Introduction
As cyber threats become increasingly sophisticated, the necessity for proactive security measures is paramount. Organizations are increasingly adopting penetration testing – an essential strategy that simulates cyberattacks to identify vulnerabilities before they can be exploited by malicious actors. However, with numerous providers offering a variety of testing methodologies and services, how can businesses ensure they select the right partner to effectively protect their assets? This article examines the leading penetration testing providers, comparing their offerings and outlining key criteria to assist organizations in making this critical decision.
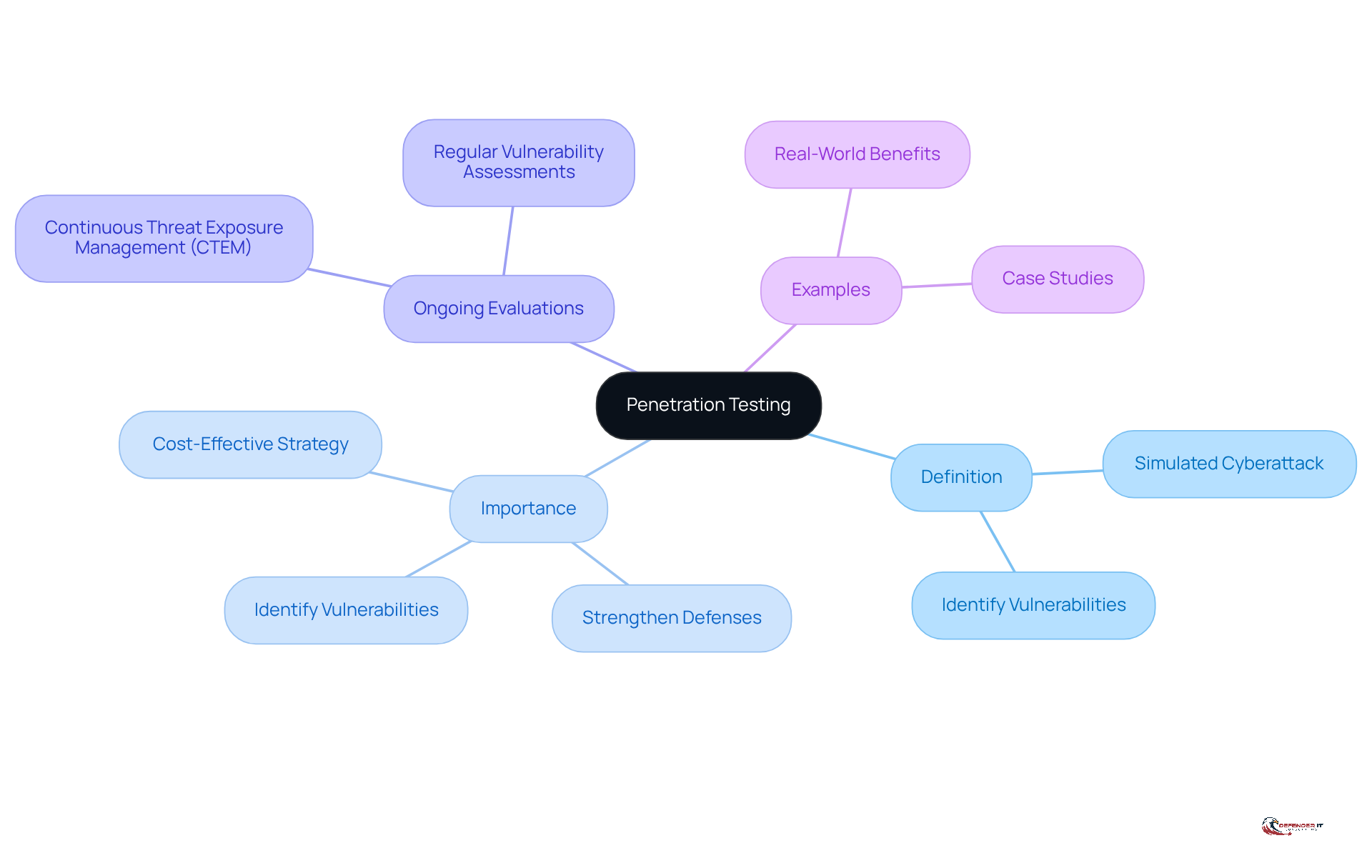
Understanding Penetration Testing: Definition and Importance
Penetration assessment, commonly referred to as ‘pen testing,’ serves as a simulated cyberattack against a computer system, network, or web application. Its primary purpose is to identify vulnerabilities that an attacker could exploit. This proactive strategy is essential for organizations to understand their weaknesses before malicious actors can take advantage of them.
The importance of security assessments lies in their ability to provide actionable insights. These insights help firms strengthen their defenses, comply with regulatory requirements, and protect sensitive information from breaches. By regularly conducting vulnerability assessments, companies can ensure that their protective measures are effective and up-to-date, ultimately safeguarding their reputation and financial stability.
As cyber threats continue to evolve, organizations that prioritize ongoing evaluations and integrate insights into their security strategies will be better positioned to mitigate risks and enhance their overall security posture. Continuous Threat Exposure Management (CTEM) transforms security evaluations from a one-time event into an ongoing process. This shift allows organizations to view security assessments as rather than isolated incidents, fostering a culture of continuous improvement in cybersecurity practices.
For example, organizations that have adopted CTEM frameworks have reported improved risk management and a more agile approach to vulnerability remediation. Furthermore, considering that the average cost of a data breach in 2025 was $4.44 million, utilizing penetration testing providers for regular assessments represents a cost-effective strategy to prevent significant financial losses.
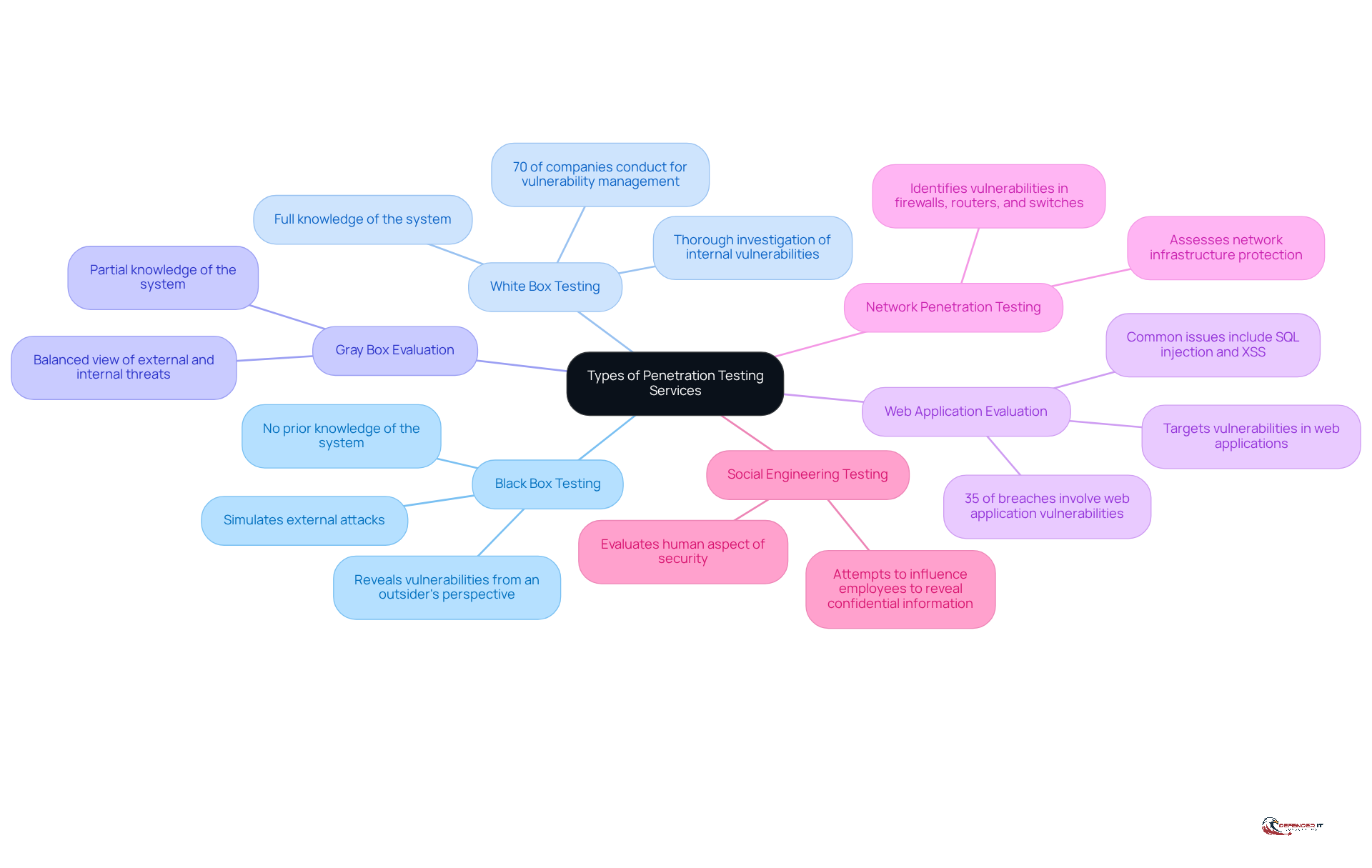
Exploring Types of Penetration Testing Services Offered
Penetration testing services can be categorized into several types, each tailored to address specific security concerns:
- Black Box Testing: This approach involves testers who have no prior knowledge of the system, simulating an external attack. It effectively assesses security posture from an outsider’s perspective, revealing vulnerabilities that could be exploited by malicious actors. As Dan DeCloss, Founder of PlexTrac, states, “Security leaders no longer see security tests as one-time engagements that conclude with a PDF,” underscoring the necessity for ongoing evaluation.
- White Box Testing: In this method, the tester possesses full knowledge of the system, including source code and architecture. This comprehensive approach allows for a thorough investigation of internal vulnerabilities, facilitating the identification of potential weaknesses that might be overlooked in other evaluation methods. A report indicates that 70% of companies conduct penetration tests for vulnerability management, highlighting the importance of thorough internal assessments.
- Gray Box Evaluation: This hybrid approach combines elements of both black and white box assessments, where the examiner has partial knowledge of the system. Gray box evaluation offers a balanced view of both external and internal threats, making it a versatile option for organizations aiming to enhance their security measures.
- Web Application Evaluation: Focused on , this type of assessment targets common issues such as SQL injection and cross-site scripting (XSS). Given that web applications are a primary attack vector, effective testing in this area is crucial for safeguarding sensitive data. Notably, 35% of successful corporate breaches involve web application vulnerabilities, emphasizing the necessity for robust web application protection measures.
- Network Penetration Testing: This service assesses the protection of network infrastructure, identifying vulnerabilities in firewalls, routers, and switches. As network environments grow more complex, routine assessments are essential to ensure comprehensive protection.
- Social Engineering Testing: This method evaluates the human aspect of security by attempting to influence employees into revealing confidential information. Given the prevalence of social engineering attacks, this form of evaluation is vital for understanding and mitigating risks associated with human behavior.
Each type of assessment from penetration testing providers serves a distinct function and can be tailored to meet the specific requirements of a company, ensuring comprehensive protection coverage. As organizations increasingly recognize the importance of proactive security strategies, the demand for customized vulnerability assessment services continues to rise.
Criteria for Choosing the Right Penetration Testing Provider
When selecting a penetration testing provider, organizations should prioritize the following criteria:
- Experience and Expertise: Look for providers with a proven track record in penetration testing, particularly within your industry. It’s essential to verify their certifications and qualifications to ensure they possess the necessary skills.
- Methodology: Confirm that the provider follows established methodologies, such as OWASP or NIST. This adherence guarantees a comprehensive and to the evaluation process.
- Reporting: The quality of the final report is paramount. It should deliver clear, actionable insights and prioritize vulnerabilities based on their associated risks.
- Personalization: A proficient provider should tailor their services to meet the specific needs of your organization, considering factors such as industry regulations and unique security challenges.
- Post-Test Support: Evaluate whether the provider offers support after the assessment phase, including guidance on remediation and options for retesting.
- Client References: Request references or case studies from previous clients to assess the provider’s effectiveness and reliability.
By thoroughly evaluating these criteria, organizations can select penetration testing providers that align with their security objectives and enhance their overall cybersecurity posture.
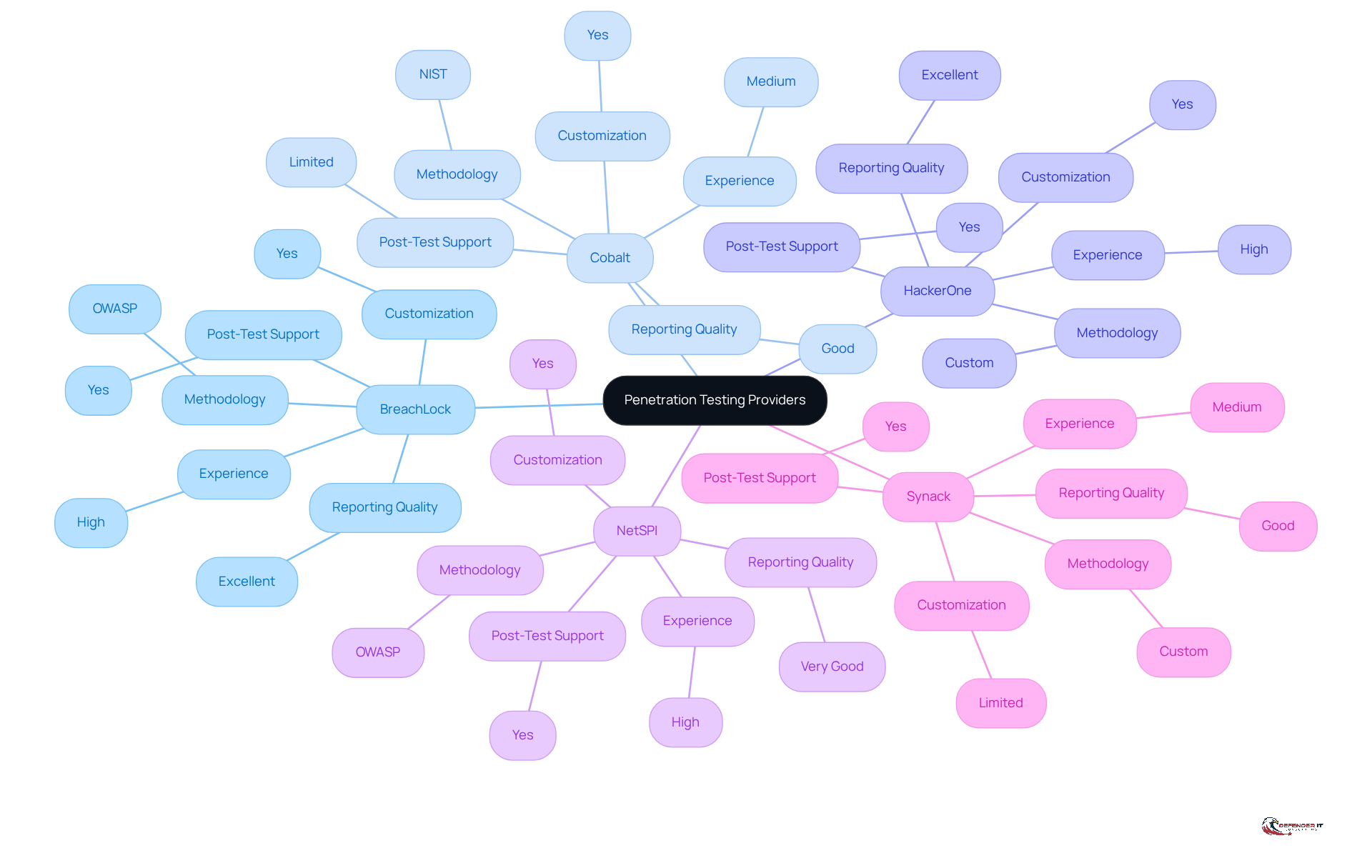
Comparative Analysis of Leading Penetration Testing Providers
In this comparative analysis, we evaluate several leading penetration testing providers based on key criteria:
- Provider: BreachLock
Experience: High
Methodology: OWASP
Reporting Quality: Excellent
Customization: Yes
Post-Test Support: Yes - Provider: Cobalt
Experience: Medium
Methodology: NIST
Reporting Quality: Good
Customization: Yes
Post-Test Support: Limited - Provider: HackerOne
Experience: High
Methodology: Custom
Reporting Quality: Excellent
Customization: Yes
Post-Test Support: Yes - Provider: NetSPI
Experience: High
Methodology: OWASP
Reporting Quality: Very Good
Customization: Yes
Post-Test Support: Yes - Provider: Synack
Experience: Medium
Methodology: Custom
Reporting Quality: Good
Customization: Limited
Post-Test Support: Yes
Key Insights:
- BreachLock excels with its excellent reporting quality and comprehensive post-test support, making it ideal for organizations seeking thorough insights and guidance.
- Cobalt offers a robust approach but may have constraints in post-test support, which could be a factor for entities requiring ongoing assistance.
- HackerOne stands out in customization and reporting, making it a strong option for businesses with distinct protection requirements.
- NetSPI combines extensive experience with a robust methodology, providing a balanced choice for entities seeking reliability and thoroughness.
- Synack is suitable for those who prioritize a custom approach but may not offer as much post-test support as others.
This comparative analysis equips organizations with the necessary information to make when selecting penetration testing providers that align with their security objectives.
Conclusion
In conclusion, understanding the landscape of penetration testing is essential for organizations seeking to strengthen their cybersecurity defenses. Proactive assessments are vital for identifying vulnerabilities before they can be exploited by malicious actors. By fostering a culture of continuous evaluation, businesses can significantly improve their security posture and mitigate risks associated with cyber threats.
The article outlines various types of penetration testing services, including:
- Black box
- White box
- Gray box
- Web application
- Network
- Social engineering testing
Each type serves a distinct purpose, enabling organizations to customize their security strategies to meet their specific needs. Additionally, selecting the right penetration testing provider is crucial; organizations should consider factors such as experience, methodology, reporting quality, and post-test support to make informed decisions.
As cyber threats grow increasingly sophisticated, the necessity of regular penetration testing becomes paramount. Organizations are urged to prioritize these assessments as a fundamental component of their security strategy, investing in reputable providers that align with their unique requirements. This approach not only protects sensitive information but also safeguards their reputation and financial stability in an ever-evolving digital landscape.
Frequently Asked Questions
What is penetration testing?
Penetration testing, or ‘pen testing,’ is a simulated cyberattack against a computer system, network, or web application aimed at identifying vulnerabilities that could be exploited by attackers.
Why is penetration testing important for organizations?
It is important because it helps organizations identify weaknesses before malicious actors can exploit them, providing actionable insights to strengthen defenses, comply with regulations, and protect sensitive information.
How do security assessments benefit organizations?
Security assessments help organizations strengthen their defenses, ensure compliance with regulatory requirements, protect sensitive information from breaches, and maintain their reputation and financial stability.
What is Continuous Threat Exposure Management (CTEM)?
CTEM is an approach that transforms security evaluations into an ongoing process, allowing organizations to continuously improve their cybersecurity practices rather than viewing assessments as isolated events.
What are the advantages of adopting CTEM frameworks?
Organizations using CTEM frameworks report improved risk management and a more agile approach to vulnerability remediation.
What is the financial impact of data breaches?
The average cost of a data breach in 2025 was $4.44 million, making regular penetration testing a cost-effective strategy to prevent significant financial losses.
How often should organizations conduct penetration testing?
Organizations should conduct penetration testing regularly to ensure that their protective measures are effective and up-to-date in the face of evolving cyber threats.
List of Sources
- Understanding Penetration Testing: Definition and Importance
- How Pentesting Fits Into a 2026 Security Game Plan – Blog – NopSec (https://nopsec.com/blog/how-pentesting-fits-into-a-2026-security-game-plan)
- The 2026 State of Pentesting: How Modern Teams Manage and Deliver Results (https://thehackernews.com/expert-insights/2026/01/the-2026-state-of-pentesting-how-modern.html)
- Pentesting in 2026: Insights, Trends, and Predictions | Capture The Bug (https://capturethebug.xyz/Blogs/Pentesting-in-2026-Insights-Trends-and-Predictions)
- Pentesting Statistics 2025: Key Insights and Emerging Trends (https://zerothreat.ai/blog/emerging-penetration-testing-statistics)
- Rapid7 (https://rapid7.com/blog/tag/penetration-testing)
- Exploring Types of Penetration Testing Services Offered
- 83 Penetration Testing Statistics: Key Facts and Figures (https://getastra.com/blog/security-audit/penetration-testing-statistics)
- The 2026 State of Pentesting: How Modern Teams Manage and Deliver Results (https://thehackernews.com/expert-insights/2026/01/the-2026-state-of-pentesting-how-modern.html)
- 100+ essential penetration testing statistics [2023 edition] (https://pentest-tools.com/blog/penetration-testing-statistics)
- Penetration Testing — Latest News, Reports & Analysis | The Hacker News (https://thehackernews.com/search/label/Penetration Testing)
- 120+ Penetration Testing Statistics for 2026 (https://brightdefense.com/resources/penetration-testing-statistics)
- Criteria for Choosing the Right Penetration Testing Provider
- The top 20 expert quotes from the Cyber Risk Virtual Summit (https://diligent.com/resources/blog/top-20-quotes-cyber-risk-virtual-summit)
- 83 Penetration Testing Statistics: Key Facts and Figures (https://getastra.com/blog/security-audit/penetration-testing-statistics)
- 120+ Penetration Testing Statistics for 2026 (https://brightdefense.com/resources/penetration-testing-statistics)
- 100+ essential penetration testing statistics [2023 edition] (https://pentest-tools.com/blog/penetration-testing-statistics)
- Penetration testing statistics, vulnerabilities and trends in 2026 – Cyphere (https://thecyphere.com/blog/penetration-testing-statistics)
- Comparative Analysis of Leading Penetration Testing Providers
- Penetration Testing Services Market Outlook 2026-2034 (https://intelmarketresearch.com/penetration-testing-services-market-37048)
- Top Penetration Testing Companies in 2026 (Independent Ranking) (https://deepstrike.io/blog/top-penetration-testing-companies-2026)
- 120+ Penetration Testing Statistics for 2026 (https://brightdefense.com/resources/penetration-testing-statistics)
- Pentesting Statistics 2025: Key Insights and Emerging Trends (https://zerothreat.ai/blog/emerging-penetration-testing-statistics)