Introduction
The Cybersecurity Maturity Model Certification (CMMC) serves as a vital framework for organizations engaging with the Department of Defense, providing a structured approach to the protection of sensitive information.
As compliance becomes increasingly critical for securing federal contracts, it is essential for contractors to grasp the complexities of the CMMC levels and their associated practices.
Navigating the path to compliance presents numerous challenges; thus, organizations must effectively manage these complexities to ensure not only adherence but also the enhancement of their cybersecurity posture.
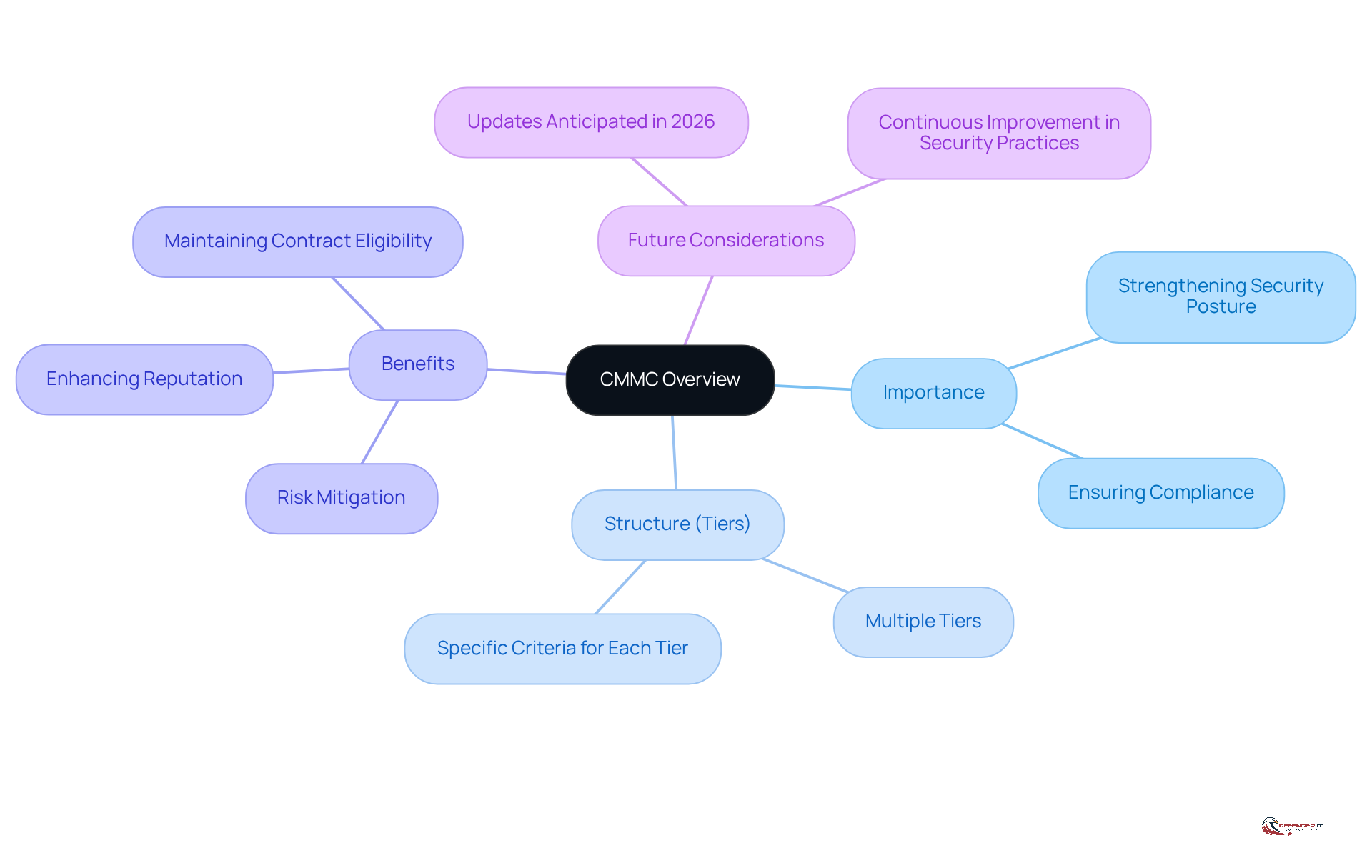
Understand CMMC: Importance and Overview
The Cybersecurity Maturity Model Certification (CMMC) is a vital framework established by the Department of Defense (DoD) aimed at strengthening the security posture of organizations handling Federal Contract Information (FCI) and Controlled Unclassified Information (CUI). This framework ensures that contractors implement robust security protocols, thereby protecting sensitive information from a range of cyber threats.
Organized into multiple tiers, the CMMC outlines specific criteria that entities must fulfill to qualify for federal contracts. A thorough understanding of these levels is essential for any organization looking to engage with the DoD. The framework not only emphasizes compliance but also fosters a culture of continuous improvement in security practices.
Adhering to these standards allows companies to significantly mitigate the risk of data breaches, enhance their reputation, and maintain eligibility for lucrative government contracts. As the DoD continues to refine its digital security requirements, including anticipated updates in 2026, organizations must remain vigilant and proactive in their compliance efforts. This overview serves as a critical first step in , underscoring its essential role in safeguarding sensitive information and ensuring operational resilience.
Identify CMMC Levels: Requirements and Practices
CMMC is organized into three primary levels, each representing a distinct degree of cybersecurity maturity:
- Level 1 (Foundational): This level emphasizes basic cyber hygiene practices essential for protecting Federal Contract Information (FCI). Organizations must implement 17 specific practices, including access control and user identification. Compliance is achieved through self-assessment, requiring an annual affirmation in the Supplier Performance Risk System (SPRS).
- Level 2 (Advanced): Building on foundational practices, Level 2 introduces additional requirements aligned with NIST SP 800-171, necessitating 110 security practices. Organizations must demonstrate enhanced security measures, including incident response and risk management strategies. Compliance at this level involves a more rigorous assessment process, often requiring third-party validation for prioritized acquisitions every three years.
- Level 3 (Expert): The highest level requires entities to implement advanced security measures to protect Controlled Unclassified Information (CUI). This includes continuous monitoring and proactive threat detection. Achieving compliance at Level 3 necessitates third-party assessments conducted by the Defense Industrial Base Cybersecurity Assessment Center (DIBCAC) every three years.
Understanding these levels enables organizations to effectively, ensuring they meet the necessary requirements for their specific contracts. As of late 2026, the Department of Defense is anticipated to broaden cybersecurity clauses in solicitations, progressing beyond self-assessments to necessitate third-party validated certifications for higher-risk contracts.
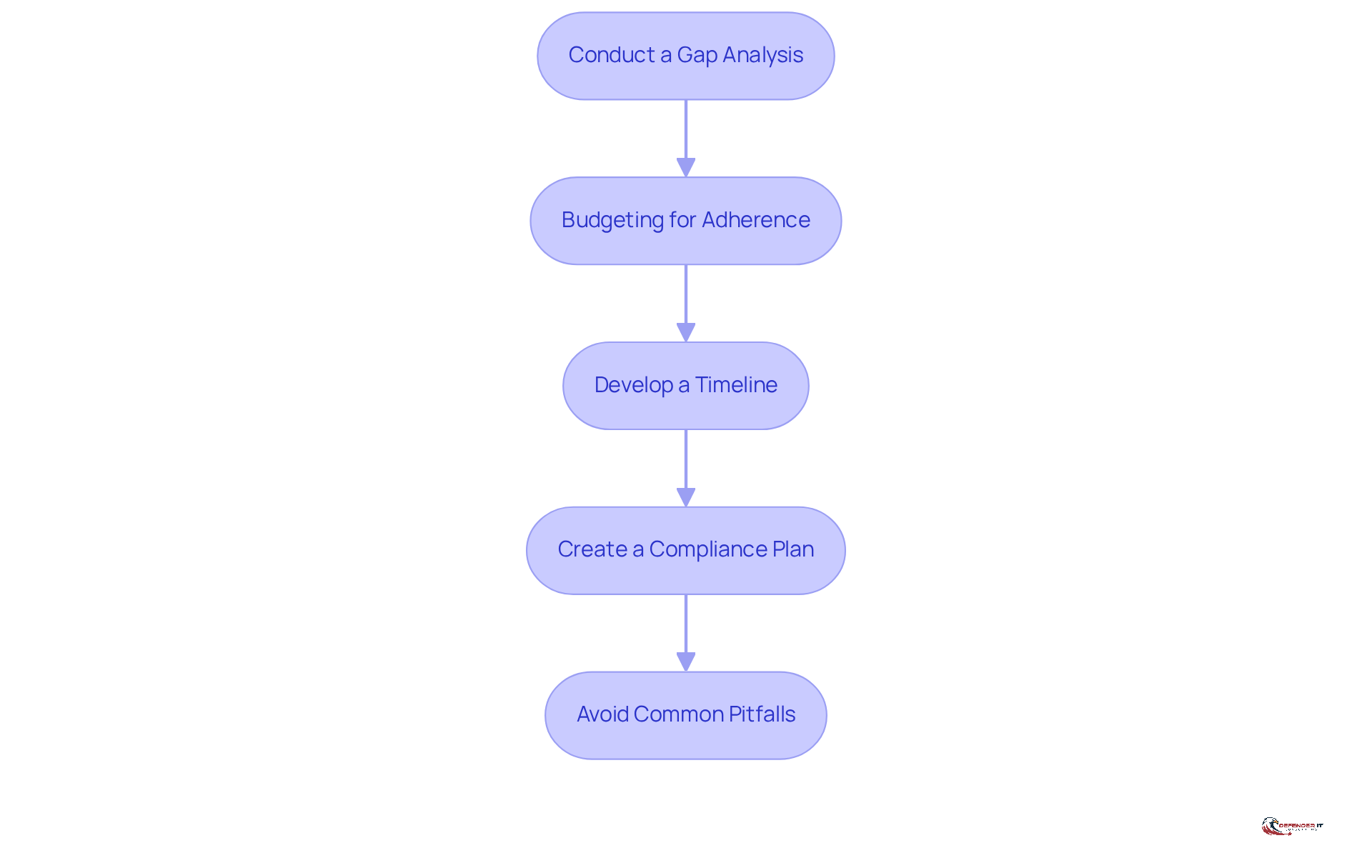
Plan for Compliance: Cost, Timeline, and Strategy
Planning for CMMC compliance involves several key steps:
- Conduct a Gap Analysis: Assess your current cybersecurity posture against CMMC requirements to identify areas needing improvement. This analysis will help prioritize actions and allocate resources effectively, revealing vulnerabilities that could be exploited by hackers.
- Budgeting for Adherence: Organizations should prepare for potential costs associated with achieving compliance. Estimates suggest that adherence efforts can range from approximately $63,000 to over $200,000 for Level 2 compliance, depending on the certification level and the size of the organization. Small enterprises may find expenses for Level 2 compliance between $100,000 and $200,000, which is minimal compared to the potential loss of lucrative DoD contracts without certification.
- Develop a Timeline: Establish a realistic schedule for achieving compliance. The CMMC certification process can take up to 12 months, and organizations should plan accordingly, especially considering that C3PAOs may have backlogs of six to twelve months. Early preparation can help avoid rushed remediation and increased costs.
- Create a Compliance Plan: Develop a comprehensive strategy that outlines the steps needed to achieve conformity, including training, technology upgrades, and policy development. This strategy should emphasize the importance of through tangible proof, rather than merely possessing policies on paper. Regularly revisiting this strategy will assist in adapting to evolving threats and regulatory changes, ensuring that entities maintain a robust security posture.
- Avoid Common Pitfalls: Be aware of common traps, such as engaging C3PAOs too early or misjudging the FCI and CUI footprint, which can lead to unnecessary complications in the compliance process.
By following these steps, companies can establish a systematic approach to meeting regulatory standards, ensuring they are adequately prepared for future requirements and minimizing the risk of unforeseen costs.
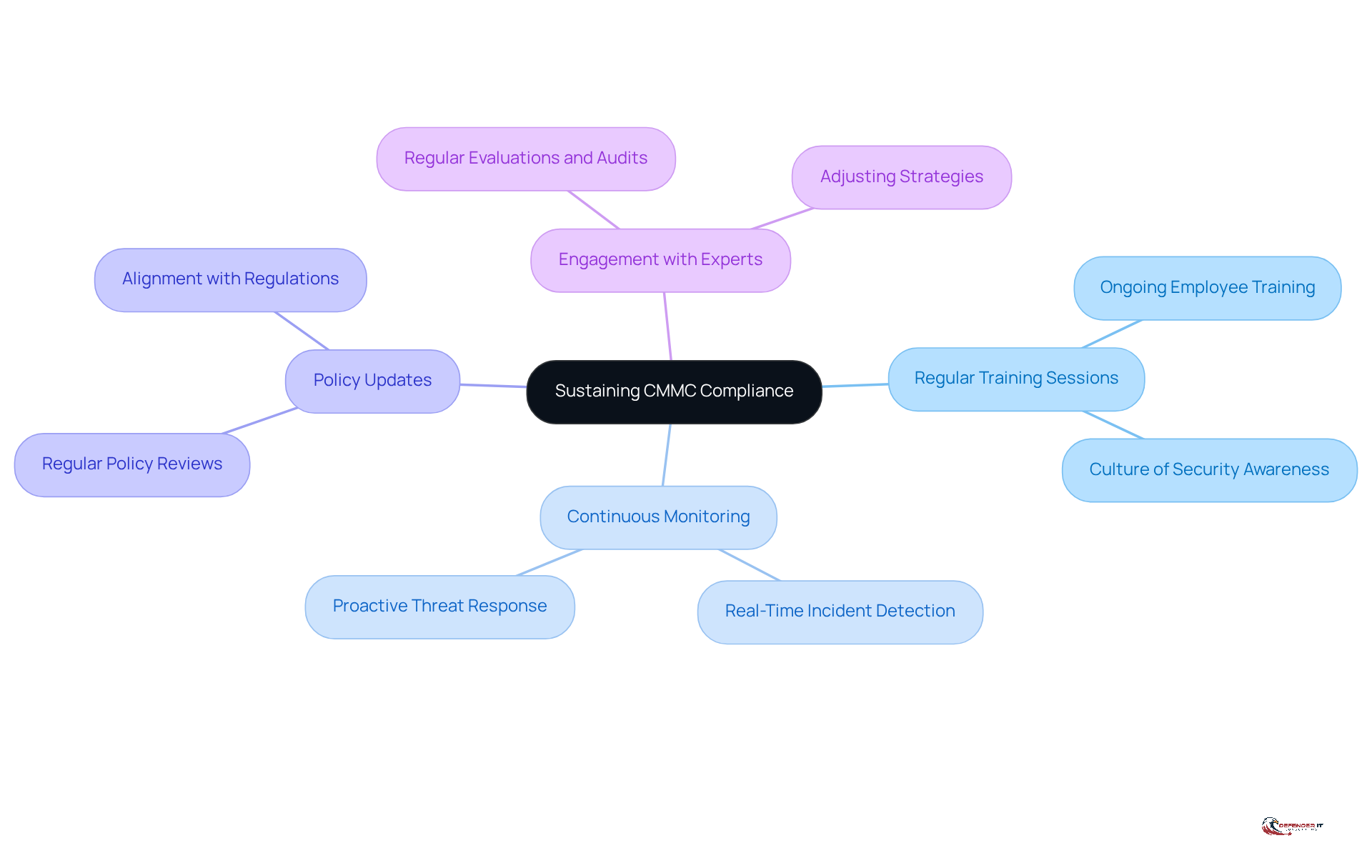
Sustain Compliance: Ongoing Support and Training
Sustaining CMMC compliance requires a strategic approach that incorporates several essential practices:
- Regular Training Sessions: Ongoing training for employees is vital to keep them informed about evolving threats, phishing tactics, and best practices for managing sensitive data. This continuous education fosters a culture of security awareness throughout the organization.
- Continuous Monitoring: Implementing continuous monitoring solutions is crucial for detecting and responding to potential security incidents in real-time. This proactive approach enables organizations to stay ahead of emerging threats, significantly .
- Policy Updates: Regular reviews and updates of security policies are necessary to align with changes in regulations, technology, and the threat landscape. Keeping policies current is fundamental to maintaining compliance and ensuring effective risk management.
- Engagement with Experts: Collaborating with security specialists for regular evaluations and audits provides organizations with valuable insights into areas needing improvement. This expert involvement aids in adjusting strategies to effectively meet evolving regulatory requirements.
By prioritizing ongoing support and training, organizations can not only achieve compliance but also strengthen their cybersecurity defenses, thereby protecting their operations and reputation in an increasingly complex digital landscape.
Conclusion
Understanding and adhering to the Cybersecurity Maturity Model Certification (CMMC) is essential for organizations aiming to engage with the Department of Defense (DoD). This framework establishes a structured approach to cybersecurity and underscores the necessity of continuous improvement in safeguarding sensitive information. As threats evolve, so must the strategies employed to protect data, making compliance an ongoing priority.
The article explores the various levels of CMMC, detailing the specific requirements and practices necessary for compliance. Organizations must tailor their cybersecurity strategies to meet the distinct criteria set forth by the DoD, ranging from the foundational practices of Level 1 to the advanced measures of Level 3. Furthermore, planning for compliance requires careful budgeting, establishing timelines, and developing comprehensive strategies that consider potential pitfalls.
Ultimately, the significance of CMMC compliance transcends mere certification; it fosters a culture of security awareness and resilience. By investing in ongoing training, continuous monitoring, and expert engagement, organizations can achieve compliance while enhancing their overall cybersecurity posture. Embracing these best practices ensures that entities remain competitive and secure in an increasingly complex digital landscape, paving the way for success in securing federal contracts and protecting vital information.
Frequently Asked Questions
What is the Cybersecurity Maturity Model Certification (CMMC)?
The CMMC is a framework established by the Department of Defense (DoD) aimed at enhancing the security posture of organizations that handle Federal Contract Information (FCI) and Controlled Unclassified Information (CUI).
Why is CMMC important for organizations?
CMMC is important because it ensures that contractors implement robust security protocols to protect sensitive information from cyber threats, thereby mitigating the risk of data breaches and enhancing their reputation.
How is the CMMC organized?
The CMMC is organized into multiple tiers, each outlining specific criteria that organizations must fulfill to qualify for federal contracts.
What are the benefits of adhering to CMMC standards?
Adhering to CMMC standards allows companies to significantly reduce the risk of data breaches, enhance their reputation, and maintain eligibility for lucrative government contracts.
What is the significance of continuous improvement in security practices within the CMMC framework?
The CMMC framework fosters a culture of continuous improvement in security practices, which is essential for organizations looking to engage with the DoD and navigate compliance complexities.
What should organizations be aware of regarding future updates to CMMC?
Organizations should remain vigilant and proactive in their compliance efforts as the DoD continues to refine its digital security requirements, with anticipated updates expected in 2026.