Introduction
Choosing the right web application penetration testing service is a critical decision for organizations seeking to strengthen their cybersecurity defenses. As cyber threats become increasingly sophisticated, understanding the essential criteria for selecting a provider is paramount. Key factors differentiate a competent testing service from one that may leave vulnerabilities unaddressed. This article explores best practices for evaluating penetration testing services, ensuring that organizations make informed choices that align with their security needs.
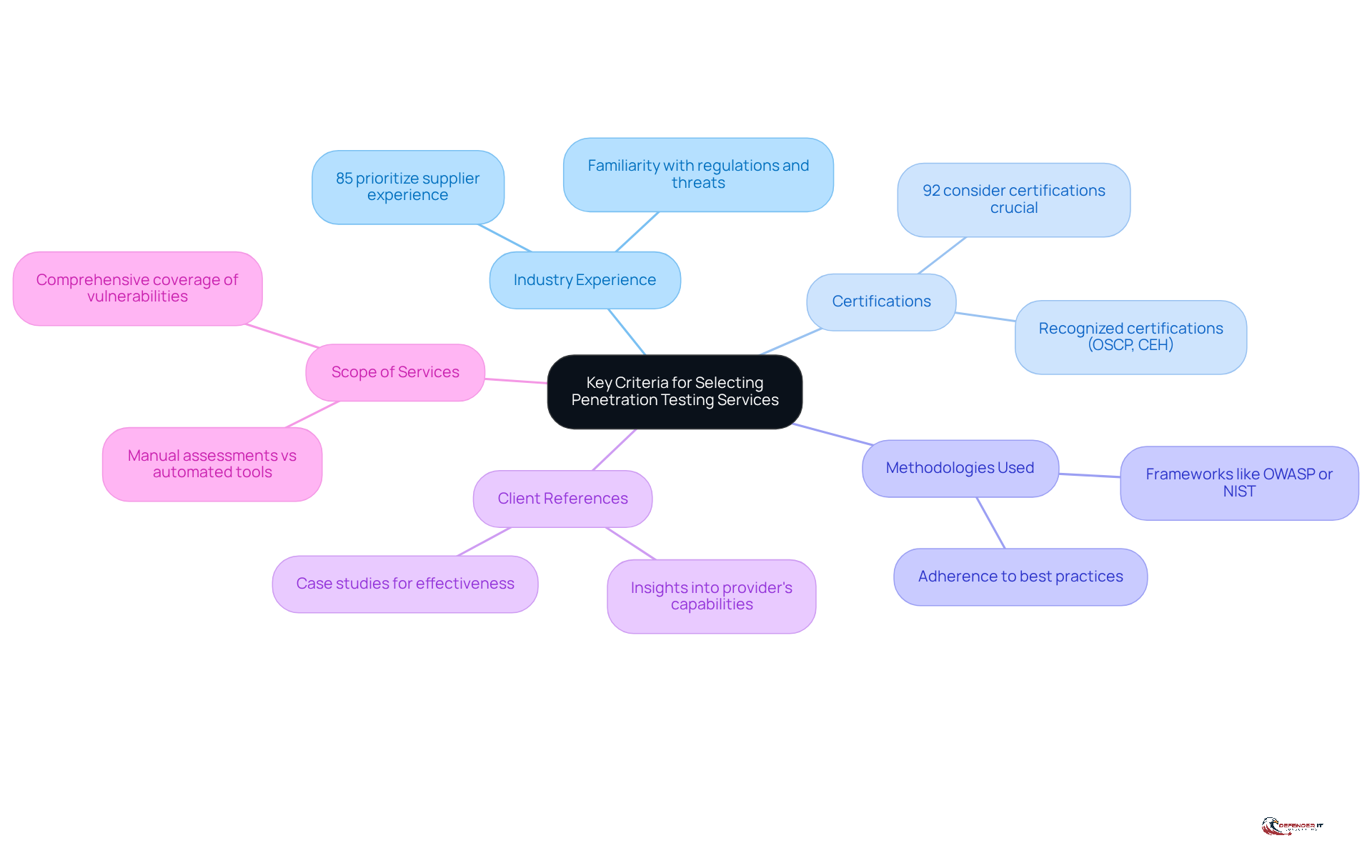
Identify Key Criteria for Selecting Penetration Testing Services
When selecting a web application penetration testing service, organizations should effectively prioritize several key criteria to enhance their security.
- Industry Experience: It is essential to choose suppliers with a proven track record. Their familiarity with applicable regulations and threats can significantly improve the efficiency of the evaluation process. A recent survey indicates that 85% of entities prioritize industry experience.
- Certifications: Ensure that the evaluation team possesses relevant certifications. These credentials validate their expertise and commitment to maintaining high standards in cybersecurity. Research shows that 92% of organizations consider supplier certifications crucial when selecting a service provider.
- Methodologies Used: Inquire about the testing methodologies used. Adherence to established best practices is vital for conducting thorough assessments of vulnerabilities.
- Client References: Request to evaluate the provider’s effectiveness and reliability. Successful engagements can offer insights into the provider’s capabilities and approach. For example, a case study from a leading manufacturer demonstrated that selecting a vendor with a strong industry background resulted in a 40% reduction in security incidents.
- Scope of Services: Understand the scope of services, distinguishing between manual assessments and automated tools. Comprehensive coverage of potential vulnerabilities is crucial for a robust security posture. Be wary of vendors offering low-cost solutions, as they may lack the thoroughness required.
By focusing on these criteria, organizations can make informed decisions that significantly enhance their security posture, ultimately leading to a more secure operational environment.
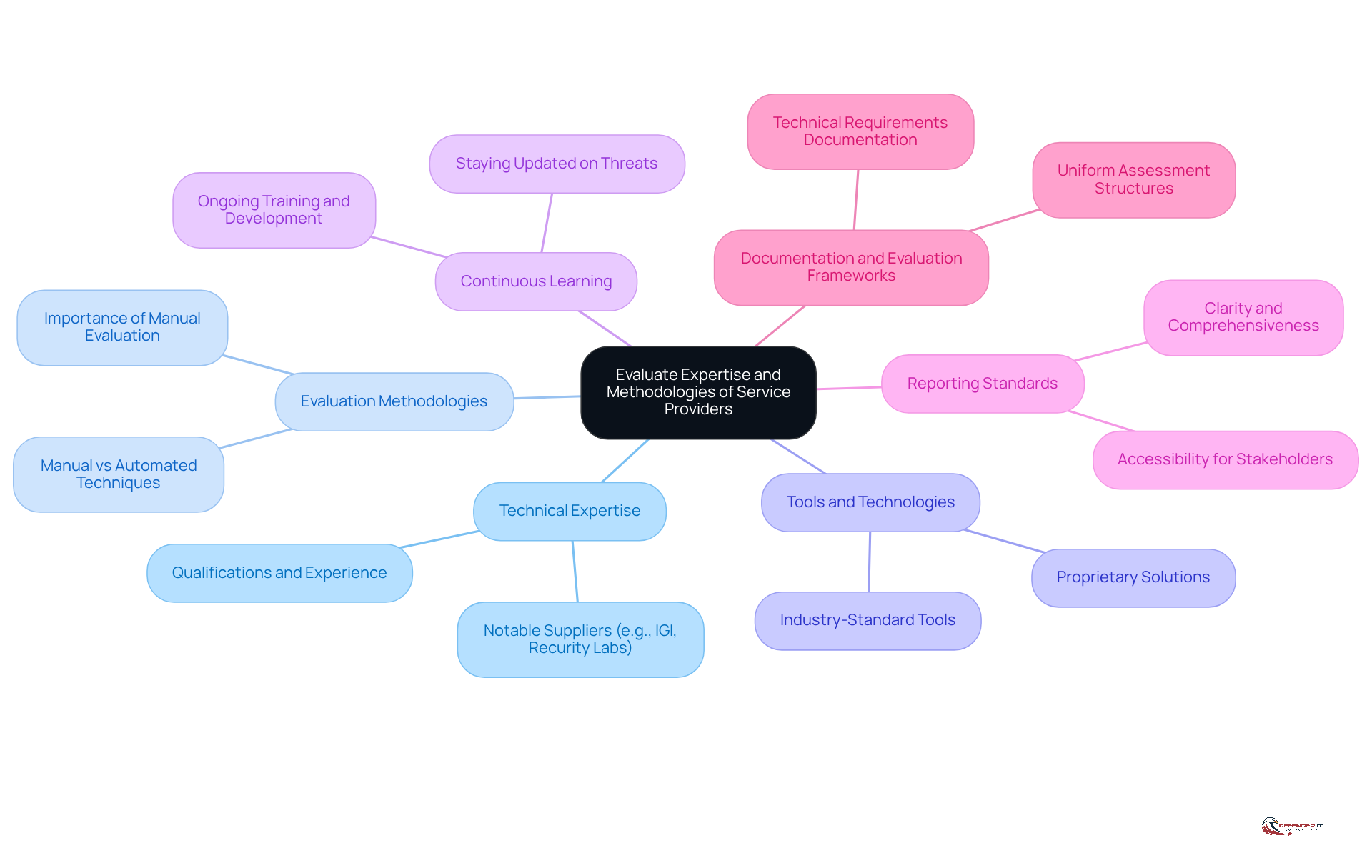
Evaluate Expertise and Methodologies of Service Providers
To effectively evaluate potential providers, consider the following key factors:
- Technical Expertise: Assess the qualifications and experience of the testing team. Look for professionals with extensive hands-on experience in a web application environment, as their expertise is crucial for identifying vulnerabilities that could compromise your systems. Notable suppliers like IGI and Recurity Labs exemplify the level of expertise to seek in this area.
- Methodologies: Ensure the vendor employs a balanced approach that combines both manual and automated assessment techniques. This approach is especially crucial for revealing intricate vulnerabilities that automated tools might miss, thereby improving the overall assessment of safety. This aligns with current trends emphasizing the importance of thorough testing in the web application for web application security.
- Tools: Inquire about the tools used for evaluation. Reputable providers will leverage industry-standard tools and may also offer proprietary solutions that enhance the depth and effectiveness of their evaluation processes.
- Continuous Learning: Check if the supplier prioritizes training for their team. Staying informed about the latest threats and vulnerabilities is crucial in the swiftly changing cybersecurity environment, ensuring that the evaluation team is prepared to tackle emerging challenges.
- Reporting: Assess the clarity and comprehensiveness of the supplier’s reporting. A competent provider should deliver detailed reports that are accessible and understandable to both technical and non-technical stakeholders, facilitating informed decision-making.
- Documentation and Evaluation Frameworks: Before interacting with suppliers, document your requirements, testing timelines, and budget parameters. Creating uniform assessment structures throughout supplier conversations is crucial for equitable evaluations and choosing a provider that aligns with your wider protection strategy.
By thoroughly assessing these aspects, companies can choose a vendor that not only meets their needs but also aligns with their broader security strategy, ultimately enhancing their security posture.
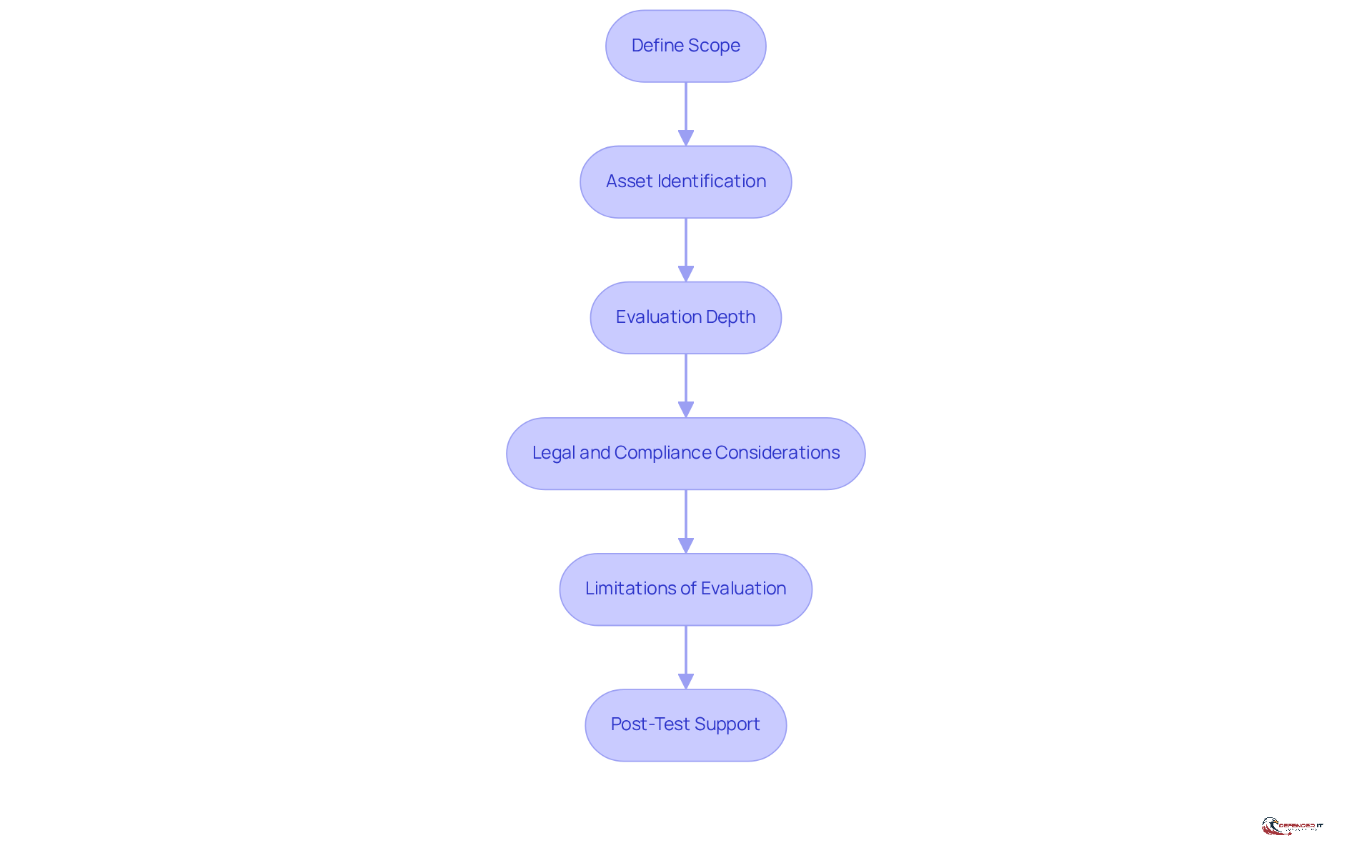
Understand the Scope and Limitations of Testing Services
Before engaging a web application penetration testing service, organizations must clearly define the scope of the assessment. This foundational step ensures that critical assets are not overlooked, ultimately enhancing the overall security posture.
- Scope Definition: Organizations should clearly identify which applications, systems, and networks will be included in the evaluation. Effective scope definition significantly contributes to thorough coverage during the assessment. It is essential to document all pertinent assets, including web applications, databases, and network components.
- Testing Depth: Organizations must determine the depth of examination required. Will it be a black-box test, where the tester has no prior knowledge of the system, or a white-box test, where full knowledge is provided? Each method presents its advantages and drawbacks; black-box evaluation simulates real-world attacks, while white-box analysis allows for a more comprehensive examination of the system’s vulnerabilities. Current trends indicate a growing preference for a hybrid approach, combining elements of both methodologies to maximize effectiveness.
- Compliance Requirements: It is crucial to ensure that the evaluation scope complies with relevant regulations to the industry. This is particularly important in sectors like finance and healthcare, where regulations such as the GLBA and HIPAA mandate specific evaluation protocols. For instance, HIPAA emphasizes the necessity for regular penetration assessments to satisfy compliance standards. Organizations must remain aware of these requirements to avoid potential legal repercussions and ensure that their security measures meet industry standards.
- Limitations of Evaluation: Understanding the limitations of the evaluation service is vital. Some vendors may not test certain components due to legal restrictions or operational concerns, potentially leaving critical vulnerabilities unaddressed. Open discussions with the evaluation provider about any limitations that may impact the assessment process are essential.
- Post-Assessment Support: Organizations should discuss the assistance available after the assessment is completed, including remediation guidance and retesting options. Effective post-assessment support is crucial for addressing identified vulnerabilities and ensuring that necessary changes can be implemented to improve safety.
By establishing a clear scope and understanding limitations, entities can maximize the effectiveness of their web application penetration testing, ultimately leading to a more secure operational environment.
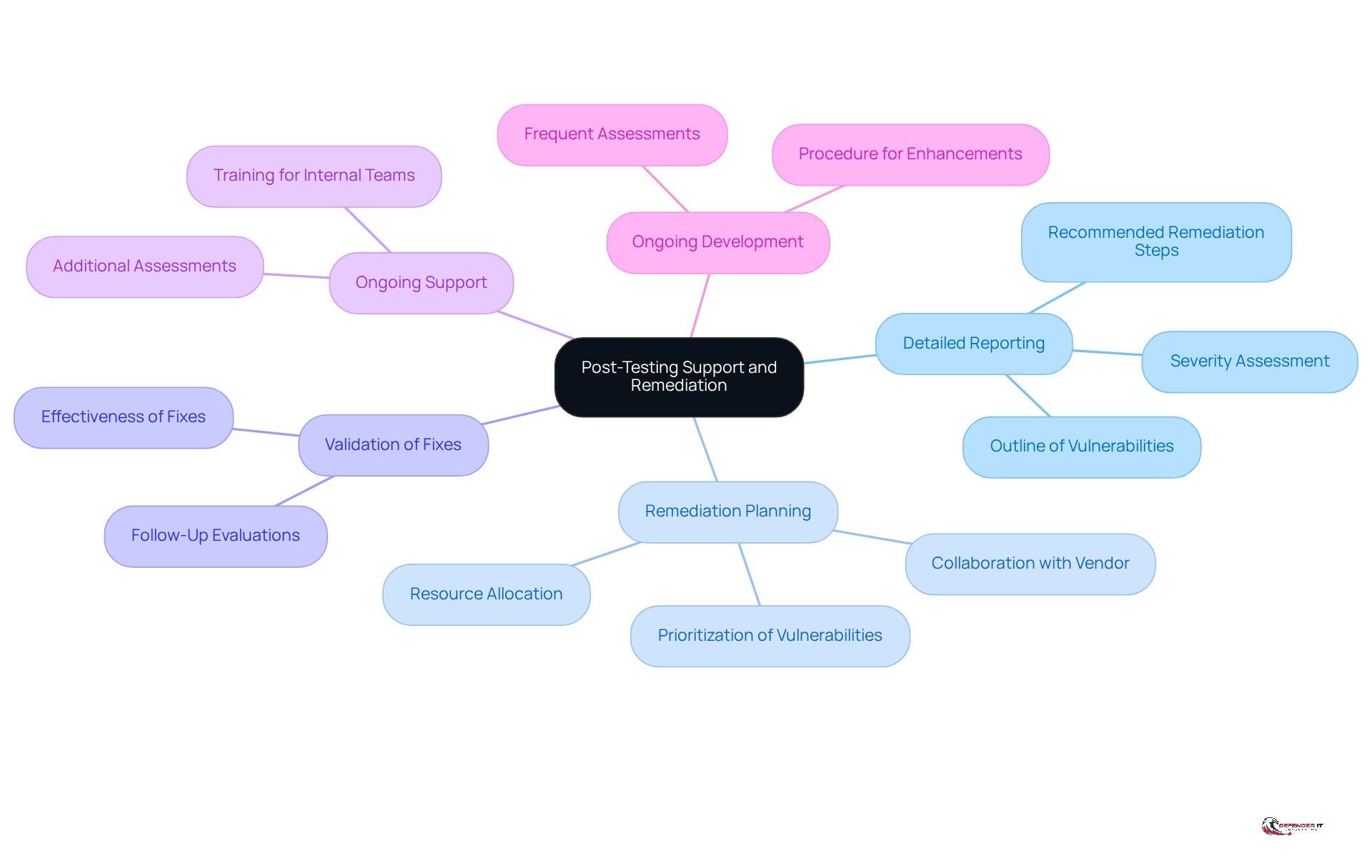
Seek Comprehensive Post-Testing Support and Remediation
Following a penetration test, organizations must focus on several key areas to ensure effective remediation and enhance their security posture:
- Comprehensive Report: A thorough report from the supplier is essential, outlining identified vulnerabilities, their severity, and recommended remediation steps. This clarity is vital for prioritizing actions.
- Remediation Plan: Collaborating with the vendor to create a remediation plan that prioritizes vulnerabilities based on their risk and potential impact on the organization is crucial. This strategic approach helps allocate resources effectively.
- Verification Process: Arranging to confirm that identified vulnerabilities have been adequately addressed is necessary. This step ensures that fixes are not only implemented but are effective in mitigating risks.
- Training Options: Inquiring about options, such as training for internal teams or additional assessments, is important. This assistance is essential for sustaining a strong protective stance over time, particularly as new threats arise.
- Continuous Improvement: Establishing a procedure for ongoing enhancement based on evaluation outcomes is vital. Frequent assessments of security policies and practices can aid organizations in adjusting to changing threats and improving their overall security framework.
By concentrating on these areas, organizations can transform their remediation efforts into significant enhancements in their cybersecurity defenses.
Conclusion
Choosing the right web application penetration testing service is crucial for strengthening an organization’s cybersecurity posture. By focusing on key criteria such as industry experience, certifications, methodologies, and post-testing support, organizations can select a provider adept at identifying and mitigating vulnerabilities. This strategic choice not only enhances security but also aligns with the organization’s overarching protection objectives.
The article emphasizes the necessity of evaluating potential vendors based on their technical expertise, the methodologies they utilize, and the comprehensiveness of their offerings. A clear understanding of the testing scope and the limitations of the selected service is essential for maximizing the assessment’s effectiveness. Additionally, the importance of detailed reporting and ongoing remediation support highlights the need for a proactive cybersecurity strategy.
Ultimately, dedicating time and resources to select the appropriate penetration testing service is vital. Organizations must acknowledge that a thorough evaluation process not only protects their assets but also cultivates a culture of continuous improvement in cybersecurity practices. By adhering to these best practices, companies can significantly enhance their defenses against evolving threats, ensuring a secure operational environment for the future.
Frequently Asked Questions
What key criteria should organizations consider when selecting penetration testing services?
Organizations should prioritize industry experience, certifications, methodologies used, client references, and the scope of services offered.
Why is industry experience important in selecting a penetration testing service?
Choosing suppliers with a proven track record in your specific industry enhances the evaluation process, as they are familiar with relevant regulations and threats. A survey shows that 85% of entities prioritize supplier experience.
What certifications should the evaluation team possess?
The evaluation team should have recognized certifications such as OSCP (Offensive Security Certified Professional) or CEH (Certified Ethical Hacker), which validate their expertise and commitment to high standards in cybersecurity. Research indicates that 92% of organizations consider these certifications crucial.
What methodologies should be inquired about when selecting a service provider?
Organizations should ask about the methodologies employed by the supplier, including established frameworks like OWASP (Open Web Application Security Project) or NIST (National Institute of Standards and Technology), to ensure adherence to best practices in vulnerability assessments.
How can client references help in the selection process?
Requesting case studies or references from previous clients allows organizations to evaluate a provider’s effectiveness and reliability. Successful engagements can provide insights into the provider’s capabilities, such as a case study showing a 40% reduction in vulnerabilities.
What should organizations understand about the scope of services offered?
Organizations should clarify what services are included in the evaluation, distinguishing between manual assessments and automated tools. Comprehensive coverage of potential vulnerabilities is essential, and low-cost solutions may lack thoroughness.
How can focusing on these criteria enhance cybersecurity defenses?
By concentrating on these key criteria, organizations can make informed decisions that significantly improve their cybersecurity defenses, leading to a more secure operational environment.
List of Sources
- Identify Key Criteria for Selecting Penetration Testing Services
- Pentesting Statistics 2026: Key Insights and Emerging Trends (https://zerothreat.ai/blog/emerging-penetration-testing-statistics)
- Penetration Testing Market Size, Share & Growth Forecast 2030 (https://marketsandmarkets.com/Market-Reports/penetration-testing-market-13422019.html)
- 5 Things to Look for in a Penetration Testing Company in 2026 – Netragard (https://netragard.com/blog/5-things-look-for-penetration-testing-company)
- Global Penetration Testing Market To Exceed $5 Billion USD Annually By 2031 (https://cybersecurityventures.com/penetration-testing-statistics-2024)
- 83 Penetration Testing Statistics: Key Facts and Figures (https://getastra.com/blog/security-audit/penetration-testing-statistics)
- Evaluate Expertise and Methodologies of Service Providers
- 83 Penetration Testing Statistics: Key Facts and Figures (https://getastra.com/blog/security-audit/penetration-testing-statistics)
- The 2026 State of Pentesting: How Modern Teams Manage and Deliver Results (https://thehackernews.com/expert-insights/2026/01/the-2026-state-of-pentesting-how-modern.html)
- Penetration Testing Companies To Consider In 2026 (https://blazeinfosec.com/post/penetration-testing-companies)
- Financial Industry / Penetration Testing Case Study | IGI Cybersecurity (https://igicybersecurity.com/case-studies/financial-owasp-penetration-testing)
- Essential Considerations When Selecting a Penetration Testing Partner | Schellman (https://schellman.com/blog/penetration-testing/essential-considerations-when-selecting-a-penetration-testing-partner)
- Understand the Scope and Limitations of Testing Services
- Penetration Testing Requirement: What U.S. Rules Mandate It in 2026? (https://halock.com/penetration-testing-requirement-what-u-s-rules-mandate-it-in-2026)
- 83 Penetration Testing Statistics: Key Facts and Figures (https://getastra.com/blog/security-audit/penetration-testing-statistics)
- Penetration testing statistics, vulnerabilities and trends in 2026 – Cyphere (https://thecyphere.com/blog/penetration-testing-statistics)
- The Complete Guide to Compliance Driven Pentesting in 2026 – Graynode Security (https://graynodesecurity.com/the-complete-guide-to-compliance-driven-pentesting-in-2026)
- vaadata.com (https://vaadata.com/blog/pentest-statistics-and-most-frequent-vulnerabilities)
- Seek Comprehensive Post-Testing Support and Remediation
- 83 Penetration Testing Statistics: Key Facts and Figures (https://getastra.com/blog/security-audit/penetration-testing-statistics)
- The 2026 State of Pentesting: How Modern Teams Manage and Deliver Results (https://thehackernews.com/expert-insights/2026/01/the-2026-state-of-pentesting-how-modern.html)
- vikingcloud.com (https://vikingcloud.com/blog/penetration-testing-examples)
- 86 Penetration Testing Statistics: Key Facts and Figures (https://deepstrike.io/blog/penetration-testing-statistics-2025)