Introduction
Understanding the complexities of the Cybersecurity Maturity Model Certification (CMMC) is essential for organizations aiming to secure contracts within the defense sector. The evolving landscape of cybersecurity compliance presents businesses with a significant opportunity to enhance their security posture and streamline their preparation for certification. However, a concerning reality persists: only a small fraction of contractors are fully prepared for audits. This raises a critical question: what key strategies can organizations implement to ensure successful compliance and effectively navigate the intricate requirements of CMMC?
Understand CMMC Compliance Requirements
The is a framework established by the Department of Defense aimed at enhancing the posture of organizations handling Controlled Unclassified Information (CUI). Understanding the necessitates familiarity with its five maturity levels, each defined by specific practices and processes that must be adopted. Organizations are required to assess their existing security measures against these levels to pinpoint .
Key components of the CMMC include:
- Level 1: Basic , which encompass access control and identification.
- Level 2: Intermediate cyber hygiene, mandating documented policies and procedures.
- Level 3: Good cyber hygiene, concentrating on the protection of CUI through more advanced practices.
- Level 4: Proactive measures aimed at detecting and responding to threats.
- Level 5: Advanced security practices designed to optimize and safeguard sensitive information.
By comprehending these levels, organizations can enhance their preparedness for compliance and strengthen their overall .
Implement Effective Preparation Strategies for Certification
To effectively prepare for , organizations should adopt the following strategies:
- Conduct a : Evaluate current against CMMC requirements to pinpoint deficiencies. This step is crucial, as a well-executed gap analysis helps prioritize fixes and avoid surprises during assessments. As highlighted by the Department of Defense, “Cybersecurity adherence is now a gating factor for DoD contract eligibility-not a nice-to-have.”
- Develop a : Create a comprehensive plan that outlines the necessary steps to achieve adherence, including timelines and responsible parties. A successful adherence plan is essential for guiding entities through the complexities of regulatory criteria. Notably, only a minor fraction of organizations currently possess roadmaps for the 2026 compliance framework, underscoring the need for proactive measures.
- Implement : Establish technical controls such as access management, encryption, and . These controls are vital for fulfilling the 110 requirements detailed in , which form the foundation for CMMC Level 2 standards.
- Document Policies and Procedures: Ensure that all security practices are thoroughly documented and accessible to relevant personnel. Inconsistencies in documentation can lead to assessment delays, making accurate and aligned documentation critical.
- Engage in : Provide ongoing training for employees to ensure they understand their roles in upholding regulations. Consistent training fosters a culture of security awareness and readiness, which is crucial as entities navigate the evolving landscape of cybersecurity compliance.
By following these strategies, organizations can streamline their preparation efforts and significantly enhance their chances of successful certification. Furthermore, it is essential to acknowledge that only 1% of Defense Industrial Base contractors are fully prepared for audits, emphasizing the urgent need for the proposed strategies.
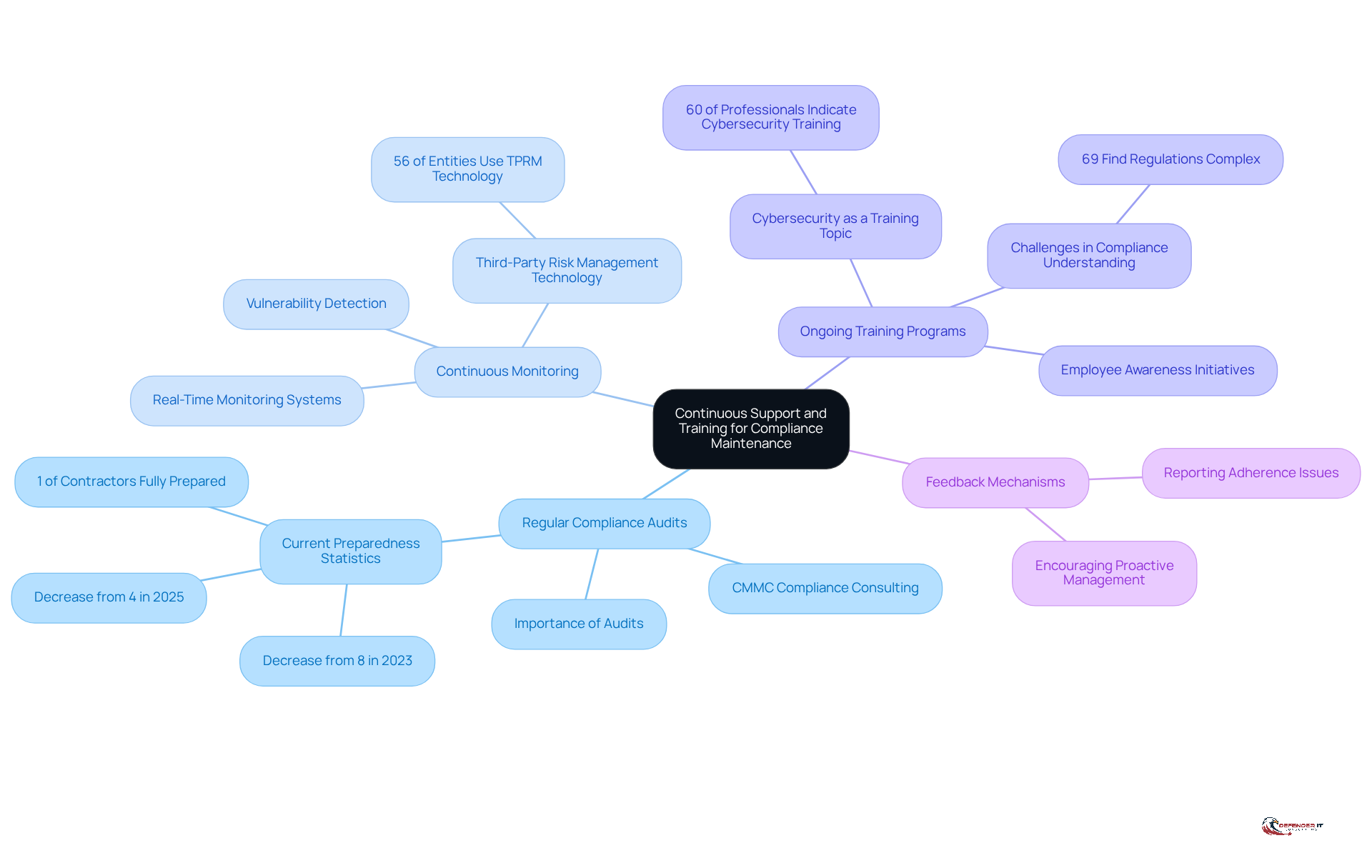
Establish Continuous Support and Training for Compliance Maintenance
To uphold compliance effectively, organizations must prioritize . Key practices include:
- , which can be enhanced through , are essential for assessing adherence to CMMC requirements and identifying areas for improvement. With only 1% of contractors -a decrease from 8% in 2023 and 4% in 2025-regular evaluations can significantly enhance readiness.
- Continuous Monitoring: Implementing is crucial for detecting potential vulnerabilities. As entities prepare for the 2026 regulatory deadline, these systems can aid in identifying misconfigurations and assist with prompt remediation. Notably, 56% of entities now employ , underscoring the increasing trend and significance of such systems in regulatory efforts.
- : Creating thorough training initiatives ensures that employees are well-informed about the latest online security threats and regulatory requirements. With 60% of risk and regulatory professionals indicating , organizations can foster a culture of awareness and preparedness. Furthermore, 69% of entities find regulations too intricate or abundant, highlighting the challenges faced in maintaining adherence and emphasizing the necessity for continual training and support.
- Feedback Mechanisms: Establishing channels for employees to report adherence issues or suggest enhancements encourages a proactive approach to management.
By promoting a and incorporating these practices, organizations can bolster their resilience against cyber threats while ensuring ongoing adherence to standards through [CMMC compliance consulting](https://defenderit.consulting).
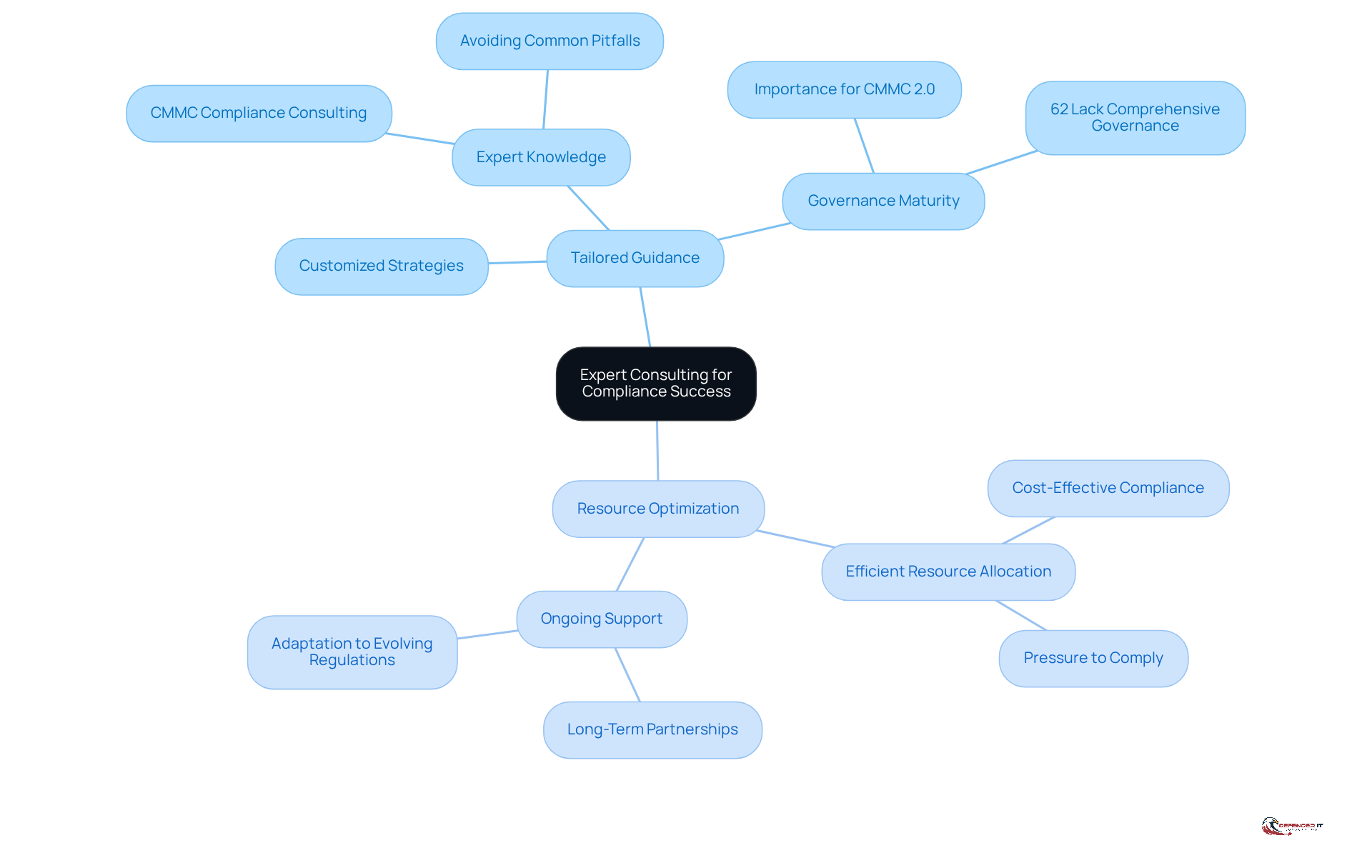
Leverage Expert Consulting for Enhanced Compliance Success
Collaborating with skilled advisors is essential for organizations aiming to manage security regulations effectively. Such partnerships offer several key benefits:
- Tailored Guidance: Consultants deliver customized strategies that cater to the unique needs and challenges of each organization, significantly increasing the chances of . Expert knowledge gained through allows organizations to leverage the expertise of advisors in cybersecurity maturity model requirements and best practices, helping them avoid common pitfalls that could jeopardize their compliance efforts. Notably, the success of than on technical sophistication, highlighting the necessity of a robust governance framework.
- Resource Optimization: Consultants facilitate the efficient allocation of resources, ensuring that regulatory initiatives are both effective and cost-efficient. This is particularly crucial as organizations face . Ongoing support through cmmc compliance consulting establishes a , ensuring continuous assistance that allows businesses to adapt to evolving regulations and maintain compliance over time.
Statistics reveal that 62% of CMMC respondents are from North America, underscoring the widespread use of consultants in this region. Additionally, mid-market firms that prioritize governance and engage with consultants have achieved a 59% success rate in meeting top-tier encryption standards. By engaging cmmc compliance consulting services, organizations can enhance their and build a strong , positioning themselves favorably in the competitive landscape of defense contracting. It is vital to acknowledge that misrepresenting compliance can result in severe repercussions, emphasizing the high stakes associated with CMMC compliance.
Conclusion
Achieving CMMC compliance is essential for organizations managing Controlled Unclassified Information. The Cybersecurity Maturity Model Certification (CMMC) framework offers a structured approach across five maturity levels, serving as a roadmap for enhancing cybersecurity practices. By understanding the nuances of these levels and their specific requirements, organizations can significantly improve their security posture and readiness for compliance.
This article outlines key strategies for effective CMMC certification preparation. These include:
- Conducting thorough gap analyses
- Developing regulatory roadmaps
- Implementing necessary controls
- Documenting policies
- Fostering ongoing employee training
Such practices not only streamline the preparation process but also underscore the importance of a proactive approach to compliance, particularly in light of the fact that only 1% of contractors are fully prepared for audits. Continuous support and training are vital for maintaining compliance, ensuring organizations remain vigilant against evolving threats and regulatory challenges.
Leveraging expert consulting can further enhance an organization’s compliance journey. Tailored guidance from experienced consultants aids in navigating the complexities of CMMC requirements, optimizing resource allocation, and establishing a robust governance framework. As the stakes associated with compliance increase, engaging in CMMC compliance consulting becomes a strategic necessity, enabling organizations to thrive in the competitive landscape of defense contracting. Embracing these strategies transcends mere regulatory compliance; it fosters a culture of security and resilience that will benefit organizations well into the future.
Frequently Asked Questions
What is the Cybersecurity Maturity Model Certification (CMMC)?
The CMMC is a framework established by the Department of Defense to enhance the information security posture of organizations that handle Controlled Unclassified Information (CUI).
How many maturity levels are there in the CMMC, and what do they represent?
There are five maturity levels in the CMMC, each defined by specific practices and processes that organizations must adopt to improve their cybersecurity measures.
What are the key components of Level 1 in the CMMC?
Level 1 focuses on basic cyber hygiene practices, which include access control and identification.
What requirements are set for Level 2 in the CMMC?
Level 2 requires intermediate cyber hygiene, which mandates that organizations have documented policies and procedures in place.
What does Level 3 of the CMMC emphasize?
Level 3 emphasizes good cyber hygiene, concentrating on the protection of Controlled Unclassified Information (CUI) through more advanced practices.
What are the objectives of Level 4 in the CMMC?
Level 4 involves proactive measures aimed at detecting and responding to cybersecurity threats.
What is the focus of Level 5 in the CMMC?
Level 5 focuses on advanced security practices designed to optimize and safeguard sensitive information.
Why is it important for organizations to understand CMMC requirements?
Understanding CMMC requirements helps organizations enhance their preparedness for compliance and strengthens their overall security posture by identifying gaps and opportunities for improvement.

. Follow the arrows to see the recommended order of implementation, ensuring a structured approach to achieving compliance.](https://images.tely.ai/telyai/tzplzrqv-each-box-represents-a-key-strategy-for-preparing-for-cmmc-certification-follow-the-arrows-to-see-the-recommended-order-of-implementation-ensuring-a-structured-approach-to-achieving-compliance.webp)