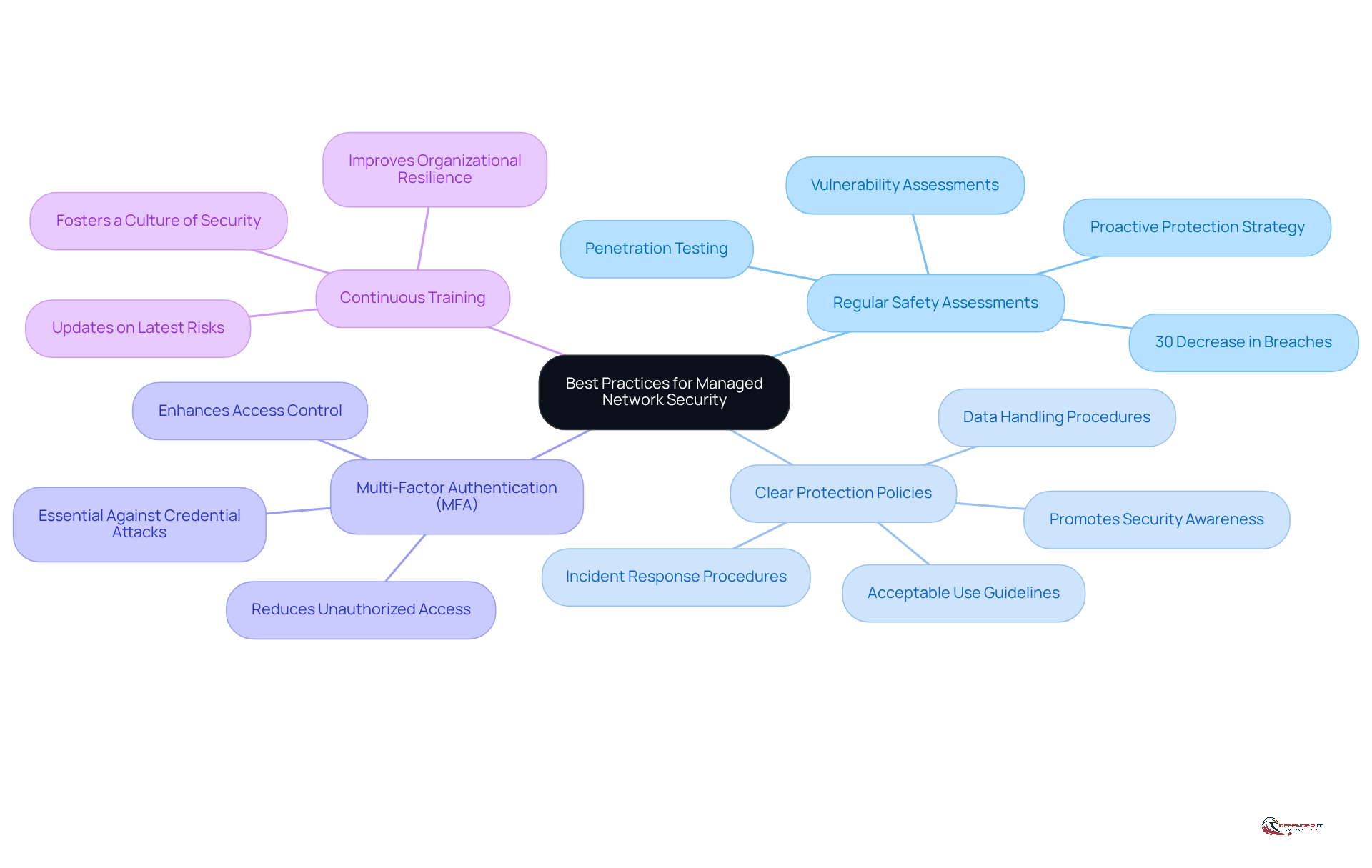
To maximize the effectiveness of managed network security services, organizations should implement several best practices:
- Conduct Regular Safety Assessments: Systematic evaluations of protective posture through vulnerability assessments and penetration testing are essential. These assessments help identify and remediate weaknesses before they can be exploited. Regular evaluations have been demonstrated to decrease successful breaches by 30%, highlighting their significance in a proactive protection strategy. Entities that emphasize regular evaluations report substantial enhancements in their defense stance, showcasing the concrete advantages of this approach.
- Establish Clear Protection Policies: Comprehensive guidelines should outline acceptable use, data handling, and incident response procedures. These policies establish a structure for consistent protection practices throughout the organization, ensuring that all employees comprehend their roles in preserving safety. Clear policies are essential to promoting a culture of awareness regarding protection, as noted by cybersecurity experts.
- Utilize Multi-Factor Authentication (MFA): Implementing MFA significantly enhances access control and reduces the risk of unauthorized access. As cyber risks develop, MFA acts as an essential layer of protection against credential assaults, which continue to be effective due to social engineering strategies. Experts emphasize that MFA is a necessary step in safeguarding sensitive information.
- Engage in Continuous Training: Ongoing education for employees is essential to keep them updated about the latest risks and protective measures. A robust protective culture, nurtured through consistent training, improves organizational resilience against cyber threats. Cybersecurity leaders promote ongoing education as a crucial element of an effective protection strategy.
By following these best practices, organizations can significantly enhance their protective stance and ensure that their managed network security service effectively reduces risks. The dedication to routine evaluations and ongoing enhancement not only safeguards digital assets but also fosters trust with stakeholders, as 72% of consumers are more inclined to trust companies with a robust safety history. Incorporating insights from industry leaders can further enhance the credibility of these practices.
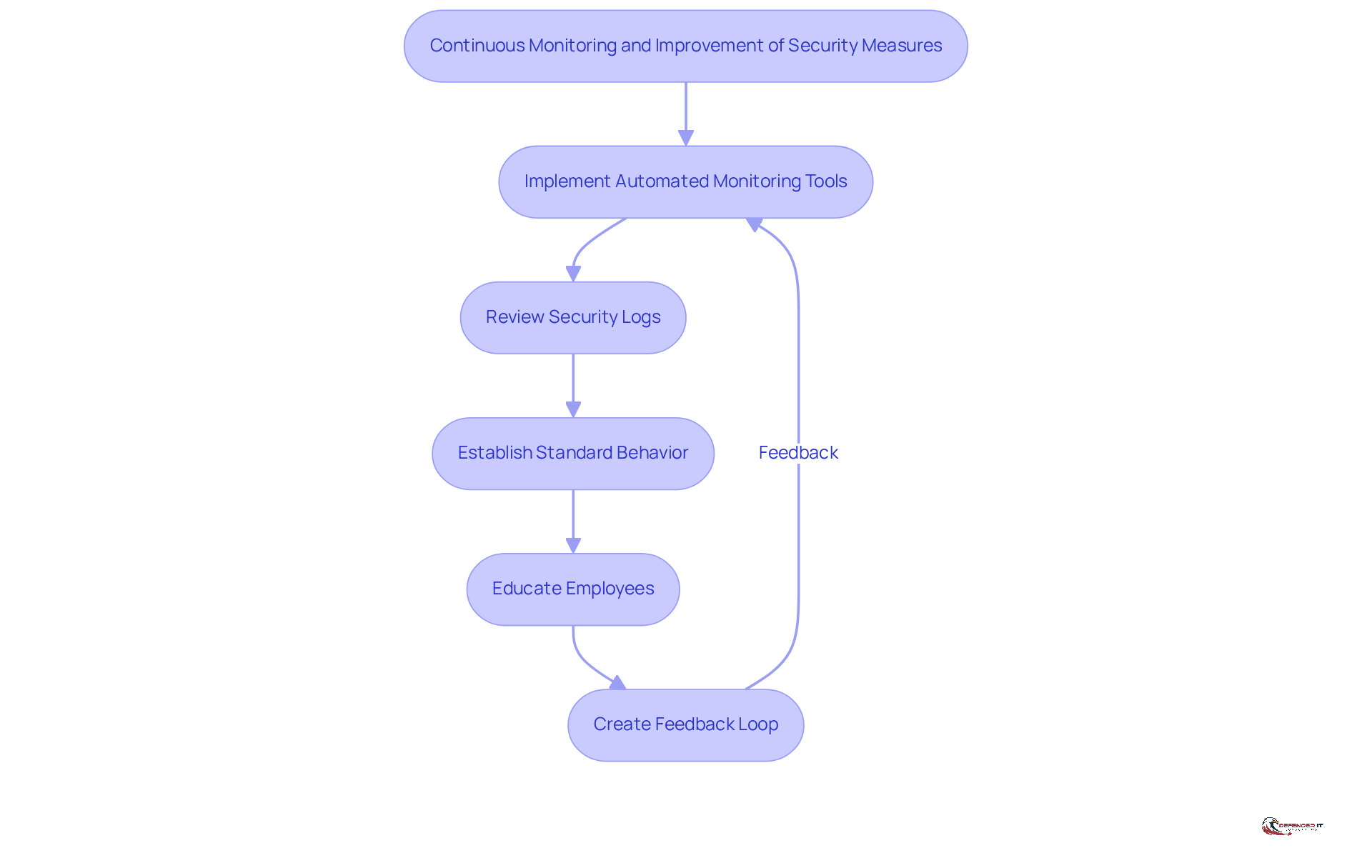
Ensure Continuous Monitoring and Improvement of Security Measures
Continuous monitoring is essential for maintaining a robust cybersecurity posture. Organizations must implement automated monitoring tools, including:
- Security Information and Event Management (SIEM) systems
- Endpoint Detection and Response (EDR) platforms
- Network Traffic Analysis (NTA) tools
These tools provide real-time visibility into network activities and potential risks. Regularly reviewing security logs and alerts is crucial for identifying anomalies that may indicate a security breach. For instance, the 2017 Equifax data breach, where attackers exploited an unpatched vulnerability, highlights the necessity of continuous monitoring to detect such threats early.
Moreover, establishing a standard of typical behavior is vital for effective monitoring, enabling organizations to swiftly recognize deviations. Additionally, educating employees and customers on cybersecurity best practices is essential to reduce overall risk. Creating a feedback loop that incorporates insights gained from incidents is critical for enhancing and advancing protective measures. Conducting thorough post-incident analyses can reveal vulnerabilities and inform future security strategies.
By fostering a culture of continuous improvement, organizations can effectively adapt to the evolving threat landscape and strengthen their defenses against cyber attacks. As cybersecurity experts emphasize, integrating real-time monitoring tools is not merely beneficial; it is a necessity for proactive risk management and compliance with regulatory standards.
Conclusion
Managed network security services (MNSS) are essential for organizations seeking robust protection against the growing complexity of cyber threats. By outsourcing cybersecurity functions, businesses can enhance their security posture while refocusing on core operations. This strategic approach enables organizations to leverage expert knowledge and advanced technologies, ensuring resilience against evolving risks.
Key practices for the successful implementation of MNSS include:
- Conducting regular safety assessments to identify vulnerabilities
- Establishing clear protection policies to guide employee behavior
- Utilizing multi-factor authentication to strengthen access controls
- Engaging in continuous training to keep staff informed about the latest threats
Furthermore, the importance of continuous monitoring and improvement is paramount, highlighting the necessity of real-time visibility and proactive risk management.
In a landscape where cyber threats are perpetually evolving, adopting these best practices is not merely beneficial but essential. Organizations must prioritize the integration of effective managed network security services to protect their digital assets and maintain compliance with regulatory standards. By fostering a culture of vigilance and continuous improvement, businesses can significantly bolster their defenses, build trust with stakeholders, and ensure long-term success in an increasingly complex cybersecurity environment.
Frequently Asked Questions
What are managed network security services (MNSS)?
Managed network security services (MNSS) are comprehensive cybersecurity solutions offered by specialized firms to protect a company’s network infrastructure. These services include ongoing monitoring, risk detection, incident response, and compliance management.
What are the benefits of outsourcing network security services?
Outsourcing network security services offers several advantages, including cost efficiency, access to specialized expertise, scalability to meet evolving security needs, and proactive risk management through 24/7 monitoring and response capabilities.
How do managed network security services enhance security posture?
MNSS enhances security posture by leveraging advanced technologies and methodologies to protect digital assets against evolving cyber threats, allowing organizations to focus on their core operations without the complexities of managing security protocols internally.
Which sectors benefit most from managed network security services?
Businesses operating in highly regulated sectors, such as finance and healthcare, particularly benefit from MNSS due to the need for strict compliance with regulations and the mitigation of risks associated with data breaches.
Can managed network security services scale with a business?
Yes, managed network security services can easily scale to meet changing cybersecurity needs as businesses expand, ensuring that security measures remain robust without significant additional investment.
How does MNSS help organizations with compliance management?
MNSS assists organizations in adhering to stringent regulations by ensuring compliance while addressing risks linked to data breaches, which is especially critical for sectors like finance.
List of Sources
- Define Managed Network Security Services
- The Benefits of Outsourcing Cybersecurity Management (https://amatas.com/blog/the-benefits-of-outsourced-cybersecurity-management)
- 12 Benefits of Outsourced Security Services – ClearNetwork, Inc (https://clearnetwork.com/12-benefits-of-outsourced-security-services)
- Security outsourcing on the rise as CISOs seek cyber relief (https://csoonline.com/article/3593324/security-outsourcing-on-the-rise-as-cisos-seek-cyber-relief.html)
- The Benefits of Outsourcing Network Security to Managed Service Providers (https://easychair.org/publications/preprint/JRbn)
- 7 Benefits of Outsourcing Cybersecurity Services | Huntress (https://huntress.com/blog/7-benefits-of-outsourcing-cybersecurity-services)
- Address Compliance and Security Challenges in Regulated Industries
- 10 Global Compliance Concerns for 2026: How the compliance landscape is transforming – Thomson Reuters Institute (https://thomsonreuters.com/en-us/posts/corporates/10-global-compliance-concerns-2026)
- New Legislation Seeks to Fortify Healthcare Cybersecurity (https://alliant.com/news-resources/article-new-legislation-seeks-to-fortify-healthcare-cybersecurity)
- Cyber Insights 2026: Regulations and the Tangled Mess of Compliance Requirements (https://securityweek.com/cyber-insights-2026-regulations-and-the-tangled-mess-of-compliance-requirements)
- Privacy and Cybersecurity Laws in 2026 Pose Challenges (https://darkreading.com/cyber-risk/navigating-privacy-and-cybersecurity-laws-in-2026-will-prove-difficult)
- HIPAA Updates: New Cybersecurity Rules Challenge Healthcare IT – Medical ITG (https://medicalitg.com/hipaa-compliance/hipaa-cybersecurity-updates-managed-it-support-for-healthcare-healthcare-data-breach-costs)
- Implement Best Practices for Effective Managed Network Security
- The Critical Role of Regular Cybersecurity Assessments in Risk… (https://visualedgeit.com/blog/the-critical-role-of-regular-cybersecurity-assessments-in-risk-management)
- Managed Security Is Getting Harder to Deliver in 2026 – What the Next Wave Looks Like for MSSPs (https://msspalert.com/news/managed-security-is-getting-harder-to-deliver-in-2026-what-the-next-wave-looks-like-for-mssps)
- Cyber Security Best Practices for 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-best-practices)
- The Importance of Regular Cybersecurity Assessments (https://intersourcesinc.com/insights/the-importance-of-regular-cybersecurity-assessments)
- Latest Cybersecurity Best Practices 2026: A Practical Checklist (https://nmsconsulting.com/latest-cybersecurity-best-practices-2026)
- Ensure Continuous Monitoring and Improvement of Security Measures
- The Importance of Continuous Monitoring in Cybersecurity (https://kaluari.com/blog/the-importance-of-continuous-monitoring-in-cybersecurity)
- Why continuous monitoring matters for cybersecurity leaders (https://heightscg.com/2026/04/17/why-continuous-monitoring-matters-cybersecurity-leaders)
- Constant Vigilance: The Importance of Continuous Cybersecurity Monitoring (https://csiweb.com/what-to-know/content-hub/blog/continuous-cybersecurity-monitoring)
- The Importance of Continuous Security Monitoring in Modern IT Environments (https://lynxtechnologypartners.com/blog/the-importance-of-continuous-security-monitoring-in-modern-it-environments)
- Top Cybersecurity Trends of 2026: AI, Zero Trust & Quantum Security (https://eccu.edu/blog/cybersecurity-trends-2026)