Introduction
As the manufacturing sector increasingly embraces digital transformation, the significance of robust cloud networking security is paramount. With the convergence of operational technology and information technology, manufacturers encounter heightened risks from cyber threats that can disrupt operations and compromise sensitive data. This article delves into essential best practices for securing cloud networks, providing insights into shared responsibilities and effective strategies that can strengthen defenses against prevalent vulnerabilities.
How can manufacturers adeptly navigate this complex landscape to ensure their cloud security measures are not only compliant but also resilient against evolving threats?
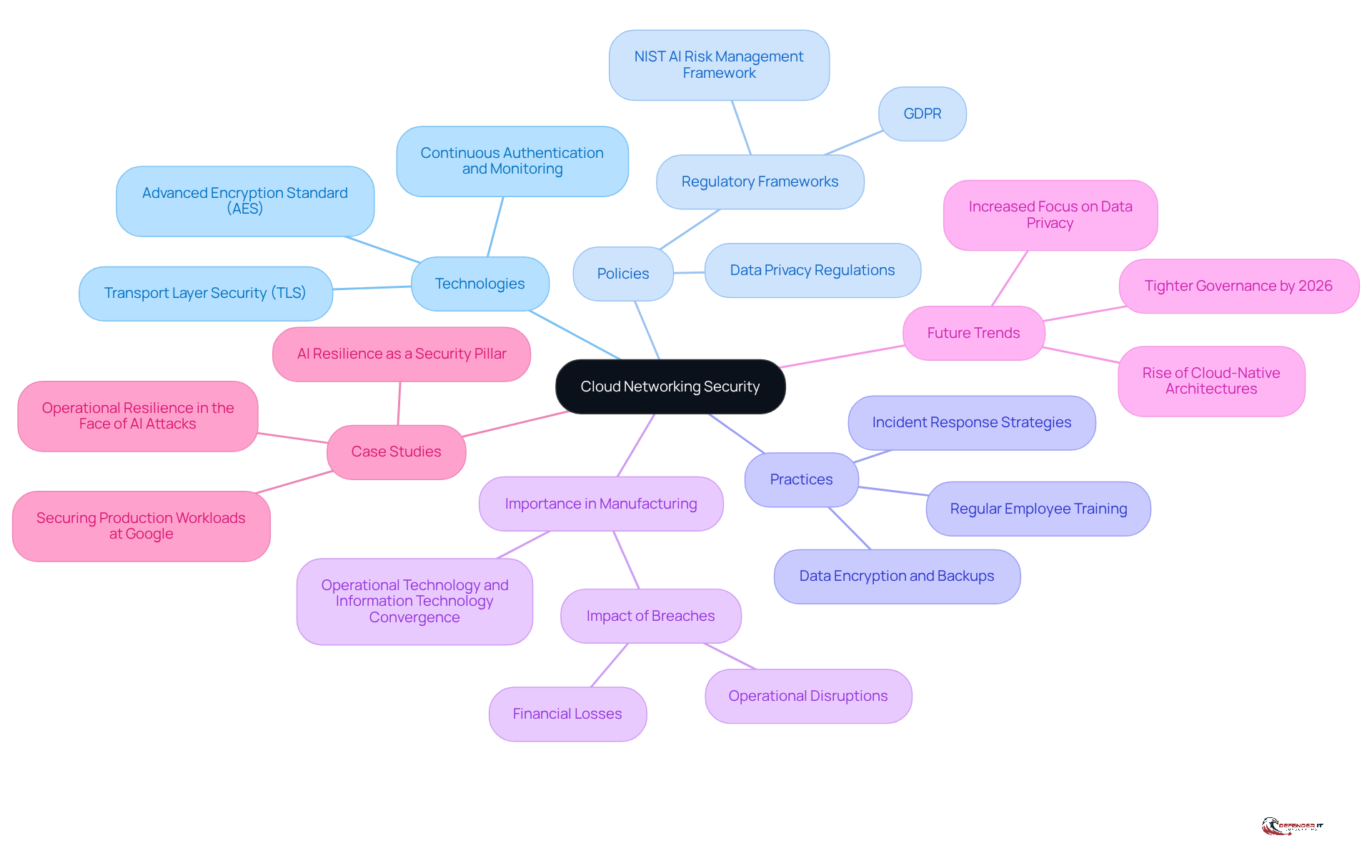
Define Cloud Networking Security and Its Importance
encompasses the technologies, policies, and practices designed to safeguard cloud-based networks from unauthorized access, information breaches, and various . In the manufacturing sector, where converge, the protection of network systems is paramount. As manufacturers increasingly adopt , analysis, and operational efficiency, the risks associated with inadequate protective measures also escalate.
By 2026, the focus on online networking protection is expected to intensify, driven by stricter governance and more robust regulatory frameworks concerning consumer information. Effective not only protects sensitive data but also ensures , thereby safeguarding the organization’s reputation and financial stability.
Recent case studies illustrate the consequences of breaches within the manufacturing industry; notably, half of OT organizations experienced attacks in 2025, underscoring the urgent need for . The impact of online data breaches can lead to . As organizations navigate these challenges, prioritizing becomes essential for maintaining resilience and trust in an increasingly digital landscape.
Clarify Shared Responsibilities in Cloud Security
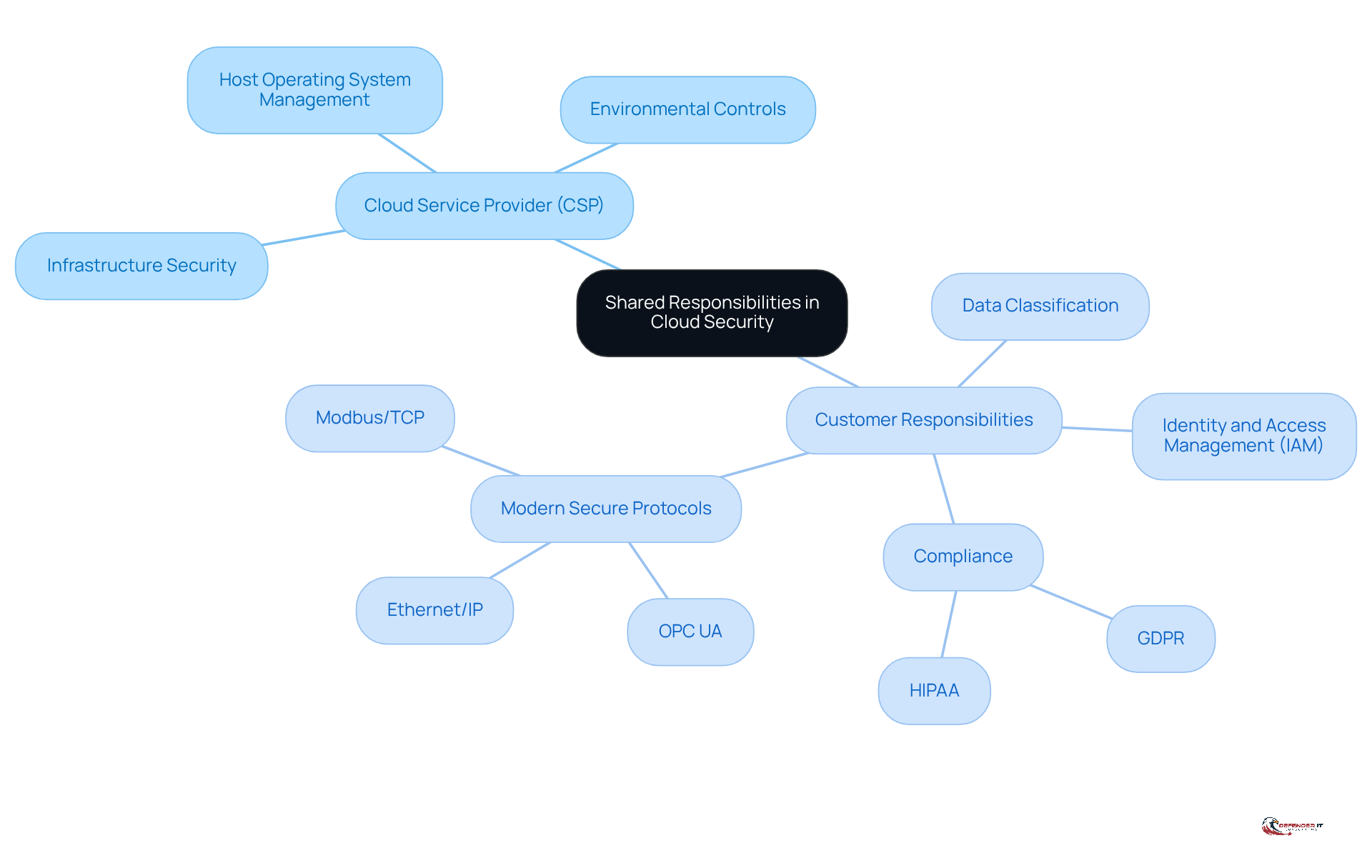
In a cloud environment, operates within a between the cloud service provider (CSP) and the customer. The CSP is tasked with safeguarding the underlying infrastructure, while the customer is responsible for managing their information, which includes implementing encryption and access controls. For manufacturers, this necessitates a clear understanding of their safety obligations, such as:
- (IAM)
- Data classification
Significantly, a large percentage of manufacturers – over 56% – struggle to fully grasp their responsibilities in multi-cloud environments. This lack of understanding of can lead to compliance issues and increased vulnerability to cyber threats. By clearly delineating these responsibilities, manufacturers can enhance their and ensure that measures are effectively implemented and aligned with their operational needs.
For instance, in the Infrastructure as a Service (IaaS) model, while the CSP manages physical security and the host operating system, clients must ensure . In the Platform as a Service (PaaS) model, customers are accountable for application protection and identity management, whereas the CSP oversees environmental controls. Furthermore, manufacturers should adopt modern secure industrial network protocols such as:
- OPC UA
- Ethernet/IP
- Modbus/TCP
to bolster their protection framework. This understanding is essential for manufacturers to safeguard their assets and maintain compliance in an increasingly complex digital landscape.
Identify Common Threats to Cloud Networking Security
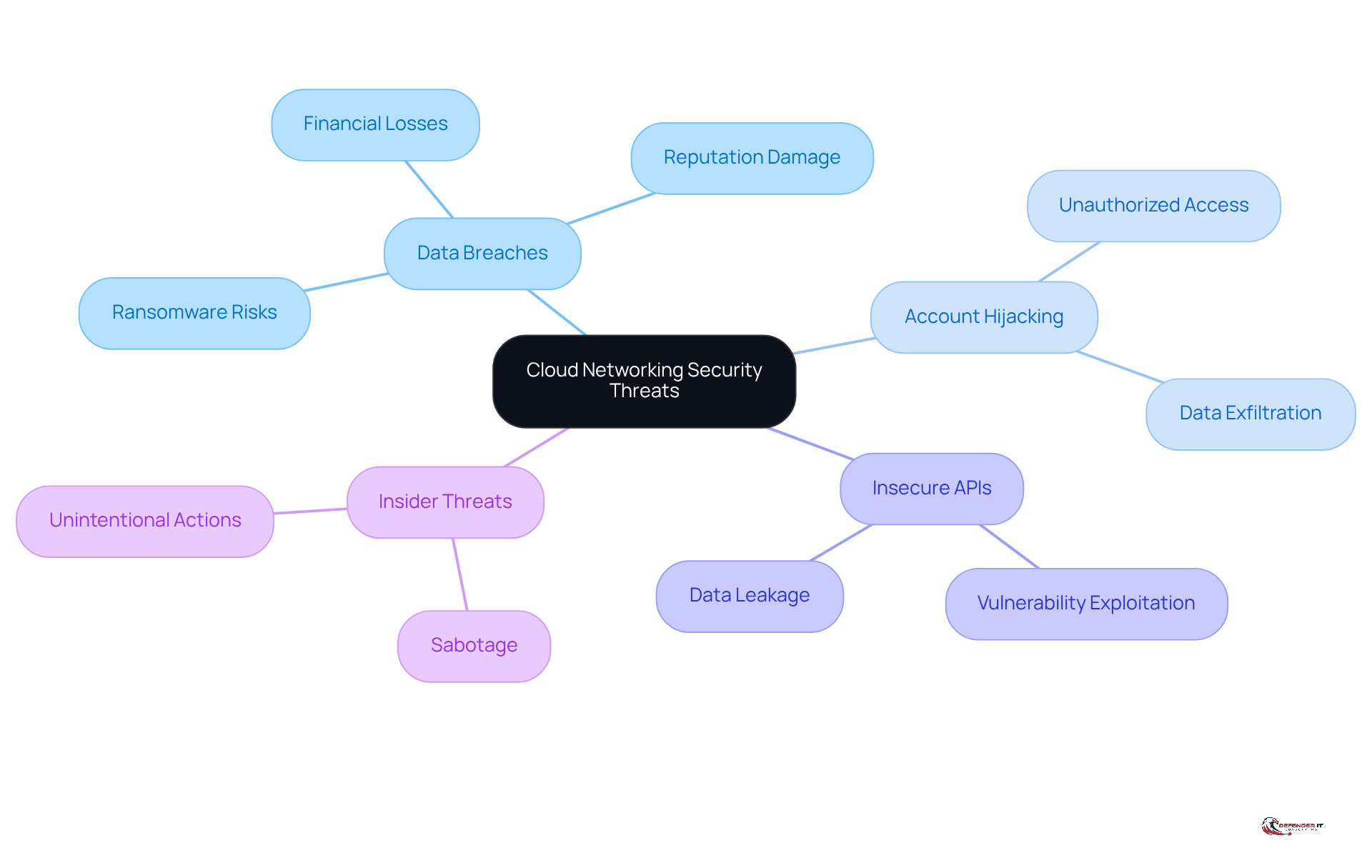
Producers face significant risks to their , including:
- Account hijacking
- Insecure APIs
- Insider threats
, often stemming from misconfigurations or inadequate access controls, can result in substantial and damage to reputation. Additionally, the rise of presents a serious threat to .
Understanding these risks enables producers to implement related to . and are essential strategies to effectively mitigate these threats. By prioritizing these actions, producers can enhance their and safeguard their operations.
Implement Effective Strategies for Cloud Networking Security
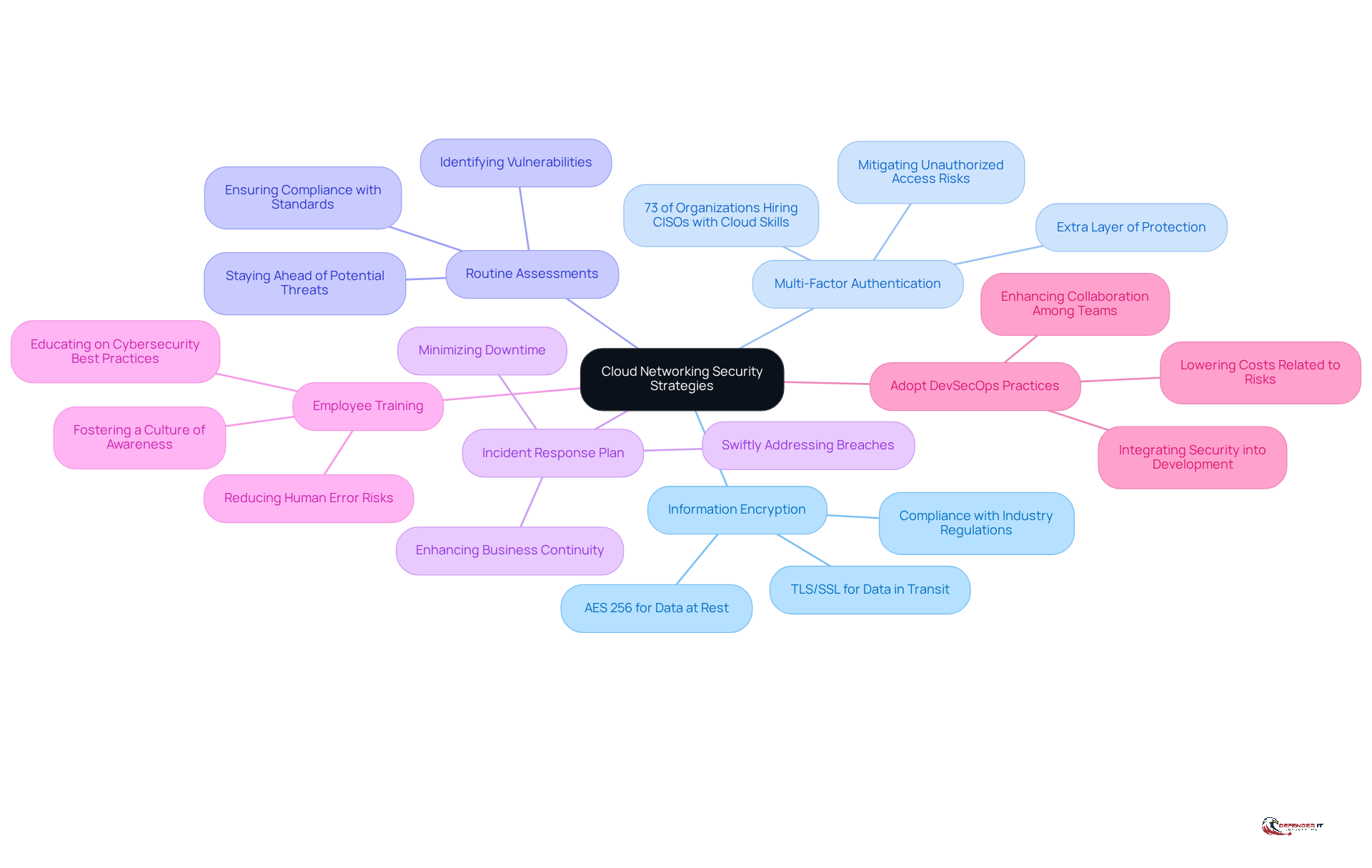
To enhance , manufacturers should adopt several best practices:
- : Securing all sensitive information, both at rest and in transit, is essential. This practice protects against unauthorized access and ensures compliance with industry regulations. Strong encryption methods, such as TLS/SSL for data in transit and AES 256 for data at rest, are recommended to safeguard critical information.
- : Implementing MFA for all user accounts adds an extra layer of protection against credential theft. Adoption rates of MFA in manufacturing are rising, as organizations recognize its importance in mitigating risks associated with unauthorized access. Recent data indicates that 73% of organizations are either recruiting or intending to recruit a CISO with advanced cloud skills, highlighting the increasing focus on robust protective measures.
- : Regular evaluations are essential for identifying vulnerabilities and ensuring compliance with industry standards. These audits assist manufacturers in staying ahead of potential threats and maintaining a strong protective stance.
- : Creating and routinely revising an is crucial for swiftly addressing any breaches. A well-defined plan minimizes downtime and enhances business continuity during incidents.
- : Ongoing training for employees on is vital to reduce the risk of human error, which accounts for 88% of data breaches. Informing employees about the shared responsibility model and cloud threats fosters a culture of awareness.
- Adopt : Incorporating protection into the development process through DevSecOps can significantly lower costs related to risks and enhance collaboration among development, infrastructure, and protection teams. This approach ensures that protection is prioritized at every stage of the development lifecycle.
By following these strategies, manufacturers can significantly enhance their to protect their critical assets from evolving cyber threats.
Conclusion
Cloud networking security is essential for manufacturers facing the complexities of modern operational environments. With the increasing reliance on cloud solutions, robust security measures are crucial to protect sensitive data and ensure compliance with regulatory standards. The convergence of operational technology and information technology underscores the urgency for manufacturers to prioritize their cloud security strategies.
This article outlines essential best practices, including:
- Understanding shared responsibilities
- Identifying common threats
- Implementing effective security strategies
Key insights emphasize the importance of:
- Information encryption
- Multi-factor authentication
- Routine assessments
- Employee training
These practices not only strengthen defenses against cyber threats but also cultivate a culture of security awareness within organizations, ultimately enhancing operational resilience.
In a rapidly evolving digital landscape, manufacturers must remain vigilant and proactive in their approach to cloud networking security. By adopting these best practices and staying informed about emerging threats, organizations can protect their critical assets and maintain trust with stakeholders. The time to act is now; investing in cloud security is not merely a necessity but a strategic imperative for long-term success in the manufacturing sector.
Frequently Asked Questions
What is cloud networking security?
Cloud networking security refers to the technologies, policies, and practices aimed at protecting cloud-based networks from unauthorized access, information breaches, and various cyber threats.
Why is cloud networking security important in the manufacturing sector?
In the manufacturing sector, where operational technology (OT) and information technology (IT) converge, safeguarding network systems is crucial due to the increasing adoption of online solutions for data storage and operational efficiency. Inadequate protective measures can lead to significant risks.
What factors are driving the focus on cloud networking security by 2026?
The focus on online networking protection is expected to intensify due to stricter governance and more robust regulatory frameworks regarding consumer information.
How does effective cloud networking security benefit organizations?
Effective cloud networking security protects sensitive data, ensures compliance with industry regulations, and helps safeguard an organization’s reputation and financial stability.
What are the consequences of breaches in the manufacturing industry?
Breaches in the manufacturing industry can lead to significant operational disruptions and financial losses, as evidenced by case studies showing that half of OT organizations experienced attacks in 2025.
What is the overall impact of online data breaches?
The impact of online data breaches includes operational disruptions and financial losses, highlighting the urgent need for robust protective measures in organizations.
How can organizations maintain resilience and trust in a digital landscape?
Organizations can maintain resilience and trust by prioritizing network protection and implementing effective cloud networking security measures.
List of Sources
- Define Cloud Networking Security and Its Importance
- Security industry trends for 2026 | Zenitel (https://zenitel.com/news/security-industry-trends-2026)
- Industry News 2026 The 6 Cybersecurity Trends That Will Shape 2026 (https://isaca.org/resources/news-and-trends/industry-news/2026/the-6-cybersecurity-trends-that-will-shape-2026)
- 2026 and beyond: Urgent need for integrated cybersecurity strategies in evolving industrial landscape – Industrial Cyber (https://industrialcyber.co/features/2026-and-beyond-urgent-need-for-integrated-cybersecurity-strategies-in-evolving-industrial-landscape)
- Top 5 Cloud Security Trends to Watch in 2026 (https://sentinelone.com/cybersecurity-101/cloud-security/cloud-security-trends)
- Cloud CISO Perspectives: Our 2026 Cybersecurity Forecast report | Google Cloud Blog (https://cloud.google.com/blog/products/identity-security/cloud-ciso-perspectives-our-2026-cybersecurity-forecast-report)
- Clarify Shared Responsibilities in Cloud Security
- consilien.com (https://consilien.com/news/cybersecurity-solutions-protecting-manufacturing-companies)
- Navigating Manufacturing Cybersecurity and the Cloud (https://nexusconnect.io/articles/navigating-manufacturing-cybersecurity-and-the-cloud)
- ISACA Now Blog 2022 The Customers Responsibility in the Cloud Shared Responsibility Model (https://isaca.org/resources/news-and-trends/isaca-now-blog/2022/the-customers-responsibility-in-the-cloud-shared-responsibility-model)
- 50+ Cloud Security Statistics in 2026 (https://sentinelone.com/cybersecurity-101/cloud-security/cloud-security-statistics)
- Identify Common Threats to Cloud Networking Security
- Cybersecurity Threats To Watch Out For In 2026: A Network Optix Guide (https://networkoptix.com/blog/cybersecurity-threats-to-watch-out-for-in-2026)
- Top Cybersecurity Threats in the Manufacturing Industry 2026 – Hoxhunt (https://hoxhunt.com/blog/cyber-security-threats-in-manufacturing-industry)
- Cloud and SaaS risks rise in 2026 as trust and outages collide (https://scworld.com/feature/cloud-and-saas-risks-rise-in-2026-as-trust-and-outages-collide)
- netskope.com (https://netskope.com/resources/cloud-and-threat-reports/cloud-and-threat-report-2026)
- Inside the Breach: Why & How Manufacturers are Compromised (https://processunity.com/resources/blogs/inside-the-breach-why-and-how-manufacturers-are-compromised)
- Implement Effective Strategies for Cloud Networking Security
- Cybersecurity for Manufacturing in 2026 (https://blog.thriveon.net/cybersecurity-for-manufacturing-in-2026)
- Encryption demand soars as 60% of business data kept on the cloud (https://cloudcomputing-news.net/news/encryption-demand-soars-as-60-of-business-data-kept-on-the-cloud)
- Cybersecurity in Manufacturing: Why It’s More Important Now Than Ever | KBI.Media (https://kbi.media/cybersecurity-in-manufacturing-why-its-more-important-now-than-ever)
- Top 5 Cloud Security Trends to Watch in 2026 (https://sentinelone.com/cybersecurity-101/cloud-security/cloud-security-trends)
- 8 Core Hybrid Cloud Security Best Practices for 2026 (https://strongdm.com/blog/hybrid-cloud-security-best-practices)