Introduction
Selecting the appropriate penetration testing organization is a pivotal decision for any business striving to enhance its cybersecurity defenses. Given the escalating sophistication of cyber threats, it is crucial to grasp the nuances of penetration testing – from its fundamental phases to the diverse methodologies employed. This article explores best practices for choosing a penetration testing provider, emphasizing key factors that can significantly impact the effectiveness of security assessments. As organizations navigate this intricate landscape, the pressing question is: how can they ensure they select a provider that not only fulfills compliance requirements but also aligns with their distinct security needs?
Understand Penetration Testing Fundamentals
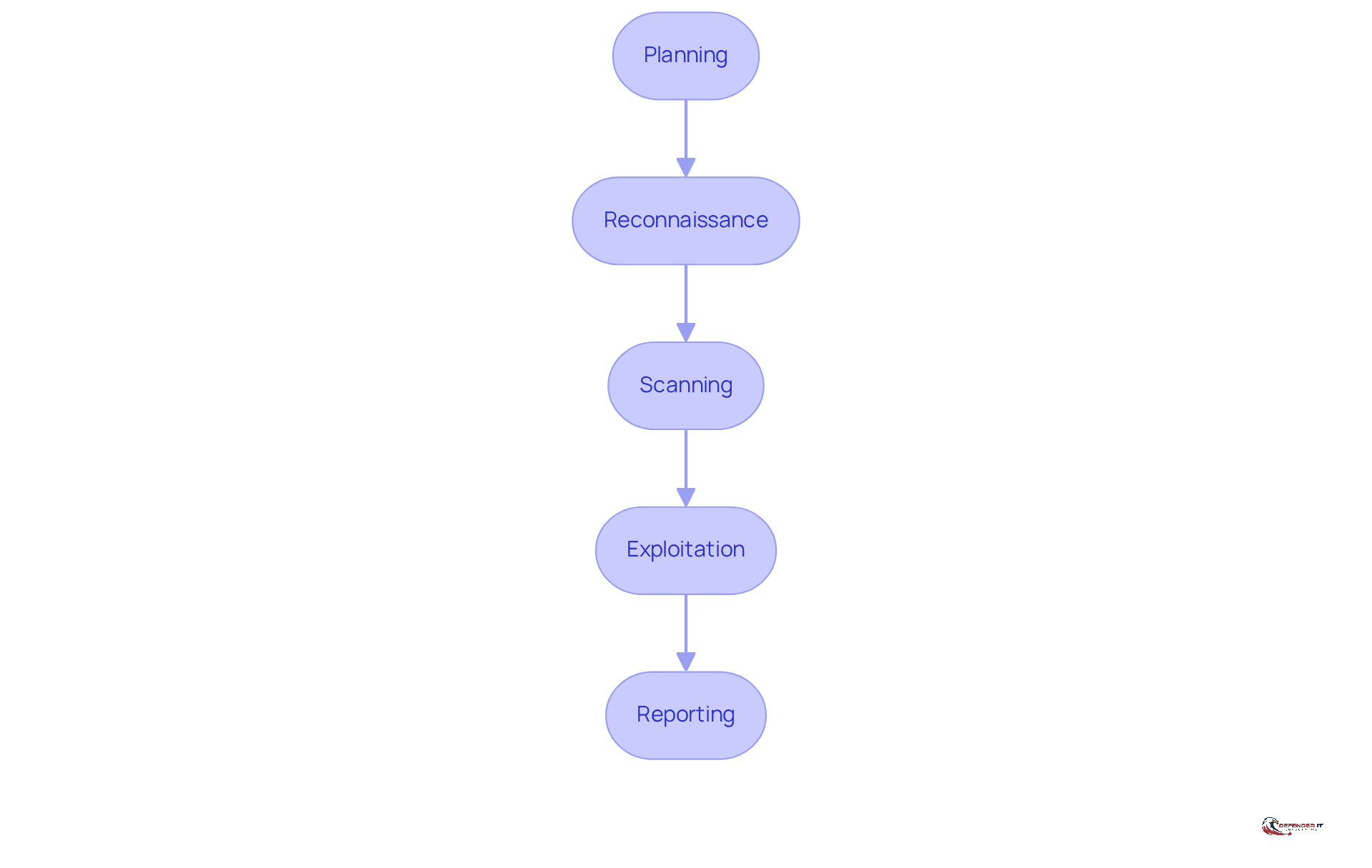
Penetration testing, commonly referred to as ‘pen testing,’ represents a simulated cyber assault on computer systems aimed at identifying exploitable weaknesses. This process encompasses several critical phases:
- Planning
- Reconnaissance
- Scanning
- Exploitation
- Reporting
Understanding these phases is essential to appreciate the depth and value of the evaluation process.
During the reconnaissance phase, for instance, testers collect information, which is crucial for pinpointing potential vulnerabilities. This foundational knowledge empowers organizations to make informed decisions with a strategic approach, enabling them to improve security regarding outcomes. By grasping the intricacies of each phase, companies can better navigate the complexities of penetration testing.
Explore Different Types of Penetration Testing
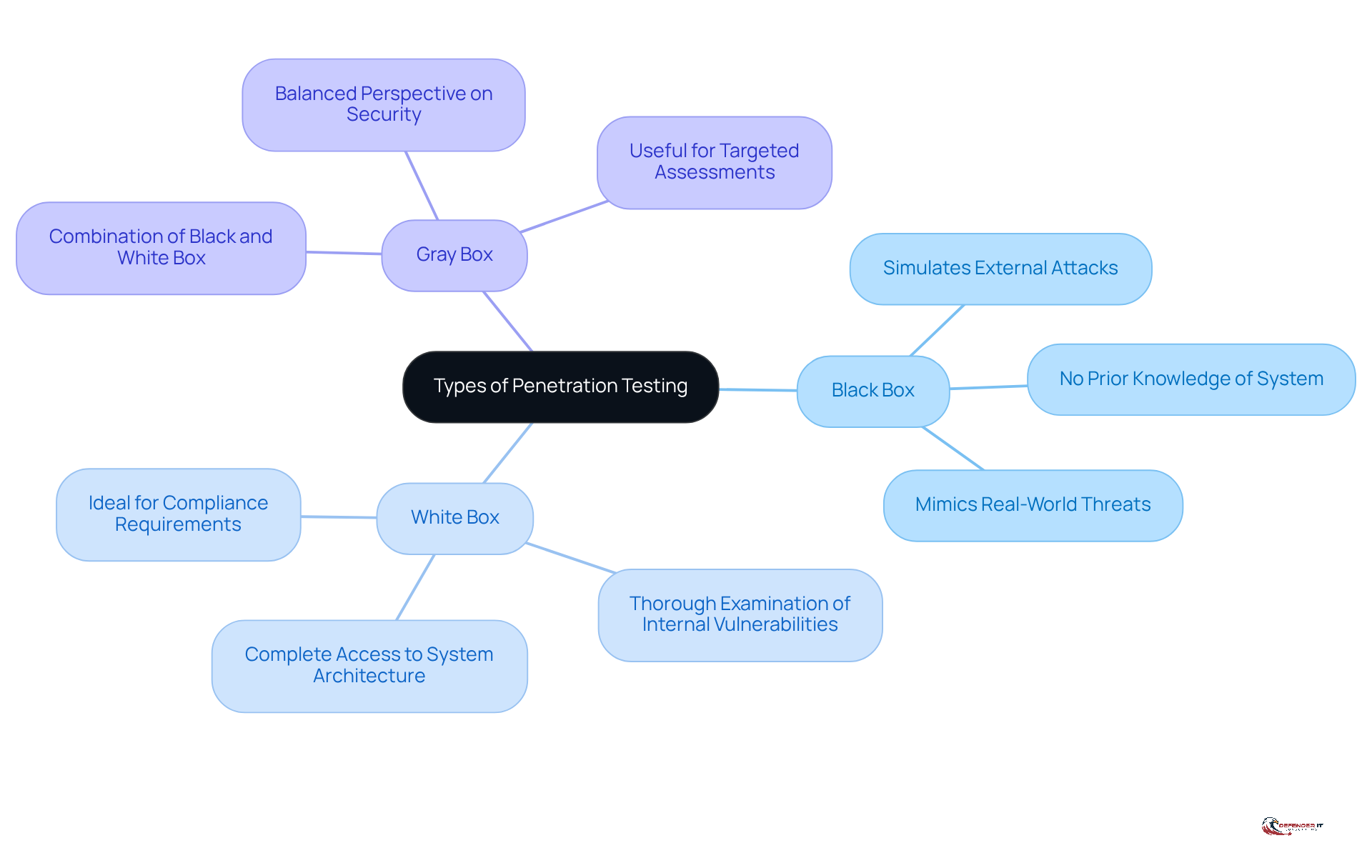
Penetration assessment is a critical component of cybersecurity, encompassing various methodologies: black box, white box, and gray box approaches. Black box evaluation simulates an external attack without prior knowledge of the system, effectively mimicking real-world threats. In contrast, white box assessment grants testers complete access to the system’s architecture, allowing for a thorough examination of vulnerabilities. Gray box evaluation merges aspects of both approaches, providing a balanced perspective on security.
Organizations must carefully evaluate their specific needs when selecting a provider for assessment. This includes considering risks and the sensitivity of the data they handle. For instance, to ensure comprehensive coverage of their internal systems, organizations should align with stringent regulatory requirements.
As the security assessment landscape evolves, it is essential for entities aiming to enhance their security posture to stay informed about current trends and methodologies used by experts. Additionally, regulated parties are required to conduct assessments, as mandated by compliance standards such as PCI DSS.
Integrating perspectives from cybersecurity experts, such as Tim Campbell, who emphasizes the significance of thorough vetting, can further assist a company in making well-informed choices. By recognizing common pitfalls in selecting providers, organizations can prevent errors and ensure they effectively meet their security requirements.
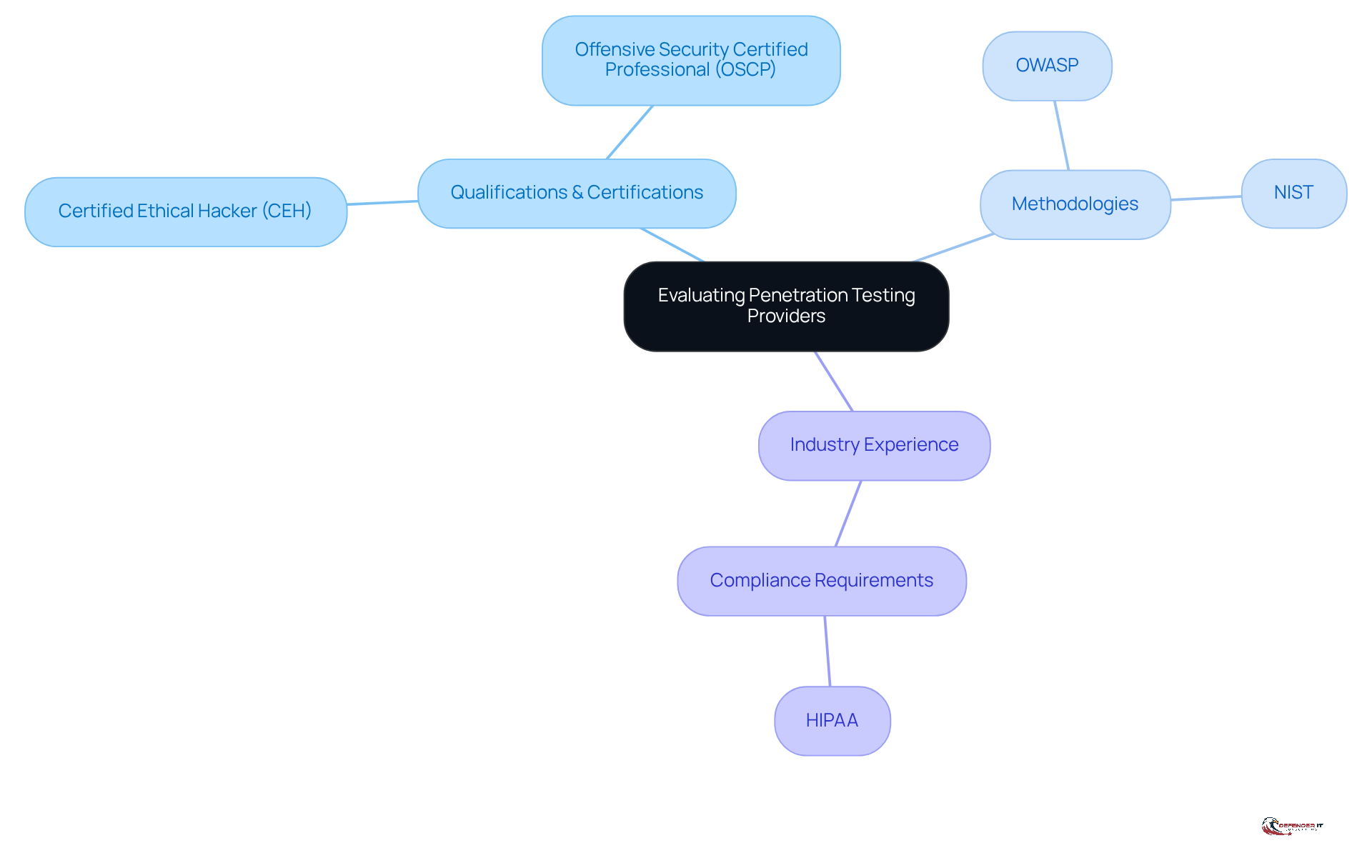
Evaluate Expertise and Methodologies of Providers
When selecting a penetration testing organization, it is crucial to evaluate the qualifications and certifications of their evaluation team. Look for industry-recognized certifications such as:
These certifications demonstrate a commitment to maintaining high standards. Additionally, inquire about the methodologies employed by the provider. Do they adhere to recognized frameworks:
- OWASP
- NIST
These frameworks ensure that evaluations are thorough and effective.
Experience in your specific industry can also provide a significant advantage. A provider with relevant experience will be well-versed in regulations like HIPAA. This expertise enables them to customize their assessment approach effectively. Such familiarity not only enhances the quality of the evaluation but also ensures that the unique challenges faced by your organization are adequately addressed, ultimately leading to a more robust security posture.
By 2026, penetration testing will be a necessary component of compliance in certain regulated environments, making it essential to choose a qualified organization as a provider. As Cindy Kaplan pointed out, “the reality is that by 2026, penetration tests are going to be a necessary component of compliance in certain regulated settings and anticipated as a fundamental aspect of demonstrable cybersecurity programs in other contexts.” This highlights the urgency for entities to prioritize their evaluation process. Moreover, case studies have shown that organizations employing certified experts for penetration testing experience a notable decrease in vulnerabilities and improved compliance outcomes.
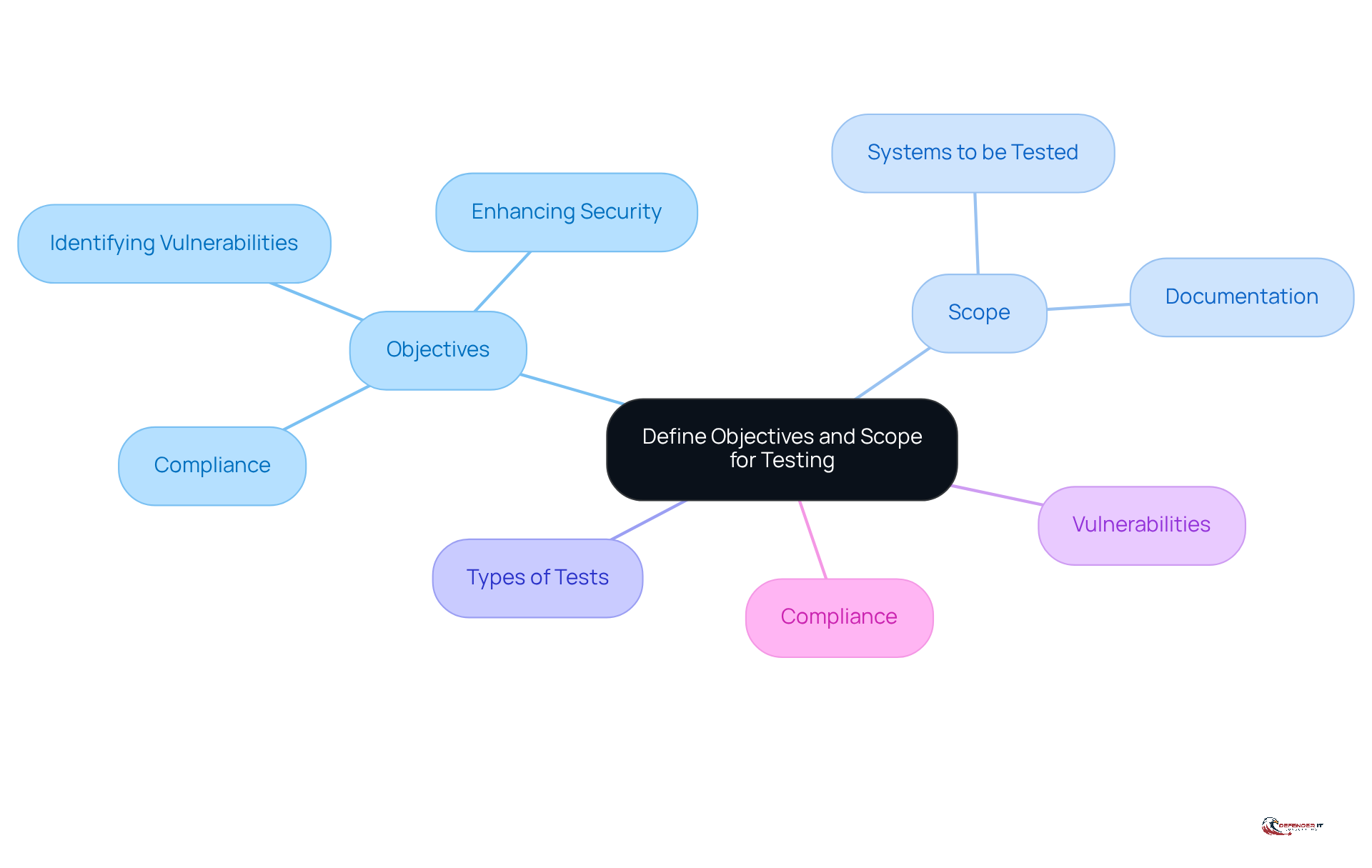
Define Objectives and Scope for Testing
Before engaging a penetration testing organization, companies must clearly define their objectives and the scope of the evaluation. This involves identifying which systems will be tested, the resources available, and the timeline for the assessment. For instance, if an organization is particularly concerned about its web applications, it should specify that the testing should focus on those systems. Establishing clear goals is crucial for evaluating the effectiveness of the testing process. Organizations should consider what they aim to achieve – whether it’s compliance with regulations, identifying vulnerabilities, or enhancing their overall security posture. Notably, 70% of organizations conduct assessments primarily for compliance, underscoring the importance of clarity.
Furthermore, as Brian Tant observes, “Evaluating beyond the defined scope exposes the company to potential liability,” which highlights the critical nature of scoping in penetration assessments. Setting these objectives not only aligns with business requirements but also ensures that the evaluation process effectively addresses the unique risks associated with their operations. Successful entities often engage in thorough planning, which a penetration testing organization can help define, leading to more focused assessments and actionable insights. This organized approach fosters a collaborative environment and enhances the overall efficiency of the assessment process. Continuous improvement significantly bolsters an organization’s security program by facilitating quicker risk identification, making it essential to have clear objectives.
Review Reporting Processes and Deliverables
A comprehensive report must include an executive summary, detailed findings, recommendations, and conclusions. Organizations should proactively inquire about the reporting process of a penetration testing organization before selecting a provider. Key questions to consider include:
- Whether the report will feature visual aids, such as charts or graphs, to simplify complex information.
- If it will outline remediation steps for each identified issue.
Additionally, the report should present supporting evidence, such as screenshots or logs, to enhance the credibility of the findings. A well-organized report not only identifies weaknesses but also provides context within the organization. For instance, categorizing vulnerabilities by severity enables entities to prioritize remediation efforts effectively.
This structured approach ensures that stakeholders can make informed decisions based on the insights provided in the report, ultimately strengthening the organization’s security posture.
Conclusion
Selecting the appropriate penetration testing organization is vital for enhancing an organization’s cybersecurity posture. A solid understanding of penetration testing fundamentals, including its various phases and methodologies, enables companies to make informed decisions tailored to their specific needs. By clearly defining objectives and scope, organizations can ensure that their assessments are both focused and effective, ultimately resulting in improved security outcomes.
This article outlines essential criteria for choosing a penetration testing provider, emphasizing the evaluation of expertise, methodologies, and reporting processes. The importance of industry-recognized certifications and adherence to established frameworks is highlighted, as these factors significantly enhance the reliability of assessments. Furthermore, clear communication regarding the testing scope and deliverables is crucial, ensuring that organizations receive actionable insights to effectively address vulnerabilities.
In today’s rapidly evolving threat landscape, prioritizing the selection of a qualified penetration testing organization is more critical than ever. By implementing these best practices, organizations can not only fulfill compliance requirements but also cultivate a proactive security culture. Dedicating time to select the right partner in penetration testing will ultimately contribute to a more resilient cybersecurity framework, safeguarding valuable assets and fostering trust with stakeholders.
Frequently Asked Questions
What is penetration testing?
Penetration testing, often called ‘pen testing,’ is a simulated cyber assault on computer systems designed to identify exploitable weaknesses.
What are the critical phases of penetration testing?
The critical phases of penetration testing include Planning, Reconnaissance, Scanning, Exploitation, and Reporting.
Why is the reconnaissance phase important in penetration testing?
The reconnaissance phase is crucial because testers collect vital information about the target system, which helps in identifying potential vulnerabilities and enables effective collaboration with the penetration testing organization.
What are the different types of penetration testing methodologies?
The different types of penetration testing methodologies include black box, white box, and gray box approaches. Black box simulates an external attack without prior knowledge of the system, white box provides complete access to the system’s architecture, and gray box combines aspects of both approaches.
How do organizations choose a penetration testing organization?
Organizations should evaluate their specific needs, including compliance mandates and the sensitivity of the data they handle, when selecting a penetration testing organization.
What compliance standards require regular security assessments?
Compliance standards such as PCI DSS require regulated parties to conduct security assessments at least once every 12 months.
How can organizations enhance their security posture through penetration testing?
Organizations can enhance their security posture by staying informed about current trends and methodologies in penetration testing and by recognizing common pitfalls in selecting security evaluation methods.
List of Sources
- Understand Penetration Testing Fundamentals
- The 2026 State of Pentesting: How Modern Teams Manage and Deliver Results (https://thehackernews.com/expert-insights/2026/01/the-2026-state-of-pentesting-how-modern.html)
- isaca.org (https://isaca.org/resources/news-and-trends/industry-news/2026/the-6-cybersecurity-trends-that-will-shape-2026)
- The Critical Phases of Penetration Testing for Business (https://digitdefence.com/blog/the-critical-phases-of-penetration-testing-for-business)
- 5 Stages of Penetration Testing Explained | Step-by-Step Guide (https://invicti.com/blog/web-security/5-stages-of-penetration-testing)
- The Different Methods and Stages of Penetration Testing (https://thehackernews.com/2023/03/the-different-methods-and-stages-of.html)
- Explore Different Types of Penetration Testing
- Penetration Testing for Compliance (https://netspi.com/blog/executive-blog/penetration-testing-as-a-service/penetration-testing-for-compliance)
- Penetration Testing Requirement: What U.S. Rules Mandate It in 2026? (https://halock.com/penetration-testing-requirement-what-u-s-rules-mandate-it-in-2026)
- schellman.com (https://schellman.com/blog/penetration-testing/penetration-testing-key-stats)
- 83 Penetration Testing Statistics: Key Facts and Figures (https://getastra.com/blog/security-audit/penetration-testing-statistics)
- Medical Device Penetration Testing Case Study (https://vumetric.com/resources/medical-device-penetration-testing-case-study)
- Evaluate Expertise and Methodologies of Providers
- 83 Penetration Testing Statistics: Key Facts and Figures (https://getastra.com/blog/security-audit/penetration-testing-statistics)
- Penetration Testing Requirement: What U.S. Rules Mandate It in 2026? (https://halock.com/penetration-testing-requirement-what-u-s-rules-mandate-it-in-2026)
- pentest-tools.com (https://pentest-tools.com/blog/penetration-testing-statistics)
- Penetration testing statistics, vulnerabilities and trends in 2026 – Cyphere (https://thecyphere.com/blog/penetration-testing-statistics)
- Define Objectives and Scope for Testing
- pentest-tools.com (https://pentest-tools.com/blog/penetration-testing-statistics)
- Continuous Penetration Testing: The Ultimate 2025 Guide (https://deepstrike.io/blog/continuous-penetration-testing)
- Penetration Testing Requirement: What U.S. Rules Mandate It in 2026? (https://halock.com/penetration-testing-requirement-what-u-s-rules-mandate-it-in-2026)
- Penetration testing best practices: Strategies for all test types (https://strikegraph.com/blog/pen-testing-best-practices)
- Penetration Testing: What is it? (https://netspi.com/blog/executive-blog/penetration-testing-as-a-service/penetration-testing-security)
- Review Reporting Processes and Deliverables
- What Should a Penetration Testing Report Include? | JUMPSEC (https://jumpsec.com/guides/what-should-a-penetration-testing-report-include)
- 5 Things to Look for in a Penetration Testing Company in 2026 – Netragard (https://netragard.com/5-things-look-for-penetration-testing-company)
- 83 Penetration Testing Statistics: Key Facts and Figures (https://getastra.com/blog/security-audit/penetration-testing-statistics)
- Penetration testing statistics, vulnerabilities and trends in 2026 – Cyphere (https://thecyphere.com/blog/penetration-testing-statistics)
- Penetration Testing Report: What’s Included & How to Use (https://vikingcloud.com/blog/penetration-testing-report)