Introduction
Recent statistics indicate that the manufacturing sector is a primary target for cyberattacks, representing a significant 25% of global incidents in 2023. This concerning trend highlights the urgent need for manufacturers to confront critical cybersecurity risks that jeopardize their operations and financial stability. As threats such as ransomware, phishing, and supply chain attacks grow increasingly sophisticated, organizations must consider effective strategies to safeguard their assets and ensure resilience.
Investigating key approaches for risk mitigation and employee training may provide essential insights for strengthening the manufacturing industry against these evolving threats.
Identify Key Cybersecurity Risks in Manufacturing
Recent cybersecurity reports specific to manufacturing, including the , highlight that the sector faces significant , being the most targeted and accounting for 25% of global incidents in 2023. This statistic underscores the urgent need for enhanced measures to for the manufacturing sector.
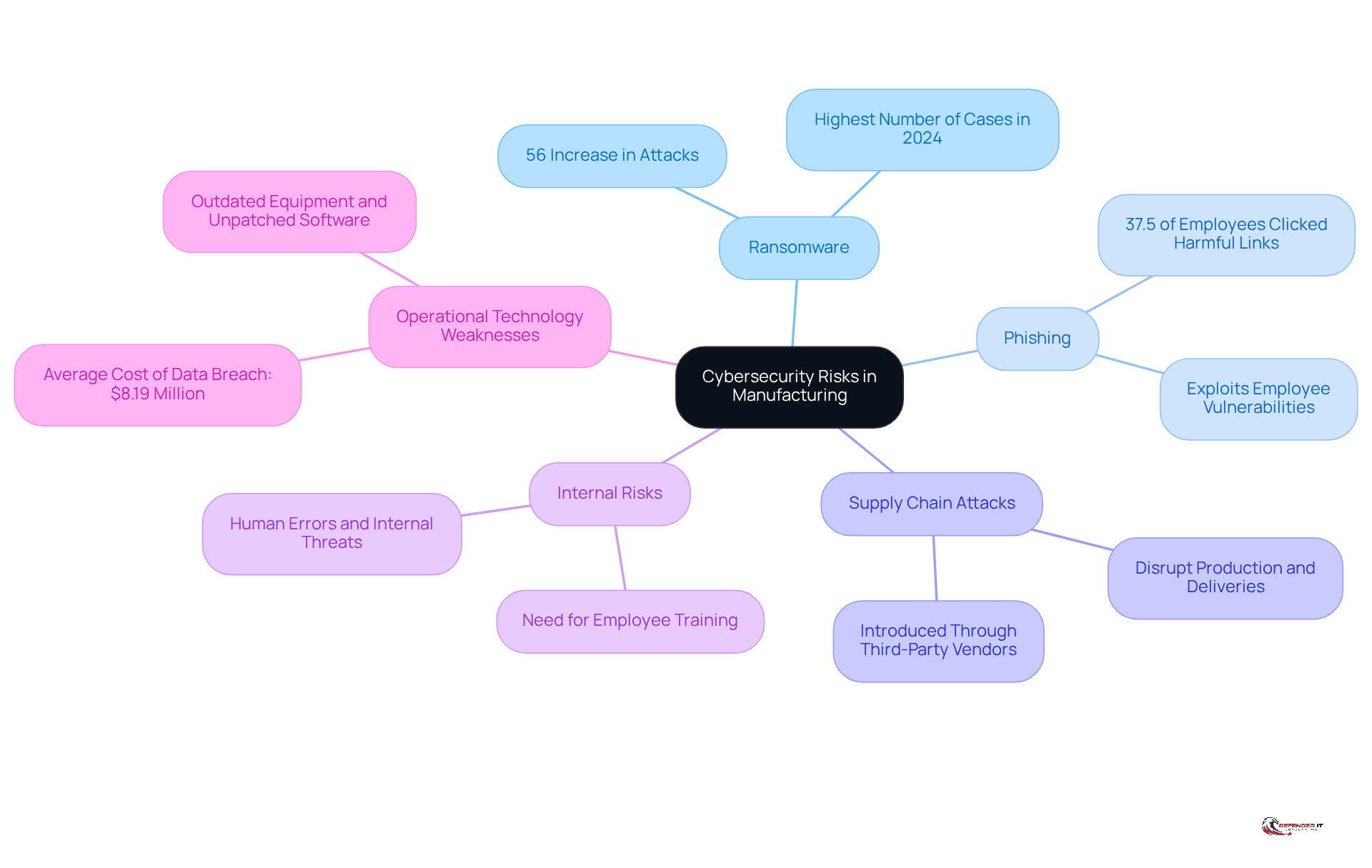
Common threats that represent include:
- Phishing attempts that exploit employee vulnerabilities
Notably, 37.5% of employees in large organizations have clicked on harmful links, as reported by KnowBe4. Additionally, for the manufacturing sector, often introduced through third-party vendors, which further complicates the cybersecurity landscape.
The impact of operational technology (OT) weaknesses on production processes cannot be overstated. Outdated equipment and unpatched software can lead to substantial disruptions and . In fact, the average cost of a data breach in the manufacturing sector, which underscores the , reached $8.19 million in 2023, highlighting the severe financial implications of these vulnerabilities.
Internal risks and human errors are critical factors in the . A proactive approach to is essential to mitigate , including those associated with social engineering fraud and accidental data exposure. By fostering a culture of , organizations can significantly reduce their vulnerability to .
Documenting findings is crucial for developing a for your organization. It is imperative to address all identified weaknesses and threats. Regular audits and updates to your are essential for addressing and maintaining a robust defense against evolving dangers.
Conduct Comprehensive Vulnerability Assessments
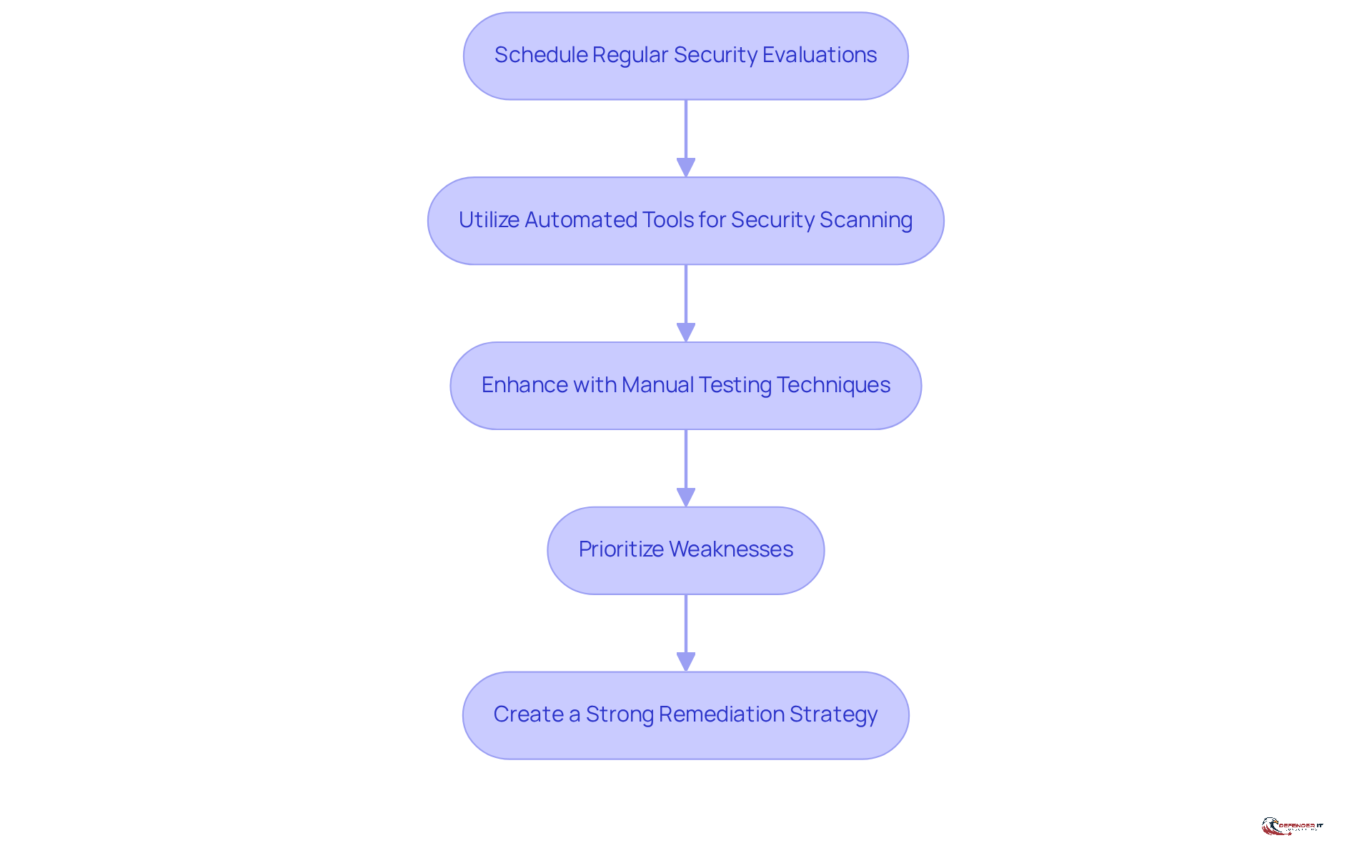
- Schedule regular , ideally on a quarterly basis, to stay ahead of evolving threats. In 2026, entities are encouraged to view testing as an ongoing process rather than a mere annual task, as this approach significantly enhances security posture.
- Utilize across networks and systems. These tools can efficiently identify outdated software, misconfigurations, and known weaknesses, allowing for . The Edgescan Vulnerability Statistics Report highlights that entities employing automated scanning see improved visibility into their .
- Enhance automated scanning with manual testing techniques, such as , to reveal concealed weaknesses that automated tools may overlook. This dual approach guarantees a thorough comprehension of potential risks, as demonstrated by successful case studies where organizations recognized essential weaknesses through .
- Prioritize weaknesses based on their risk level and potential impact. With over 33% of identified weaknesses categorized as , concentrating remediation efforts on the most urgent threats is essential. This approach enables security teams to distribute resources efficiently and tackle the weaknesses that present the highest threat to operations.
- Create a strong for addressing identified weaknesses. This plan should incorporate timelines for corrections, accountable individuals, and approaches for confirming that weaknesses have been effectively addressed. is crucial for maintaining compliance and demonstrating due diligence to customers and regulators.
Implement Targeted Cybersecurity Solutions
To effectively counter cybersecurity risks for the manufacturing sector, companies must adopt targeted solutions that address their unique vulnerabilities. A critical step is the adoption of for all critical systems. MFA can block up to 99.2% of account compromise attacks, significantly reducing the risk of unauthorized access. While MFA is essential for businesses, it is important to note that it is . Adoption rates for MFA are significantly higher in larger entities, with 78% of firms utilizing MFA in those with 1,001 to 10,000 employees, compared to only 34% in smaller businesses with fewer than 100 employees. This disparity highlights the need for smaller manufacturers to prioritize MFA implementation as part of their security strategy. MFA adoption should be treated as a C-suite and board-level risk metric for organizational security.
In addition to MFA, investing in is essential. Technologies like Endpoint Detection and Response (EDR) and Security Information and Event Management (SIEM) systems offer real-time monitoring and analytics, allowing organizations to detect and react to threats promptly. For instance, the integration of AI-driven tools can enhance detection capabilities, enabling manufacturers to stay ahead of evolving cyber threats.
Regular software updates and patch management are also vital components of a robust cybersecurity framework. By ensuring that all systems are up-to-date, manufacturers can mitigate vulnerabilities that cybercriminals often exploit. Furthermore, adopting a limits access to sensitive data, ensuring that only authorized users can interact with critical systems.
can provide tailored solutions that meet the specific needs of manufacturing organizations. For example, the aims to help small manufacturers enhance their cybersecurity. Case studies have shown that implementing MFA , which helps to mitigate cybersecurity risks for the manufacturing sector and reduces the risk of hacking incidents. As Lindsey O’Donnell-Welch states, “MFA isn’t just a nice-to-have anymore-it’s a must for keeping your business safe from cyber threats.” By leveraging these targeted cybersecurity solutions, manufacturers can better protect their operations and maintain compliance with industry regulations.
Enhance Employee Cybersecurity Training and Awareness
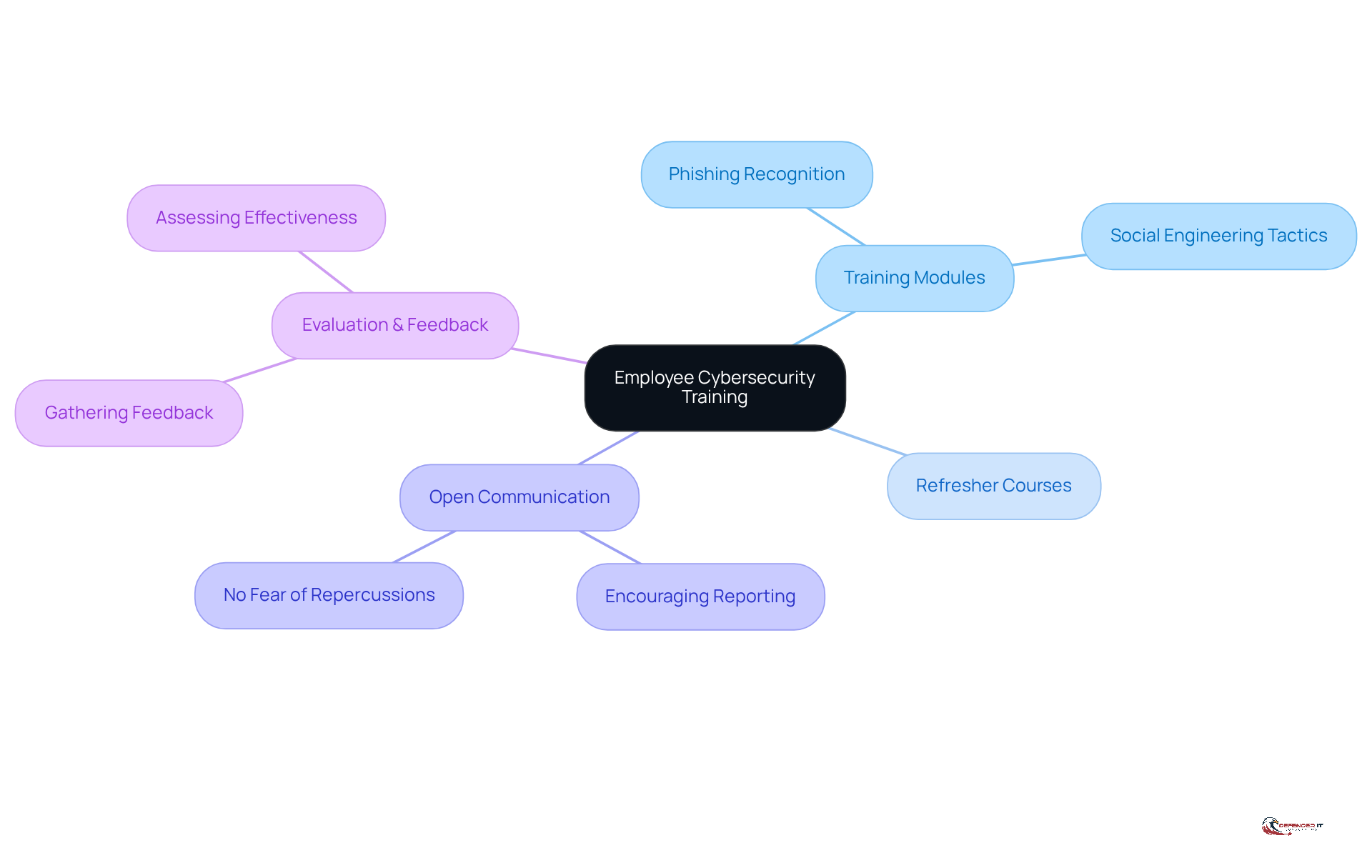
To establish a robust , it is essential to develop a for all employees. This program should include modules focused on and understanding , which are critical in today’s digital landscape.
Regular must be conducted to reinforce learning and ensure that employees remain vigilant against evolving threats. These sessions will not only enhance knowledge retention but also prepare staff to respond effectively to .
Furthermore, it is crucial to foster an environment where employees feel encouraged to without fear of repercussions. This open communication can significantly enhance the organization’s overall .
To assess the effectiveness of the , it is important to implement evaluations and . This data will provide insights into areas for improvement and help refine the training initiatives, ensuring they meet the organization’s cybersecurity needs.
Establish an Effective Incident Response Plan
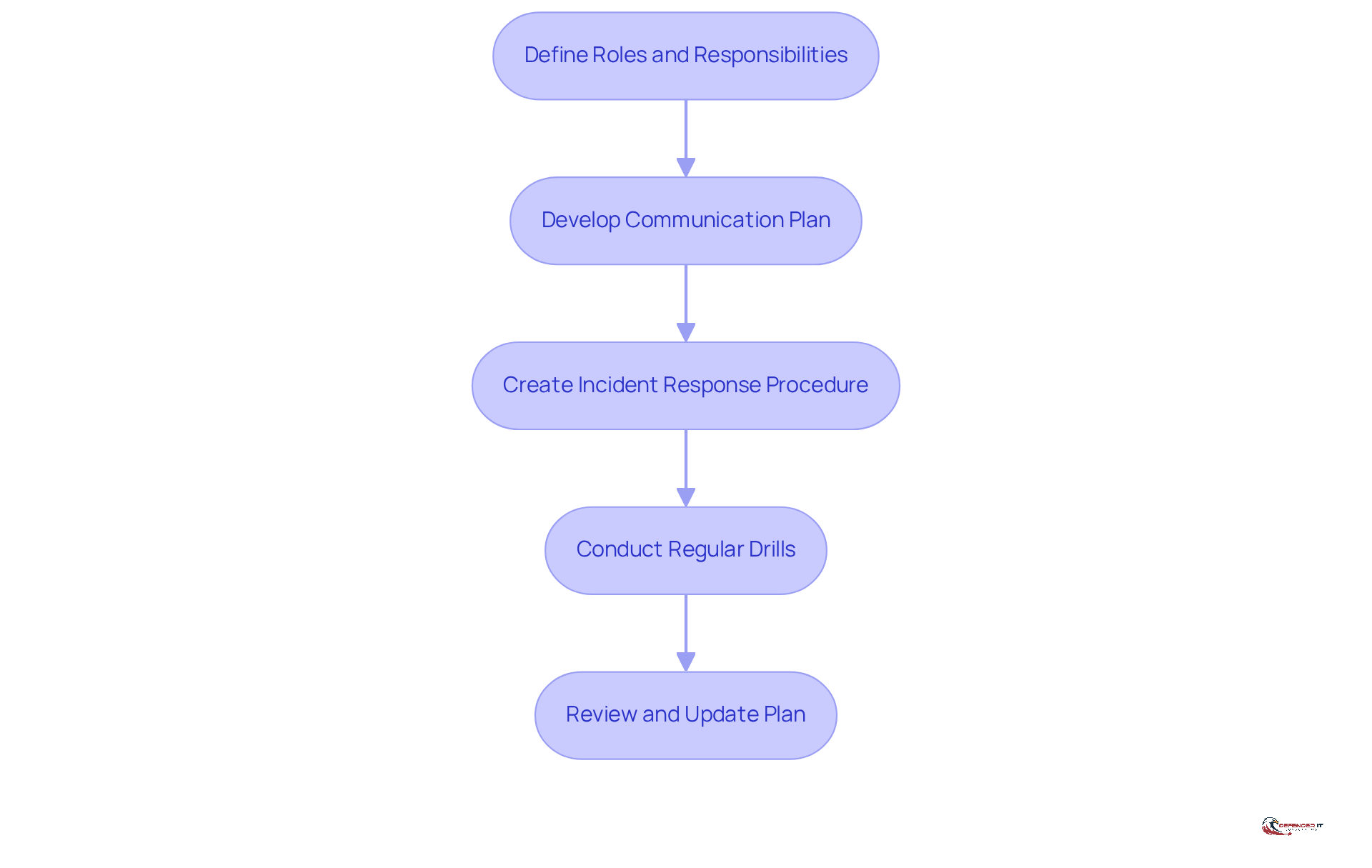
- Clearly define the roles and responsibilities of each member of the to ensure accountability and effective collaboration.
- Develop a comprehensive that addresses the needs of both internal and external stakeholders, facilitating timely and accurate information dissemination during incidents.
- Create a incident response procedure that encompasses all phases: , ensuring a systematic approach to .
- Conduct of the , allowing for of response capabilities.
- Continuously review and update the based on insights gained from previous incidents and drills, .
Conclusion
Addressing cybersecurity risks in the manufacturing sector is a necessity. The industry faces numerous threats, including ransomware, phishing, and vulnerabilities in operational technology. Given that manufacturing is a prime target for cyberattacks, organizations must prioritize robust cybersecurity measures to safeguard their operations and data.
Key insights emphasize the importance of:
- Regular vulnerability assessments
- Targeted cybersecurity solutions
- Comprehensive employee training
By implementing:
- Multi-factor authentication
- Investing in advanced detection tools
- Fostering a culture of cybersecurity awareness
Manufacturers can significantly reduce their exposure to cyber threats. Furthermore, establishing a well-defined incident response plan is crucial for effectively managing any potential breaches.
As the manufacturing sector evolves, so do the cybersecurity challenges it faces. It is imperative for organizations to remain proactive, continuously updating their security strategies and training programs to adapt to the changing landscape. By doing so, they not only protect their assets but also contribute to a more secure industry overall. Taking action now can make a significant difference in mitigating risks and ensuring a resilient future in manufacturing.
Frequently Asked Questions
What are the main cybersecurity risks facing the manufacturing sector?
The manufacturing sector faces significant cybersecurity risks, including ransomware, phishing attempts, supply chain attacks, and weaknesses in operational technology (OT). In 2023, manufacturing accounted for 25% of global cybersecurity incidents.
How much did ransomware attacks increase in the manufacturing sector?
Ransomware attacks saw a 56% increase in the manufacturing sector, according to KnowBe4.
What percentage of employees in large organizations have clicked on harmful links?
Notably, 37.5% of employees in large organizations have clicked on harmful links, which highlights vulnerabilities to phishing attempts.
What is the average cost of a data breach in the manufacturing sector?
The average cost of a data breach in the manufacturing sector reached $8.19 million in 2023, emphasizing the financial implications of cybersecurity vulnerabilities.
What role do internal risks and human errors play in cybersecurity for manufacturing?
Internal risks and human errors are critical factors in cybersecurity risks for the manufacturing sector. Proactive employee training is essential to mitigate these risks, including social engineering fraud and accidental data exposure.
How often should vulnerability assessments be conducted?
Regular security evaluations should ideally be scheduled on a quarterly basis to stay ahead of evolving threats.
What tools can be utilized for vulnerability assessments?
Automated tools for security scanning across networks and systems can efficiently identify outdated software, misconfigurations, and known weaknesses, allowing for timely remediation.
Why is manual testing important in addition to automated scanning?
Manual testing techniques, such as penetration testing, are important because they can reveal concealed weaknesses that automated tools may overlook, ensuring a thorough understanding of potential risks.
How should organizations prioritize identified weaknesses?
Organizations should prioritize weaknesses based on their risk level and potential impact, focusing remediation efforts on the most urgent threats, as over 33% of identified weaknesses are categorized as critical or high severity.
What should a remediation strategy for identified weaknesses include?
A remediation strategy should include timelines for corrections, accountable individuals, and methods for confirming that weaknesses have been effectively addressed, with regular reviews and updates to maintain compliance and demonstrate due diligence.
List of Sources
- Identify Key Cybersecurity Risks in Manufacturing
- X-Force 2025 Threat Intelligence Index | IBM (https://ibm.com/reports/threat-intelligence)
- Cyber Attacks Continue to Pose Major Threat to Manufacturing Sector | CBIZ (https://cbiz.com/insights/article/cyber-attacks-continue-to-pose-major-threat-to-manufacturing-sector)
- Cybersecurity Facts and Stats as of 2026 (https://preveil.com/blog/cybersecurity-statistics)
- valonaintelligence.com (https://valonaintelligence.com/resources/blog/7-cybersecurity-statistics-for-heavy-manufacturing-companies)
- Conduct Comprehensive Vulnerability Assessments
- Threat and Vulnerability Management in 2026 (https://recordedfuture.com/blog/threat-and-vulnerability-management)
- Embracing Cybersecurity in the New Year: A 2026 Perspective | Digital Segment (https://digitalsegment.com/2026/01/14/embracing-cybersecurity-in-the-new-year-a-2026-perspective)
- The top 20 expert quotes from the Cyber Risk Virtual Summit (https://diligent.com/resources/blog/top-20-quotes-cyber-risk-virtual-summit)
- Vulnerability Statistics Report (https://edgescan.com/stats-report)
- Implement Targeted Cybersecurity Solutions
- MFA for Business: Benefits, Methods & Why It Still Matters | Huntress (https://huntress.com/blog/demystifying-multi-factor-authentication-for-businesses)
- Must-Have Cybersecurity Tools for 2026 (https://uscsinstitute.org/cybersecurity-insights/blog/must-have-cybersecurity-tools-for-2026)
- Multi-Factor Authentication: The Four Most Important Things to Know | MxD (https://mxdusa.org/news/multi-factor-authentication-the-four-most-important-things-to-know)
- The Secure Sign-in Trends Report 2025 (https://okta.com/newsroom/articles/secure-sign-in-trends-report-2025)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Enhance Employee Cybersecurity Training and Awareness
- ien.com (https://ien.com/operations/blog/22958561/manufacturing-cybersecurity-training-must-become-experiential)
- Security awareness training in manufacturing: The ultimate guide | Infosec (https://infosecinstitute.com/resources/security-awareness/ultimate-guide-manufacturing)
- Security Awareness Training Statistics 2025 [100+ Studies] | Brightside AI Blog (https://brside.com/blog/security-awareness-training-statistics-2025-100-studies)
- 40 Security Awareness Statistics MSPs Can’t Ignore in 2025 | Guardz.com (https://guardz.com/blog/40-security-awareness-statistics-msps-cant-ignore-in-2025)
- Security Awareness Training: USA 2025 Statistics | Infrascale (https://infrascale.com/security-awareness-training-statistics-usa)
- Establish an Effective Incident Response Plan
- 5 Incident Management Lessons To Carry Into 2026 (https://thenewstack.io/5-incident-management-lessons-to-carry-into-2026)
- Incident Response Teams: Roles and Responsibilities & Structure (https://sygnia.co/blog/incident-response-team)
- Incident Response Statistics to Know in 2025 (https://jumpcloud.com/blog/incident-response-statistics)
- Incident Response Statistics: USA | Infrascale (https://infrascale.com/incident-response-statistics-usa-2025)
- frsecure.com (https://frsecure.com/blog/incident-response-statistics-how-do-you-compare)