Introduction
Vulnerability scanning has become an essential element for organizations operating within regulated industries, where compliance is not merely a formality but a fundamental requirement. By implementing robust scanning solutions, organizations can effectively identify and address potential security threats, thereby strengthening their overall cybersecurity posture. However, given the rapid evolution of cyber threats and the shifting landscape of regulatory requirements, how can organizations ensure that their vulnerability scanning practices remain both effective and compliant? This article explores four best practices designed to enhance vulnerability scanning efforts, ensuring robust security while adhering to industry standards.
Understand the Importance of Vulnerability Scanning in Regulated Industries
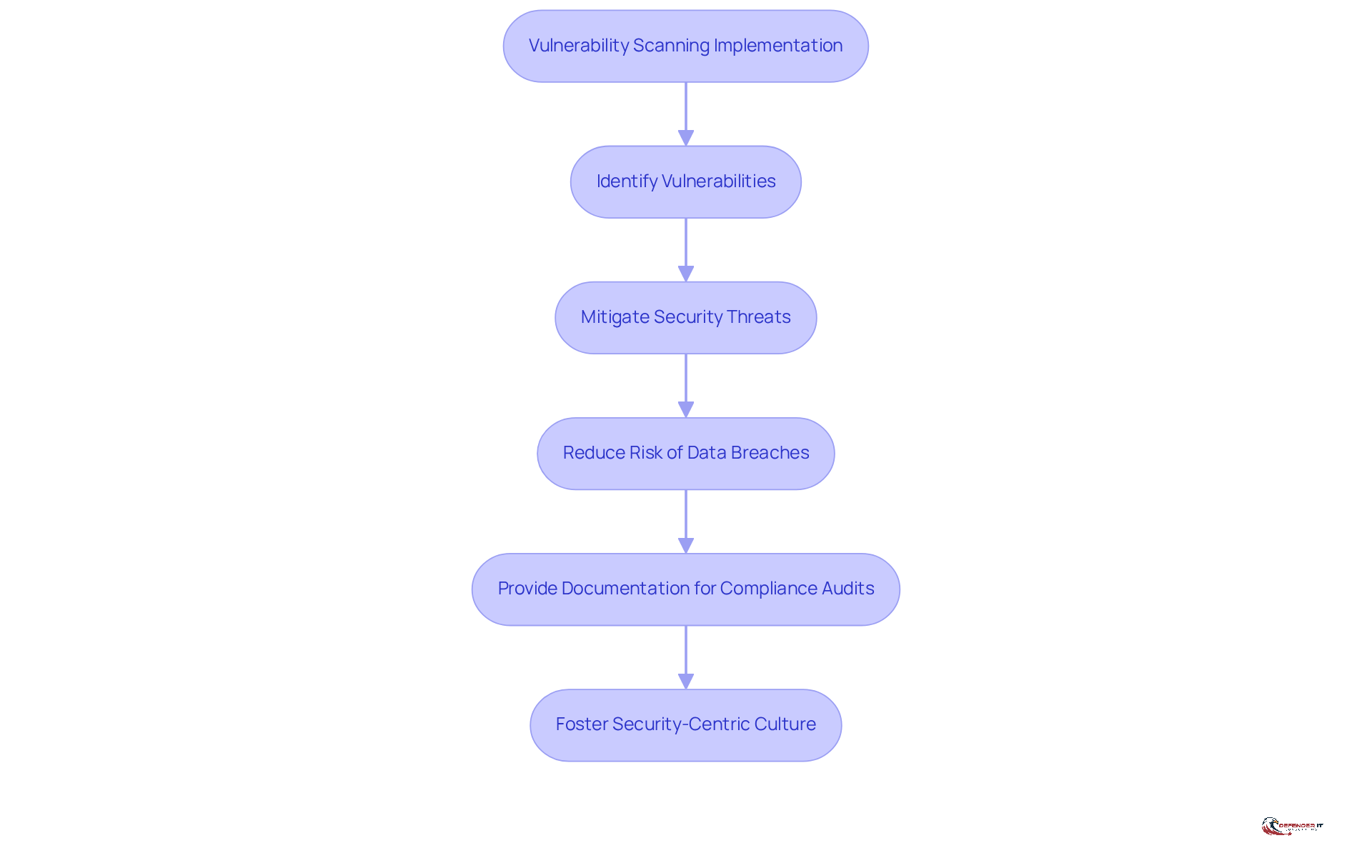
is essential for organizations operating in regulated sectors such as finance, healthcare, and government, where is critical. Frameworks like PCI DSS, HIPAA, and GDPR mandate regular assessments to identify and mitigate potential security threats. For instance, in 2023, , highlighting the urgent need for .
By implementing a solution, organizations can early detect vulnerabilities in their systems, significantly reducing the risk of data breaches and . Furthermore, ongoing monitoring not only strengthens security but also provides vital documentation for , thereby reinforcing trust with clients and stakeholders.
As emphasize, ; it involves fostering a that prioritizes the protection of valuable data.
Select and Implement Effective Vulnerability Scanning Tools and Methodologies
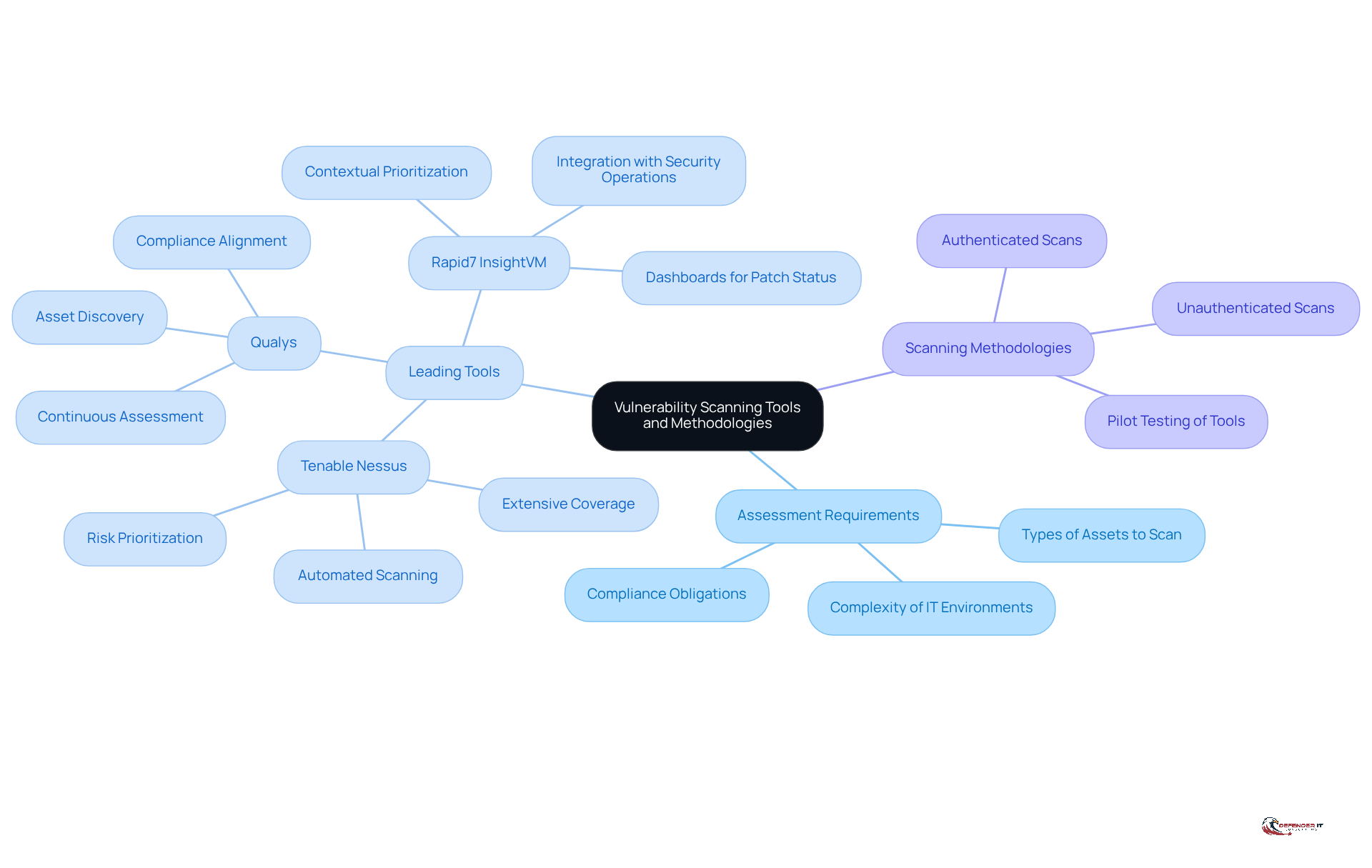
Choosing the appropriate is essential for . Organizations need to assess their specific requirements, including the types of assets to scan, the complexity of their IT environments, and . Leading tools such as Tenable Nessus, Qualys, and Rapid7 InsightVM provide a range of features, including , , and detailed reporting capabilities. For instance, Tenable Nessus is recognized for its extensive coverage across IT, cloud, and APIs, while Qualys is particularly strong in asset discovery and continuous assessment. Rapid7 InsightVM stands out with its contextual prioritization and seamless integration with security operations.
It is advisable to conduct , particularly a , to assess their effectiveness in identifying vulnerabilities within the organization’s infrastructure. Additionally, employing a combination of – such as authenticated and unauthenticated scans – ensures thorough coverage and improves the accuracy of results. This comprehensive approach not only strengthens the but also adheres to established in risk management.
Establish Continuous Monitoring and Regular Assessment Protocols
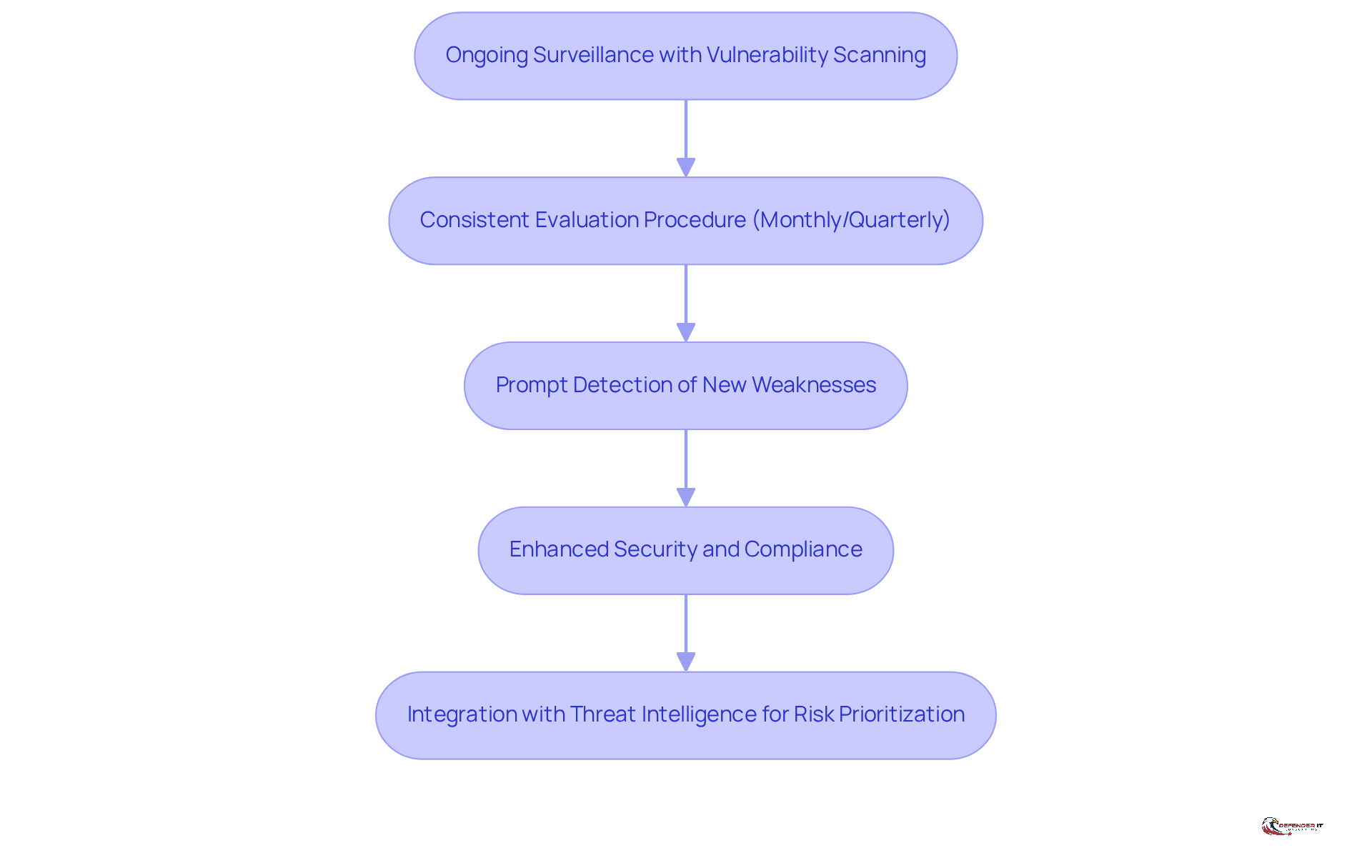
Ongoing surveillance through a is essential for organizations aiming to stay ahead of . By implementing a consistent evaluation procedure, such as monthly or quarterly , entities can promptly detect new weaknesses as they arise. This proactive strategy not only enhances security but also incorporates a to meet that mandate frequent assessments.
Following the recommendations of NIST, institutions must conduct revised risk evaluations to link threats and vulnerabilities to business outcomes, underscoring the necessity of . The implementation of a significantly improves ongoing monitoring, facilitating of weaknesses and enabling swift remediation. Moreover, utilizing a and integrating its results with threat intelligence provides a deeper understanding of potential risks, allowing organizations to prioritize their remediation efforts effectively.
For example, the ISCM program detailed in illustrates how can be implemented to sustain a robust . As we approach 2026, organizations are increasingly adopting these practices, recognizing that regular evaluations are vital for ensuring compliance with industry standards and enhancing overall security.
Align Vulnerability Scanning with Compliance and Reporting Requirements
To effectively address weaknesses, companies must align their scanning practices with mandated by regulations such as PCI DSS, HIPAA, and ISO 27001. These frameworks necessitate documented proof of , making it essential for organizations to establish clear reporting protocols. Such protocols should detail the results of , including the severity of identified issues and the actions taken to resolve them.
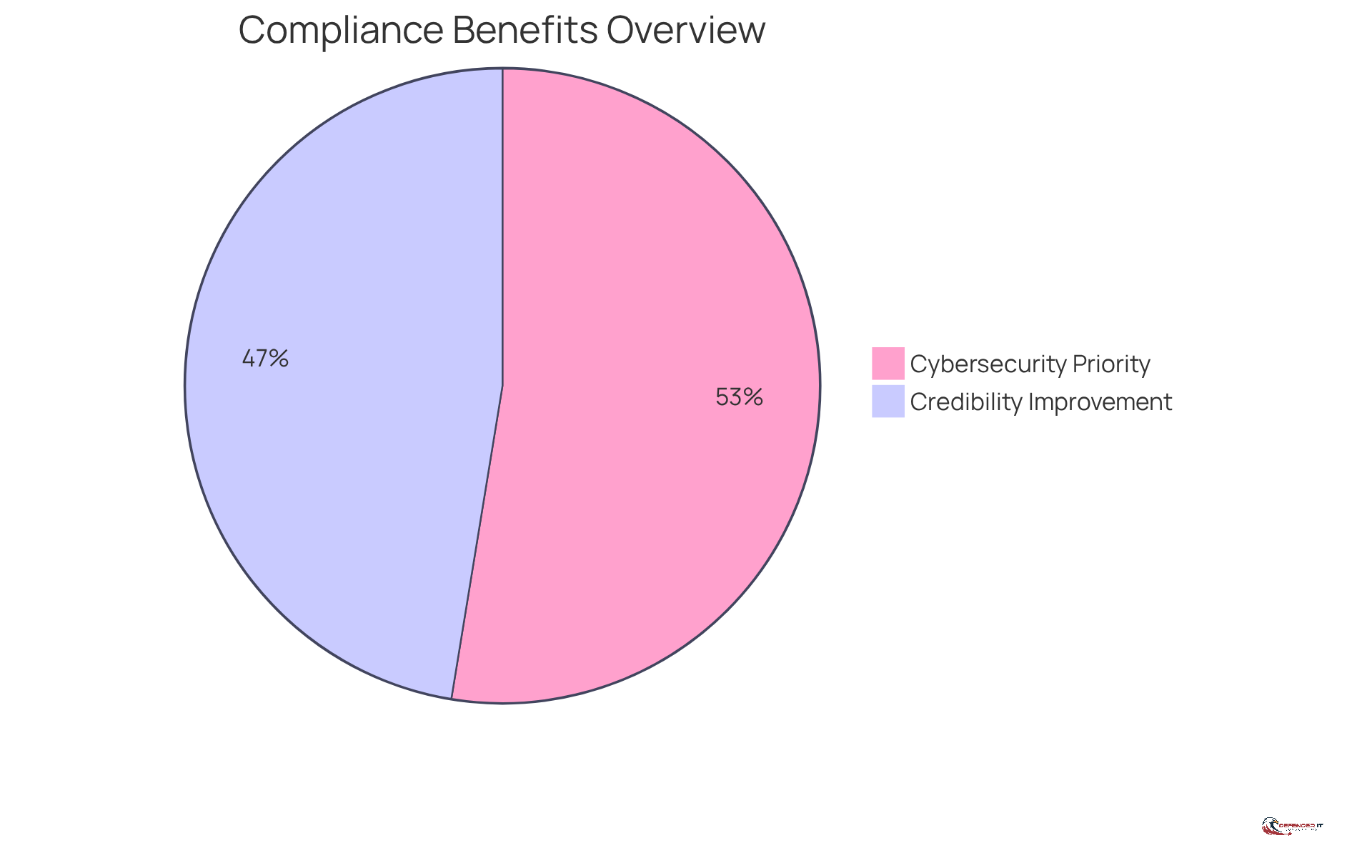
For instance, entities that have successfully implemented have reported significant improvements in their . Notably, 46% of these organizations indicate that aligning their scanning practices with has enhanced their credibility and reduced the risk of penalties associated with non-compliance. Furthermore, 51% of entities prioritize , underscoring the critical nature of these initiatives.
By maintaining comprehensive records and demonstrating commitment to , organizations not only bolster their compliance efforts but also strengthen their overall security framework. Additionally, with the upcoming compliance deadline of February 16, 2026, for the revised , it is imperative for organizations to remain proactive in their by utilizing a solution.
Conclusion
Effective vulnerability scanning solutions are essential for organizations, especially those in regulated industries where compliance is critical. By prioritizing vulnerability management, organizations not only protect sensitive data but also foster a security culture that resonates with clients and stakeholders. Proactively identifying and addressing vulnerabilities is vital for maintaining trust and ensuring compliance with industry regulations.
Key practices include:
- Selecting scanning tools that meet specific organizational needs
- Conducting continuous monitoring to stay ahead of emerging threats
- Aligning scanning efforts with compliance and reporting requirements
These strategies highlight the necessity of a comprehensive approach that fulfills regulatory obligations while enhancing overall cybersecurity posture. By integrating tools such as Tenable Nessus, Qualys, and Rapid7 InsightVM, organizations can effectively manage risks and maintain a strong defense against potential breaches.
As the cybersecurity landscape evolves, the importance of vulnerability scanning remains paramount. Organizations must stay vigilant and proactive in their vulnerability management strategies, particularly with impending compliance deadlines. By adopting best practices for vulnerability scanning, companies can safeguard their assets and position themselves as leaders in security and compliance, ultimately contributing to a safer digital environment across industries.
Frequently Asked Questions
Why is vulnerability scanning important in regulated industries?
Vulnerability scanning is crucial in regulated sectors such as finance, healthcare, and government because it helps organizations comply with strict regulations like PCI DSS, HIPAA, and GDPR, which mandate regular assessments to identify and mitigate security threats.
What are some statistics that highlight the need for vulnerability scanning in healthcare?
In 2023, healthcare organizations reported an average of 1.99 data breaches daily, underscoring the urgent need for proactive security measures like vulnerability scanning.
How does vulnerability scanning help organizations protect sensitive information?
By implementing a vulnerability scanning solution, organizations can detect vulnerabilities early, significantly reducing the risk of data breaches and safeguarding sensitive information.
What additional benefits does ongoing monitoring provide for organizations?
Ongoing monitoring strengthens security and provides vital documentation for compliance audits, which helps reinforce trust with clients and stakeholders.
What do cybersecurity experts say about effective risk management?
Cybersecurity experts emphasize that effective risk management goes beyond regulatory compliance; it involves fostering a security-centric culture that prioritizes the protection of valuable data.
List of Sources
- Understand the Importance of Vulnerability Scanning in Regulated Industries
- 9 Quotes that Capture the State of Offensive Security (https://netspi.com/blog/executive-blog/security-industry-trends/quotes-on-the-state-of-offensive-security)
- New HIPAA Regulations in 2026 (https://hipaajournal.com/new-hipaa-regulations)
- OCR’s Latest HIPAA Guidance: Strategic Measures to Protect Your Systems and Data (https://bakerdonelson.com/ocrs-latest-hipaa-guidance-strategic-measures-to-protect-your-systems-and-data)
- Healthcare Data Breach Statistics (https://hipaajournal.com/healthcare-data-breach-statistics)
- Vulnerability Management Metrics: 20 Key KPIs to Track (https://sentinelone.com/cybersecurity-101/cybersecurity/vulnerability-management-metrics)
- Select and Implement Effective Vulnerability Scanning Tools and Methodologies
- Best Vulnerability Scanning Tool for 2026- Top 10 List (https://securityboulevard.com/2025/12/best-vulnerability-scanning-tool-for-2026-top-10-list)
- Top 11 Open Source Vulnerability Management Tools for 2026 (https://defectdojo.com/blog/top-11-open-source-vulnerability-management-tools-for-2026)
- 10 Best Vulnerability Scanning Tools in 2026 Ranked (https://invicti.com/blog/web-security/10-best-vulnerability-scanning-tools)
- 9 Vulnerability Management Tools in 2026 | SentinelOne (https://sentinelone.com/cybersecurity-101/cybersecurity/8-vulnerability-management-tools)
- Establish Continuous Monitoring and Regular Assessment Protocols
- RMF Continuous Monitoring Strategy [for 2026] (https://ipkeys.com/blog/rmf-continuous-monitoring)
- Top NIST Best Practices for Enhancing Cyber Resilience in 2026 (https://panorays.com/blog/nist-best-practices)
- linkedin.com (https://linkedin.com/posts/gerry-blass-917a482_continuousmonitoring-cybersecurity-2026standards-activity-7426626399626514432-LSFE)
- Five things to watch in cybersecurity for 2026 | Federal News Network (https://federalnewsnetwork.com/cybersecurity/2026/01/five-things-to-watch-in-cybersecurity-for-2026)
- Industry News 2026 The 6 Cybersecurity Trends That Will Shape 2026 (https://isaca.org/resources/news-and-trends/industry-news/2026/the-6-cybersecurity-trends-that-will-shape-2026)
- Align Vulnerability Scanning with Compliance and Reporting Requirements
- 110 security and compliance statistics for tech leaders to know in 2025 (https://vanta.com/resources/compliance-statistics)
- HIPAA NPRM: A New Era of Healthcare Cybersecurity & Compliance (https://avertium.com/blog/hipaa-notice-of-proposed-rulemaking-a-new-era-of-healthcare-cybersecurity-compliance)
- Critical HIPAA Updates for 2026 (https://corsicatech.com/blog/hipaa-updates-security-rules)
- HIPAA Updates and HIPAA Changes in 2026 (https://hipaajournal.com/hipaa-updates-hipaa-changes)
- 2026 HIPAA Changes: New Security Rule Requirements (https://hipaavault.com/resources/2026-hipaa-changes)