Introduction
Effective penetration testing is essential in modern cybersecurity strategies, acting as a proactive measure to identify and mitigate vulnerabilities before they can be exploited by malicious actors. This practice not only enhances an organization’s security posture but also ensures compliance with regulatory standards and fosters a culture of continuous improvement.
However, many organizations face challenges in implementing structured methodologies that effectively uncover weaknesses while adapting to the ever-evolving threat landscape. Therefore, businesses must navigate these complexities to safeguard their digital assets.
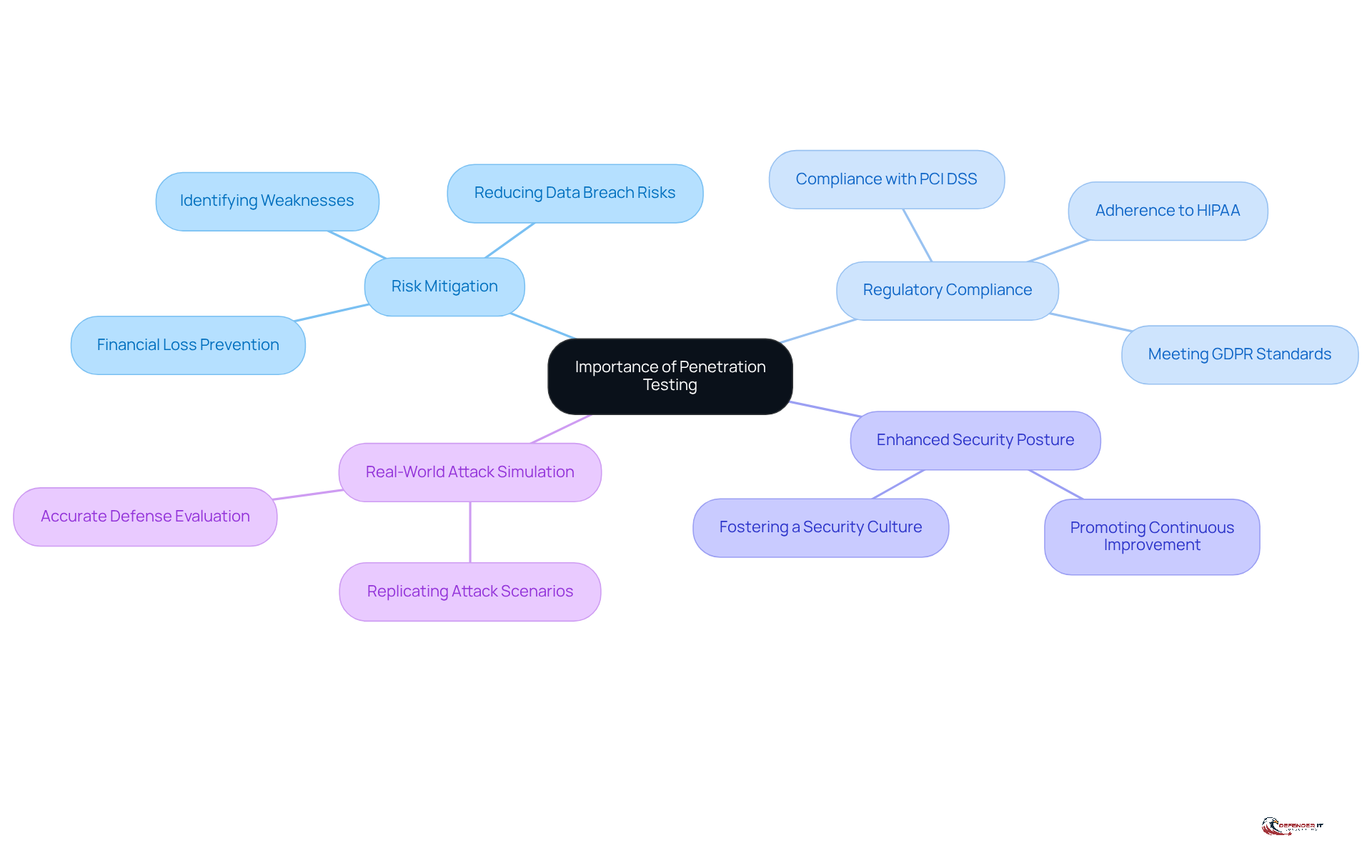
Understand the Importance of Penetration Testing
Penetration testing security serves as a simulated cyber attack that aids organizations in identifying vulnerabilities within their systems, applications, and networks. This practice is essential for several reasons:
- Risk Mitigation: Identifying weaknesses before they can be exploited by attackers allows organizations to significantly reduce the risk of data breaches and financial losses.
- Regulatory Compliance: Various sectors, particularly finance and healthcare, are subject to stringent regulations that require regular risk evaluations. Penetration assessments help ensure compliance with standards such as PCI DSS, HIPAA, and GDPR.
- Enhanced Security Posture: Conducting regular penetration testing security fosters a culture of security within an organization, promoting proactive measures and continuous improvement in security practices.
- Real-World Attack Simulation: Unlike automated scans, penetration tests replicate , providing a more accurate evaluation of a company’s defenses.
For example, a financial organization that conducts routine penetration tests can identify and rectify vulnerabilities that may lead to unauthorized access to sensitive customer information, thereby protecting its reputation and maintaining customer trust.
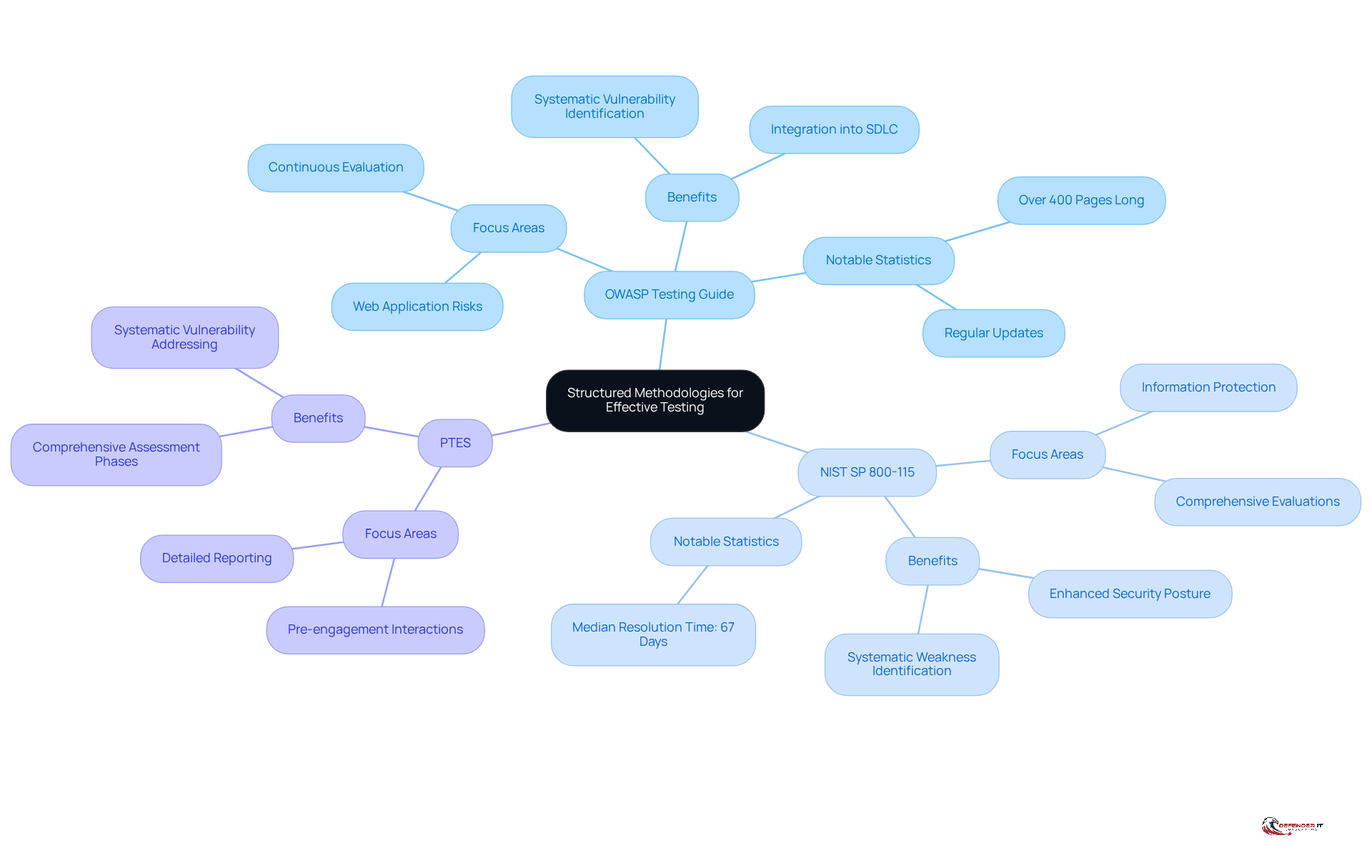
Adopt Structured Methodologies for Effective Testing
To enhance the efficiency of penetration evaluations, organizations should implement organized methodologies that provide a clear framework for assessing safety. Key frameworks include:
- OWASP Testing Guide: This extensive resource, spanning over 400 pages, focuses on the most significant risks in web applications, offering a systematic approach to identifying vulnerabilities. The guide is regularly updated, with the latest version emphasizing the importance of and integration into the Software Development Lifecycle (SDLC). Cybersecurity experts note, “The OWASP Web Security Testing Guide offers a thorough, organized approach for evaluating web application vulnerabilities.”
- NIST SP 800-115: This technical guide outlines a systematic method for evaluating and assessing information protection, ensuring that penetration evaluations are comprehensive and effective. Organizations that adopt this framework can enhance their security posture by systematically identifying and addressing weaknesses. Notably, the median time to resolve all penetration test findings is approximately 67 days, highlighting the critical role of structured methodologies in facilitating timely remediation.
- PTES (Penetration Execution Standard): PTES encompasses all phases of penetration assessments, from pre-engagement interactions to detailed reporting. This framework ensures that all essential components, including reconnaissance, scanning, exploitation, and reporting, are systematically addressed.
By adhering to these methodologies, organizations can conduct penetration tests that are not only systematic but also thorough, effectively identifying vulnerabilities such as those outlined in the OWASP Top 10, including SQL injection and cross-site scripting. The global penetration testing market, valued at $1.98 billion in 2025 and projected to reach $4.39 billion by 2031, underscores the growing significance of these structured approaches in the evolving cybersecurity landscape.
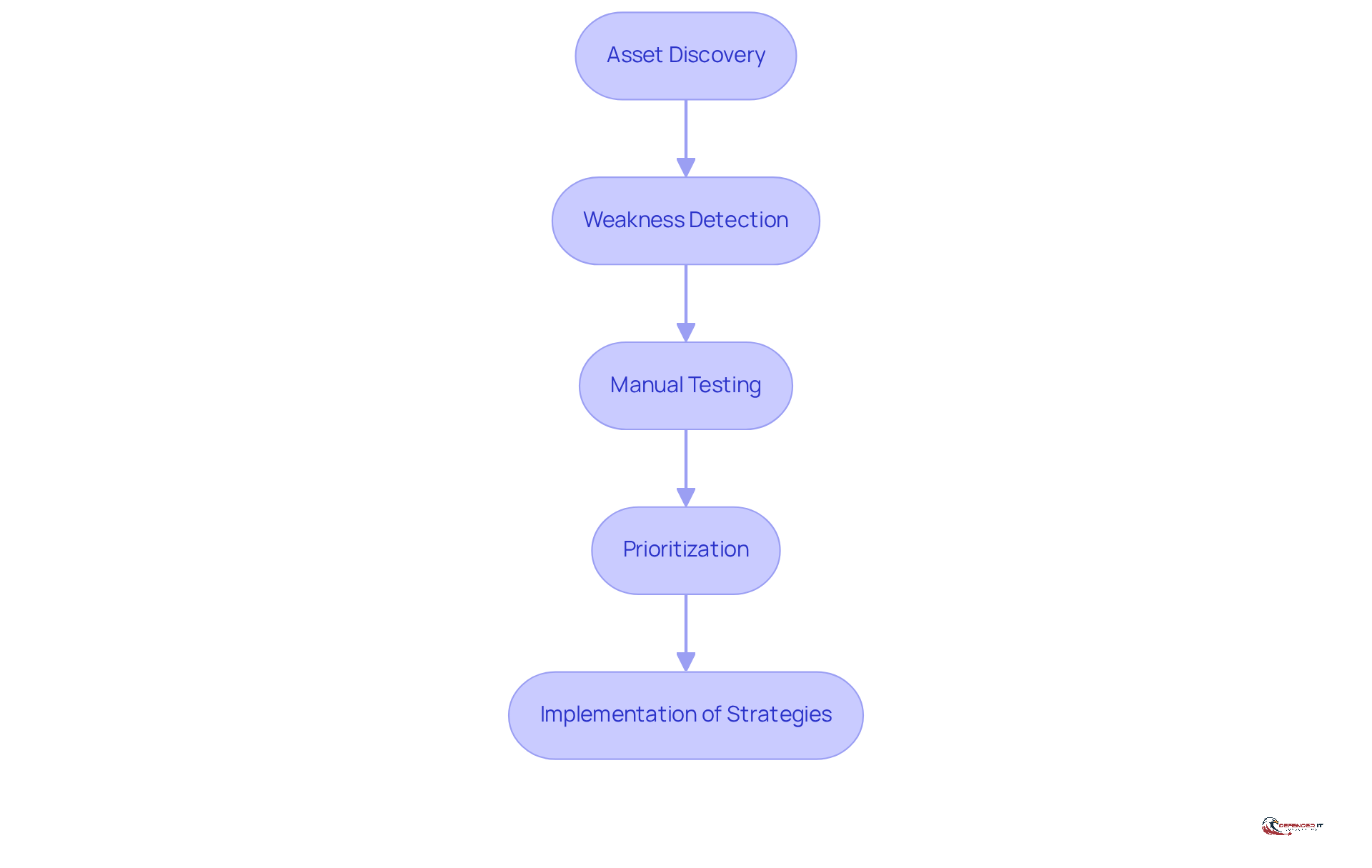
Conduct Comprehensive Vulnerability Assessments
A thorough risk evaluation is essential for revealing security flaws within a company. This assessment is critical for maintaining a robust security posture and involves several key steps:
- Asset Discovery: Identify all assets within the organization, including hardware, software, and network components. Ongoing asset identification is vital for maintaining an accurate inventory, which is crucial for effective risk management. As Acronis states, “VA is not a siloed tool but a continuous, integrated part of your entire security posture.”
- Weakness Detection: Utilize automated tools to examine known weaknesses in systems and applications. Tools such as Nessus and Qualys are widely recognized for their efficiency in this stage, allowing for quick identification of vulnerabilities and promoting prompt remediation. Notably, the average ‘patching gap’ is 27 days between exploit and patch, highlighting the urgency of timely remediation efforts.
- Manual Testing: Complement automated scans with manual testing to uncover weaknesses that automated tools may overlook, such as business logic flaws. This dual approach enhances the overall effectiveness of the assessment.
- Prioritization: Assess the severity of identified weaknesses based on their potential impact and exploitability. This prioritization enables organizations to focus remediation efforts on the most critical issues, thereby reducing risk exposure. With forecasts predicting approximately 59,000 weaknesses in 2026, the importance of cannot be overstated.
For instance, a healthcare organization may uncover vulnerabilities in its patient management system that could jeopardize sensitive patient data. By addressing these weaknesses, the organization can implement strategies to mitigate risks, safeguarding both patient information and regulatory compliance. Additionally, organizations should be aware of common pitfalls in risk assessments, such as neglecting to update asset inventories or failing to integrate findings into a cohesive remediation plan.
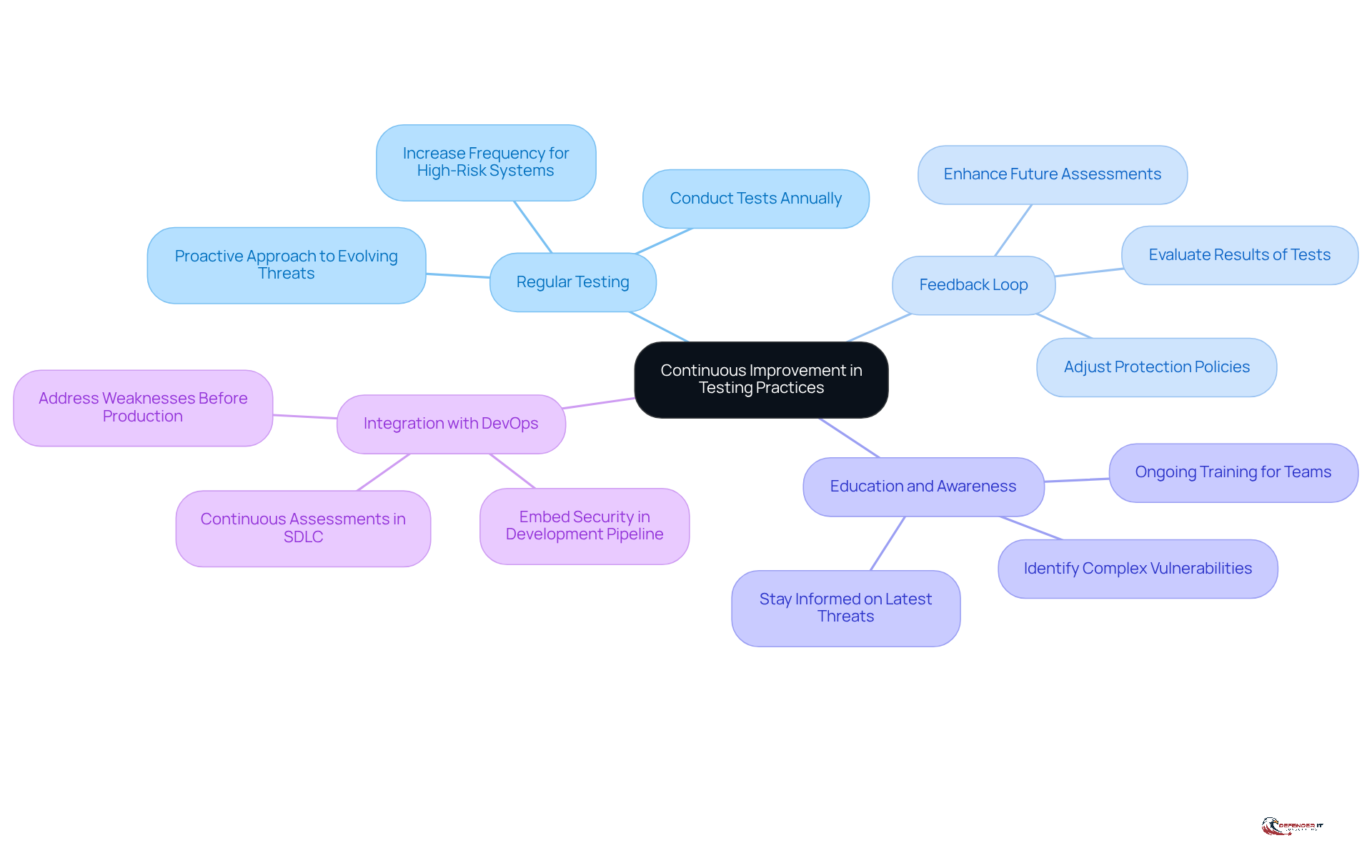
Implement Continuous Improvement in Testing Practices
To maintain an effective protective stance, organizations must prioritize continuous improvement in their . Here are key strategies to consider:
- Regular Testing: Conduct penetration tests at least annually, increasing frequency for high-risk systems or after significant environmental changes. This proactive approach enables organizations to stay ahead of evolving threats, as exploitation of vulnerabilities rose 34% year-over-year, according to Verizon’s 2025 Data Breach Investigation Report.
- Feedback Loop: Establish a robust feedback mechanism to learn from each penetration test. By evaluating results and adjusting protection policies accordingly, organizations can enhance the effectiveness of future assessments and strengthen overall safety measures.
- Education and Awareness: Provide ongoing training for protection teams to keep them informed about the latest threats and assessment techniques. This ensures that teams are equipped to identify complex vulnerabilities that automated tools may overlook.
- Integration with DevOps: Embed security evaluations within the DevOps pipeline, ensuring that security considerations are integrated at every stage of development. Organizations that incorporate continuous penetration assessments into their software development lifecycle can identify and address weaknesses before they reach production, significantly reducing the risk of exploitation.
For instance, companies adopting a hybrid model of penetration evaluation, which combines automated tools with human expertise, have reported improved outcomes in vulnerability management. This approach, often referred to as Penetration Testing as a Service (PTaaS) or Continuous Application Security Testing, not only enhances the quality of security assessments but also aligns with the evolving regulatory landscape, underscoring the necessity for continuous testing to meet compliance requirements.
Conclusion
Penetration testing is essential to an organization’s cybersecurity strategy, acting as a proactive measure to identify and address vulnerabilities before they can be exploited. Understanding the importance of penetration testing, adopting structured methodologies, conducting comprehensive vulnerability assessments, and implementing continuous improvement practices significantly enhance an organization’s security posture and mitigate risks associated with cyber threats.
Key insights emphasize the necessity of:
- Risk mitigation
- Regulatory compliance
- The value of real-world attack simulations
Utilizing established frameworks such as:
- OWASP
- NIST SP 800-115
- PTES
ensures that penetration tests are thorough and systematic. Moreover, the importance of ongoing assessments and timely remediation is critical, as these practices enable organizations to stay ahead of evolving threats and maintain a robust defense against potential breaches.
Ultimately, effective penetration testing extends beyond mere compliance; it fosters a culture of security within organizations, empowering teams to proactively identify and remediate vulnerabilities. By prioritizing penetration testing and continuously refining testing methodologies, organizations not only protect their assets but also build trust with stakeholders, ensuring long-term resilience in an increasingly complex cybersecurity landscape. Embracing these best practices is crucial for organizations aiming to safeguard their systems and maintain a competitive edge in the digital age.
Frequently Asked Questions
What is penetration testing?
Penetration testing is a simulated cyber attack that helps organizations identify vulnerabilities within their systems, applications, and networks.
Why is penetration testing important for organizations?
It is important because it helps in risk mitigation by identifying weaknesses before they can be exploited, ensures regulatory compliance, enhances the security posture of the organization, and provides real-world attack simulations for more accurate defense evaluations.
How does penetration testing help with risk mitigation?
By identifying vulnerabilities before they can be exploited by attackers, organizations can significantly reduce the risk of data breaches and financial losses.
What role does penetration testing play in regulatory compliance?
Penetration testing helps organizations comply with stringent regulations, particularly in sectors like finance and healthcare, by ensuring regular risk evaluations that meet standards such as PCI DSS, HIPAA, and GDPR.
How does penetration testing enhance an organization’s security posture?
Regular penetration testing fosters a culture of security within an organization, promoting proactive measures and continuous improvement in security practices.
What distinguishes penetration testing from automated scans?
Penetration tests replicate real-world attack scenarios, providing a more accurate evaluation of a company’s defenses compared to automated scans.
Can you provide an example of how penetration testing benefits a financial organization?
A financial organization that conducts routine penetration tests can identify and rectify vulnerabilities that may lead to unauthorized access to sensitive customer information, thereby protecting its reputation and maintaining customer trust.