Introduction
Organizations must navigate the complexities of safeguarding digital assets against escalating cyber threats. Cyber incident response services should be viewed as proactive strategies that can significantly mitigate the impact of potential breaches. Many organizations encounter difficulties in implementing best practices that enhance their resilience and streamline response efforts. Identifying essential components is key to transforming a reactive approach into a robust defense against cyber threats.
Develop a Comprehensive Cybersecurity Incident Response Plan
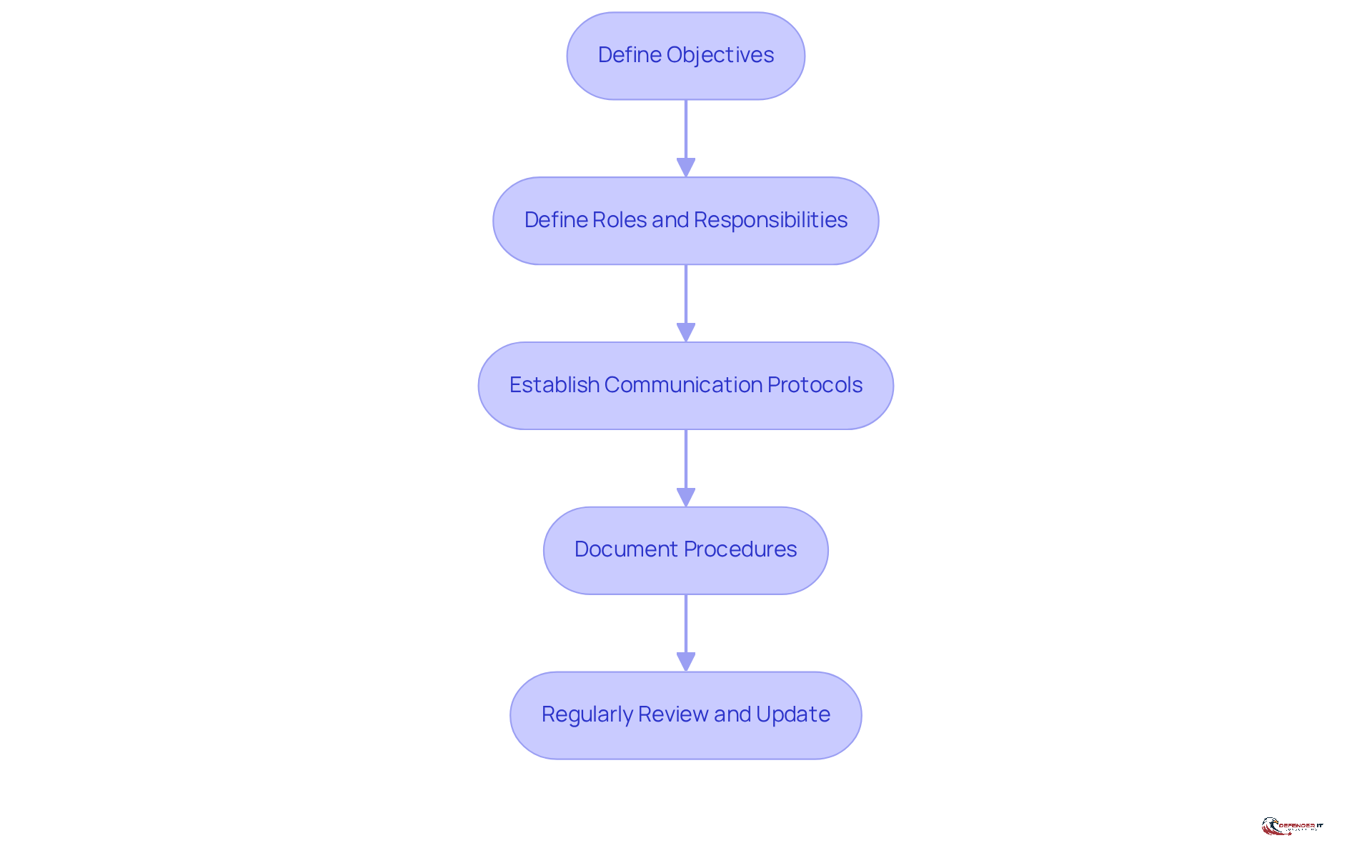
A well-structured cybersecurity crisis management plan (CIRP) is essential for organizations aiming to mitigate the impact of cyber incidents by utilizing cyber incident response services. Key components of an effective CIRP include:
- Define Objectives: Clearly outline the goals of the occurrence management plan, such as minimizing damage, ensuring business continuity, and protecting sensitive data. Organizations that establish clear goals are better prepared to react efficiently during events.
- Define Roles and Responsibilities: Allocate distinct roles to group members, including an emergency management coordinator, communication leader, and technical specialists. This clarity streamlines the response process and enhances coordination among team members.
- Establish Communication Protocols: Create clear guidelines for communication, both internally and externally, during an event. This includes timely alerts to stakeholders, law enforcement, and regulatory bodies. Notably, 60% of organizations lack a clear communication strategy during cyber events. Poor internal communication can lead to a 33% increase in the time it takes to contain a breach, highlighting just how crucial effective communication protocols are.
- Document Procedures: Create detailed procedures for each phase of response to events, including detection, containment, eradication, and recovery. Available documentation guarantees that all team members can adhere to established protocols, which is essential for efficient event management.
- Regularly Review and Update: The plan must remain a living document, regularly reviewed and updated to incorporate lessons learned from past events and shifts in the threat landscape. Organizations that implement changes based on past breaches lower future occurrence rates by 50%, highlighting the financial advantages of preparedness. Furthermore, entities that frequently evaluate their crisis management strategies save an average of $1.49 million for each breach, underscoring the necessity for ongoing enhancement.
By integrating these elements, companies can enhance their cyber incident response services to improve their preparedness to react to cyber events, thus minimizing potential effects on their operations and reputation. As the landscape of cyber threats evolves, organizations must prioritize the continuous improvement of their crisis management strategies to safeguard their operations and reputation.
Implement Key Steps in Cyber Incident Response
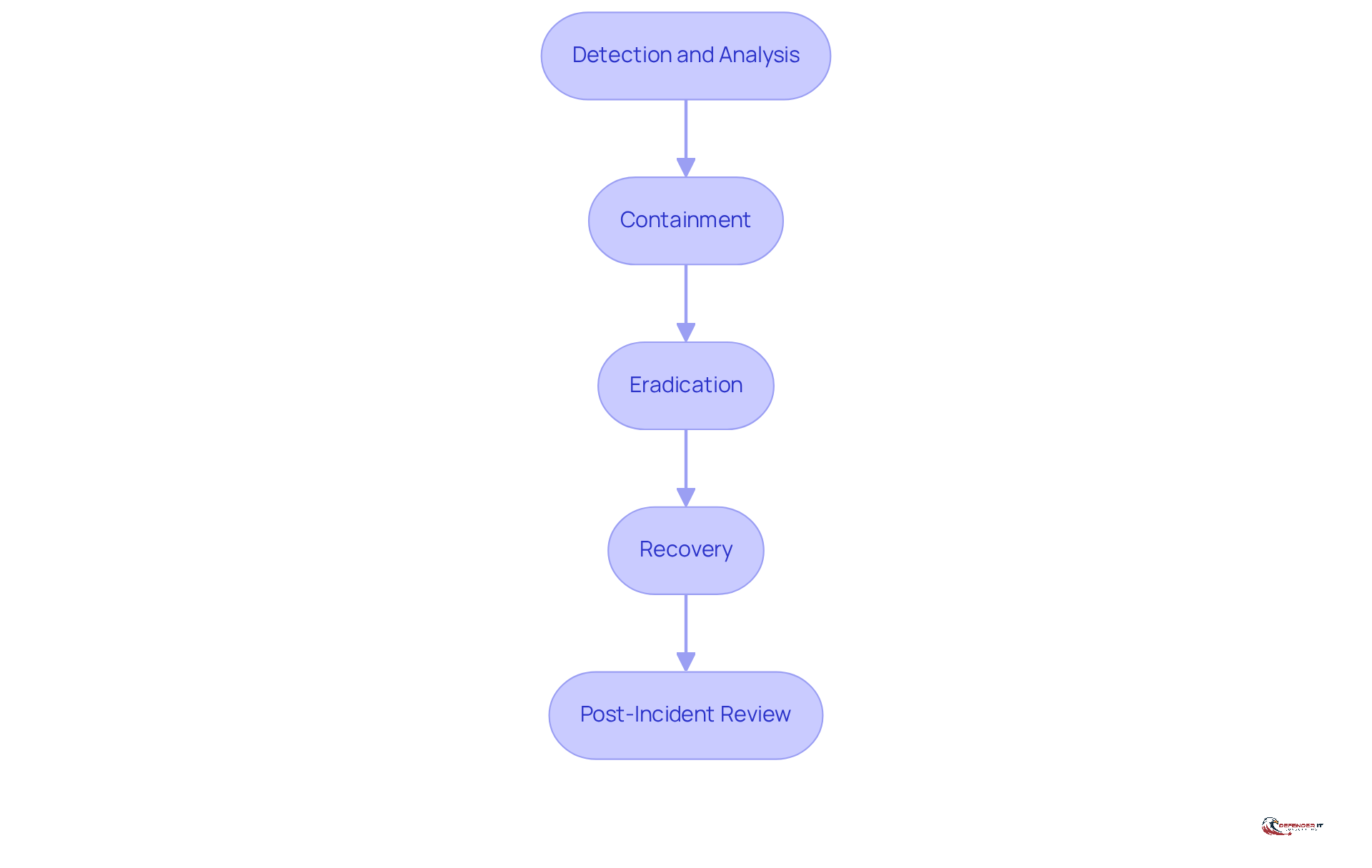
In an era where cyber threats are increasingly sophisticated, organizations must act decisively to mitigate risks and protect their assets. To effectively respond to a cyber incident, organizations should implement the following key steps:
- Detection and Analysis: Utilize monitoring tools to detect anomalies and potential threats. Examine the data to verify whether an event has taken place and evaluate its severity.
- Containment: Once an occurrence is confirmed, take immediate action to contain the threat. This involves isolating affected systems to prevent further damage.
- Eradication: Identify the root cause of the occurrence and eliminate the threat from the environment. This includes removing malware, closing vulnerabilities, and applying patches.
- Recovery: Restore affected systems to normal operations. This involves ensuring that systems are clean and secure before bringing them back online.
- Post-Incident Review: Conduct a thorough evaluation of the event to identify what went well and what could be enhanced. Record lessons learned and revise the occurrence management plan as needed.
By following these steps and utilizing cyber incident response services, organizations can effectively manage cyber events, reducing their impact and enhancing their overall security posture. Failure to implement these steps could result in significant vulnerabilities that jeopardize organizational integrity and trust.
Establish a Skilled Cybersecurity Incident Response Team
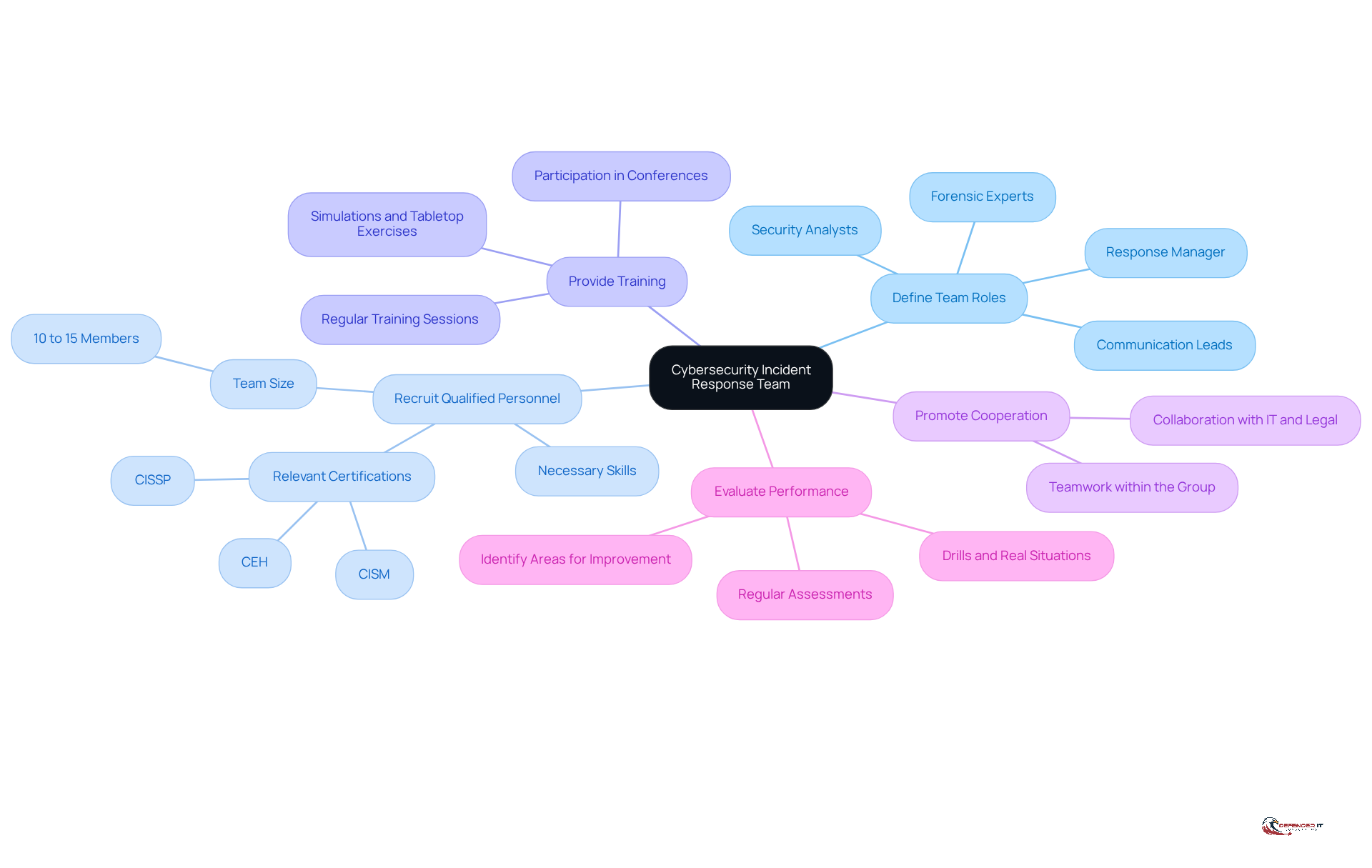
Establishing a proficient team for cyber incident response services is critical in today’s threat landscape. This involves several key considerations:
- Define Team Roles: Clearly outline the roles within the team, including response manager, security analysts, forensic experts, and communication leads. Each role should have defined responsibilities to ensure accountability and efficiency during events. Expert opinions emphasize that clearly defined roles enhance decision-making and operational efficiency during high-pressure situations.
- Recruit Qualified Personnel: Hire individuals with the necessary skills and experience in cybersecurity, crisis management, and relevant technologies. Look for certifications such as CISSP, CISM, or CEH. In 2026, the average cybersecurity response group consists of roughly 10 to 15 members, indicating the increasing complexity of cyber threats. With 76% of organizations facing at least one cyber attack in the past year, having a well-resourced group is crucial for effective incident management.
- Provide Training: Regular training helps the team stay current with the latest threats and tools. This can include simulations, tabletop exercises, and participation in cybersecurity conferences. Ongoing training is essential to ensure that the group is prepared for evolving cyber threats.
- Promote Cooperation: Encourage teamwork within the group and with other divisions, such as IT and legal, to guarantee a united approach during events. This cross-disciplinary teamwork is crucial for thorough and efficient crisis management.
- Evaluate Performance: Regularly assess the group’s performance through drills and actual situations. Use these evaluations to identify areas for improvement and provide additional training as needed. Moreover, entities should recognize that 90% of participants find it challenging to align important stakeholders during an attack, emphasizing a frequent downfall in crisis management.
Ultimately, the effectiveness of a crisis management group can significantly influence an organization’s resilience against cyber threats by leveraging cyber incident response services. This structured approach not only improves operational readiness but also aligns with the need for defined decision-making roles and regular rehearsals, as emphasized by industry experts.
Maintain Readiness Through Continuous Training and Testing
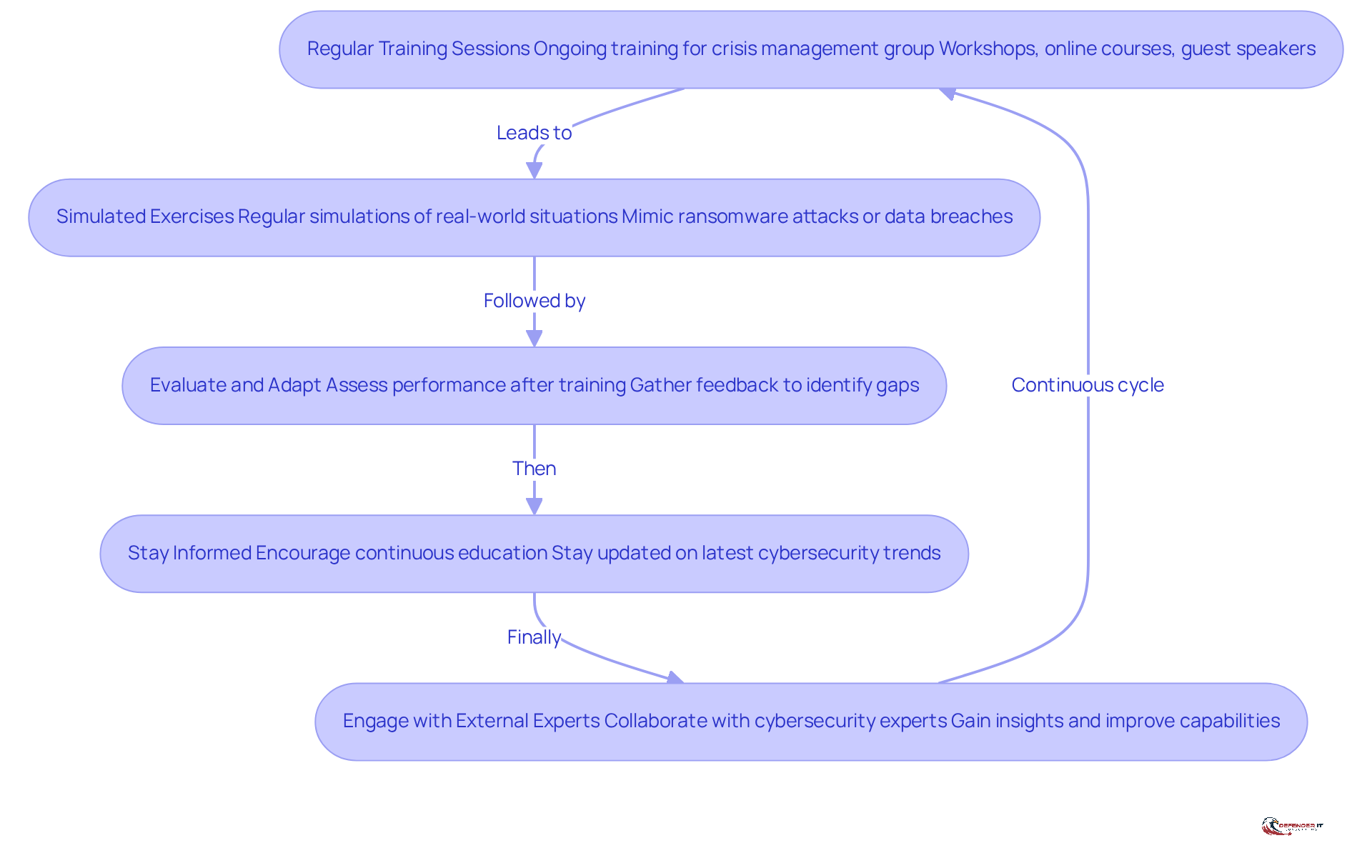
To effectively prepare for cyber incidents, organizations must implement continuous training and testing strategies that evolve with emerging threats:
- Regular Training Sessions: Conduct ongoing training for the crisis management group to keep them informed about emerging threats, tools, and best practices. This can include workshops, online courses, and guest speakers from the cybersecurity community, fostering a culture of learning.
- Simulated Exercises: Conduct regular simulations and tabletop activities that mimic real-world situations, such as ransomware attacks or data breaches. Research indicates that organizations engaging in these simulations can reduce employee-related security issues by up to 72% in the first year. This significantly boosts their preparedness and recovery capabilities.
- Evaluate and Adapt: After every training session or exercise, assess the group’s performance and the effectiveness of the incident management plan. Without regular feedback, organizations risk falling behind in their preparedness efforts. Gathering feedback is essential for identifying gaps and making necessary adjustments, ensuring that the response strategies remain relevant and effective.
- Stay Informed: Encourage group members to remain updated on the latest cybersecurity trends and threats through continuous education and professional development opportunities. This proactive method assists groups in anticipating and mitigating potential risks.
- Engage with External Experts: Collaborate with external cybersecurity experts to gain additional training and insights. Failing to collaborate with experts may leave organizations vulnerable to emerging threats. This partnership can offer new viewpoints and improve the group’s capabilities, ensuring they are well-equipped to manage evolving threats.
Investing in ongoing education and expert collaboration is essential for safeguarding your organization against evolving cyber threats, especially by utilizing cyber incident response services. As Chris Wilkes notes, “Whether you opt for a hands-on simulation or a discussion-based tabletop exercise, investing in regular preparedness exercises is essential for effectively mitigating cyber risks and ensuring your organization is ready to respond to potential security incidents.
Conclusion
Organizations face increasing challenges from sophisticated cyber threats, making a robust cyber incident response strategy indispensable. Developing a comprehensive cybersecurity incident response plan, defining clear roles, and establishing communication protocols are essential steps. These actions, combined with a culture of continuous improvement, significantly enhance resilience against cyber incidents.
Key practices discussed throughout this article include:
- The importance of regular training and simulations
- The establishment of a skilled response team
- The necessity of ongoing evaluation and adaptation of incident response strategies
Each of these elements plays a critical role in ensuring that organizations are equipped to detect, contain, and recover from cyber incidents effectively. Moreover, the financial benefits of a well-prepared response plan cannot be overlooked, as they can lead to substantial savings in the event of a breach.
Ultimately, organizations must recognize that the cyber threat landscape is ever-evolving. By committing to best practices in cyber incident response, fostering a culture of readiness, and engaging with external experts, businesses can position themselves to not only withstand but also thrive in the face of cyber challenges. Proactive measures today will not only fortify defenses but also ensure long-term sustainability in an unpredictable cyber landscape.
Frequently Asked Questions
What is a Cybersecurity Incident Response Plan (CIRP)?
A Cybersecurity Incident Response Plan (CIRP) is a structured plan that organizations use to mitigate the impact of cyber incidents by outlining clear objectives, roles, communication protocols, and procedures for response.
What are the key components of an effective CIRP?
Key components of an effective CIRP include defining objectives, defining roles and responsibilities, establishing communication protocols, documenting procedures, and regularly reviewing and updating the plan.
Why is it important to define objectives in a CIRP?
Defining objectives helps organizations clearly outline their goals during a cyber incident, such as minimizing damage, ensuring business continuity, and protecting sensitive data, which enhances their preparedness and response efficiency.
How should roles and responsibilities be structured in a CIRP?
Roles and responsibilities should be allocated to specific team members, including an emergency management coordinator, communication leader, and technical specialists, to streamline the response process and improve coordination.
What is the significance of establishing communication protocols in a CIRP?
Establishing communication protocols ensures timely alerts to stakeholders, law enforcement, and regulatory bodies during an event. Effective communication can significantly reduce the time it takes to contain a breach.
What procedures should be documented in a CIRP?
Detailed procedures should be documented for each phase of response, including detection, containment, eradication, and recovery, ensuring all team members can follow established protocols.
How often should a CIRP be reviewed and updated?
A CIRP should be regularly reviewed and updated to incorporate lessons learned from past incidents and changes in the threat landscape, ensuring it remains effective and relevant.
What are the financial benefits of regularly updating a CIRP?
Organizations that implement changes based on past breaches can lower future occurrence rates by 50% and save an average of $1.49 million for each breach by frequently evaluating their crisis management strategies.
How can organizations improve their preparedness for cyber events?
By integrating the key components of a CIRP and prioritizing continuous improvement of their crisis management strategies, organizations can enhance their preparedness and minimize the potential impact of cyber events on their operations and reputation.
List of Sources
- Develop a Comprehensive Cybersecurity Incident Response Plan
- The Critical Importance of a Robust Incident Response Plan in 2025 | Sygnia (https://sygnia.co/blog/critical-importance-incident-response-plan)
- Incident Response Statistics to Know in 2025 (https://jumpcloud.com/blog/incident-response-statistics)
- Implement Key Steps in Cyber Incident Response
- Average Time to Detect Cyber Attack in 2026: Latest Statistics (https://cybersecuritytime.com/average-time-to-detect-cyber-attack)
- Cyberattack Report 2026: Statistics Every Security Team Needs to See (https://zerothreat.ai/blog/cyberattack-statistics)
- Cyber Incident Response Playbook Examples for 2026 (https://cm-alliance.com/cybersecurity-blog/cyber-incident-response-playbook-examples-for-2026)
- 2026 Global Threat Report | Latest Cybersecurity Trends & Insights | CrowdStrike (https://crowdstrike.com/en-us/global-threat-report)
- Incident Response in 2026: A Complete Enterprise Guide (https://uscsinstitute.org/cybersecurity-insights/resources/incident-response-in-2026-a-complete-enterprise-guide)
- Establish a Skilled Cybersecurity Incident Response Team
- SANS 2026 report flags cybersecurity skills crisis, putting critical infrastructure and OT sectors at measurable breach risk – Industrial Cyber (https://industrialcyber.co/reports/sans-2026-report-flags-cybersecurity-skills-crisis-putting-critical-infrastructure-and-ot-sectors-at-measurable-breach-risk)
- 73% of CISOs Unprepared for the Next Big Cyber Attack, Incident Response Readiness Report Reveals (https://finance.yahoo.com/sectors/technology/articles/73-cisos-unprepared-next-big-120000695.html)
- Incident Response in 2026: A Complete Enterprise Guide (https://uscsinstitute.org/cybersecurity-insights/resources/incident-response-in-2026-a-complete-enterprise-guide)
- Incident Response Team Depth Chart: Roles & Responsibilities | Wiz (https://wiz.io/academy/detection-and-response/incident-response-team)
- Maintain Readiness Through Continuous Training and Testing
- Managing Cyber Risk in 2026 With Incident Response Training and Drills (https://cm-alliance.com/cybersecurity-blog/managing-cyber-risk-in-2026-with-incident-response-training-and-drills)
- Security Awareness Training Statistics 2025 [100+ Studies] | Brightside AI Blog (https://brside.com/blog/security-awareness-training-statistics-2025-100-studies)
- US Coast Guard mandates cybersecurity training for personnel with IT, OT access by January 2026 – Industrial Cyber (https://industrialcyber.co/training-development/ics-cyber-security-training/us-coast-guard-mandates-cybersecurity-training-for-personnel-with-it-ot-access-by-january-2026)
- [Updated 2026] Security Awareness Training Statistics – Keepnet (https://keepnetlabs.com/blog/security-awareness-training-statistics)
- Incident Response Simulations vs Exercise: Which Strengthens Your Defense? (https://sans.org/blog/enhancing-your-cyber-defense-comparing-simulations-and-tabletop-exercises)