Introduction
As cyber threats become increasingly sophisticated, organizations must confront the pressing challenge of strengthening their defenses. The selection of an effective vulnerability scanner has never been more critical, as it serves as the frontline defense in identifying and mitigating potential security weaknesses.
With so many options available, how can organizations identify the scanner that best fits their unique requirements? This article delves into the essential features and comparative strengths of the best vulnerability scanners for 2023, equipping readers with the insights necessary to make informed decisions in their cybersecurity strategy.
Understanding the nuances of vulnerability scanners is essential; the wrong choice could leave your organization exposed to significant risks.
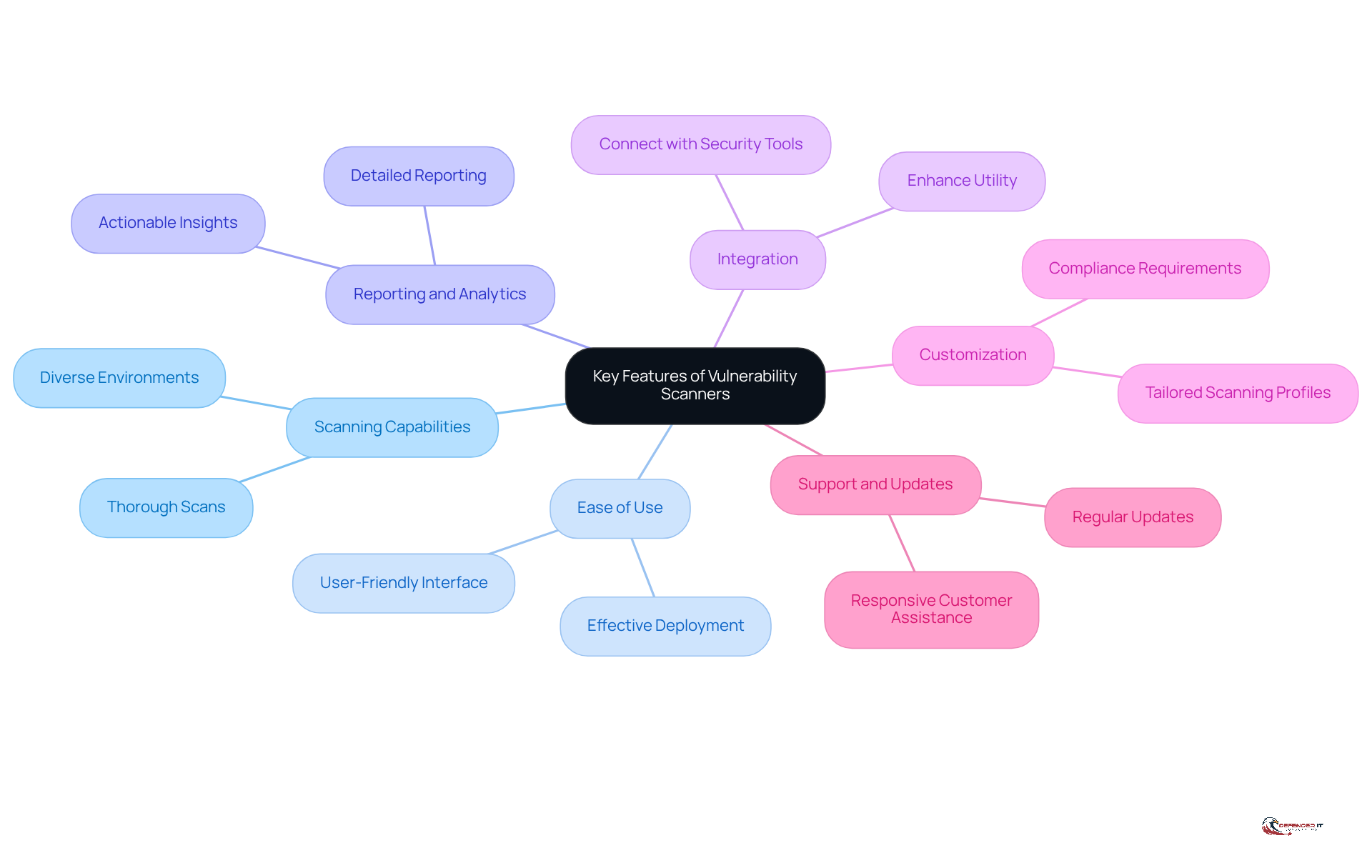
Key Features to Consider in Vulnerability Scanners
In an era where cyber threats are increasingly sophisticated, selecting the best vulnerability scanner 2023 is critical for organizations aiming to safeguard their assets. When evaluating vulnerability scanners, several key features should be prioritized:
- Scanning Capabilities: Seek out resources that can conduct thorough scans across diverse environments, including networks, web applications, and databases.
- Ease of Use: A user-friendly interface is crucial for effective deployment and management, especially for teams with varying levels of expertise.
- Reporting and Analytics: Detailed reporting features that provide actionable insights and prioritize vulnerabilities based on risk are essential for effective remediation.
- Integration: The capability to connect with current security tools and workflows improves the device’s utility and effectiveness.
- Customization: Customizable scanning profiles enable entities to tailor scans to their specific environments and compliance requirements.
- Support and Updates: Regular updates and responsive customer assistance are essential for maintaining the device’s effectiveness against evolving threats.
Without these essential features, organizations risk leaving vulnerabilities unaddressed, potentially exposing them to significant threats. By prioritizing these features, organizations can significantly enhance their security posture and effectively mitigate risks with the best vulnerability scanner 2023.
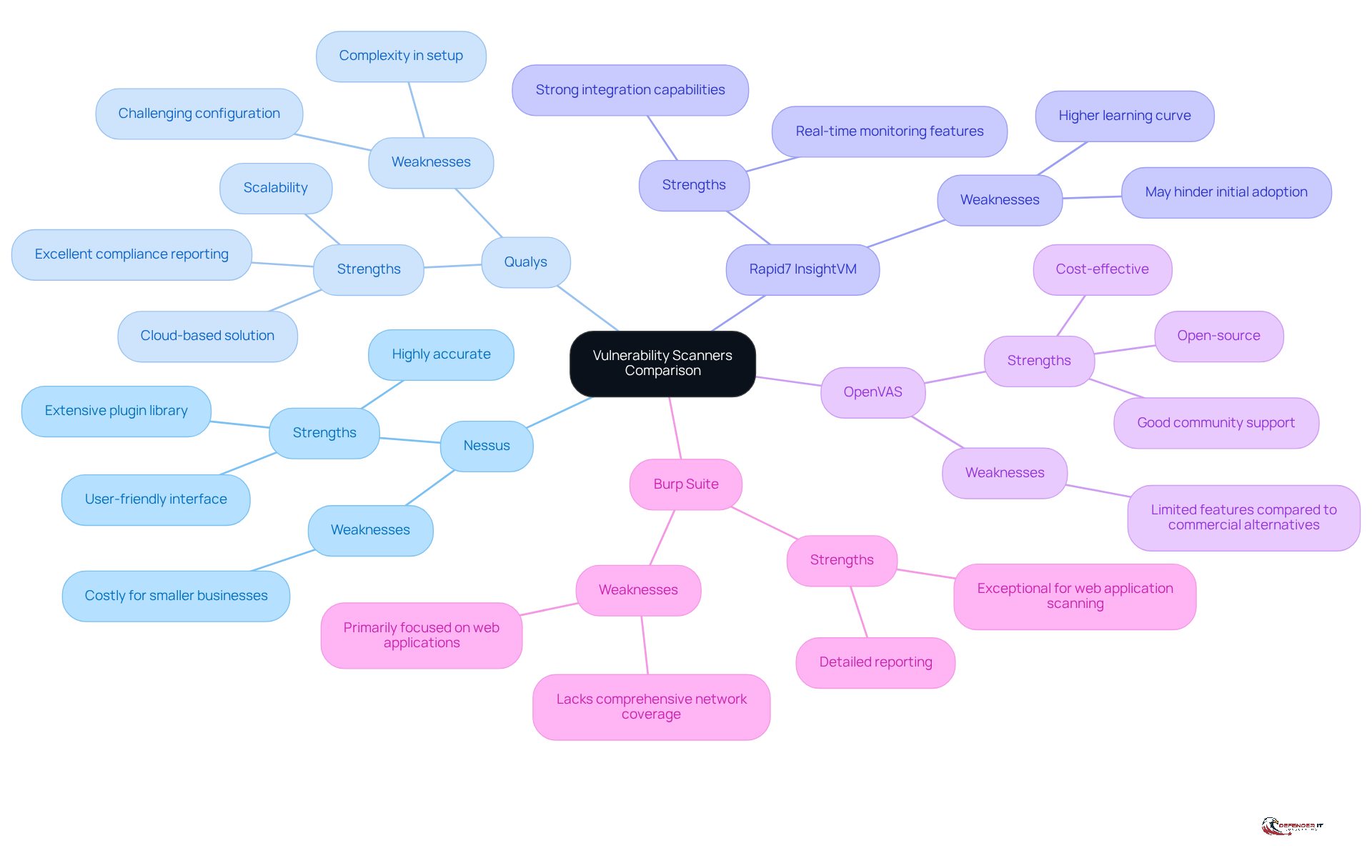
Comparison of Top Vulnerability Scanners: Strengths and Weaknesses
In an era where cybersecurity threats are increasingly sophisticated, vulnerability assessment applications play a pivotal role in identifying and mitigating security weaknesses in IT environments. In 2023, a comparative examination of the best vulnerability scanner 2023 reveals their unique strengths and weaknesses, allowing entities to choose the most appropriate option for their cybersecurity requirements. Various types of security assessment tools, such as network-based, host-based, application, and database tools, each fulfill specific roles in enhancing security measures.
- Nessus: Highly accurate with an extensive plugin library and a user-friendly interface.
Weaknesses: Can be costly for smaller businesses. - Qualys: Cloud-based solution with excellent compliance reporting and scalability.
Weaknesses: Complexity in setup and configuration can be challenging. - Rapid7 InsightVM: Strong integration capabilities and real-time monitoring features.
Weaknesses: Higher learning curve for new users may hinder initial adoption. - OpenVAS: Open-source and cost-effective, with good community support.
Weaknesses: Limited features compared to commercial alternatives. - Burp Suite: Exceptional for web application scanning, providing detailed reporting.
Weaknesses: Primarily focused on web applications, lacking comprehensive network coverage.
The following encapsulates the essential attributes of each scanner, providing organizations with a clear comparison to identify the tool that best aligns with their specific security requirements. Based on recent information, the best vulnerability scanner 2023 includes top commercial security assessment tools such as Nessus, Qualys, and Rapid7 InsightVM, emphasizing their market presence and significance in the cybersecurity field. Choosing the right assessment tool is not merely a technical decision; it is a critical step in safeguarding an organization’s digital assets against evolving threats.
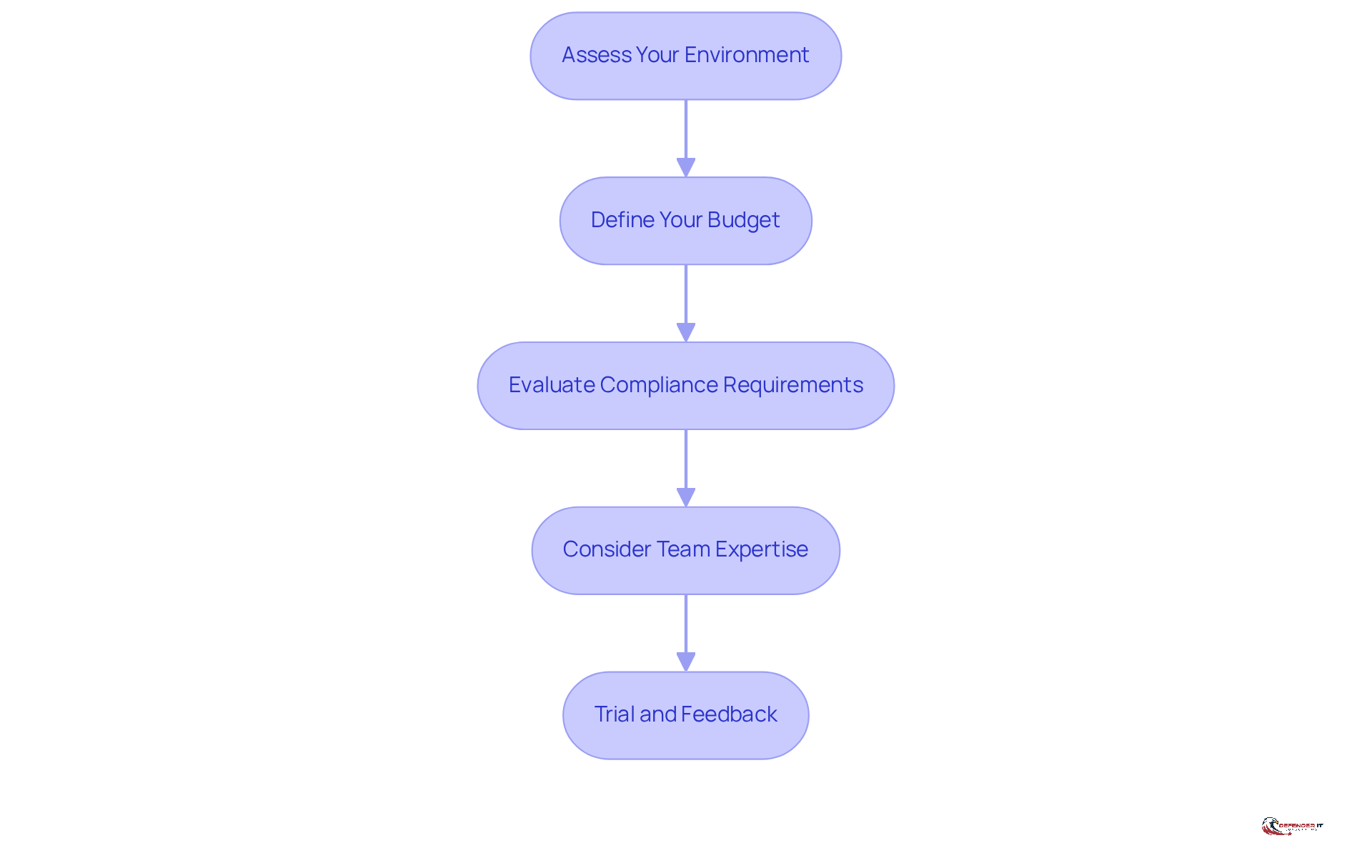
Choosing the Right Vulnerability Scanner for Your Business Needs
Selecting the best vulnerability scanner 2023 is crucial for safeguarding your organization’s digital assets against potential threats. Several key considerations should guide this selection process:
- Assess Your Environment: Understand the specific assets and environments that need protection, including networks, applications, and databases.
- Define Your Budget: Determine how much your organization can allocate for vulnerability management resources, considering both initial costs and ongoing expenses.
- Evaluate Compliance Requirements: Identify any regulatory requirements that may dictate the need for specific scanning capabilities or reporting features.
- Consider Team Expertise: Assess the skill level of your team to ensure they can effectively utilize the selected device. A more complex tool may require additional training.
- Trial and Feedback: If possible, conduct trials of shortlisted scanners to gather feedback from users and assess their effectiveness in real-world scenarios.
Ultimately, selecting the best vulnerability scanner 2023 can significantly bolster your organization’s cybersecurity defenses.
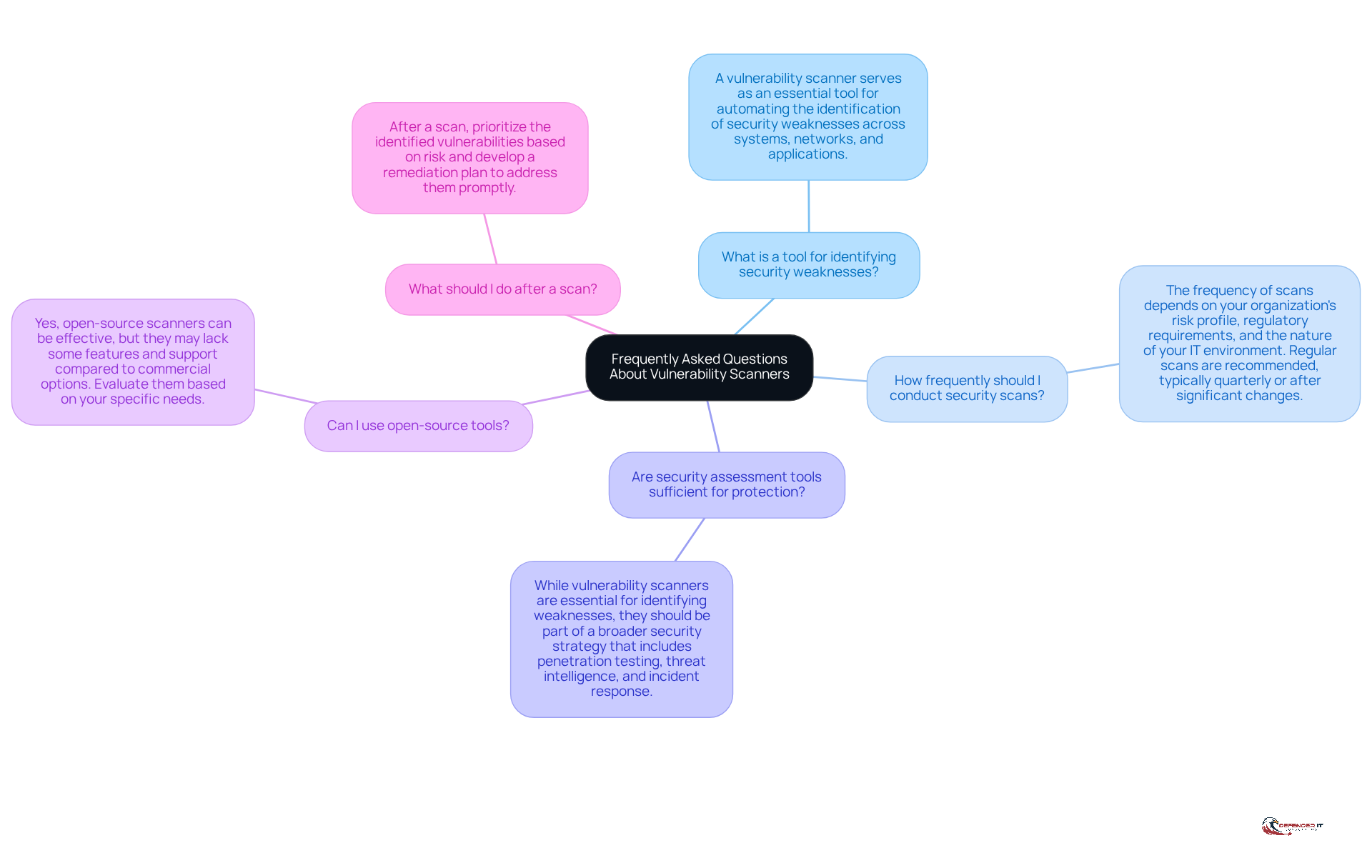
Frequently Asked Questions About Vulnerability Scanners
Understanding the role of the best vulnerability scanner 2023 is crucial for maintaining robust cybersecurity measures in any organization.
Here are some common questions regarding vulnerability scanners:
- What is a tool for identifying security weaknesses?
A vulnerability scanner serves as an essential tool for automating the identification of security weaknesses across systems, networks, and applications. - How frequently should I conduct security scans?
The frequency of scans depends on your organization’s risk profile, regulatory requirements, and the nature of your IT environment. Regular scans are recommended, typically quarterly or after significant changes. - Are security assessment tools sufficient for protection?
While vulnerability scanners are essential for identifying weaknesses, they should be part of a broader security strategy that includes penetration testing, threat intelligence, and incident response. - Can I use open-source tools?
Yes, open-source scanners can be effective, but they may lack some features and support compared to commercial options. Evaluate them based on your specific needs. - What should I do after a scan?
After a scan, prioritize the identified vulnerabilities based on risk and develop a remediation plan to address them promptly.
Integrating the best vulnerability scanner 2023 into your security strategy is vital for safeguarding your organization against potential threats.
Conclusion
In an era where cyber threats are increasingly sophisticated, selecting the optimal vulnerability scanner is crucial for organizations. The right tool not only identifies weaknesses but also empowers businesses to implement effective remediation strategies, thereby safeguarding their digital assets against an ever-evolving threat landscape.
This article has emphasized critical features essential for evaluating vulnerability scanners, including:
- Scanning capabilities
- Ease of use
- Reporting and analytics
- Integration
- Customization
- Ongoing support
A comparative analysis of leading tools like Nessus, Qualys, Rapid7 InsightVM, OpenVAS, and Burp Suite has highlighted their unique strengths and weaknesses, enabling organizations to make informed decisions tailored to their specific security needs.
Ultimately, the significance of incorporating the best vulnerability scanner cannot be overstated. By prioritizing the right tools and understanding their functionalities, organizations can enhance their security posture and proactively address vulnerabilities. By carefully assessing your needs, budget, and team expertise, you can build a stronger cybersecurity strategy, ensuring resilience against potential threats in an increasingly complex digital environment. Failing to choose the right vulnerability scanner could leave organizations exposed to significant risks in their cybersecurity defenses.
Frequently Asked Questions
What are the key features to consider when selecting a vulnerability scanner?
Key features to consider include scanning capabilities, ease of use, reporting and analytics, integration with existing tools, customization options, and support and updates.
Why are scanning capabilities important in a vulnerability scanner?
Scanning capabilities are important because they allow the scanner to conduct thorough scans across diverse environments, including networks, web applications, and databases.
How does ease of use impact the effectiveness of a vulnerability scanner?
A user-friendly interface is crucial for effective deployment and management, especially for teams with varying levels of expertise, ensuring that all users can operate the scanner effectively.
What role do reporting and analytics play in vulnerability management?
Detailed reporting features provide actionable insights and prioritize vulnerabilities based on risk, which is essential for effective remediation and addressing security issues.
Why is integration with current security tools important for a vulnerability scanner?
Integration with existing security tools and workflows improves the scanner’s utility and effectiveness, allowing for a more cohesive security strategy.
How does customization benefit organizations using vulnerability scanners?
Customizable scanning profiles enable organizations to tailor scans to their specific environments and compliance requirements, enhancing the scanner’s relevance and effectiveness.
What is the significance of support and updates for vulnerability scanners?
Regular updates and responsive customer assistance are essential for maintaining the scanner’s effectiveness against evolving threats, ensuring ongoing protection for the organization.
What risks do organizations face if they do not prioritize these features in vulnerability scanners?
Without these essential features, organizations risk leaving vulnerabilities unaddressed, potentially exposing them to significant cyber threats.
List of Sources
- Key Features to Consider in Vulnerability Scanners
- Top 8 Commercial Vulnerability Scanners of 2023 (https://emagined.com/blog/top-8-vulnerability-scanners-of-2023)
- 12 popular vulnerability scanning tools in 2025 | Red Canary (https://redcanary.com/cybersecurity-101/security-operations/vulnerability-scanning-tools)
- Top 5 Vulnerability Scanners for Enterprises in 2023 (https://secpod.com/blog/top-5-vulnerability-scanners-for-enterprises-in-2023)
- Comparison of Top Vulnerability Scanners: Strengths and Weaknesses
- Tenable Fixes Three High-Severity Flaws in Nessus (https://infosecurity-magazine.com/news/tenable-fixes-flaws-nessus)
- Top 8 Commercial Vulnerability Scanners of 2023 (https://emagined.com/blog/top-8-vulnerability-scanners-of-2023)
- Choosing the Right Vulnerability Scanner for Your Business Needs
- How to Choose the Best Vulnerability Scanning Tool for Your Business (https://cio.com/article/250492/how-to-choose-the-best-vulnerability-scanning-tool-for-your-business.html)
- 5 Vulnerability Management Tools for Your Business (https://legitsecurity.com/aspm-knowledge-base/top-vulnerability-management-tools)
- Best 10 Vulnerability Management Tools in 2026 (https://tuxcare.com/blog/vulnerability-management-tool)
- 9 Vulnerability Management Tools in 2026 | SentinelOne (https://sentinelone.com/cybersecurity-101/cybersecurity/8-vulnerability-management-tools)
- vulnerability management — Latest News, Reports & Analysis | The Hacker News (https://thehackernews.com/search/label/vulnerability management)
- Frequently Asked Questions About Vulnerability Scanners
- Best Practices for Vulnerability Scanning (https://kirkpatrickprice.com/blog/best-practices-vulnerability-scanning)
- Vulnerability Statistics 2026: Key Trends & Data | Indusface (https://indusface.com/blog/key-vulnerability-statistics)
- How Often Should You Perform Vulnerability Scans? (https://secureideas.com/knowledge/how-often-should-vulnerability-assesments-run)
- How Often Should You Perform Vulnerability Scans? (https://secure.com/blog/cybersecurity/how-often-should-you-perform-vulnerability-scans)
- Vulnerability Scanning: How Often Should I Scan? (https://thehackernews.com/2023/10/vulnerability-scanning-how-often-should.html)