Introduction
Cyber threats present significant challenges for the manufacturing sector, particularly at the intersection of operational and information technology. Engaging a skilled penetration testing company is a critical strategy for identifying vulnerabilities that jeopardize operational integrity and regulatory compliance. Organizations must carefully evaluate potential partners to ensure they effectively safeguard assets and enhance cybersecurity posture.
Understand the Fundamentals of Penetration Testing
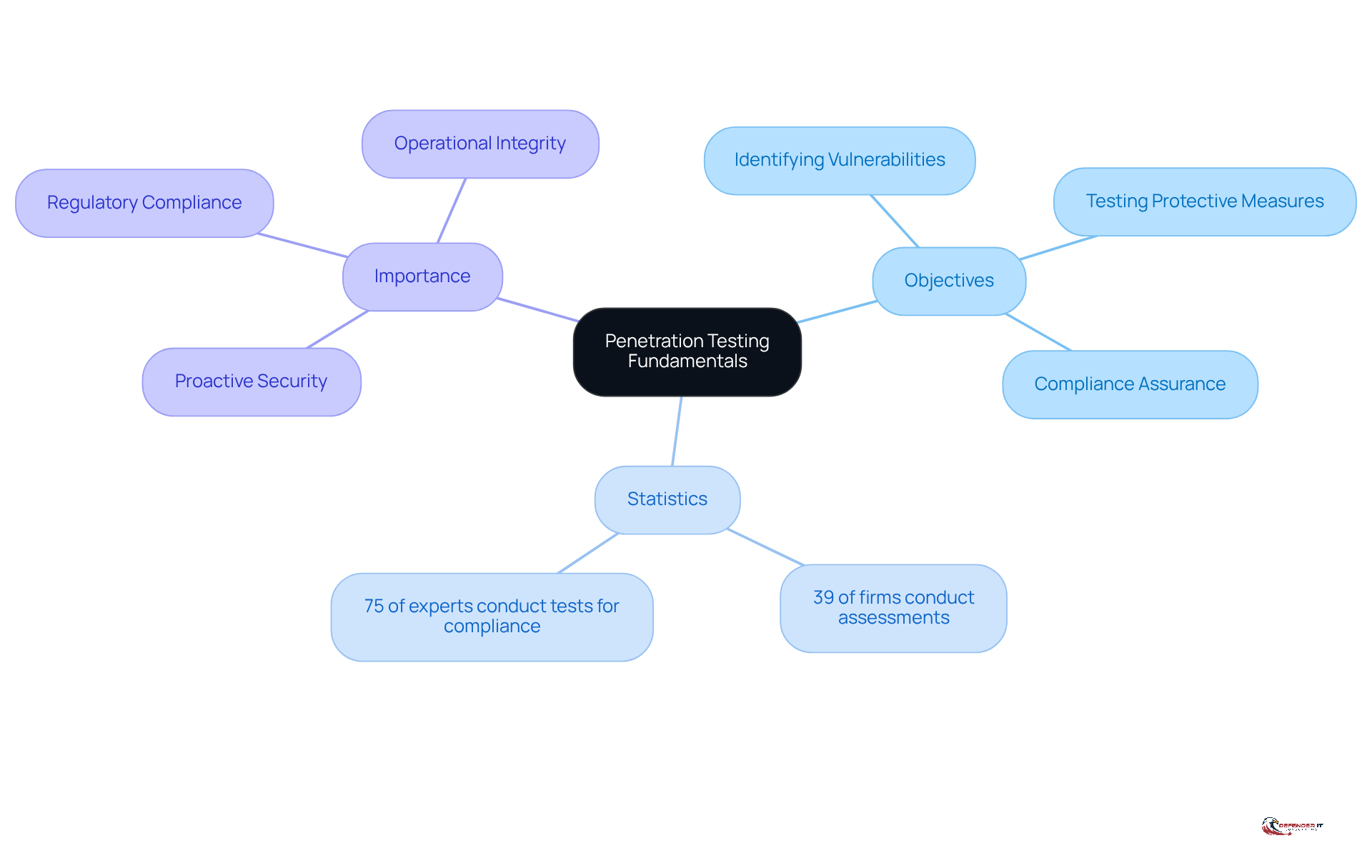
In an era where cyber threats are increasingly sophisticated, it is vital for manufacturing operations to understand the importance of a pen testing company in conducting penetration assessments. Penetration assessment, or pen testing, simulates cyber attacks on systems, networks, or web applications to identify vulnerabilities that malicious actors might exploit. In the manufacturing sector, where operational technology (OT) and information technology (IT) intersect, many organizations struggle to navigate the complexities of OT and IT integration. A solid understanding of pen assessment fundamentals is crucial. This understanding enables organizations to evaluate their security posture and comply with industry regulations. The primary objectives of penetration testing include:
- Identifying Vulnerabilities: Proactively discovering weaknesses in systems before they can be exploited.
- Testing Protective Measures: Evaluating the effectiveness of current safeguards to defend against potential threats.
- Compliance Assurance: Verifying adherence to regulatory requirements, which is especially vital in the manufacturing industry.
About 39% of firms in manufacturing carry out vulnerability assessments at least once or twice annually, indicating an increasing awareness of the necessity for strong protective measures. Additionally, 75% of security experts conduct security tests to meet compliance requirements, highlighting the essential role of these evaluations in regulatory adherence. Without proper penetration testing conducted by a pen testing company, organizations may face significant risks that threaten their operational integrity. Understanding these essentials helps organizations see why engaging a skilled security assessment provider is crucial. As cybersecurity expert [Expert Name] states, “Identifying vulnerabilities in operational technology is essential for maintaining a secure manufacturing environment.” Without a proactive approach to identifying vulnerabilities, organizations risk not only compliance failures but also potential operational disruptions.
Define Your Pen Testing Objectives Clearly
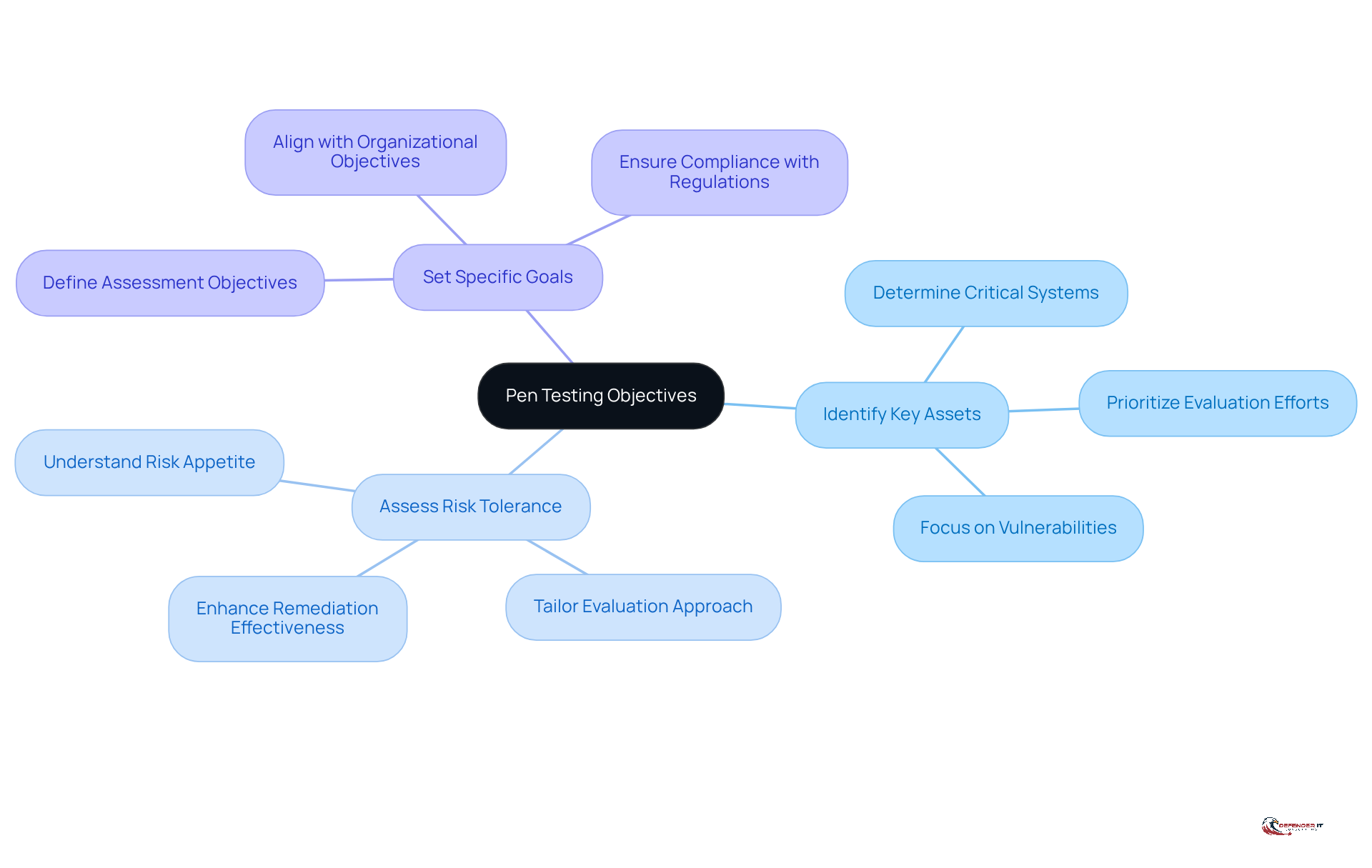
Without clear goals, organizations risk wasting resources on irrelevant assessments during penetration evaluations. Here are key steps to consider:
- Identify Key Assets: Determine which systems, applications, or data are critical to your operations. This helps prioritize evaluation efforts on critical systems and data essential to your operations. For instance, organizations that focus on their key assets often find they can allocate resources more effectively and concentrate on vulnerabilities that pose the greatest risk.
- Assess Risk Tolerance: Understand your organization’s risk appetite to tailor the evaluation approach accordingly. This evaluation indicates how aggressive or conservative your examination strategy should be. As noted in the case study “Prioritizing Remediation Based on Real Exploitability,” understanding risk tolerance can significantly enhance the effectiveness of remediation efforts.
- Set Specific Goals: Clearly define what you aim to accomplish through security assessments. This could include identifying vulnerabilities, evaluating incident response capabilities, or ensuring compliance with industry regulations. Cybersecurity specialist Josh Schmidt emphasizes that aligning vulnerability assessments with organizational objectives is essential for enhancing their effectiveness and ensuring that security measures are robust and responsive to real-world threats.
Setting these goals allows organizations to align their penetration assessments with their cybersecurity strategy and risk management framework, especially when collaborating with a pen testing company. However, organizations often face challenges in establishing clear scopes and objectives, which can hinder the efficiency of the evaluation process. Additionally, compliance requirements significantly shape these objectives, particularly for organizations operating in regulated industries. By addressing these factors, organizations can enhance their vulnerability assessments and fortify their defenses against potential threats.
Evaluate Expertise and Methodologies of Providers
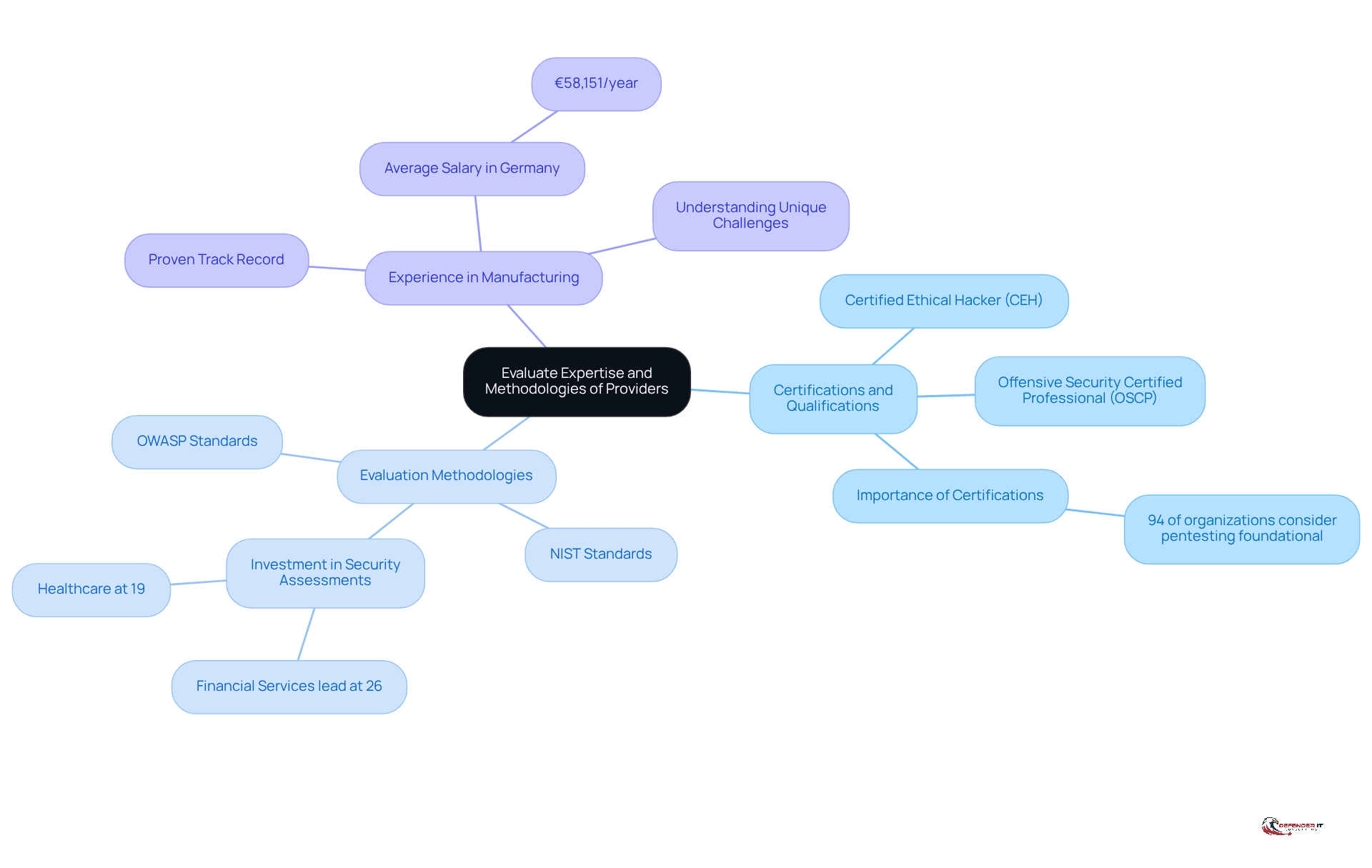
In an era where cyber threats are increasingly sophisticated, selecting the right pen testing company is critical for safeguarding organizational assets. Here are key factors to consider:
- Certifications and Qualifications: Look for providers with recognized certifications such as Certified Ethical Hacker (CEH) or Offensive Security Certified Professional (OSCP). These credentials demonstrate a commitment to industry standards and best practices, which is crucial in a field where 94% of organizations consider a pen testing company to be foundational for modern security programs.
- Evaluation Methodologies: Ensure the provider adheres to established methodologies, such as OWASP or NIST standards, which direct the assessment process. According to a 2025 report by the SANS Institute, various sectors are increasingly investing in security assessments, with financial services leading at 26% due to high-value data and regulatory requirements.
- Experience in Manufacturing: Choose vendors with a proven track record in the manufacturing sector, as they will better understand the unique challenges and regulatory requirements. The typical salary for security testers in Germany is €58,151/year, reflecting the investment companies should consider when choosing a provider.
Failing to conduct thorough evaluations may expose organizations to significant security vulnerabilities and compliance risks.
Assess Reporting and Communication Practices
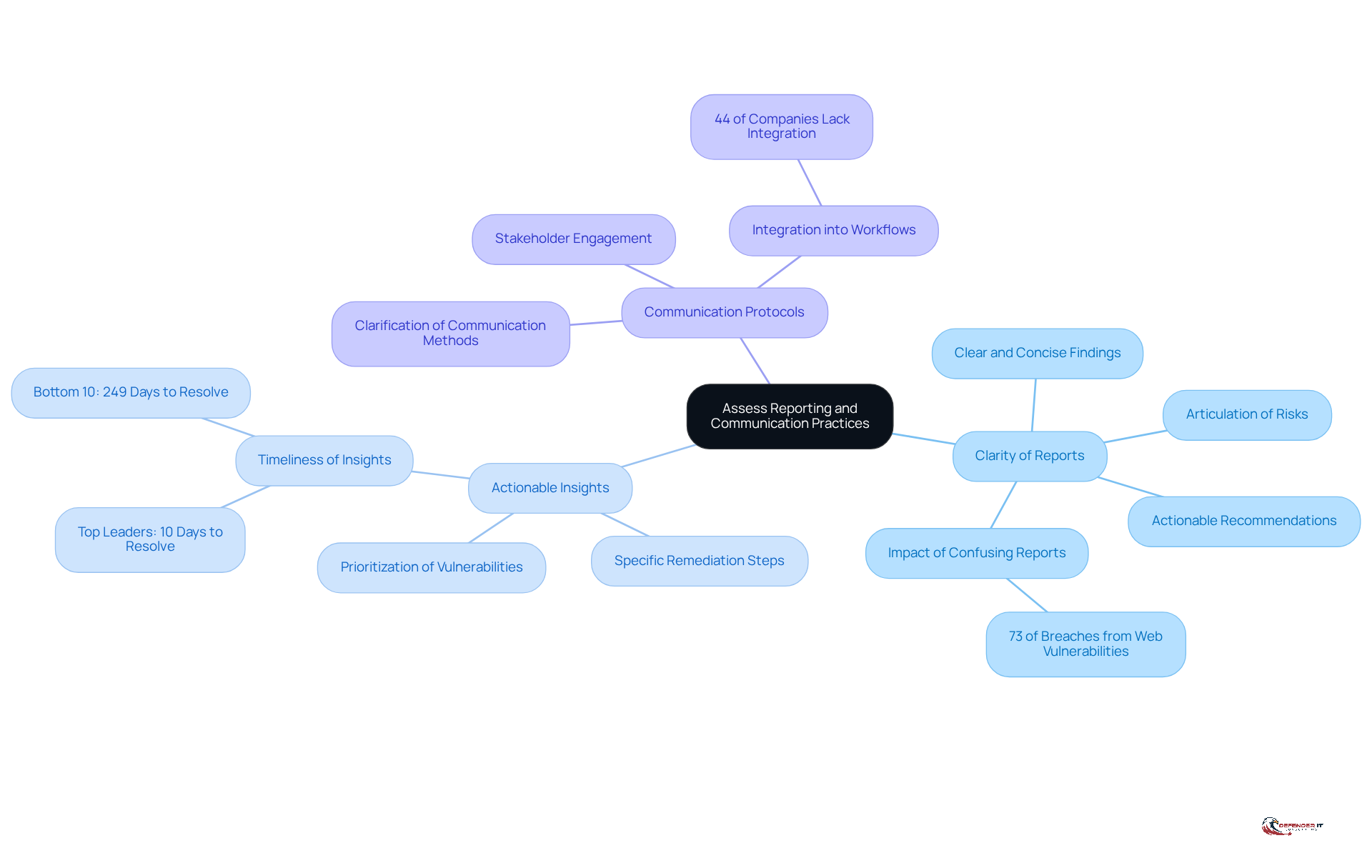
Effective reporting and communication are pivotal in enhancing an organization’s cybersecurity posture. Organizations should evaluate the following aspects to improve their security assessment process:
- Clarity of Reports: Providers must deliver clear and concise reports that articulate findings, associated risks, and actionable recommendations in an easily understandable format. Clear reports are essential; many documents from a pen testing company confuse stakeholders with long lists of vulnerabilities, failing to explain the associated business risks. According to a recent study, 73% of successful breaches were due to vulnerabilities in web applications, underscoring the need for clear communication of risks.
- Actionable Insights: It is vital to seek reports that not only identify vulnerabilities but also offer specific remediation steps. Actionable insights enable entities to prioritize and tackle security vulnerabilities effectively, turning findings into concrete enhancements in their security frameworks. As Gunter Ollmann, CTO at Cobalt, states, “Top-performing leaders achieve a high-risk finding half-life of just 10 days. Meanwhile, the bottom 10% of organizations allow these same vulnerabilities to languish for 249 days,” highlighting the importance of timely and actionable insights.
- Communication Protocols: Establishing robust communication protocols is key. Organizations should clarify how the provider will communicate findings and updates throughout the assessment process, ensuring that all relevant stakeholders remain informed and engaged. This ongoing dialogue promotes a cooperative atmosphere that improves the overall efficiency of the security assessment effort. Notably, only 44% of companies have integrated security tests into their coding workflows, indicating a significant opportunity for improvement in communication and collaboration.
By focusing on clarity, actionable insights, and robust communication, a pen testing company can help organizations significantly strengthen their cybersecurity defenses.
Conclusion
Selecting an appropriate penetration testing company is essential for manufacturing organizations seeking to bolster their cybersecurity defenses. Understanding penetration testing fundamentals is crucial for evaluating a provider’s capabilities. Recognizing the importance of identifying vulnerabilities and testing protective measures enables organizations to make informed decisions that protect their operational integrity.
Throughout this article, we have explored key practices for selecting a penetration testing provider. These include:
- Defining clear objectives
- Assessing the provider’s expertise and methodologies
- Evaluating their reporting and communication practices
By focusing on critical assets, risk tolerance, and specific goals, organizations can tailor their assessments to align with their cybersecurity strategies. Furthermore, the importance of clear communication and actionable insights in reporting cannot be overstated, as they are vital for effective remediation and ongoing security improvements.
Engaging a skilled penetration testing company is vital for safeguarding against evolving cyber threats. As these threats continue to grow in complexity, organizations must prioritize their cybersecurity measures and adopt a proactive approach to vulnerability management. By implementing these best practices, manufacturing firms can not only protect their assets but also foster a culture of security that empowers them to navigate the complexities of the digital landscape confidently. Proactive engagement in cybersecurity practices today will ensure a more secure and resilient manufacturing environment tomorrow.
Frequently Asked Questions
What is penetration testing?
Penetration testing, or pen testing, is a simulated cyber attack on systems, networks, or web applications aimed at identifying vulnerabilities that malicious actors might exploit.
Why is penetration testing important for manufacturing operations?
It is crucial for manufacturing operations to understand penetration testing as it helps evaluate their security posture, comply with industry regulations, and proactively identify vulnerabilities before they can be exploited.
What are the primary objectives of penetration testing?
The primary objectives of penetration testing include identifying vulnerabilities, testing protective measures, and ensuring compliance with regulatory requirements.
How prevalent is the practice of vulnerability assessments in the manufacturing sector?
About 39% of firms in manufacturing conduct vulnerability assessments at least once or twice annually, indicating a growing awareness of the need for strong protective measures.
What percentage of security experts conduct security tests for compliance?
Approximately 75% of security experts perform security tests to meet compliance requirements, highlighting the importance of these evaluations in regulatory adherence.
What risks do organizations face without proper penetration testing?
Organizations that do not conduct proper penetration testing may face significant risks, including compliance failures and potential operational disruptions.
How does understanding penetration testing fundamentals benefit organizations?
A solid understanding of penetration testing fundamentals enables organizations to effectively evaluate their security posture and engage skilled security assessment providers, which is vital for maintaining a secure environment.
List of Sources
- Understand the Fundamentals of Penetration Testing
- 7 Key Manufacturing Cybersecurity Trends for 2026 | Huntress (https://huntress.com/blog/manufacturing-cybersecurity-trends)
- Penetration testing statistics, vulnerabilities and trends in 2026 – Cyphere (https://thecyphere.com/blog/penetration-testing-statistics)
- 100+ essential penetration testing statistics [2023 edition] (https://pentest-tools.com/blog/penetration-testing-statistics)
- 120+ Penetration Testing Statistics for 2026 (https://brightdefense.com/resources/penetration-testing-statistics)
- 83 Penetration Testing Statistics: Key Facts and Figures (https://getastra.com/blog/penetration-testing/statistics)
- Define Your Pen Testing Objectives Clearly
- The Importance of a Clearly Defined Pentesting Scope (https://guidepointsecurity.com/blog/the-importance-of-a-clearly-defined-pentesting-scope)
- Penetration Testing Best Practices in 2026 | Iterasec (https://iterasec.com/blog/4-tips-to-maximize-application-pentest-value)
- What is the Primary Goal of Penetration Testing | BPM (https://bpm.com/insights/what-is-the-primary-goal-of-penetration-testing)
- Pentesting Statistics 2026: Key Insights and Emerging Trends (https://zerothreat.ai/blog/emerging-penetration-testing-statistics)
- Why Penetration Testing is Important for Your Business in 2026 (https://brightdefense.com/resources/why-penetration-testing-is-important)
- Evaluate Expertise and Methodologies of Providers
- Case Study • Manufacturing company – Arco IT (https://arco-it.ch/referenz/case-study-manufacturing-company)
- 100+ essential penetration testing statistics [2023 edition] (https://pentest-tools.com/blog/penetration-testing-statistics)
- Pentesting Statistics 2026: Key Insights and Emerging Trends (https://zerothreat.ai/blog/emerging-penetration-testing-statistics)
- Case_studies page (https://cybersafehaven.com/Case_studies.html)
- Assess Reporting and Communication Practices
- 83 Penetration Testing Statistics: Key Facts and Figures (https://getastra.com/blog/penetration-testing/statistics)
- 100+ essential penetration testing statistics [2023 edition] (https://pentest-tools.com/blog/penetration-testing-statistics)
- The 2026 State of Pentesting: How Modern Teams Manage and Deliver Results (https://thehackernews.com/expert-insights/2026/01/the-2026-state-of-pentesting-how-modern.html)
- 5 Key Takeaways from the 2026 State of Pentesting Report (https://cobalt.io/blog/5-key-takeaways-from-the-2026-state-of-pentesting-report)
- Outsourcing Penetration Testing in 2026: What Actually Works | Capture The Bug (https://capturethebug.xyz/Blogs/Why-Smart-Companies-Rethink-Outsourcing-Penetration-Testing-in-2026)