Introduction
Selecting the appropriate managed IT company is a pivotal decision that can profoundly influence an organization’s cybersecurity posture. In an era where businesses confront an increasingly intricate threat landscape, it is essential to comprehend specific cybersecurity needs and align them with the capabilities of potential providers. Given the multitude of options available, how can organizations ensure they choose a partner that not only fulfills their current requirements but also adapts to future challenges? This article explores best practices for evaluating managed IT services, providing insights that empower organizations to make informed decisions and strengthen their digital security strategies.
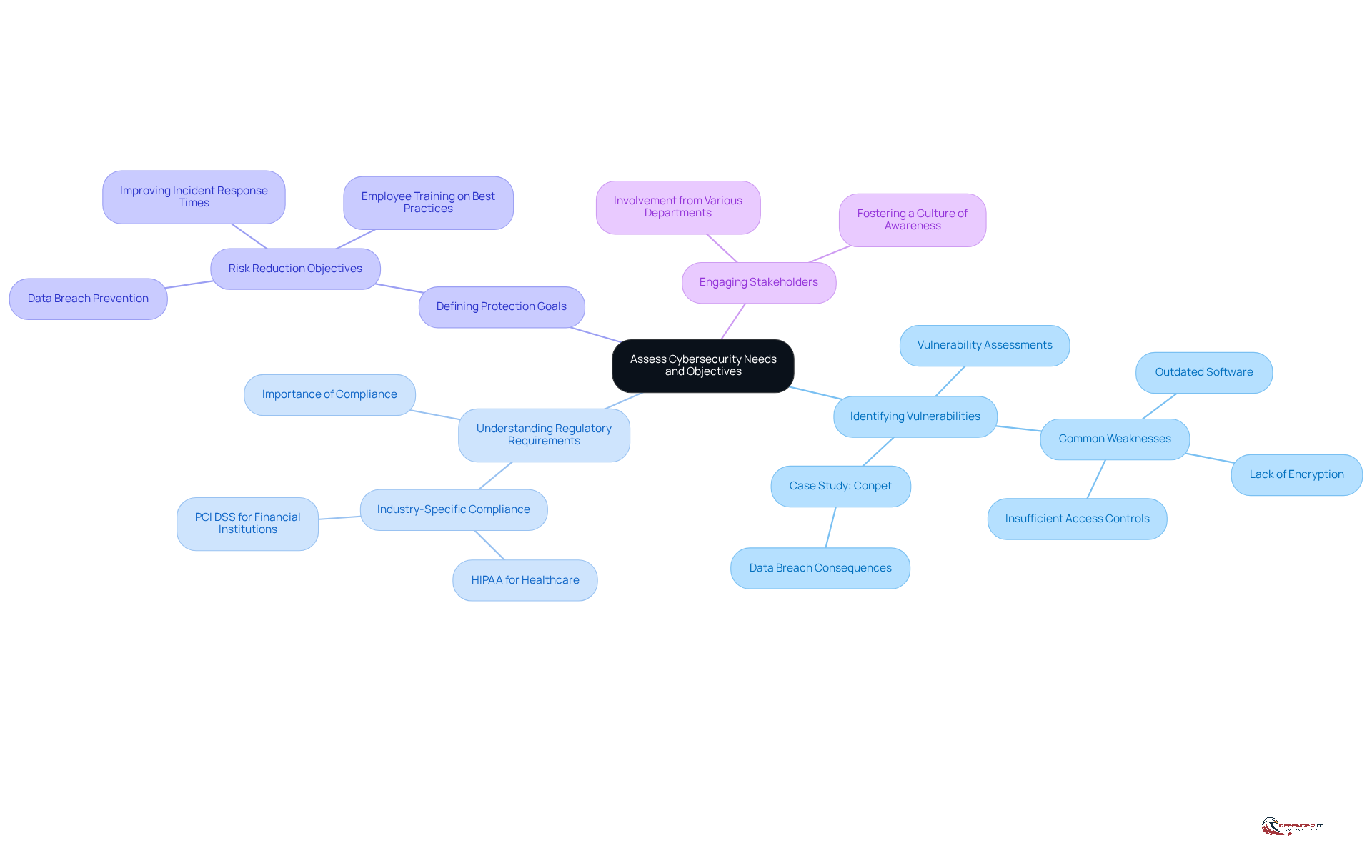
Assess Your Cybersecurity Needs and Objectives
Before selecting a managed IT company, it is crucial to conduct a thorough assessment of your organization’s cybersecurity needs and objectives. This assessment should encompass the following key areas:
- Vulnerability assessment: Conduct assessments to pinpoint weaknesses in your current IT infrastructure. By 2026, approximately 70% of businesses are expected to perform these assessments regularly, underscoring their significance in identifying outdated software, lack of encryption, or insufficient access controls. For instance, organizations like Conpet, Romania’s oil pipeline operator, faced severe repercussions, including a data breach, due to unaddressed vulnerabilities, highlighting the necessity for proactive measures.
- Regulatory requirements: Different industries have varying compliance needs. For example, healthcare organizations must adhere to HIPAA regulations, while financial institutions must comply with PCI DSS. Grasping these requirements is essential for selecting a provider capable of ensuring compliance and mitigating risks associated with regulatory scrutiny.
- Security objectives: Establish clear objectives for safeguarding your organization, such as reducing risk, improving incident response, or enhancing employee training on best practices for digital safety. This clarity will guide your selection process and align your cybersecurity strategy with organizational goals.
- Stakeholder involvement: Involve key stakeholders from various departments to gather diverse perspectives on safety requirements. This collaborative approach ensures that all facets of the organization are considered, fostering a culture of awareness and collective responsibility.
By implementing these steps, organizations can develop a comprehensive understanding of their digital security environment, which will inform their choice of a managed IT company and strengthen their overall security posture.
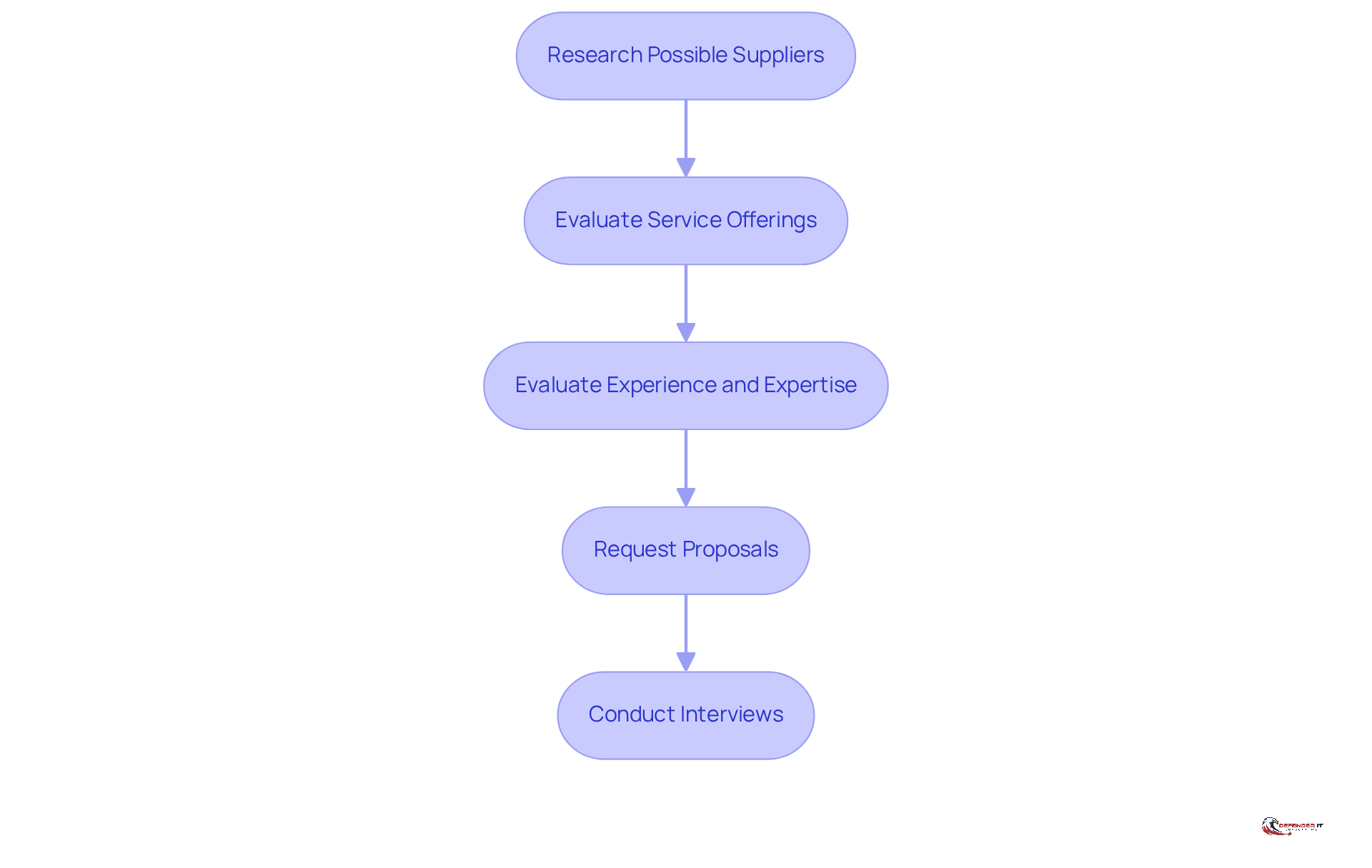
Evaluate and Select the Right Managed IT Provider
Choosing the appropriate managed IT service requires a systematic assessment process that ensures alignment with your organization’s security requirements. This process can be guided by the following essential steps:
- Research Possible Suppliers: Identify suppliers with a strong reputation. Utilize online reviews, testimonials, and case studies to assess their effectiveness and reliability.
- Evaluate Service Offerings: Ensure the supplier offers a comprehensive suite of services, including cybersecurity, cloud solutions, help desk support, and data backup. A broad range of services is crucial for addressing diverse IT needs and enhancing operational efficiency.
- Assess Industry Experience: Consider the supplier’s experience within your specific industry. Those with a proven track record in your sector will have a deeper understanding of your unique challenges and regulatory requirements, which is vital for effective service delivery.
- Request Proposals: Solicit detailed proposals from potential suppliers. These should clearly outline their approach to digital security, including plans, monitoring capabilities, and compliance strategies, allowing for a thorough comparison.
- Conduct Interviews: Engage in discussions with potential suppliers to evaluate their communication skills, responsiveness, and collaborative spirit. This interaction can provide insights into their commitment to customer service and support, which are critical for a successful partnership.
By following these steps, companies can make informed choices when selecting a managed IT provider, ensuring that their requirements are effectively addressed in the evolving landscape of 2026. Additionally, with managed security services projected to grow at a rate of 18% annually through 2026, the importance of choosing the right provider cannot be overstated. Industry leaders emphasize that a layered defense approach is essential, and operational fit should be prioritized over brand reputation. Furthermore, entities should be aware of common pitfalls, such as concentrating too much on price without comprehending the full range of services. Adherence to regulations such as PIPEDA is also vital for entities in regulated sectors, ensuring that data management and vendor supervision meet required standards.
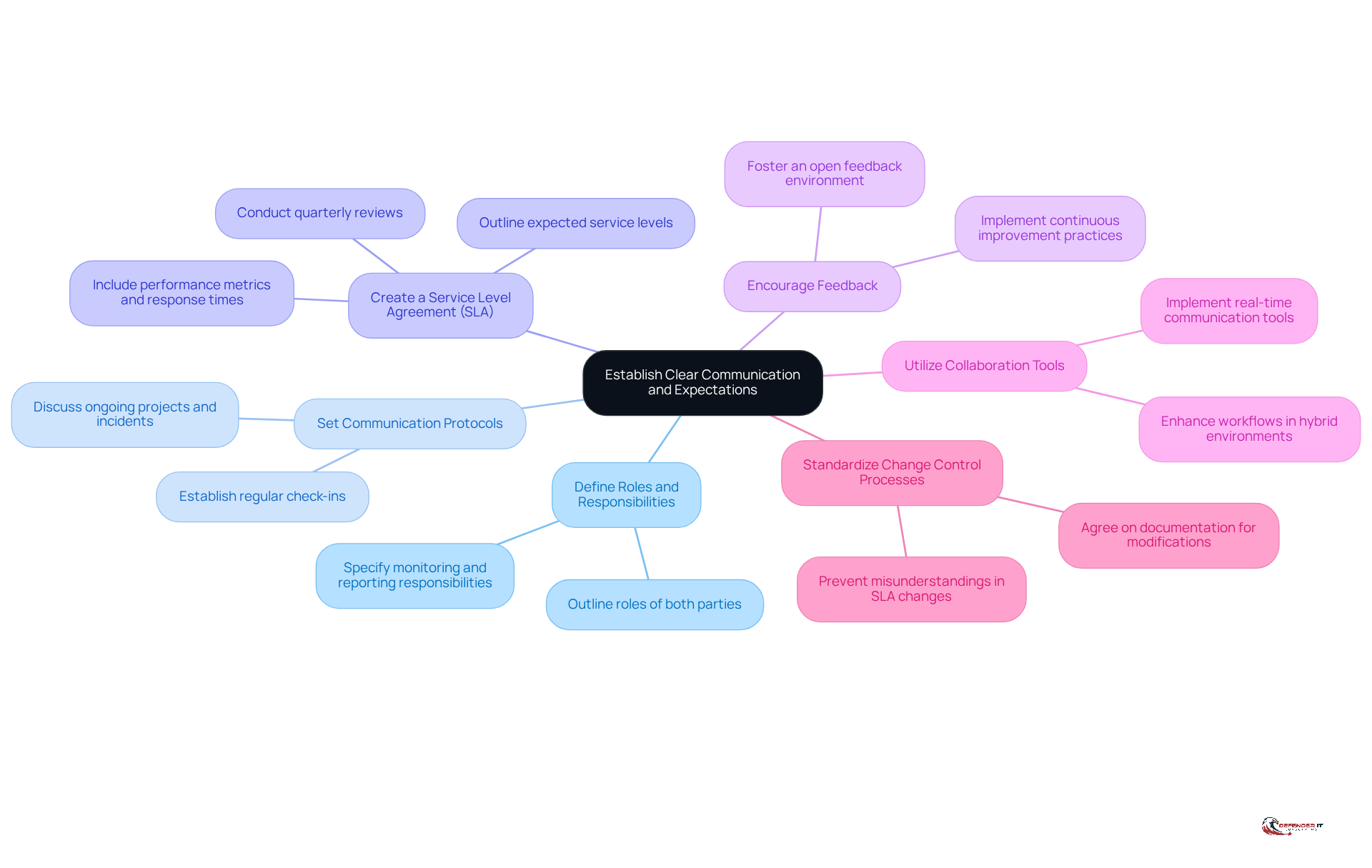
Establish Clear Communication and Expectations
Effective communication serves as the backbone of a successful partnership with a managed IT company. To establish clear communication and expectations, consider the following best practices:
- Define Roles: Clearly outline the roles of both your organization and the managed IT provider. Specify who is responsible for monitoring, reporting, and responding to incidents, ensuring accountability and clarity in operations.
- Set Communication Protocols: Establish regular meetings to discuss ongoing projects, safety incidents, and changes in the threat landscape. This practice ensures that both parties remain informed and engaged, fostering a proactive approach to cybersecurity.
- Create a Service Level Agreement: Develop an SLA that outlines expected service levels, response times, and performance metrics. This document serves as a reference point for accountability and should be updated to reflect changing business needs and technological advancements. Regular quarterly reviews of the SLA are essential to ensure alignment with these evolving needs.
- Encourage Feedback: Foster an environment where both parties can provide feedback on performance and communication. This openness can lead to continuous improvement in the partnership, enhancing overall service delivery.
- Utilize Collaboration Tools: Implement collaboration tools that facilitate real-time communication and information sharing. Such tools can enhance responsiveness and streamline workflows, particularly in hybrid work environments where 51% of businesses are adopting comprehensive support capabilities.
- Standardize Change Control Processes: Both parties must agree on procedures for authorizing and documenting modifications to the SLA. This agreement helps prevent misunderstandings and ensures that the SLA remains relevant as business priorities shift.
By prioritizing clear communication and establishing expectations, companies can create a solid foundation for their relationship with a managed IT provider, which ultimately enhances their cybersecurity posture and operational resilience. As Steven Kirz, Managing Director for Business Transformation, emphasizes, “Customers who get the most out of their SLAs are those that view it on a positive trajectory and use it as part of an ongoing process of motivating their service providers to achieve continuous improvement.”
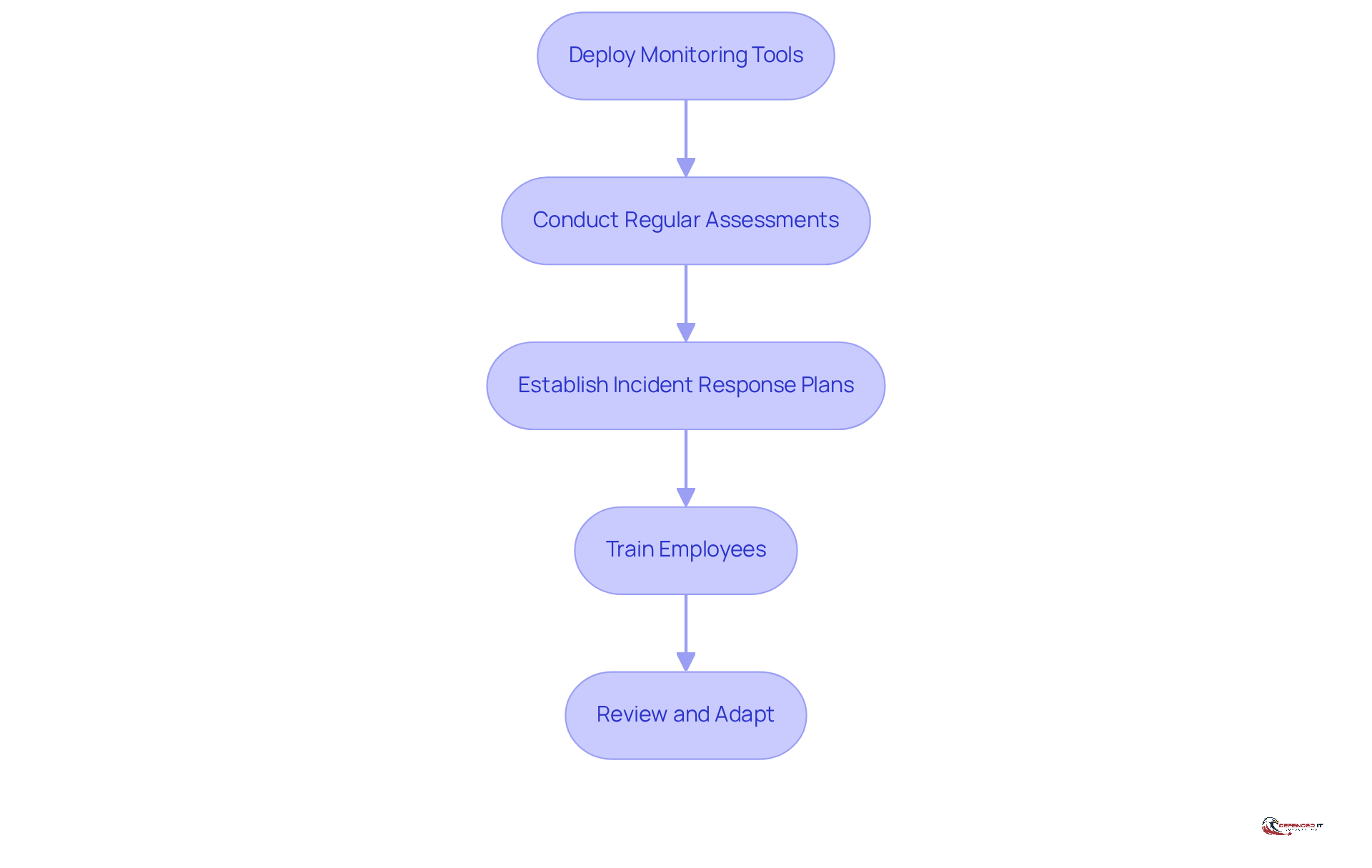
Implement Continuous Monitoring and Assessment
To effectively manage digital security risks, organizations must prioritize continuous monitoring. Establishing these processes involves several essential steps:
- Deploy monitoring tools: Implement advanced monitoring solutions that provide real-time visibility into your IT environment. These tools are crucial for identifying anomalies, unauthorized access, and potential threats, thereby enhancing overall safety.
- Conduct assessments: Schedule periodic evaluations to assess the effectiveness of your cybersecurity measures. This should include vulnerability scans, penetration tests, and compliance audits, which are vital for identifying weaknesses and ensuring adherence to regulatory standards. These assessments assist organizations in strengthening their defensive posture and staying ahead of threats.
- Establish response plans: Develop and routinely update procedures that outline the actions to take in the event of a security breach. Readiness in this area can significantly decrease response times and mitigate potential damage, making it a critical component of your security strategy.
- Provide training: Provide education on online safety best practices and threat awareness. A well-informed workforce serves as a crucial line of defense against cyber threats, reducing the likelihood of human error leading to breaches.
- Review and adapt: Continuously evaluate your monitoring and assessment strategies to adapt to new technologies and changes in your IT environment. This proactive approach ensures that your digital security stance remains robust and adaptable to evolving threats. By 2026, security strategies will increasingly incorporate cloud-native architectures with continuous authentication and monitoring.
By establishing ongoing monitoring and evaluation, organizations can remain proactive against potential dangers and uphold a robust security framework. Cybersecurity measures are increasingly recognized as essential, with 93% of organizations planning to increase their cybersecurity spending in the coming year, reflecting a growing awareness of the need for proactive defense measures.
Conclusion
Selecting the right managed IT company is a pivotal decision that can profoundly influence an organization’s cybersecurity posture and overall operational efficiency. A comprehensive understanding of cybersecurity needs and objectives forms the foundation for this choice, enabling businesses to safeguard their digital assets while navigating the complexities of the modern threat landscape.
This article delineates several best practices for choosing a managed IT provider. These include:
- Assessing cybersecurity requirements
- Evaluating potential suppliers
- Establishing clear communication and expectations
- Implementing continuous monitoring and assessment
Each of these steps is essential for forging a robust partnership that not only addresses current security needs but also adapts to evolving threats and regulatory demands. By prioritizing these practices, organizations can make informed decisions that align with their unique operational goals and compliance obligations.
Ultimately, the significance of a proactive and collaborative approach cannot be overstated. Organizations must engage stakeholders, foster open communication, and commit to continuous improvement in their cybersecurity strategies. As the digital landscape continues to evolve, emphasizing these best practices will empower businesses to stay ahead of potential threats, ensuring their resilience and security in an increasingly interconnected world.
Frequently Asked Questions
Why is it important to assess cybersecurity needs before selecting a managed IT company?
Assessing cybersecurity needs is crucial to identify vulnerabilities, understand regulatory requirements, define protection goals, and engage stakeholders, which collectively inform the choice of a managed IT company and strengthen overall security.
What areas should be included in a cybersecurity needs assessment?
A thorough assessment should include identifying vulnerabilities, understanding regulatory requirements, defining protection goals, and engaging stakeholders from various departments.
How can organizations identify vulnerabilities in their IT infrastructure?
Organizations can conduct vulnerability assessments to pinpoint weaknesses, such as outdated software, lack of encryption, or insufficient access controls, which are essential for improving their cybersecurity posture.
What are some industry-specific regulatory requirements organizations should be aware of?
Different industries have varying compliance requirements; for example, healthcare organizations must adhere to HIPAA regulations, while financial institutions must comply with PCI DSS.
What should organizations consider when defining their protection goals?
Organizations should establish clear objectives for safeguarding their data, such as reducing the risk of data breaches, improving incident response times, and enhancing employee training on digital safety best practices.
Why is it important to engage stakeholders in the cybersecurity assessment process?
Engaging stakeholders from various departments ensures diverse perspectives on safety requirements are considered, fostering a culture of awareness and collective responsibility within the organization.
How can conducting a cybersecurity needs assessment benefit an organization?
Implementing a comprehensive assessment helps organizations better understand their digital security environment, guiding their selection of a managed IT company and ultimately strengthening their security posture.
List of Sources
- Assess Your Cybersecurity Needs and Objectives
- 10 Cyber Security Trends For 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-trends)
- Cyber Security Report 2026 – Check Point Research (https://research.checkpoint.com/2026/cyber-security-report-2026)
- 2026 and beyond: Urgent need for integrated cybersecurity strategies in evolving industrial landscape – Industrial Cyber (https://industrialcyber.co/features/2026-and-beyond-urgent-need-for-integrated-cybersecurity-strategies-in-evolving-industrial-landscape)
- The Top Cybersecurity Threats in 2026 & How to Prevent Them | Prime Secured (https://primesecured.com/top-cybersecurity-threats-2026-and-prevention)
- Evaluate and Select the Right Managed IT Provider
- How to Evaluate IT Providers | Wired For The Future (https://wiredforthefuture.com/blog/how-to-evaluate-a-managed-it-provider)
- How Small Businesses Are Relying on Managed IT Services to Stay Competitive in 2026 (https://bignewsnetwork.com/news/278857101/how-small-businesses-are-relying-on-managed-it-services-to-stay-competitive-in-2026)
- 2026 IT Resolutions: Why SMBs Need Managed IT (https://safeboxtech.com/blogs/2026-it-resolutions-why-smbs-should-prioritize-managed-services)
- How Business Leaders Should Evaluate Cybersecurity Solutions in 2026 (https://meriplex.com/how-business-leaders-should-evaluate-cybersecurity-solutions-in-2026)
- Managed Services On The Rise: The CRN 2026 MSP 500 (https://crn.com/news/managed-services/2026/managed-services-on-the-rise-the-crn-2026-msp-500)
- Establish Clear Communication and Expectations
- Managed Services SLA: What to Expect in 2026 | sa.global (https://saglobal.com/en-us/insights/managed-services-slas-what-you-should-expect.html)
- sociabble.com (https://sociabble.com/blog/employee-communications/communications-statistics)
- How to build better SLAs for more strategic applications outsourcing (https://cio.com/article/244907/how-to-build-better-slas-for-more-strategic-applications-outsourcing.html)
- Implement Continuous Monitoring and Assessment
- 101 Cybersecurity Statistics and Trends for 2026 | NU (https://nu.edu/blog/cybersecurity-statistics)
- Industry News 2026 The 6 Cybersecurity Trends That Will Shape 2026 (https://isaca.org/resources/news-and-trends/industry-news/2026/the-6-cybersecurity-trends-that-will-shape-2026)
- Cybersecurity Trends in 2026: Rising Threats & Strategies | TierPoint, LLC (https://tierpoint.com/blog/cybersecurity/cybersecurity-trends)
- Why and How to Perform Cybersecurity Risk Assessments in 2026 (https://maddevs.io/blog/how-to-perform-cybersecurity-risk-assessments)
- jit.io (https://jit.io/resources/appsec-tools/continuous-security-monitoring-csm-tools)