Introduction
As cyber threats evolve, organizations must confront the critical challenge of ensuring robust security measures. Penetration testing, often referred to as ethical hacking, serves as a proactive defense strategy that enables organizations to identify and address vulnerabilities before they can be exploited.
Organizations often grapple with the challenge of choosing between in-house management and outsourcing for penetration testing assessments. This article explores the essential role of penetration testing outsourcing, highlighting its benefits, the risks of neglecting such assessments, and how it can empower organizations to adapt to the ever-evolving landscape of cybersecurity threats.
Understanding the implications of outsourcing penetration testing can be the difference between proactive defense and vulnerability exploitation.
Understand the Importance of Penetration Testing for Business Security
In an era where cyber threats are increasingly sophisticated, penetration assessments, commonly referred to as ethical hacking, involve simulating cyber attacks on systems, networks, or applications to uncover vulnerabilities that malicious actors could exploit. By proactively identifying weaknesses, companies can rectify potential security gaps before they are exploited, thereby protecting sensitive data and preserving customer trust.
Entities that participate in routine security assessments are statistically less likely to experience data breaches. A recent study showed that 72% of participants believe security assessments have directly prevented a breach at their company. This proactive stance not only assists in achieving regulatory compliance but also demonstrates due diligence to stakeholders, enhancing the entity’s market reputation.
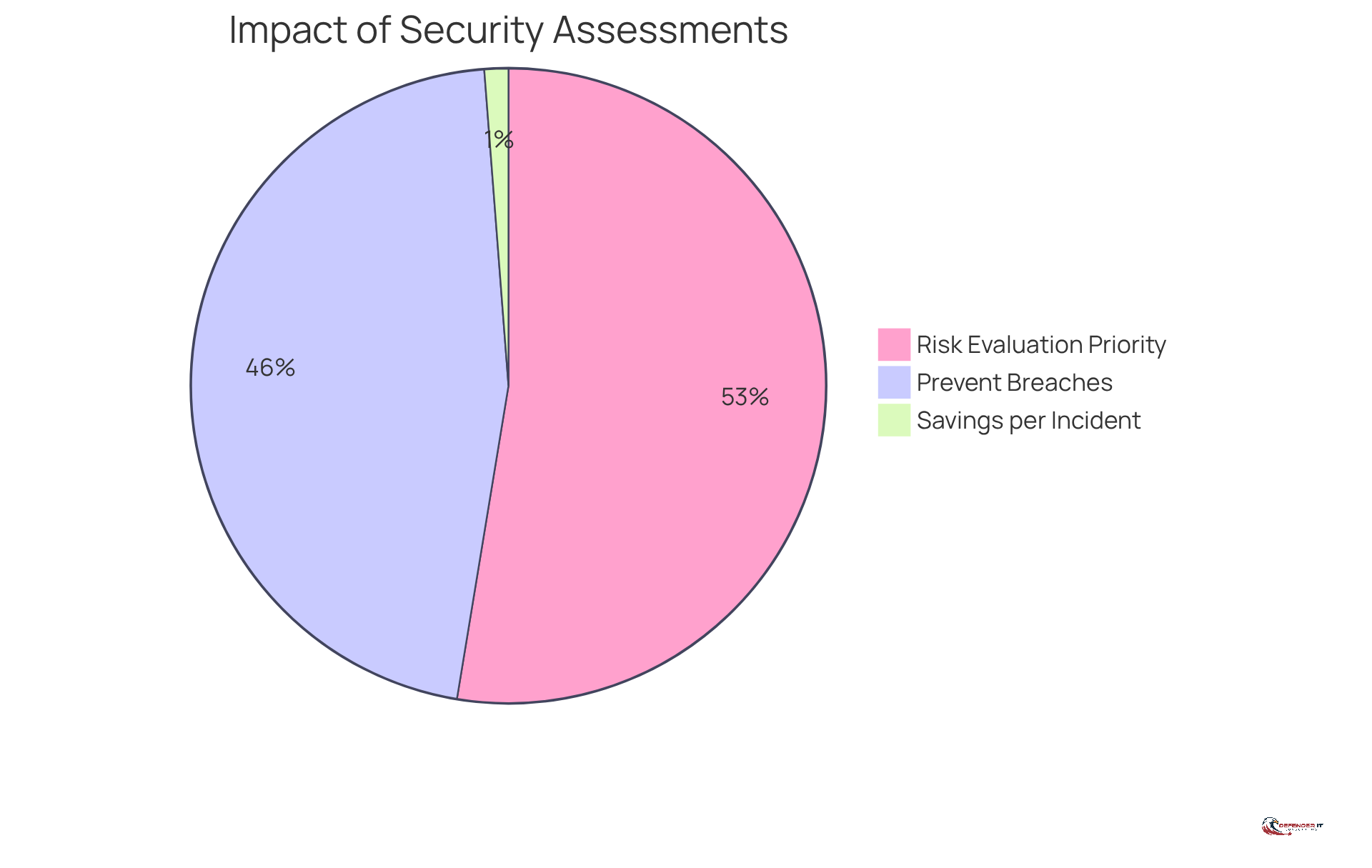
Moreover, security assessments yield actionable insights that inform investment and strategic decisions. With 82% of organizations prioritizing risk evaluation and vulnerability ranking as their main objective for security assessments, it becomes clear that these evaluations are essential for effective resource distribution to reduce risks. The median time to resolve issues from security assessments is approximately 67 days, with serious findings having a resolution rate of 69%, highlighting the need for prompt action to address vulnerabilities.
In light of evolving cyber threats, the significance of security assessments continues to increase. Organizations that conduct regular assessments can significantly lower their breach expenses, with proactive security measures saving an average of $1.9 million per incident. Furthermore, the security assessment market is anticipated to expand from $1.92 billion in 2023 to $6.98 billion by 2032, indicating the rising acknowledgment of its significance in the sector. As organizations navigate the complexities of cybersecurity, the role of vulnerability assessments will be pivotal in shaping their defensive strategies.
Explore the Benefits of Outsourcing Penetration Testing
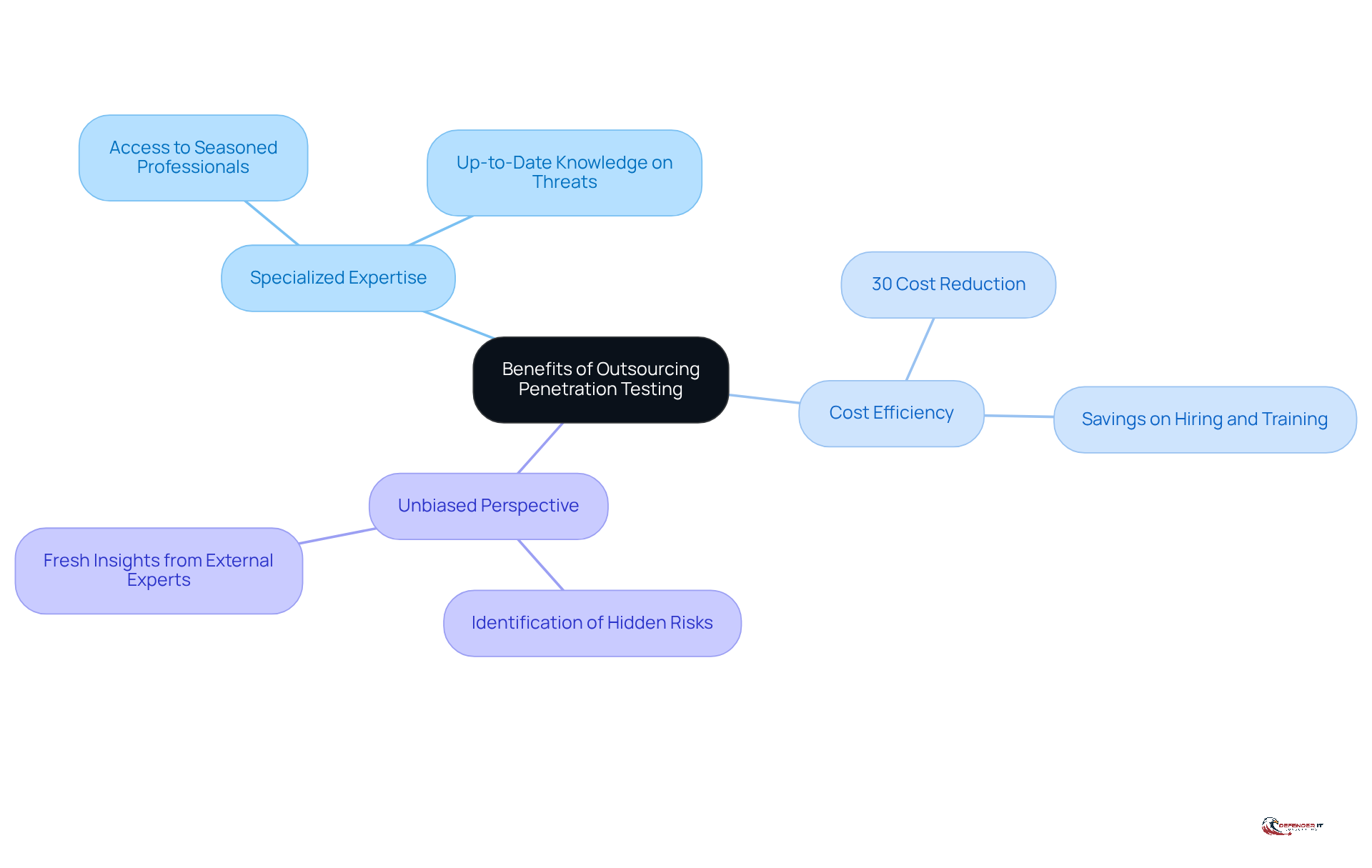
Outsourcing security assessments, specifically through penetration testing outsourcing, can significantly enhance an organization’s security posture while providing access to specialized expertise. One of the primary benefits is access to specialized expertise, as third-party providers employ seasoned professionals who are well-versed in the latest threats and vulnerabilities. This ensures that the evaluation is thorough and effective.
Outsourcing often proves to be more cost-efficient compared to the expenses associated with an in-house team. Organizations can save on hiring, training, and retaining skilled personnel, as well as on the costs associated with the tools and technologies required for effective penetration testing outsourcing. As stated in a report by Cybersecurity Ventures, companies that outsource their cybersecurity requirements can decrease expenses by as much as 30% while enhancing their protective results.
Additionally, third-party testers offer an unbiased viewpoint that can reveal vulnerabilities overlooked by internal teams. This fresh perspective is crucial for identifying hidden risks and ensuring a comprehensive security assessment. This strategic approach not only mitigates risks but also positions organizations to respond more effectively to evolving security challenges.
Examine the Risks of Neglecting Penetration Testing
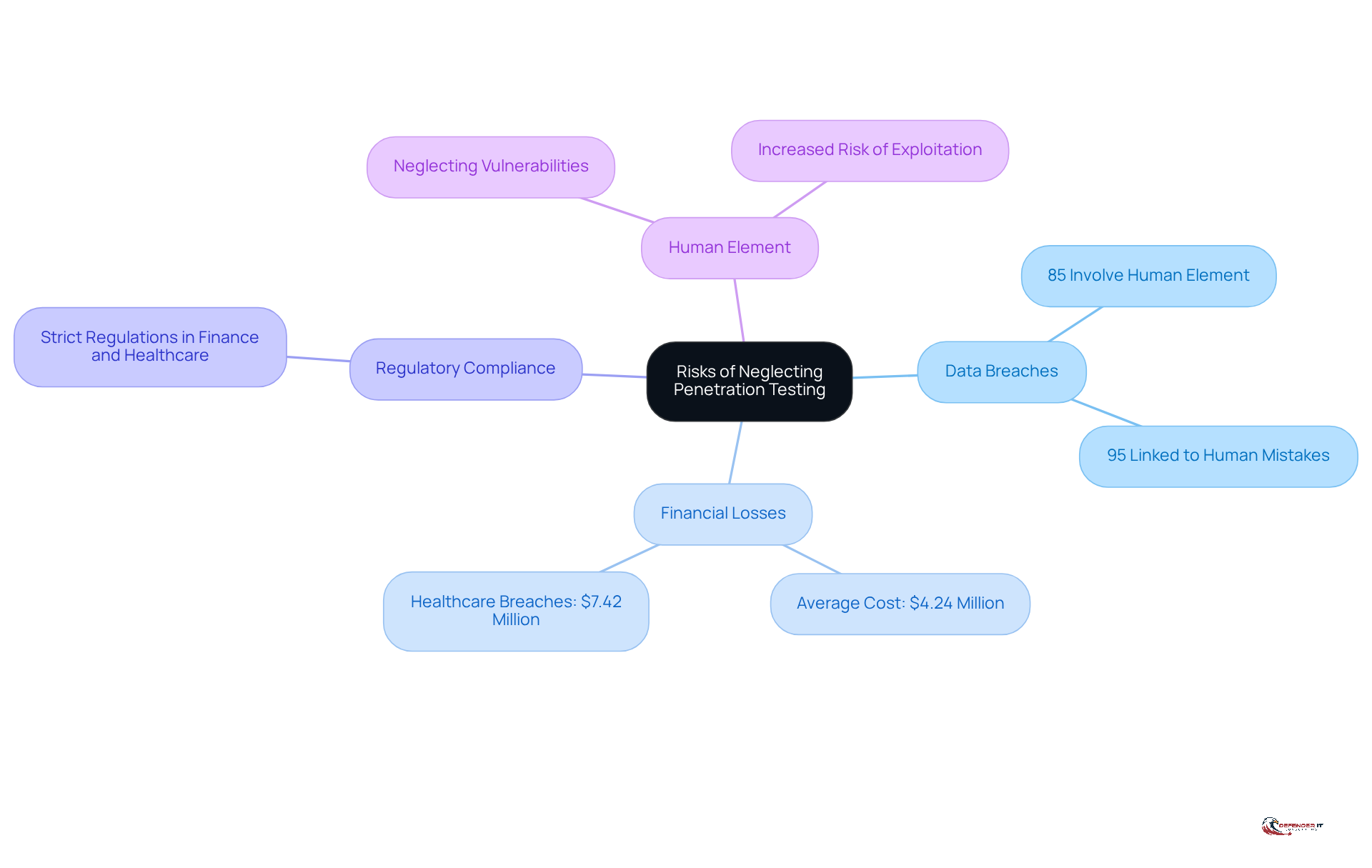
Neglecting security assessments can expose organizations to significant risks, including data breaches and financial losses. Regular assessments are crucial, as vulnerabilities can remain undetected, allowing cybercriminals to exploit them. The 2021 Verizon Data Breach Investigations Report highlighted that 85% of breaches involved a human element, often linked to unaddressed vulnerabilities. Additionally, 95% of cybersecurity breaches are linked to human mistakes, underscoring the essential requirement for comprehensive security assessments.
The financial consequences of neglecting security assessments can be staggering. According to IBM’s Cost of a Data Breach Report, the average cost of a data breach in 2021 was about $4.24 million. Significantly, healthcare data breaches incur an average expense of $7.42 million, demonstrating the serious financial consequences of overlooking security assessments in this vital sector. This figure does not encompass the long-term reputational damage that can ensue from a breach, potentially resulting in lost customers and diminished brand trust.
Regulatory compliance is another critical concern. Sectors like finance and healthcare encounter strict regulations that necessitate regular safety evaluations. Neglecting to perform security assessments can result in significant penalties and legal consequences, further worsening the financial effects of overlooking this essential protective measure. Furthermore, with 43% of cyber-attacks aimed at SMBs, and merely 14% of those entities being ready for such threats, the need for security assessments becomes increasingly clear. Organizations must prioritize security assessments to protect their assets and uphold compliance in an increasingly complex threat landscape. Moreover, the projected rise in global cybersecurity spending, expected to exceed $1.75 trillion from 2021 to 2025, highlights the growing recognition of the need for robust cybersecurity strategies, including vulnerability assessments.
Adapt to Evolving Cybersecurity Threats Through Outsourcing
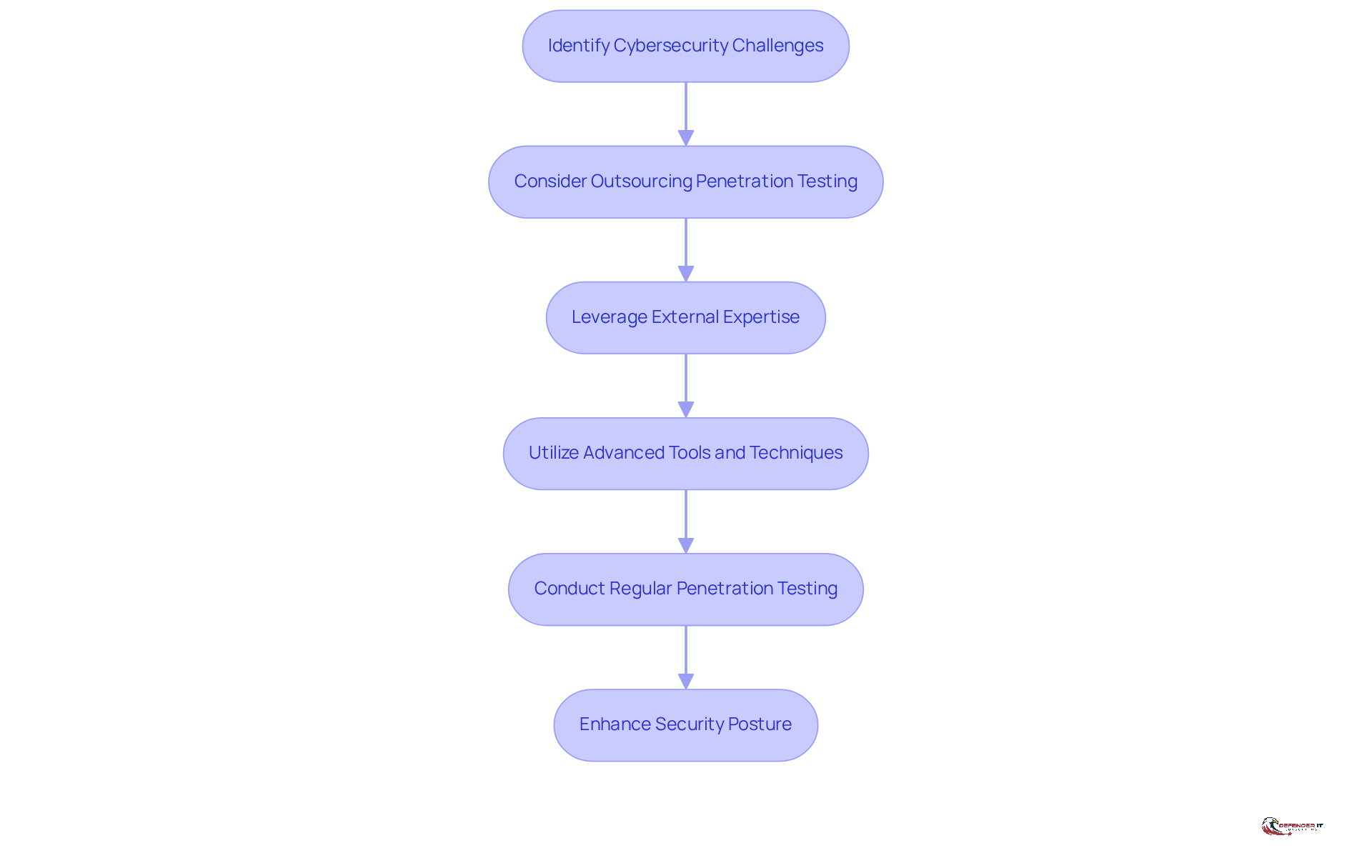
In an era where cyber threats evolve rapidly, organizations face significant challenges in maintaining robust security measures. To successfully navigate these changes, companies must adjust their security strategies, and the adoption of penetration testing outsourcing has become a crucial aspect of this adaptability. Leveraging external expertise allows companies to access the latest tools, techniques, and threat intelligence offered by specialized providers.
The increase of AI-driven cyber assaults requires a more advanced strategy for security evaluations. Outsourced providers utilize cutting-edge technologies and methods to effectively simulate these complex attacks, allowing companies to gain a clearer understanding of their vulnerabilities. Many organizations struggle to keep pace with the rapid evolution of AI-driven cyber threats, emphasizing the urgency for entities to adopt a proactive cybersecurity stance, which includes regular penetration testing.
Moreover, penetration testing outsourcing enables companies to rapidly expand their protective measures in reaction to new threats. As companies grow and their digital landscapes become more intricate, the need for thorough evaluations of protection increases. Penetration testing outsourcing provides the adaptability to modify testing frequency and scope based on the entity’s changing requirements, ensuring that protective measures stay strong and efficient. This strategic approach not only enhances security posture but also positions organizations to better withstand the evolving landscape of cyber threats. By embracing outsourced security assessments, organizations can not only enhance their defenses but also ensure they remain resilient against future cyber threats.
Conclusion
In an era where cyber threats are constantly evolving, outsourcing penetration testing has become essential for security leaders. By leveraging specialized expertise and resources from third-party providers, companies can effectively identify vulnerabilities and enhance their security posture. This ultimately safeguards sensitive data.
The article highlights several key arguments supporting the importance of penetration testing outsourcing:
- Regular security assessments significantly reduce the likelihood of data breaches, as evidenced by statistics showing that 72% of organizations believe these evaluations prevent incidents.
- Outsourcing proves to be a cost-efficient solution, allowing companies to save on hiring and training while accessing the latest technologies and methodologies.
- Neglecting penetration testing can expose organizations to significant financial losses and regulatory penalties, further underscoring the necessity of maintaining a robust security strategy.
As organizations navigate the complexities of cybersecurity, the significance of adopting outsourced penetration testing cannot be overstated. Embracing this approach not only enhances immediate security measures but also positions companies to adapt to emerging threats effectively. Security leaders must prioritize these assessments as a fundamental component of their cybersecurity strategy, ensuring their organizations remain resilient in the face of evolving challenges. Ultimately, the decision to outsource penetration testing can be the difference between robust security and vulnerability in a competitive market.
Frequently Asked Questions
What is penetration testing and why is it important for businesses?
Penetration testing, or ethical hacking, involves simulating cyber attacks on systems, networks, or applications to identify vulnerabilities that could be exploited by malicious actors. It is essential for businesses to proactively uncover weaknesses, rectify security gaps, protect sensitive data, and maintain customer trust.
How do regular security assessments impact data breaches?
Entities that conduct routine security assessments are statistically less likely to experience data breaches. A study indicated that 72% of participants believe these assessments have directly prevented breaches at their companies.
What are the benefits of conducting security assessments?
Security assessments help achieve regulatory compliance, demonstrate due diligence to stakeholders, and enhance an organization’s market reputation. They also provide actionable insights for investment and strategic decisions, prioritizing risk evaluation and vulnerability ranking.
What is the median time to resolve issues found in security assessments?
The median time to resolve issues from security assessments is approximately 67 days, with serious findings having a resolution rate of 69%.
How can security assessments affect breach expenses for organizations?
Organizations that conduct regular security assessments can significantly lower their breach expenses, with proactive security measures saving an average of $1.9 million per incident.
What is the projected growth of the security assessment market?
The security assessment market is expected to grow from $1.92 billion in 2023 to $6.98 billion by 2032, reflecting the increasing recognition of its importance in the cybersecurity sector.
Why are vulnerability assessments crucial for organizations?
As cyber threats evolve, vulnerability assessments play a pivotal role in shaping defensive strategies for organizations, helping them effectively manage and mitigate risks.
List of Sources
- Understand the Importance of Penetration Testing for Business Security
- Why Penetration Testing is Important for Your Business in 2026 (https://brightdefense.com/resources/why-penetration-testing-is-important)
- Penetration Testing Requirement: What U.S. Rules Mandate It in 2026? (https://halock.com/penetration-testing-requirement-what-u-s-rules-mandate-it-in-2026)
- Penetration testing statistics, vulnerabilities and trends in 2026 – Cyphere (https://thecyphere.com/blog/penetration-testing-statistics)
- The 2026 State of Pentesting: How Modern Teams Manage and Deliver Results (https://thehackernews.com/expert-insights/2026/01/the-2026-state-of-pentesting-how-modern.html)
- 120+ Penetration Testing Statistics for 2026 (https://brightdefense.com/resources/penetration-testing-statistics)
- Explore the Benefits of Outsourcing Penetration Testing
- 7 Benefits of Outsourcing Cybersecurity Services | Huntress (https://huntress.com/blog/7-benefits-of-outsourcing-cybersecurity-services)
- The Economics of Outsourced IT: Cost Savings & Security – New Charter Technologies (https://newchartertech.com/outsourcing-it-for-cost-and-security-benefits)
- 8 Benefits of Outsourcing Cybersecurity – Auxis (https://auxis.com/learn/cybersecurity/benefits-of-outsourcing-cybersecurity)
- The Advantages of Outsourcing: Penetration Testing as a Service Explained (https://deepthreatanalytics.com/news/outsourcing-penetration-testing-as-a-service)
- 100+ essential penetration testing statistics [2023 edition] (https://pentest-tools.com/blog/penetration-testing-statistics)
- Examine the Risks of Neglecting Penetration Testing
- 83 Penetration Testing Statistics: Key Facts and Figures (https://getastra.com/blog/penetration-testing/statistics)
- Data Breach Statistics & Trends [updated 2025] (https://varonis.com/blog/data-breach-statistics)
- Adapt to Evolving Cybersecurity Threats Through Outsourcing
- Navigating the Cyber Threat Landscape: 2026 Outlook and Emerging Risks (https://panorays.com/blog/cyber-threat-landscape-2026-emerging-risks)
- Key Cyber Security Statistics for 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-statistics)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Cybersecurity Forecast 2026 (https://cloud.google.com/security/resources/cybersecurity-forecast)
- Annual Threat Dynamics 2026: Cyber threats in motion (https://pwc.com/gx/en/issues/cybersecurity/cyber-threat-intelligence/annual-threat-dynamics.html)