Introduction
As cyber threats evolve and escalate, understanding the vulnerabilities within digital infrastructures is crucial for organizations. A free cybersecurity assessment provides an opportunity to:
- Pinpoint weaknesses
- Enhance compliance
- Build a robust incident response strategy – all essential for maintaining trust and safeguarding reputations.
Organizations must not only identify risks but also take decisive action to enhance their security posture and protect their reputations.
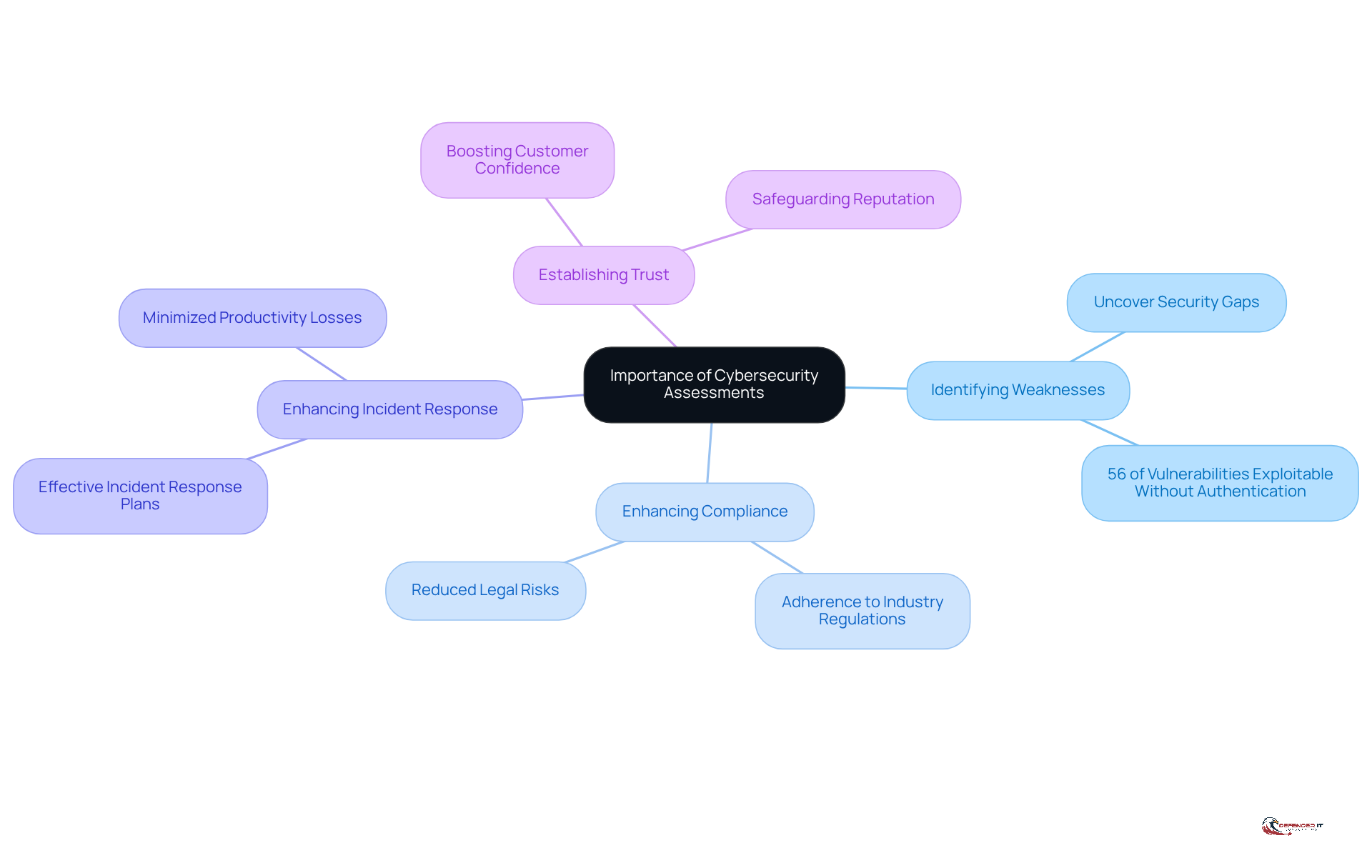
Understand the Importance of Cybersecurity Assessments
Cybersecurity evaluations are not just beneficial; they are critical for identifying vulnerabilities and fortifying a company’s defenses against cyber threats. They provide numerous benefits, including:
- Identifying Weaknesses: Assessments uncover security gaps that cybercriminals could exploit, enabling organizations to address these vulnerabilities proactively.
- Enhancing Compliance: Regular evaluations help ensure adherence to industry regulations and standards, significantly reducing legal risks associated with non-compliance. In reality, entities that carry out regular evaluations indicate enhanced compliance rates, which is essential in regulated industries.
- Enhancing Incident Response: By understanding potential threats, entities can create more effective incident response plans. A complete and tested incident response strategy can significantly minimize productivity losses and reputational damage during cyber events.
- Establishing Trust: Showing dedication to digital security through regular evaluations boosts customer confidence and safeguards the organization’s reputation. This is increasingly important as consumers become more aware of cybersecurity risks.
Statistics reveal a concerning trend: 56% of nearly 40,000 monitored vulnerabilities can be exploited without any authentication, underscoring the critical need for regular evaluations. Moreover, organizations like West Pharmaceutical and DaVita illustrate how proactive evaluations can significantly bolster security posture, enabling them to recover more effectively from incidents. For example, DaVita’s execution of a proven incident response strategy enabled them to reduce the effects of a ransomware attack, showcasing the value of routine evaluations in strengthening resilience.
In 2026, the environment of digital security evaluations is changing, emphasizing ongoing, AI-driven risk intelligence that offers real-time insights across identities, data, and third parties. This change underscores the need for organizations to adapt their strategies to effectively counter emerging threats and maintain robust security measures. As David Jones observes, “New year, new and more complex challenges for security leaders, beginning on the technology front: AI tools are transforming methods of working for security operations teams while regrettably also enabling cyber threat actors to enhance their attacks.” Organizations that neglect to evolve their cybersecurity strategies may face dire consequences in an increasingly complex threat landscape.
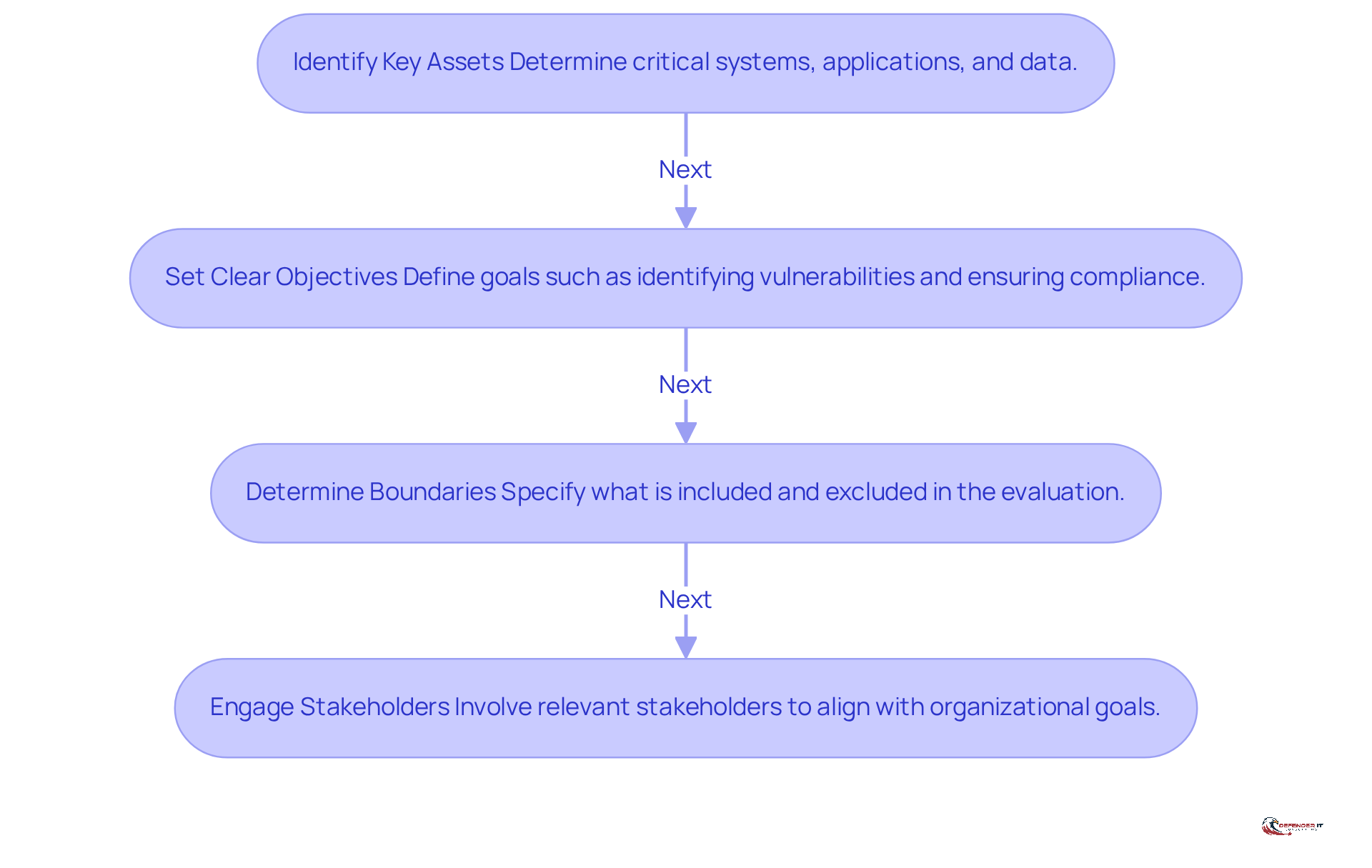
Define the Scope and Objectives of Your Assessment
To conduct a comprehensive cybersecurity evaluation, it is crucial to establish a well-defined scope and clear objectives. Follow these steps:
- Identify Key Assets: Determine which systems, applications, and data are critical to your organization’s operations. Recognizing the potential impact of a breach on critical assets is often underestimated, especially since 90% of cyber incidents stem from human error, highlighting the necessity for comprehensive stakeholder engagement and training.
- Set Clear Objectives: Define what you want to achieve with the evaluation, such as identifying vulnerabilities, ensuring compliance, or improving incident response. Organizations should prioritize evaluations based on the potential impact of identified risks to enhance their effectiveness.
- Determine Boundaries: Specify what will be included in the evaluation (e.g., specific departments, locations, or technologies) and what will be excluded to avoid scope creep.
- Engage Stakeholders: Involve relevant stakeholders early in the process to ensure that the evaluation aligns with organizational goals and addresses their concerns. Engaging stakeholders fosters ownership and enhances the evaluation’s effectiveness. Cyber Solutions emphasizes the importance of regular evaluations to identify vulnerabilities and maintain robust protection against evolving cyber threats.
By defining a clear scope and objectives, you can concentrate your efforts on the most vital areas, ensuring a more efficient evaluation process. This focused approach not only enhances the evaluation process but also significantly mitigates potential risks.
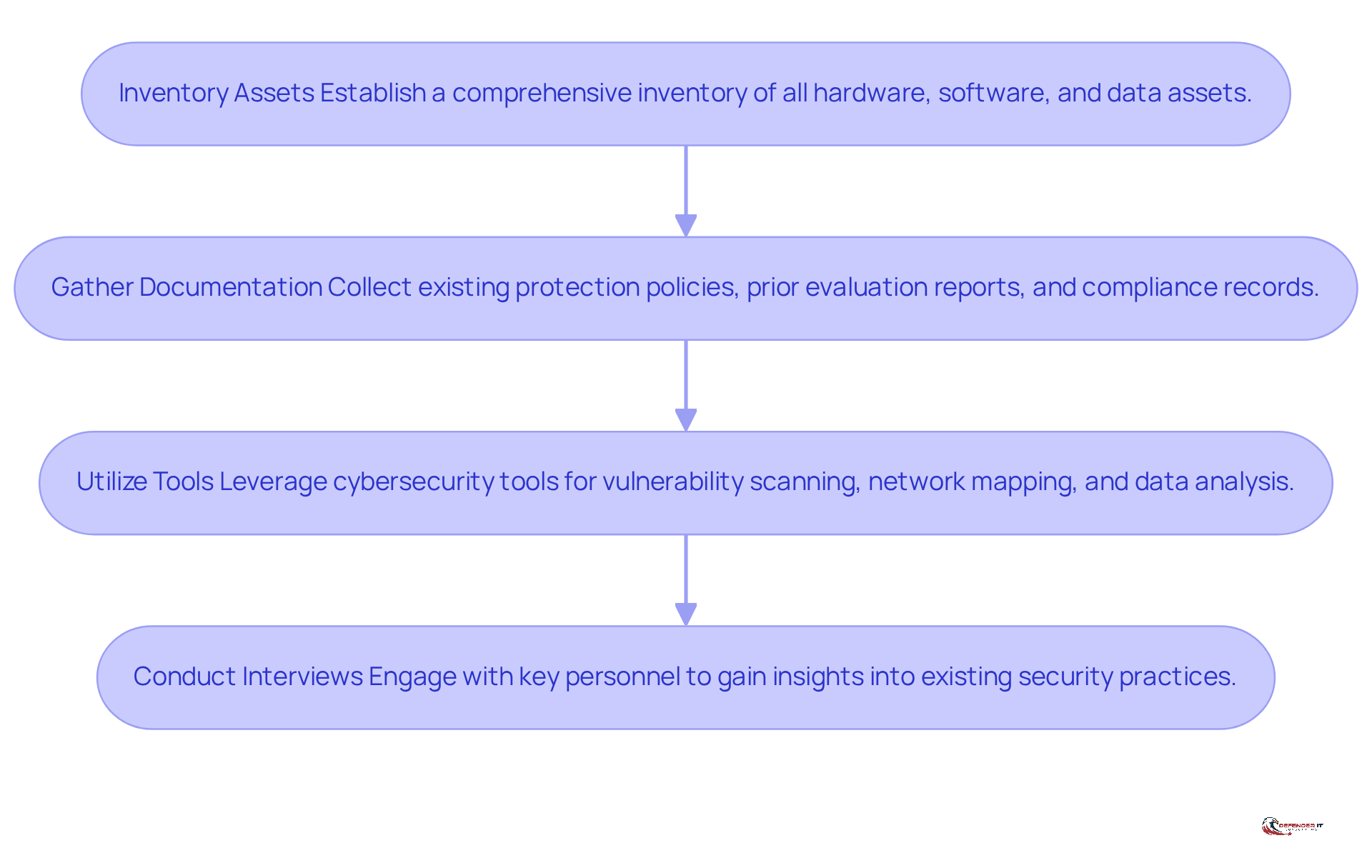
Collect Necessary Data and Resources for the Assessment
A successful security evaluation hinges on the meticulous collection of relevant information and resources. Here’s how to do it:
- Inventory Assets: Establish a comprehensive inventory of all hardware, software, and data assets within the entity. This inventory is crucial for effective cybersecurity evaluations, as it allows organizations to prioritize vulnerabilities and allocate resources efficiently. In 2026, maintaining an accurate asset inventory is crucial. Enterprises now manage over 165,000 cyber assets on average, which complicates visibility and management.
- Gather Documentation: Collect existing protection policies, prior evaluation reports, and compliance records. Without thorough documentation, identifying security gaps becomes a challenging task. Frequent evaluations of security risks are crucial for maintaining compliance with regulations such as GDPR and HIPAA, which can result in substantial penalties if not followed.
- Utilize Tools: Leverage cybersecurity tools and software for vulnerability scanning, network mapping, and data analysis. These tools can automate the identification of vulnerabilities and misconfigurations, significantly enhancing the efficiency of the assessment process. For example, entities that utilize automated asset tracking can swiftly identify non-compliant assets and obsolete software, enhancing the overall safety stance.
- Conduct Interviews: Engage with key personnel to gain insights into existing security practices and potential areas of concern. This qualitative data complements the quantitative findings from tools and documentation, providing a holistic view of the entity’s cybersecurity landscape.
This foundational knowledge is crucial for effectively addressing vulnerabilities and fortifying your entity against emerging cyber threats.
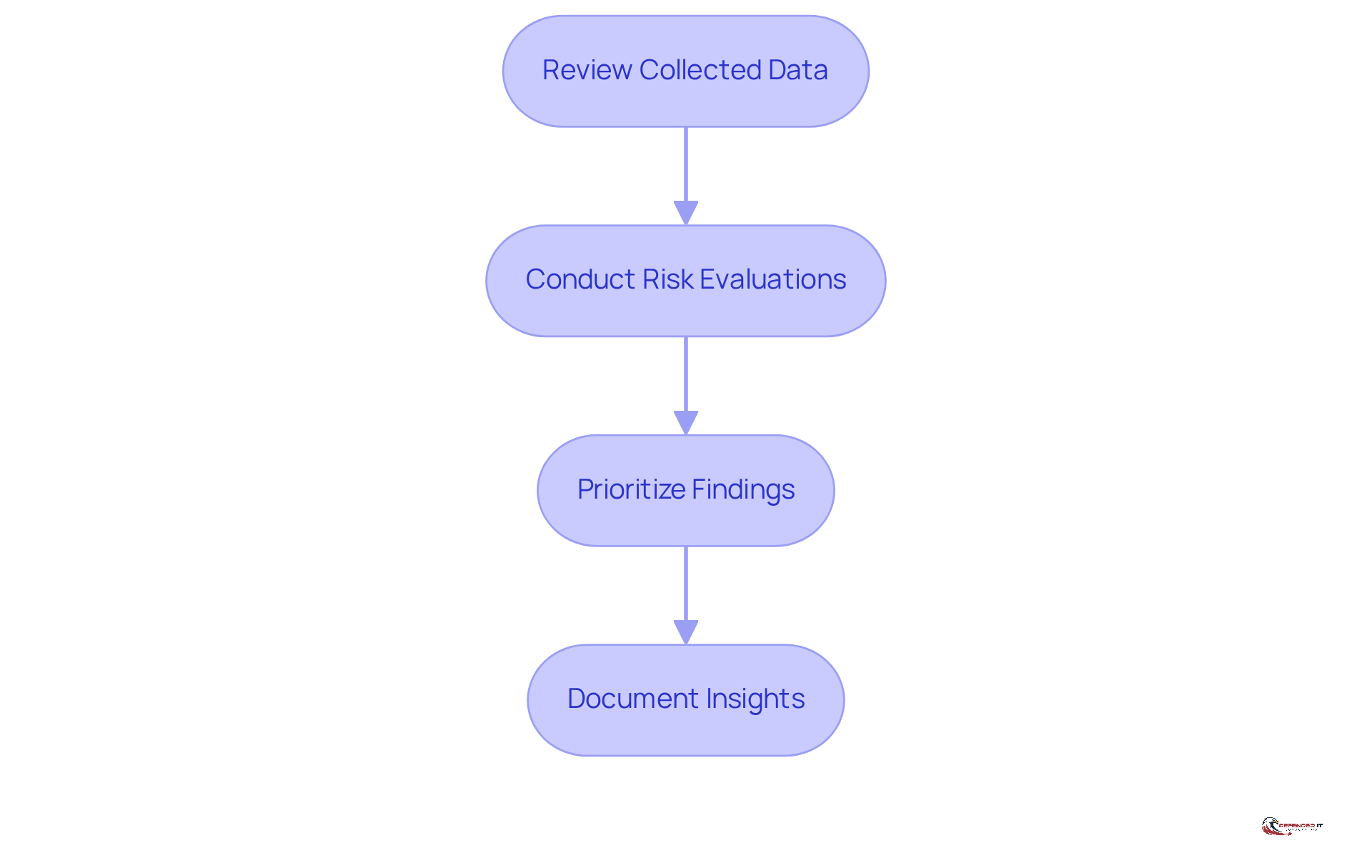
Analyze Data to Identify Vulnerabilities and Risks
Analyzing collected data is essential for identifying vulnerabilities and risks that could jeopardize cybersecurity. Follow these key steps:
- Review Collected Data: Examine the data gathered from asset inventories, documentation, and tools to identify patterns and anomalies.
- Conduct Risk Evaluations: Utilize risk evaluation frameworks (e.g., NIST, ISO 27001) to assess the likelihood and impact of identified vulnerabilities.
- Prioritize Findings: Rank vulnerabilities based on their severity and potential impact on the entity, focusing on those that pose the greatest risk.
- Document Insights: Maintain comprehensive records of your analysis process and findings to guide future evaluations and remediation efforts.
This analytical phase is crucial for understanding where your entity stands in terms of cybersecurity. Without a thorough analysis, entities may overlook critical vulnerabilities, leading to potentially severe cybersecurity threats.
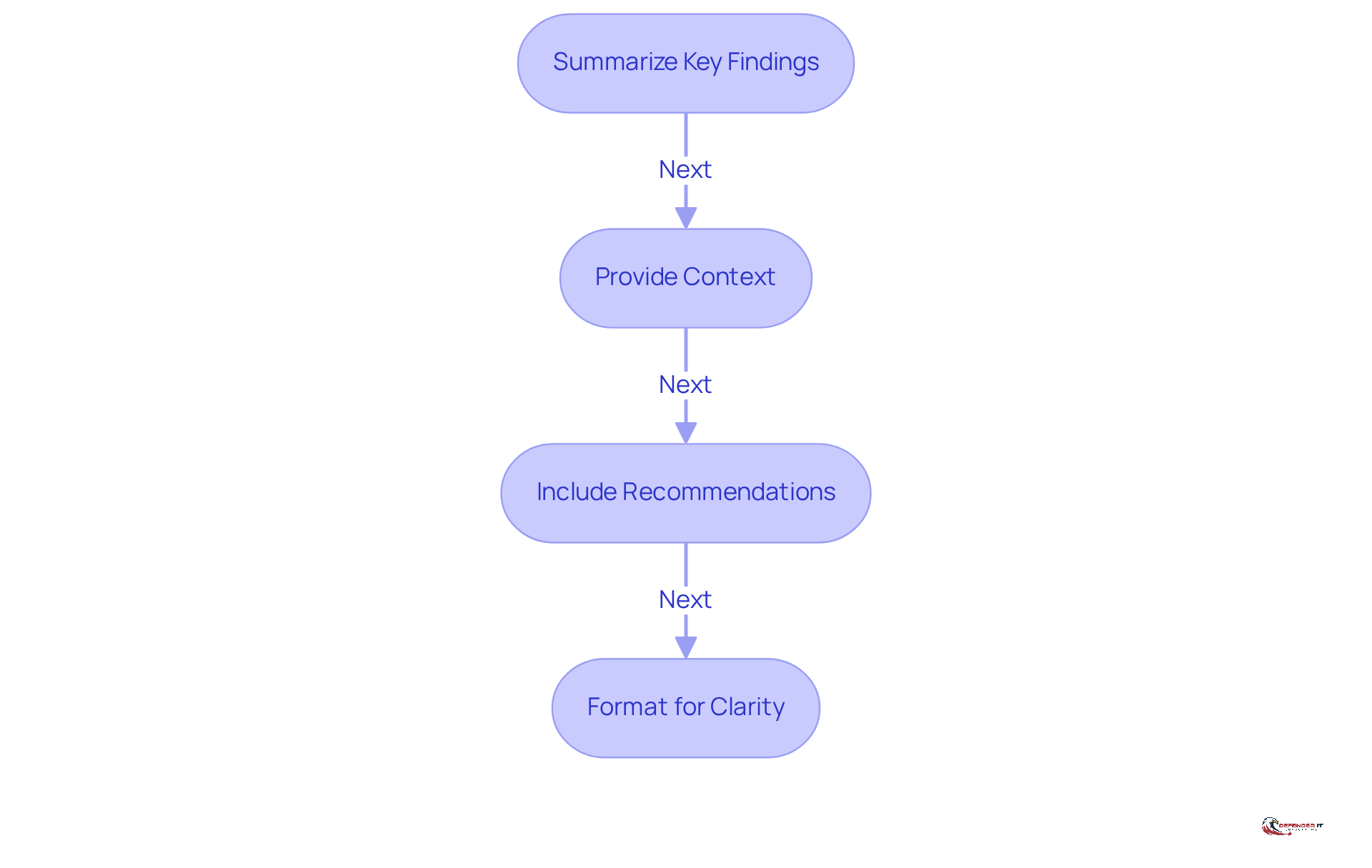
Document Findings and Create a Comprehensive Report
In an era where cyber threats are escalating, documenting vulnerabilities is not just a task; it’s a necessity for organizational resilience. Here’s how to effectively create this report:
- Summarize Key Findings: Clearly highlight the most critical vulnerabilities and risks identified during the assessment. This alarming statistic – 56% of nearly 40,000 tracked vulnerabilities could be exploited without any form of authentication – highlights a critical vulnerability that demands immediate action to safeguard organizational assets.
- Provide Context: Explain the implications of these findings concerning the organization’s overall protection stance and business objectives. The average cost of a data breach for financial firms has reached $6.4 million, and with the projected increase in the frequency of data breaches, this financial burden emphasizes the necessity for organizations to proactively address these vulnerabilities to mitigate potential losses.
- Include Recommendations: Offer actionable recommendations for mitigating identified risks, prioritizing them based on severity. Organizations that adopt strong identity management practices tend to encounter fewer credential-based incidents, emphasizing the significance of robust protective measures.
- Format for Clarity: Use clear headings, bullet points, and visuals (e.g., charts, graphs) to enhance readability and comprehension. A well-organized report not only conveys results efficiently but also acts as a useful resource for future evaluations and security planning.
In 2025, the NJCCIC issued over 94,000 compromised credential notifications, illustrating the increasing need for thorough reporting in security evaluations. Thorough reporting not only enhances immediate security measures but also fortifies long-term strategic planning against evolving threats.
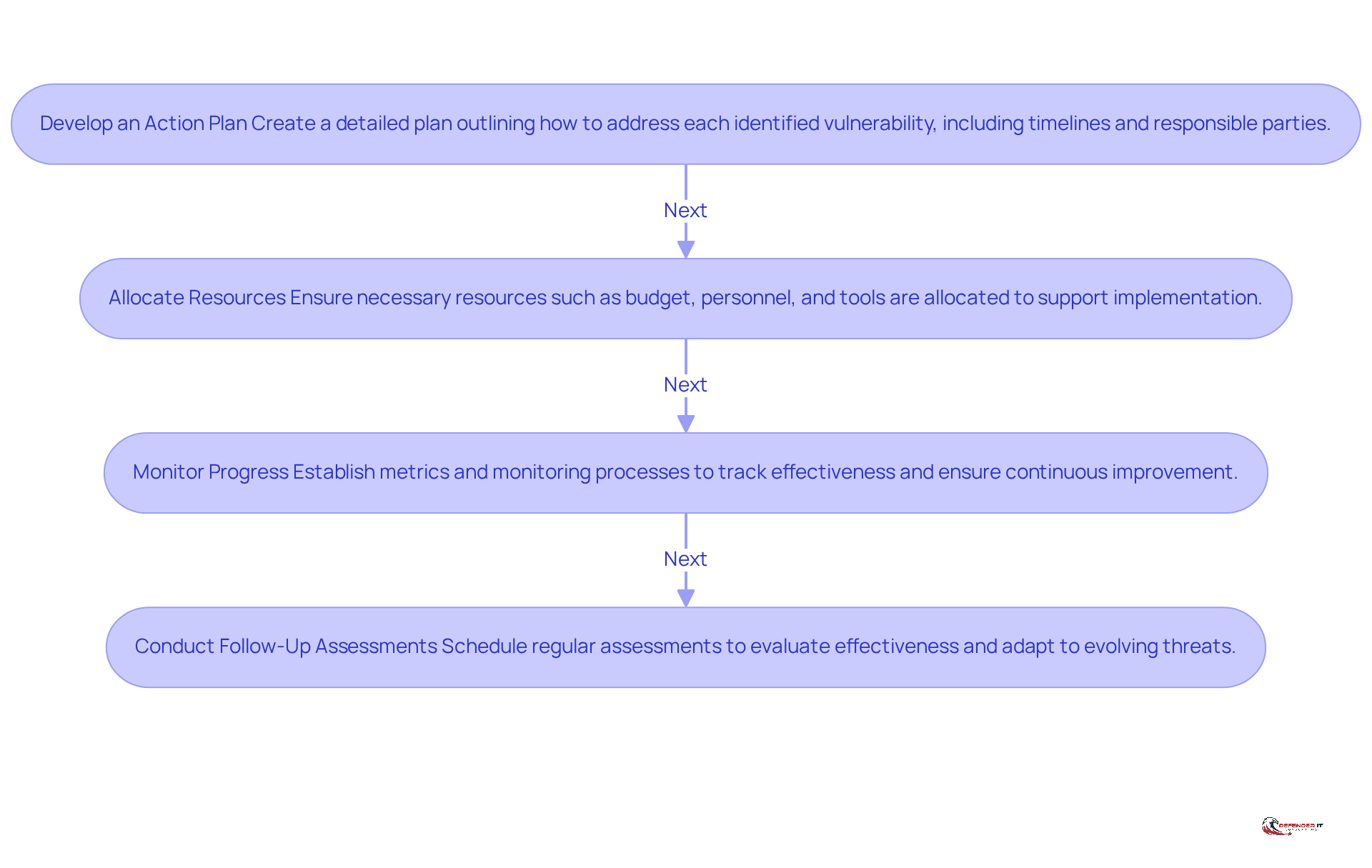
Implement Recommendations and Improve Security Posture
To effectively bolster cybersecurity, organizations must implement a comprehensive action plan that addresses vulnerabilities head-on. Follow these steps:
- Develop an Action Plan: Create a detailed plan outlining how to address each identified vulnerability, including timelines and responsible parties.
- Allocate Resources: Ensure that necessary resources – such as budget, personnel, and tools – are allocated to support the implementation of recommendations. Over the past five years, organizations have increased their cybersecurity budgets by about 8.6%. On average, they now allocate 12% of their IT budgets to security measures.
- Monitor Progress: Establish metrics and monitoring processes to track the effectiveness of implemented changes and ensure continuous improvement. Detecting a data breach typically takes an average of 204 days. This delay can result in substantial costs, particularly in the financial services sector, where breaches can cost between $5.86 and $6.08 million.
- Conduct Follow-Up Assessments: Schedule regular follow-up assessments to evaluate the effectiveness of changes and adapt to evolving threats. As threats evolve, organizations must adapt their strategies to mitigate increasing risks. Ongoing enhancement is crucial, as 61% of entities reported a rise in attack severity over the past year, with ransomware representing 51% of cyberattack expenses for small and medium-sized enterprises (SMEs).
Ultimately, implementing proactive measures in cybersecurity, such as a free cybersecurity assessment, not only safeguards assets but also enhances organizational resilience against future threats.
Conclusion
Without a thorough cybersecurity assessment, organizations risk exposing their digital assets to significant threats. Conducting such an assessment is essential for any organization looking to safeguard its digital assets and enhance its security posture. By identifying vulnerabilities and implementing proactive measures, businesses can effectively defend against the evolving landscape of cyber threats. The steps outlined in this guide provide a clear roadmap for organizations to follow, ensuring they understand their current security weaknesses and take actionable steps to address them.
Key insights from the article emphasize the importance of:
- Defining the scope and objectives of the assessment
- Collecting relevant data
- Analyzing vulnerabilities
- Documenting findings
- Implementing recommendations
Each step plays a critical role in creating a comprehensive cybersecurity strategy that meets regulatory compliance and fosters trust among customers and stakeholders. Furthermore, the necessity for ongoing evaluations cannot be overstated, as the cyber threat landscape is constantly changing.
Ultimately, organizations must recognize that cybersecurity is not a one-time task but an ongoing commitment. This ongoing commitment is vital for adapting to the ever-changing cyber threat landscape. By adopting a proactive approach to cybersecurity assessments and implementing the recommendations provided, businesses can enhance their resilience against future threats. These steps are essential not only for protecting assets but also for achieving long-term success in a digital world.
Frequently Asked Questions
Why are cybersecurity assessments important?
Cybersecurity assessments are critical for identifying vulnerabilities, enhancing compliance with regulations, improving incident response, and establishing trust with customers. They help organizations proactively address security gaps and reduce legal risks.
What are the benefits of conducting regular cybersecurity evaluations?
Regular evaluations help identify weaknesses that cybercriminals could exploit, ensure adherence to industry regulations, enhance incident response plans, and boost customer confidence in digital security.
What statistics highlight the need for regular cybersecurity evaluations?
Statistics show that 56% of nearly 40,000 monitored vulnerabilities can be exploited without authentication, emphasizing the importance of regular assessments in identifying and mitigating risks.
How can cybersecurity assessments improve incident response?
By understanding potential threats, organizations can create more effective incident response plans, which can minimize productivity losses and reputational damage during cyber events.
What steps should be taken to define the scope and objectives of a cybersecurity assessment?
To define the scope and objectives, organizations should identify key assets, set clear objectives, determine boundaries of the assessment, and engage relevant stakeholders early in the process.
Why is it important to identify key assets during a cybersecurity assessment?
Identifying key assets helps organizations understand which systems, applications, and data are critical to operations, allowing them to prioritize vulnerabilities that could have significant impacts if breached.
How does stakeholder engagement contribute to a cybersecurity assessment?
Engaging stakeholders ensures that the evaluation aligns with organizational goals and addresses their concerns, fostering ownership and enhancing the overall effectiveness of the assessment.
What changes are expected in the environment of digital security evaluations by 2026?
The future of digital security evaluations will focus on ongoing, AI-driven risk intelligence that provides real-time insights across identities, data, and third parties, necessitating organizations to adapt their strategies to counter emerging threats.
List of Sources
- Understand the Importance of Cybersecurity Assessments
- Cybersecurity 2026: AI, CISA, manufacturing sector all in the hot seat (https://cybersecuritydive.com/news/cyber-trends-outlook-2026/810708)
- 2026 Cyber Risk Management Strategies To Adopt Now (https://forbes.com/councils/forbestechcouncil/2026/03/02/2026-cyber-risk-management-strategies-to-adopt-now)
- Experts share top cybersecurity concerns for 2026 (https://news.vt.edu/articles/2026/02/top-cybersecurity-concerns-2026-experts.html)
- 2026 Global Threat Report | Latest Cybersecurity Trends & Insights | CrowdStrike (https://crowdstrike.com/en-us/global-threat-report)
- 2026 Cyber Threat Assessment | NJCCIC (https://cyber.nj.gov/threat-landscape/2026-cyber-threat-assessment)
- 10 Cyber Security Trends For 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-trends)
- Cybersecurity Trends 2026 | IBM (https://ibm.com/think/insights/more-2026-cyberthreat-trends)
- Define the Scope and Objectives of Your Assessment
- Cybersecurity Assessments and Distinctive Threats in 2026 (https://eliassen.com/blog/cybersecurity-assessments-and-distinctive-threats-in-2026)
- Cyber Security Audit Guide: Best Practices for 2026 (https://larsbirkeland.com/cyber-security-audit)
- 3 Best Practices for Effective Cyber Assessments in 2026 — Cyber Solutions Inc (https://discovercybersolutions.com/blog-posts/3-best-practices-for-effective-cyber-assessments-in-2026)
- What Is Threat Assessment in Cybersecurity? A 2026 Guide (https://cynomi.com/learn/cybersecurity-threat-assessment)
- 2024 Cybersecurity Statistics: The Ultimate List Of Stats, Data & Trends | PurpleSec (https://purplesec.us/resources/cybersecurity-statistics)
- Collect Necessary Data and Resources for the Assessment
- Cybersecurity Assessments and Distinctive Threats in 2026 (https://eliassen.com/blog/cybersecurity-assessments-and-distinctive-threats-in-2026)
- CISA, partners release asset inventory guidance to protect OT systems from cyberattacks, bolster resilience – Industrial Cyber (https://industrialcyber.co/cisa/cisa-partners-release-asset-inventory-guidance-to-protect-ot-systems-from-cyberattacks-bolster-resilience)
- Why and How to Perform Cybersecurity Risk Assessments in 2026 (https://maddevs.io/blog/how-to-perform-cybersecurity-risk-assessments)
- 2026 Cyber Threat Assessment | NJCCIC (https://cyber.nj.gov/threat-landscape/2026-cyber-threat-assessment)
- Foundations for OT Cybersecurity: Asset Inventory Guidance for Owners and Operators | CISA (https://cisa.gov/resources-tools/resources/foundations-ot-cybersecurity-asset-inventory-guidance-owners-and-operators)
- How to Build a Complete Asset Inventory for Your 2026 Security Assessments (+ Free Template) (https://siemba.io/blogs/asset-inventory-security-assessment-q1)
- Cybersecurity Asset Management in 2026: Benefits & Challenges (https://techugo.com/blog/cybersecurity-asset-management-an-efficient-manner-to-legitimize-your-security-team)
- Analyze Data to Identify Vulnerabilities and Risks
- 2026 Cyber Risk Management Strategies To Adopt Now (https://forbes.com/councils/forbestechcouncil/2026/03/02/2026-cyber-risk-management-strategies-to-adopt-now)
- Cyber Security Risk Outlook 2026 | Threats, Resilience & Risk Insights | LRQA (https://lrqa.com/en-us/resources/cyber-security-risk-outlook-2026-cyber-risk-trends-report)
- 2026 Cyber Threat Assessment | NJCCIC (https://cyber.nj.gov/threat-landscape/2026-cyber-threat-assessment)
- Navigating the Cyber Threat Landscape: 2026 Outlook and Emerging Risks (https://panorays.com/blog/cyber-threat-landscape-2026-emerging-risks)
- The biggest cyber breaches of 2026 so far (https://acilearning.com/blog/the-biggest-cybersecurity-breaches-of-2026-so-far-and-the-training-that-could-have-prevented-them)
- Cybersecurity Trends 2026 | IBM (https://ibm.com/think/insights/more-2026-cyberthreat-trends)
- Document Findings and Create a Comprehensive Report
- Cybersecurity Trends 2026 | IBM (https://ibm.com/think/insights/more-2026-cyberthreat-trends)
- 2026 Global Threat Report | Latest Cybersecurity Trends & Insights | CrowdStrike (https://crowdstrike.com/en-us/global-threat-report)
- 2026 Cyber Threat Assessment | NJCCIC (https://cyber.nj.gov/threat-landscape/2026-cyber-threat-assessment)
- Top Cybersecurity News Stories From March 2026 – Illumio Cybersecurity Blog | Illumio (https://illumio.com/blog/top-cybersecurity-news-stories-from-march-2026)
- Key Cyber Security Statistics for 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-statistics)
- Implement Recommendations and Improve Security Posture
- Strategic Priorities in the 2026 US Cyber Strategy and Cybercrime Executive Order | Weaver (https://weaver.com/resources/strategic-priorities-in-the-2026-us-cyber-strategy-and-cybercrime-executive-order)
- White House Releases New Cyber Security Plan and Executive Order on Combatting Cybercrimes (https://naco.org/news/white-house-releases-new-cyber-security-plan-and-executive-order-combatting-cybercrimes)
- White House Announces The 2026 Cyber Strategy For America (https://forrester.com/blogs/white-house-announces-the-2026-cyber-strategy-for-america)
- Top Cybersecurity Statistics: Facts, Stats and Breaches for 2025 (https://fortinet.com/resources/cyberglossary/cybersecurity-statistics)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)