Introduction
As cyber threats evolve, the need for robust application security measures, such as fuzzing, becomes paramount. This automated testing technique not only uncovers vulnerabilities that traditional methods often miss but also empowers developers to enhance application security proactively. With 82% of organizations facing unaddressed vulnerabilities, cybersecurity leaders must consider how to effectively integrate fuzzing into their security frameworks to mitigate emerging threats.
Define Application Fuzzing: Understanding the Basics
Fuzz testing, an automated technique, plays a crucial role in identifying vulnerabilities within applications by inputting unexpected data. The primary goal of fuzz testing is to uncover vulnerabilities that attackers might exploit, ultimately enhancing the security posture of applications. By simulating unexpected inputs, fuzz testing enables developers to:
- Understand software behavior under stress
- Identify weaknesses often overlooked by traditional testing methods
This method is particularly effective in recognizing issues related to input validation, memory management, and error handling, which are essential for ensuring robust application protection. Ultimately, fuzz testing serves as a vital tool in the ongoing effort to safeguard applications from emerging threats.
Contextualize Fuzzing: Its Role in Cybersecurity
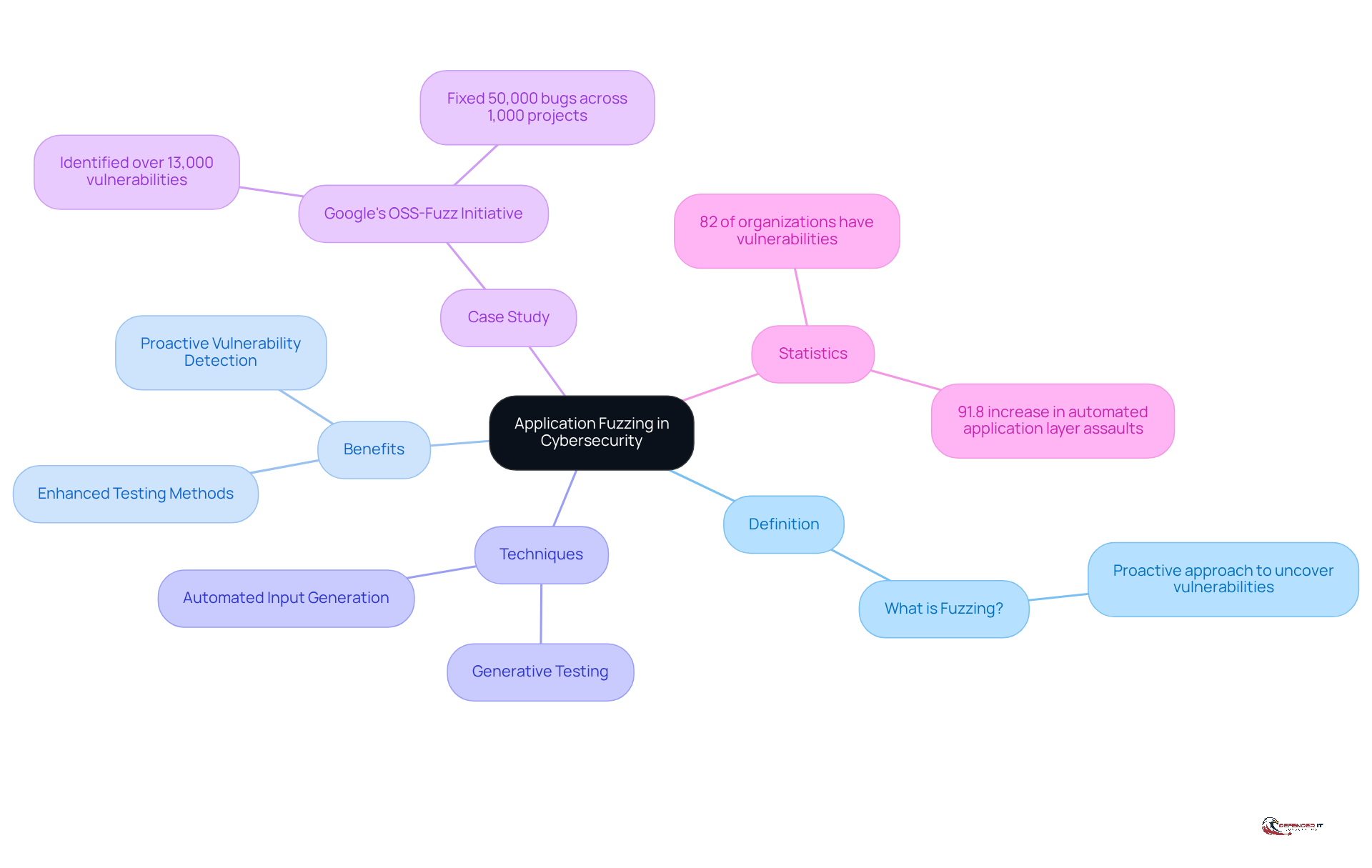
In an era where cyber threats are increasingly sophisticated, understanding what is application fuzzing? becomes a critical strategy for preemptively identifying vulnerabilities. To understand what is application fuzzing?, it is important to note that fuzzing serves as a proactive approach to uncover weaknesses before they can be exploited by cybercriminals. Traditional testing methods frequently fail to uncover critical vulnerabilities, leaving systems exposed to potential threats. Fuzzing, often discussed when exploring what is application fuzzing?, enhances these methods through automated input generation and testing, enabling a more comprehensive assessment of software security.
For instance, generative testing can theoretically produce an endless array of distinct test scenarios, greatly enhancing flaw detection capabilities. Organizations utilize testing techniques to evaluate web applications, APIs, and network protocols, ensuring they can withstand diverse attack vectors.
Google’s OSS-Fuzz initiative has effectively uncovered more than 13,000 weaknesses and 50,000 errors across 1,000 projects, showcasing the effectiveness of random testing in improving software robustness. Integrating fuzzing into protection frameworks allows businesses to significantly mitigate risk exposure, which raises the question: what is application fuzzing, especially considering that 82% of organizations have vulnerabilities associated with unaddressed weaknesses? This method is especially crucial as automated application layer assaults, known as ‘bad bots’, increased by 91.8% last year, highlighting the necessity for strong protective measures.
Trace the Origins: The Evolution of Application Fuzzing
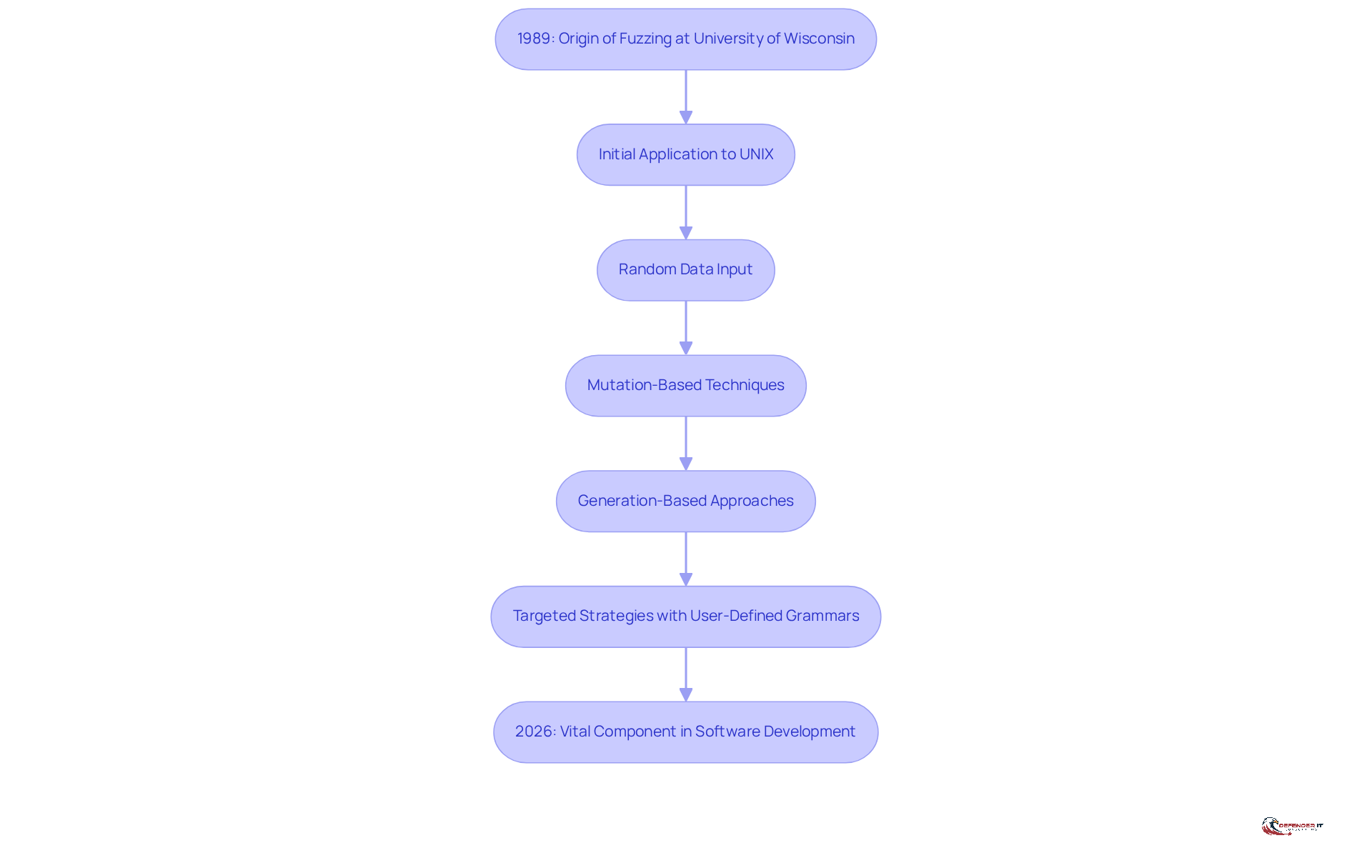
Fuzzing originated in 1989 at the University of Wisconsin as a groundbreaking method for software testing. Initially applied to UNIX applications, fuzz testing involved sending random data to input parsers, effectively revealing vulnerabilities that could lead to application crashes or security breaches. Over the years, this testing method has evolved significantly, incorporating advanced techniques such as mutation-based and generation-based approaches. These innovations have enabled fuzzers to produce more sophisticated test cases, thereby enhancing their capacity to identify complex vulnerabilities.
Key milestones in the development of fuzz testing include the shift from simple random input generation to more targeted strategies that utilize user-defined input grammars. This evolution has improved testing accuracy, allowing it to address safety concerns in increasingly complex digital environments. By 2026, fuzz testing techniques have solidified their role as a vital component of modern software development and security measures, with widespread application across various industries, particularly in sectors where protection is paramount. Continuous advancements in testing methodologies, including vulnerability-coverage-driven approaches, have further refined the process, ensuring organizations can proactively identify and mitigate potential security threats.
Fuzzing is a technique that raises the question of what is application fuzzing, as it has proven to be effective at uncovering vulnerabilities that other methods often miss, making it an indispensable tool in the cybersecurity arsenal. However, the labor-intensive nature of fuzz testing can hinder its broader implementation. For instance, the identification of CVE-2023-21041 through ongoing testing highlights the practical importance of this method in detecting critical weaknesses. As Jun Xu, an assistant professor of computer science, emphasizes, ‘Fuzzing, or what is application fuzzing?, is a popular technique to find hidden vulnerabilities in programs such as email and PDF readers that we all use in our daily lives.’ This underscores the critical need for organizations to incorporate fuzz testing into their security strategies as software systems grow increasingly complex.
Examine Key Characteristics: Techniques and Methodologies of Fuzzing
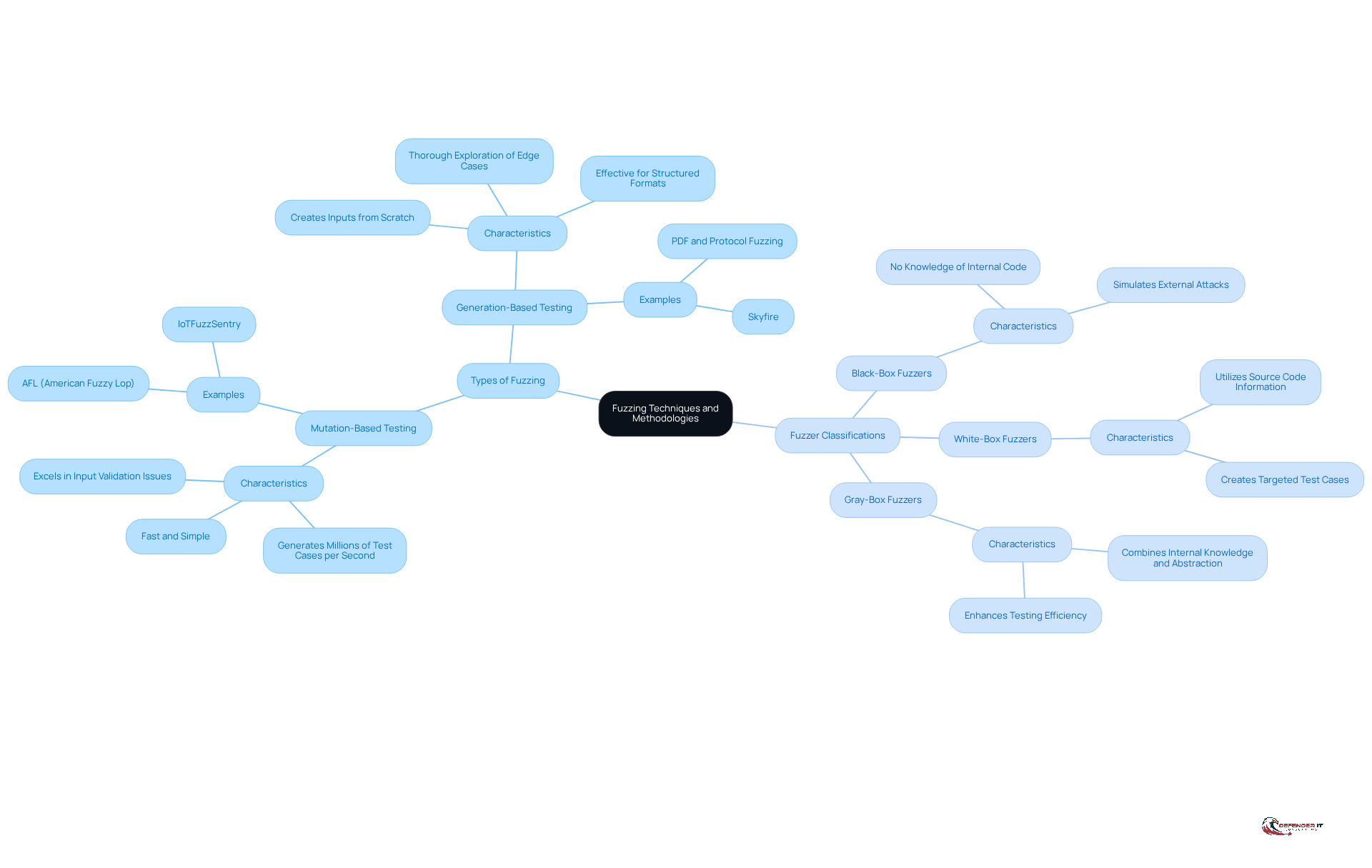
Fuzzing methods are critical in identifying vulnerabilities, and they can be categorized into two primary types: mutation-based and generation-based testing. Mutation-based testing involves taking existing valid inputs and altering them to create new test cases, making it a faster and simpler approach to implement. For instance, mutation-based testing can generate millions of test cases per second, excelling in rapid bug discovery, particularly for input validation issues and buffer overflows.
In contrast, generation-based testing creates inputs from scratch based on predefined specifications. This allows for a thorough exploration of edge cases and complex scenarios. This approach is especially efficient for organized formats such as PDFs and protocols, as it can detect minor weaknesses that mutation-based testing might overlook. Recent advancements indicate that hybrid methods, which combine the strengths of both mutation and generation-based techniques, yield better results by exploiting their complementary strengths, enhancing overall flaw discovery capabilities.
Fuzzers can also be classified into three types based on their access to the application’s internal workings: black-box, white-box, and gray-box fuzzers. Black-box fuzzers operate without any knowledge of the underlying code, simulating external attacks to evaluate the system’s defenses. White-box fuzzers, on the other hand, utilize source code information to create more targeted and effective test cases. Gray-box fuzzers combine elements of both, leveraging some internal knowledge while maintaining a level of abstraction, which can enhance testing efficiency.
For cybersecurity leaders aiming to fortify their defenses against evolving threats, understanding what is application fuzzing? is vital. Current trends indicate a growing reliance on hybrid methods, which merge the strengths of mutation and generation-based testing. This enables organizations to improve their vulnerability discovery capabilities. As vulnerability testing continues to evolve, staying informed about these techniques will be essential for maintaining robust security postures in an increasingly complex threat landscape. Notably, fuzzing has matured since its introduction in the 1990s and has been credited with finding thousands of bugs in critical infrastructure software, underscoring its importance in modern cybersecurity practices.
Conclusion
In an era where cyber threats are increasingly sophisticated, application fuzzing emerges as a critical defense mechanism. This technique is essential for preemptively identifying vulnerabilities that could be exploited by malicious actors. Fuzz testing simulates unexpected inputs, improving traditional testing methods and strengthening application security, allowing organizations to protect their digital assets more effectively.
Throughout this discussion, several key insights have been highlighted. The evolution of fuzzing from its origins in the late 1980s to its current status as a fundamental component of modern software security has been detailed. The two primary types of fuzzing – mutation-based and generation-based testing – along with their respective methodologies and the importance of hybrid approaches have been examined. Additionally, the effectiveness of fuzz testing in uncovering critical vulnerabilities has been underscored, particularly given the increasing sophistication of cyber threats.
In light of these insights, it is imperative for cybersecurity leaders to prioritize the integration of application fuzzing into their security strategies. Organizations struggle to keep pace with the rapidly evolving landscape of cyber threats. Failing to adopt fuzz testing could result in critical vulnerabilities going undetected. Embracing this proactive approach is crucial for organizations aiming to stay ahead of potential threats and ensure the integrity of their applications in an increasingly complex digital environment. Organizations that neglect to implement fuzz testing risk exposing themselves to significant security breaches.
Frequently Asked Questions
What is application fuzzing?
Application fuzzing, also known as fuzz testing, is an automated technique used to identify vulnerabilities within applications by inputting unexpected data.
What is the primary goal of fuzz testing?
The primary goal of fuzz testing is to uncover vulnerabilities that attackers might exploit, thereby enhancing the security posture of applications.
How does fuzz testing help developers?
Fuzz testing helps developers understand software behavior under stress and identify weaknesses that are often overlooked by traditional testing methods.
What types of issues can fuzz testing recognize?
Fuzz testing is particularly effective in recognizing issues related to input validation, memory management, and error handling.
Why is fuzz testing important for application security?
Fuzz testing serves as a vital tool in the ongoing effort to safeguard applications from emerging threats by identifying and addressing vulnerabilities.
List of Sources
- Define Application Fuzzing: Understanding the Basics
- The Art of Fuzzing (https://brightsec.com/blog/fuzzing)
- Google Brings AI Magic to Fuzz Testing With Eye-Opening Results (https://securityweek.com/google-brings-ai-magic-to-fuzz-testing-with-eye-opening-results)
- Vulnerability Statistics Report (https://edgescan.com/stats-report)
- Performance Analysis of the Fuzzing Method in Detecting API Vulnerabilities in Mobile Healthcare Application X Based on OWASP API Security Top 10 (https://researchgate.net/publication/403516063_Performance_Analysis_of_the_Fuzzing_Method_in_Detecting_API_Vulnerabilities_in_Mobile_Healthcare_Application_X_Based_on_OWASP_API_Security_Top_10)
- Leveling Up Fuzzing: Finding more vulnerabilities with AI (https://security.googleblog.com/2024/11/leveling-up-fuzzing-finding-more.html)
- Contextualize Fuzzing: Its Role in Cybersecurity
- What is AI fuzzing? And what tools, threats and challenges generative AI brings (https://csoonline.com/article/567053/what-is-ai-fuzzing-and-why-it-may-be-the-next-big-cybersecurity-threat.html)
- 28 application security statistics that matter | ReversingLabs (https://reversinglabs.com/blog/28-application-security-stats-that-matter)
- Generative Fuzzing Enables Unlimited Test Cases for Software Security | Technuman (https://technuman.com/2026/03/14/generative-fuzzing)
- 45 Cybersecurity Statistics and Facts [2025] (https://onlinedegrees.sandiego.edu/cyber-security-statistics)
- Google Open Sources AI-Boosted Fuzzing Framework (https://darkreading.com/application-security/google-open-sources-ai-boosted-fuzzing-framework)
- Trace the Origins: The Evolution of Application Fuzzing
- Synopsys Fuzzing Report Identifies IoT and Industrial Control Systems Software as Most Vulnerable to Exploits (https://prnewswire.com/news-releases/synopsys-fuzzing-report-identifies-iot-and-industrial-control-systems-software-as-most-vulnerable-to-exploits-300501660.html)
- Through Pioneering “Fuzzing” Techniques, Stevens Researcher Makes Clear Progress Against Cyberattacks (https://stevens.edu/news/through-pioneering-fuzzing-techniques-stevens-researcher-makes-clear-progress-against-cyberattacks)
- Android Goes All-in on Fuzzing (https://security.googleblog.com/2023/08/android-goes-all-in-on-fuzzing.html)
- Fuzzing – Communications of the ACM (https://cacm.acm.org/research/fuzzing)
- Fuzzing: Progress, Challenges, and Perspectives (https://sciencedirect.com/org/science/article/pii/S154622182400170X)
- Examine Key Characteristics: Techniques and Methodologies of Fuzzing
- Table 2 Comparison of generation based fuzzers and mutation based fuzzers (https://researchgate.net/figure/Comparison-of-generation-based-fuzzers-and-mutation-based-fuzzers_tbl2_325577316)
- Generative vs. Mutation-Based Fuzzing (https://we-fuzz.io/blog/generative-vs-mutation-based-fuzzing)
- Black Box vs White Box vs Grey Box: A Critical Choice for Security Leaders – Hitachi Cyber (https://hitachicyber.com/blog/black-box-vs-white-box-vs-grey-box-a-critical-choice-for-security-leaders)
- Fuzz Testing Landscape 2025 | Blog | Code Intelligence (https://code-intelligence.com/blog/fuzz-testing-landscape-2025)