Introduction
In the rapidly evolving landscape of manufacturing, robust cybersecurity measures are essential. Organizations are increasingly confronted with sophisticated cyber threats, making effective endpoint detection and response (EDR) systems critical for safeguarding sensitive data and operations. This article explores best practices for implementing EDR solutions, including:
- Essential components
- Integration strategies
- The importance of continuous monitoring
With the stakes higher than ever, manufacturers must ensure their endpoint detection strategies are not only effective but also adaptable to the ever-changing threat landscape.
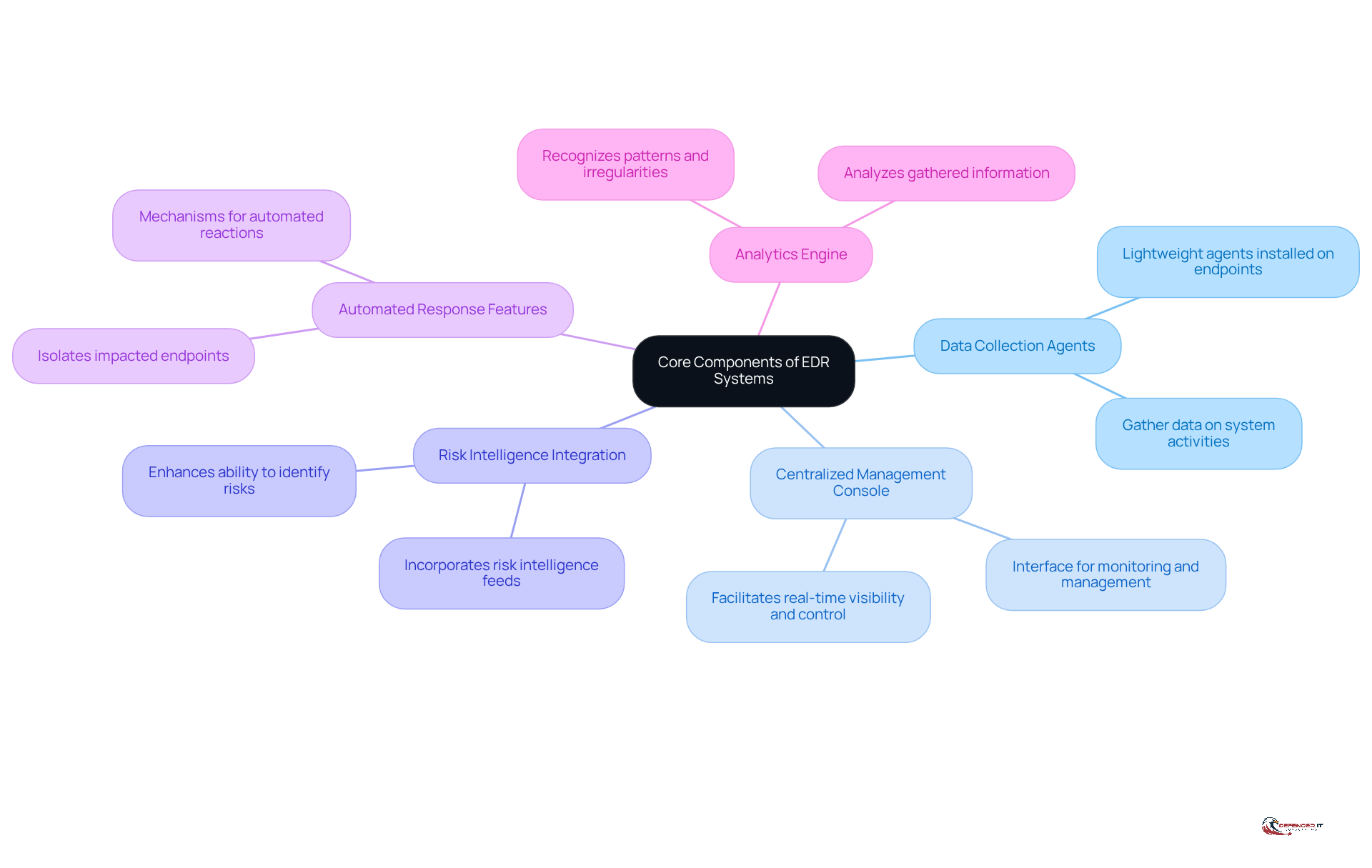
Identify Core Components of EDR Systems
To effectively implement in manufacturing, it is crucial to identify and understand their . These components typically include:
- : Lightweight agents installed on endpoints to gather data on system activities, processes, and network connections.
- : An interface that allows security teams to monitor and manage endpoint activities from a single location, facilitating real-time visibility and control.
- Integration: Incorporating feeds enhances the EDR’s ability to identify known and emerging risks, providing context for alerts and incidents.
- : EDR solutions should include mechanisms for automated reactions to identified risks, such as isolating impacted endpoints or obstructing harmful processes.
- : This component analyzes gathered information to recognize patterns and irregularities that may indicate incidents, facilitating .
By ensuring these components are present and functioning effectively, manufacturers can establish a robust foundation for their endpoint detection strategy, thereby enhancing their overall .
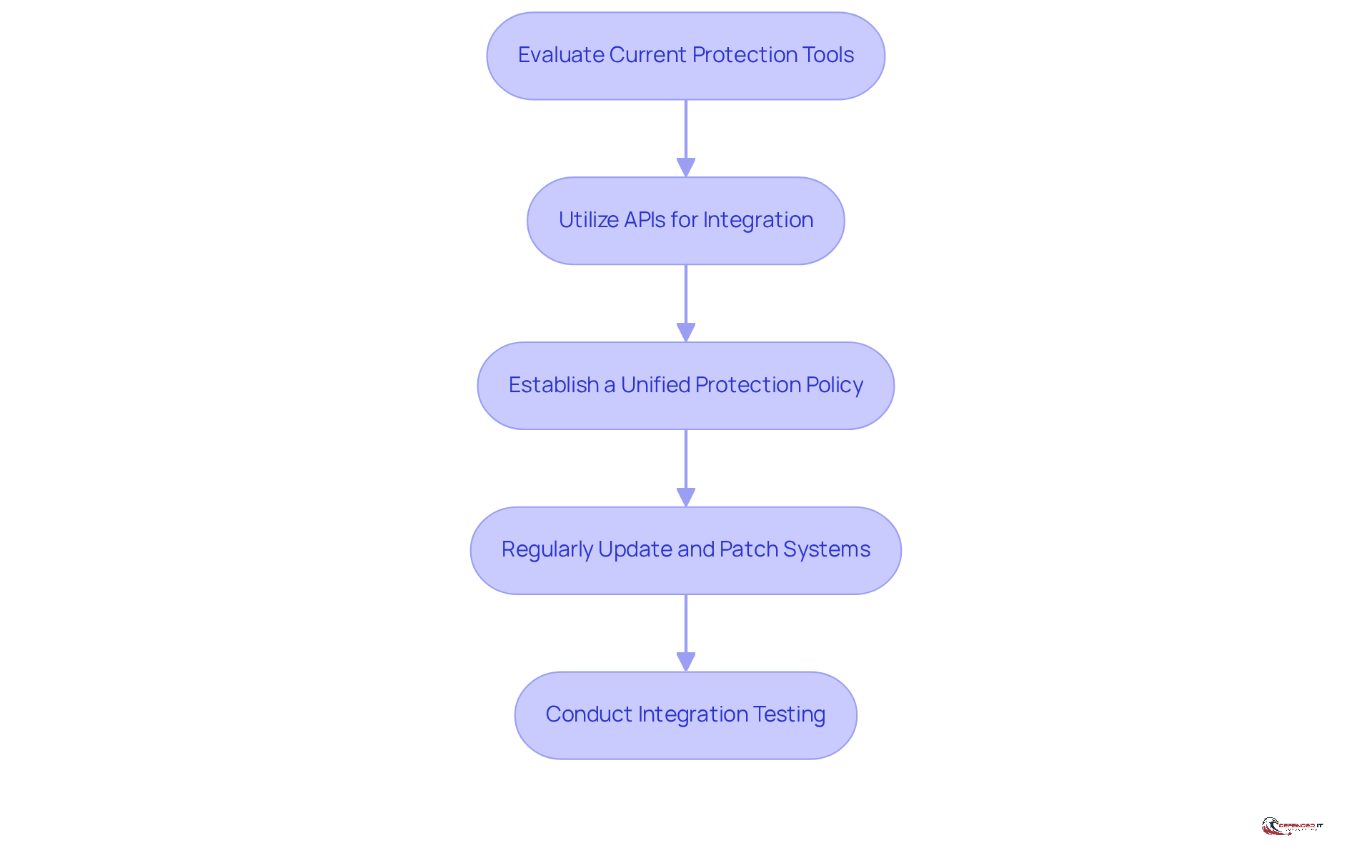
Integrate EDR with Existing Security Infrastructure
To enhance the efficiency of endpoint detection solutions, it is crucial to integrate them with current protective infrastructure, especially in light of the evolving , which includes autonomous and AI-driven threats. The following key steps outline how to achieve this:
- Evaluate Current Protection Tools: Begin by , such as firewalls, antivirus software, and Security Information and Event Management (SIEM) systems. This evaluation helps identify potential integration points that can bolster overall safety.
- Utilize APIs for Integration: Leverage to with other . This integration facilitates seamless data sharing and coordinated responses, which are essential for effective threat management.
- Establish a Unified Protection Policy: Develop a that encompasses all integrated tools. This ensures uniform protocols and procedures across the organization, fostering a cohesive protective environment. Additionally, organizations must adhere to regulatory standards, such as the , to align with industry requirements.
- Regularly Update and Patch Systems: Maintain all with the latest software patches and updates. This practice mitigates vulnerabilities and strengthens the overall protection posture.
- Conduct Integration Testing: Regularly test the integration of EDR with other to ensure they operate effectively together. This proactive approach aids in identifying and resolving potential issues before they can be exploited.
The market for endpoint detection is . This underscores the increasing importance of endpoint detection solutions in the . By following these steps, manufacturers can enhance their , leveraging the strengths of both EDR and existing security measures to better protect against evolving cyber risks.
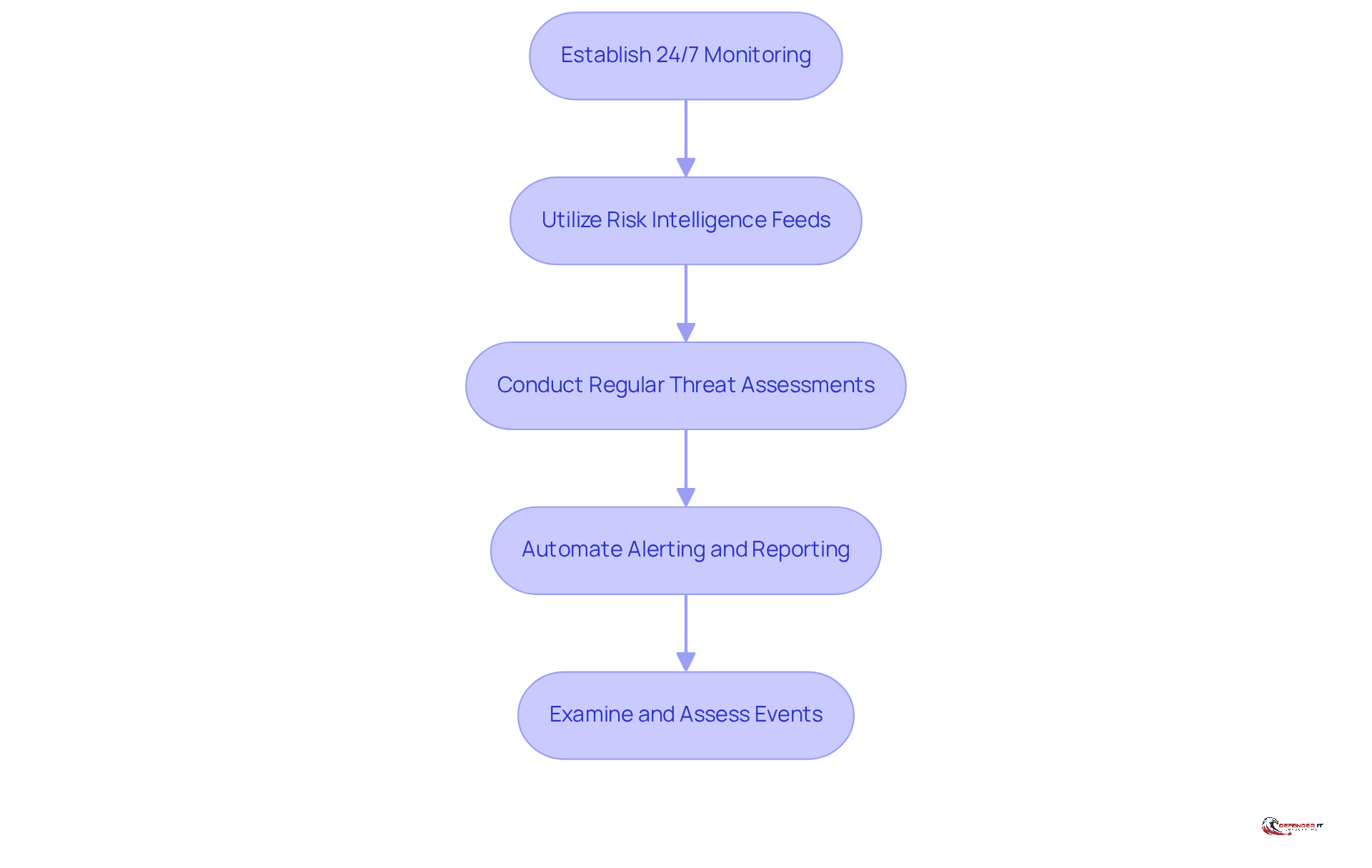
Implement Continuous Monitoring and Threat Intelligence
To ensure the effectiveness of EDR solutions, manufacturers must implement and incorporate intelligence on risks. Here are best practices to achieve this:
- Establish 24/7 Monitoring: Continuous observation of all endpoints is essential for endpoint detection of and potential risks in real-time.
- Utilize : Incorporating into the EDR system keeps manufacturers updated on emerging risks and vulnerabilities pertinent to the manufacturing sector.
- Conduct Regular : Periodic assessments of the threat landscape help identify new risks and adjust monitoring strategies accordingly.
- : Automated notifications for ensure that response teams can act swiftly to potential incidents.
- : Consistent evaluation of incidents related to safety allows for the recognition of trends and enhances detection abilities, boosting the overall efficiency of the EDR framework.
By adopting these practices, manufacturers can uphold a that effectively reduces risks linked to through endpoint detection.
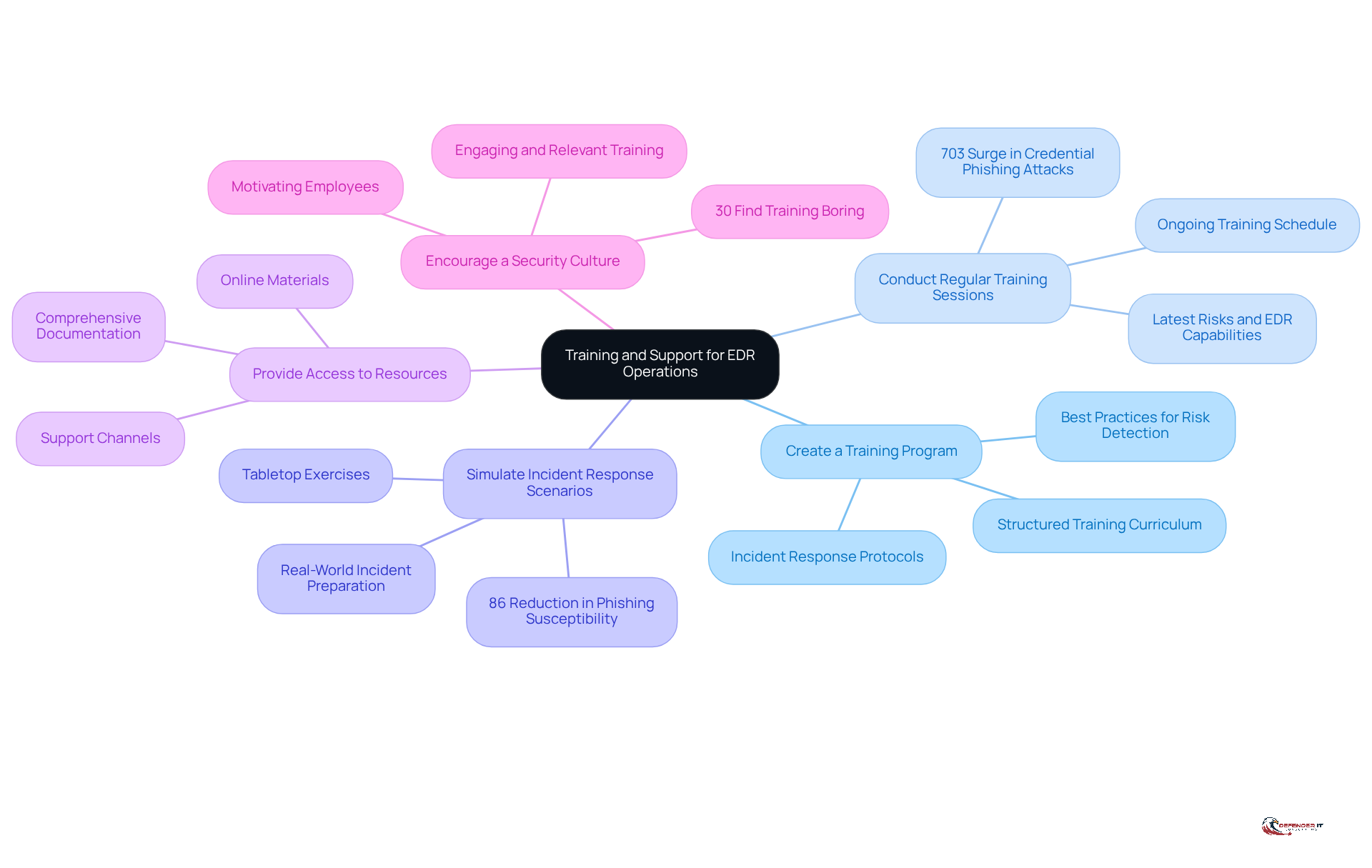
Provide Training and Support for EDR Operations
To enhance the effectiveness of endpoint detection solutions, thorough training and support for staff engaged in EDR operations are vital. Key practices include:
- Create a Training Program: Establish a structured training program that encompasses the functionalities of the EDR system, protocols, and best practices for risk detection.
- Conduct Regular : Schedule ongoing to keep staff informed about the latest risks, EDR capabilities, and response strategies. This ensures they remain proficient in a rapidly evolving landscape. Notably, a 703% surge in credential phishing attacks in the second half of 2024 underscores the necessity for effective training programs.
- Simulate Scenarios: Implement tabletop exercises and simulations to prepare staff for real-world s. This approach enhances their in handling actual threats. As Glenn Karpsen states, “Organizations with can by up to 86% compared to their initial baseline.”
- Provide Access to Resources: Ensure personnel have access to comprehensive documentation, online materials, and support channels to assist them in effectively utilizing the EDR platform.
- Encourage a : Foster a culture of security awareness throughout the organization, motivating all employees to prioritize . Given that 30% of employees find current training boring and ineffective, it is crucial to make training engaging and relevant.
By investing in these training and support initiatives, manufacturers can empower their teams to effectively leverage EDR systems for endpoint detection, significantly enhancing their overall cybersecurity posture.
Conclusion
Implementing effective endpoint detection solutions is essential for enhancing cybersecurity in the manufacturing sector. By concentrating on the core components of EDR systems, integrating these solutions with existing security infrastructure, and prioritizing continuous monitoring and staff training, manufacturers can significantly strengthen their defenses against evolving cyber threats.
Key practices include:
- Identifying critical EDR components
- Ensuring seamless integration with current protective measures
- Maintaining a proactive stance through continuous monitoring and threat intelligence
Furthermore, investing in comprehensive training programs empowers staff to effectively utilize EDR systems, fostering a culture of security awareness throughout the organization.
As the cybersecurity landscape continues to evolve, manufacturers must remain vigilant and proactive in their approach. By adopting these best practices for endpoint detection, organizations can not only safeguard their assets but also stay ahead of potential threats, ensuring a more secure and resilient manufacturing environment.
Frequently Asked Questions
What are the core components of Endpoint Detection and Response (EDR) systems?
The core components of EDR systems include Data Collection Agents, a Centralized Management Console, Risk Intelligence Integration, Automated Response Features, and an Analytics Engine.
What is the role of Data Collection Agents in EDR systems?
Data Collection Agents are lightweight agents installed on endpoints to gather data on system activities, processes, and network connections.
How does a Centralized Management Console benefit security teams?
A Centralized Management Console allows security teams to monitor and manage endpoint activities from a single location, providing real-time visibility and control.
What is the importance of Risk Intelligence Integration in EDR solutions?
Risk Intelligence Integration enhances the EDR’s ability to identify known and emerging risks by providing context for alerts and incidents.
What are Automated Response Features in EDR systems?
Automated Response Features include mechanisms for automated reactions to identified risks, such as isolating impacted endpoints or obstructing harmful processes.
How does the Analytics Engine function within an EDR system?
The Analytics Engine analyzes gathered information to recognize patterns and irregularities that may indicate incidents, facilitating proactive risk identification.
Why is it important for manufacturers to implement EDR systems effectively?
Implementing EDR systems effectively helps manufacturers establish a robust foundation for their endpoint detection strategy, enhancing their overall cybersecurity posture.
List of Sources
- Identify Core Components of EDR Systems
- acronis.com (https://acronis.com/en/blog/posts/best-edr-endpoint-detection-and-response-solutions-in-2026)
- What Is Endpoint Detection and Response (EDR)? How Does It Work? | Fortinet (https://fortinet.com/resources/cyberglossary/what-is-edr)
- What is Endpoint Detection and Response (EDR)? | IBM (https://ibm.com/think/topics/edr)
- paloaltonetworks.com (https://paloaltonetworks.com/cyberpedia/what-is-endpoint-detection-and-response-edr)
- What is EDR? Endpoint Detection & Response Defined | CrowdStrike (https://crowdstrike.com/en-us/cybersecurity-101/endpoint-security/endpoint-detection-and-response-edr)
- Integrate EDR with Existing Security Infrastructure
- Integration of Your Security Tools Is Crucial for Great Defense – Hornetsecurity – Next-Gen Microsoft 365 Security (https://hornetsecurity.com/en/blog/security-tool-integration)
- Cybersecurity Trends in 2026: Rising Threats & Strategies | TierPoint, LLC (https://tierpoint.com/blog/cybersecurity/cybersecurity-trends)
- Endpoint Detection and Response Market Size, Share & Forecast 2032 (https://credenceresearch.com/report/endpoint-detection-and-response-market)
- Effective Endpoint Security Policy in 2026 (https://sentinelone.com/cybersecurity-101/endpoint-security/endpoint-security-policy)
- Endpoint Detection and Response Market Size, Share & Growth Report 2033 (https://snsinsider.com/reports/endpoint-detection-and-response-market-3088)
- Implement Continuous Monitoring and Threat Intelligence
- Proactive IT Management: 20 Industry Stats You Should Know (https://corcystems.com/insights/proactive-it-management-20-industry-stats-you-should-know)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Why Continuous Security Monitoring Is A Requirement In 2024 (https://purplesec.us/learn/continuous-security-monitoring)
- IBM X-Force 2025 Threat Intelligence Index (https://ibm.com/thought-leadership/institute-business-value/en-us/report/2025-threat-intelligence-index)
- The Role of Threat Intelligence in EDR (https://jumpcloud.com/it-index/the-role-of-threat-intelligence-in-edr)
- Provide Training and Support for EDR Operations
- Cyber threats to watch in 2026 – and other cybersecurity news (https://weforum.org/stories/2026/02/2026-cyberthreats-to-watch-and-other-cybersecurity-news)
- Security Awareness Training: USA 2025 Statistics | Infrascale (https://infrascale.com/security-awareness-training-statistics-usa)
- Why Every Employee Needs Cybersecurity and AI Training Today (https://cybersecurityventures.com/why-every-employee-needs-cybersecurity-and-ai-training-today)
- Security Awareness Training Statistics 2025 [100+ Studies] | Brightside AI Blog (https://brside.com/blog/security-awareness-training-statistics-2025-100-studies)
- Fortinet Report Finds Nearly 70% of Organizations Say Their Employees Lack Fundamental Security Awareness (https://fortinet.com/corporate/about-us/newsroom/press-releases/2024/fortinet-report-finds-70-percent-of-organizations-lack-fundamental-security-awareness-for-employees)