Introduction
As organizations strive to enhance their cybersecurity posture, the integration of Security Operations Centers (SOCs) with Endpoint Detection and Response (EDR) systems presents both significant opportunities and formidable challenges. This synergy not only enhances threat detection and incident response but also streamlines operations, ensuring that teams can act swiftly and effectively.
However, organizations face significant hurdles in achieving this integration, including:
- Alert fatigue
- The demand for skilled professionals
Without addressing these complexities, organizations risk underutilizing the capabilities of SOC and EDR collaboration.
Define the Role of Security Operations Centers in Cybersecurity
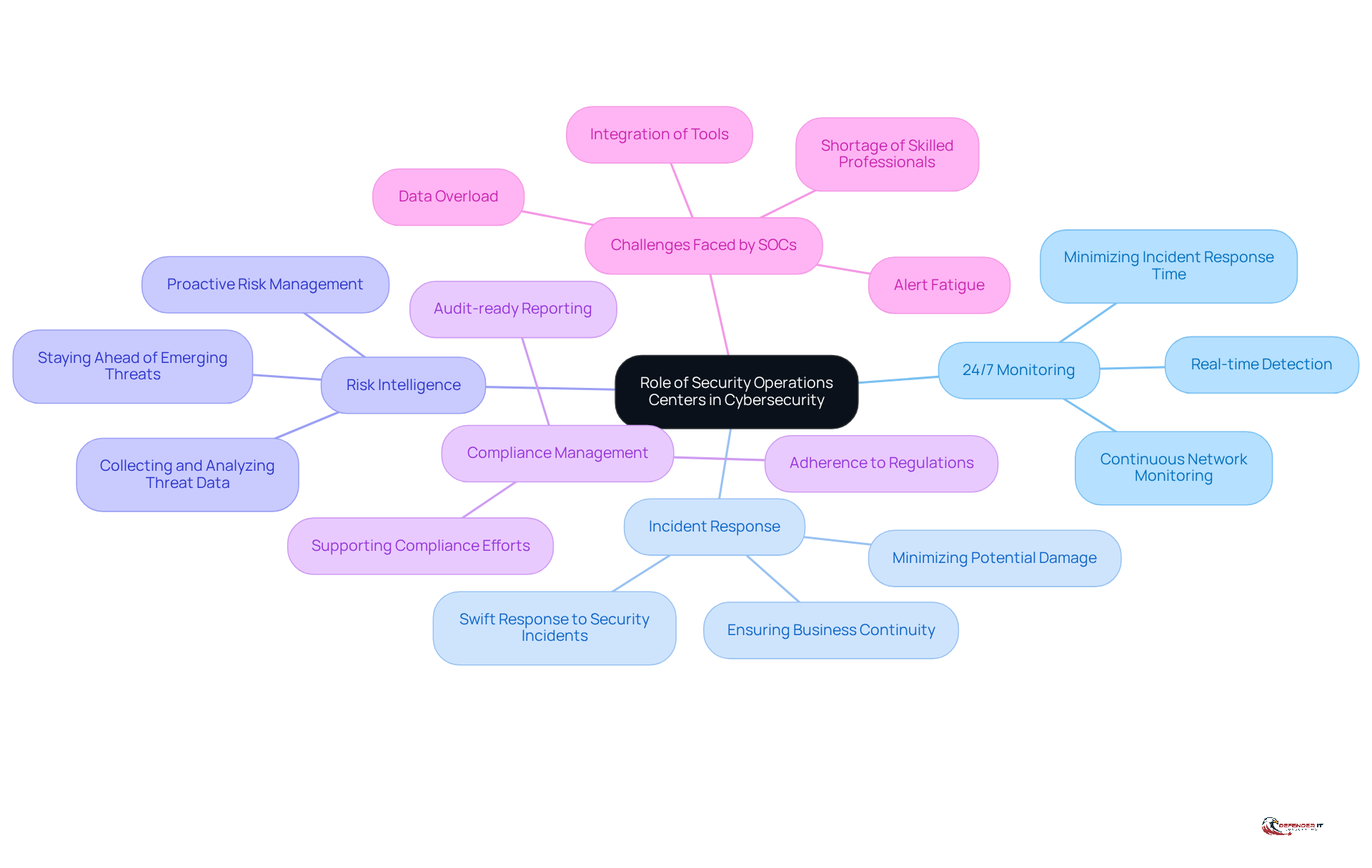
In the realm of cybersecurity, Security Operations Centers (SOCs) serve as the critical hub for safeguarding digital assets. They ensure robust protection through continuous monitoring, detection, analysis, and response to security incidents. Their key functions include:
- 24/7 Monitoring: SOCs operate around the clock, providing real-time detection and response to threats, significantly reducing the time between an incident occurring and its containment.
- Incident Response: Trained SOC teams respond swiftly to security incidents, minimizing potential damage and ensuring business continuity.
- Risk Intelligence: By collecting and examining risk intelligence, SOCs stay ahead of emerging dangers and vulnerabilities, allowing organizations to proactively address risks.
- Compliance Management: SOCs play a crucial role in ensuring adherence to relevant regulations and standards, particularly in highly regulated industries such as finance and healthcare.
To enhance operational efficiency, SOCs leverage orchestration platforms that automate repetitive tasks such as alert triage, enrichment, and initial response actions. Performance metrics for SOCs focus on outcomes rather than merely alert volume or ticket counts, providing a clearer understanding of their effectiveness. The strategic shift from detection-based security to intelligence-led operations further underscores the evolving role of SOCs in modern cybersecurity.
Despite their critical role, SOCs encounter significant challenges, including alert fatigue and a shortage of skilled professionals, which can hinder their effectiveness. The combination of SOCs with soc edr solutions enhances these capabilities, allowing organizations to utilize advanced technologies for better risk detection and incident management. This strategic alignment not only strengthens cybersecurity defenses but also enhances compliance efforts, ensuring the organization remains resilient against threats and safeguarding its reputation and operational integrity.
Explain the Functionality of Endpoint Detection and Response Systems
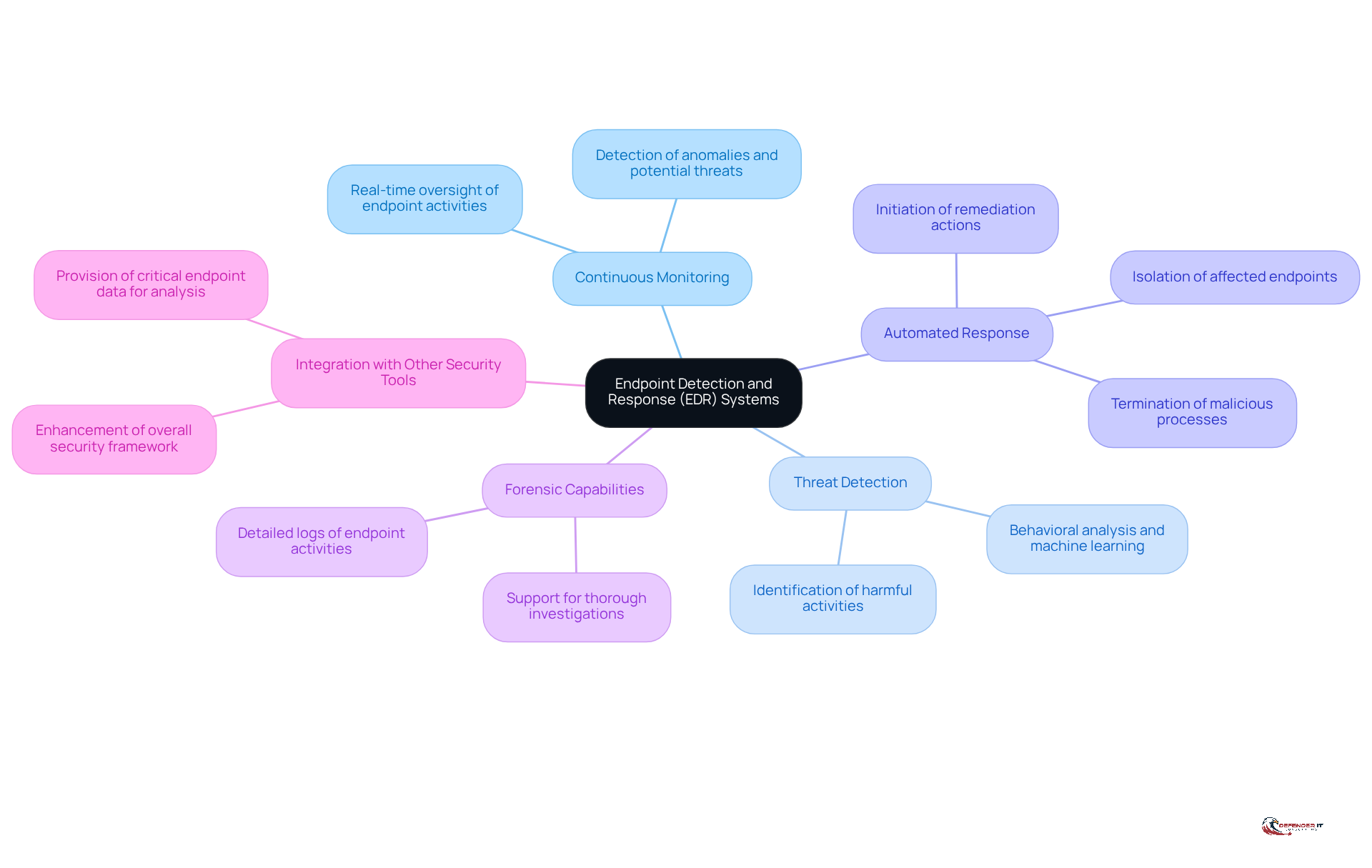
In an era where cyber threats are increasingly sophisticated, organizations must adopt advanced security measures to protect their endpoints. Endpoint Detection and Response (EDR) solutions are sophisticated security tools designed to oversee endpoint devices for unusual activities and respond to potential dangers. Key functionalities of EDR systems include:
- Continuous Monitoring: EDR solutions provide real-time monitoring of endpoint activities, allowing for the detection of anomalies and potential threats.
- Threat Detection: By employing behavioral analysis and machine learning, EDR solutions can identify harmful activities that conventional antivirus tools might overlook.
- Automated Response: EDR tools can automatically respond to detected threats by isolating affected endpoints, terminating malicious processes, and initiating remediation actions.
- Forensic Capabilities: EDR solutions keep detailed logs of what happens on endpoint devices, enabling security teams to conduct thorough investigations after an incident.
- Integration with Other Security Tools: EDR solutions can integrate with SOC EDR tools, which enhances the overall security framework by providing SOC teams with critical endpoint data for analysis and response.
This understanding empowers organizations to proactively defend against evolving cyber threats. Ultimately, leveraging EDR solutions can be the difference between thwarting a cyber attack and suffering a devastating breach.
Integrate SOC and EDR for Enhanced Threat Detection and Response
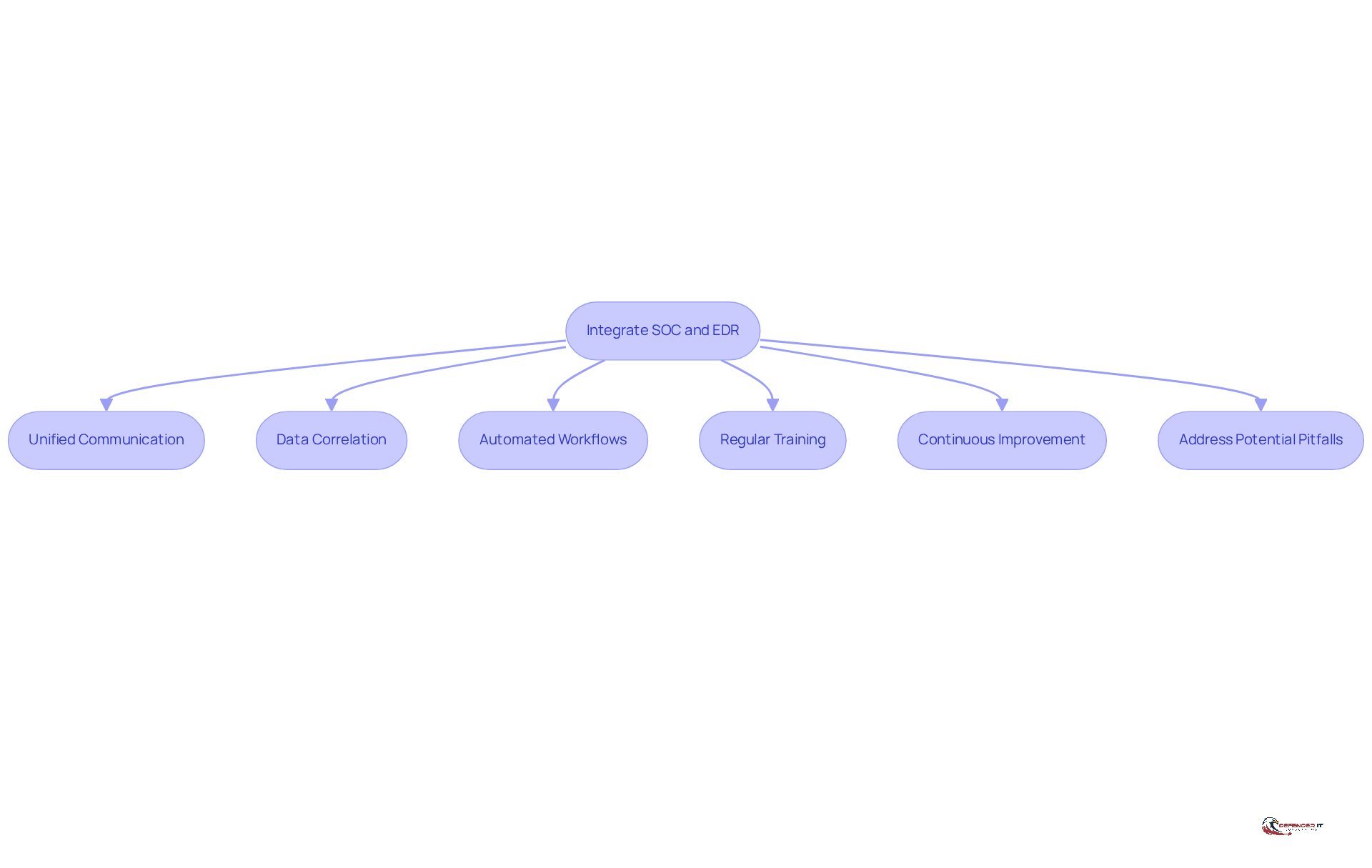
Integrating Security Operations Centers (SOCs) with SOC EDR solutions is not just beneficial; it is crucial for fortifying an organization’s cybersecurity framework. Here are key strategies for effective integration:
- Unified Communication: Establish clear communication channels between SOC analysts and EDR systems to ensure that alerts and incidents are promptly shared and addressed.
- Data Correlation: Utilize EDR data to enrich SOC investigations. By correlating endpoint data with network and threat intelligence, SOC teams can gain deeper insights into potential risks.
- Automated Workflows: Automated workflows are essential for ensuring that EDR networks can effectively trigger SOC responses when threats are detected. For example, when an EDR system identifies a risk, it can automatically notify the SOC and initiate established response protocols. Utilizing features from Fortinet’s Security Operations platform, including SOC EDR, can greatly decrease operational complexity and improve detection against AI-driven cyber risks.
- Regular Training: Conduct regular training sessions for SOC analysts on EDR functionalities and best practices. This ensures that the team is well-equipped to leverage EDR tools effectively.
- Continuous Improvement: Continuous improvement is vital; organizations should regularly assess integration processes, utilizing metrics from incident response results to adapt to evolving risk environments. This iterative approach helps maintain an effective security posture.
- Address Potential Pitfalls: Be aware of common pitfalls associated with SOC and EDR integration, such as alert fatigue from excessive data and the need for effective data management strategies.
Failure to effectively integrate these systems could leave organizations vulnerable to increasingly sophisticated cyber threats, underscoring the need for a strategic approach to cybersecurity. As Ken Xie, CEO of Fortinet, emphasizes, “Security operations must function with the same speed and coordination as attackers, especially as they weaponize AI to accelerate their efforts.
Implement Best Practices for SOC and EDR Integration
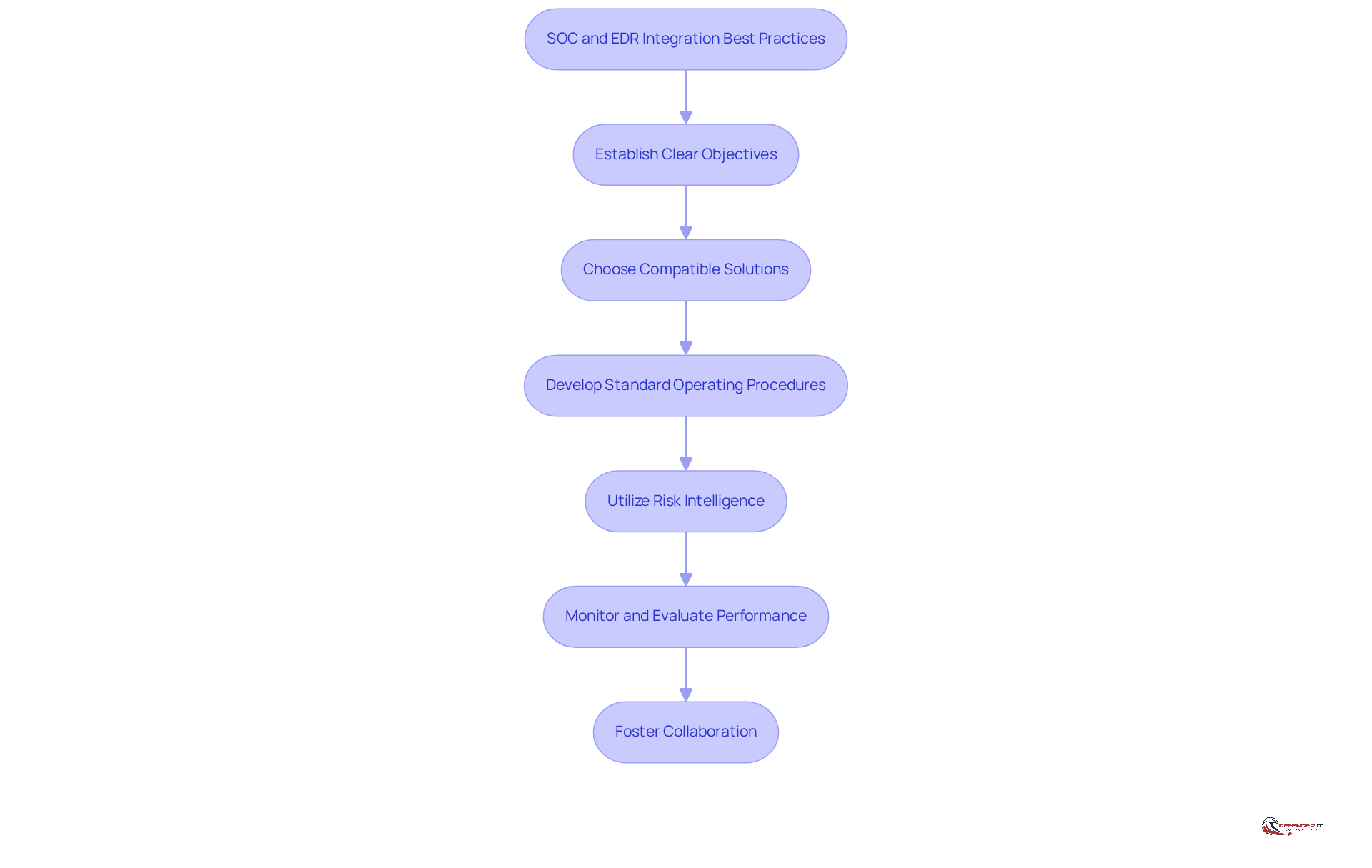
Integrating Security Operations Centers (SOCs) with EDR systems presents both challenges and opportunities for organizations aiming to enhance their cybersecurity posture. To achieve effective integration, organizations should follow these best practices:
- Establish Clear Objectives: Define the goals of the integration, such as improving incident response times or enhancing threat detection capabilities. Clear objectives guide the integration process.
- Choose Compatible Solutions: Select EDR solutions that are compatible with existing SOC tools and technologies. This guarantees smooth data exchange and interaction between networks.
- Develop Standard Operating Procedures (SOPs): Create SOPs that outline the processes for responding to alerts generated by EDR platforms. This helps ensure a consistent and efficient response to incidents.
- Utilize Risk Intelligence: Incorporate risk intelligence feeds into both SOC EDR and other frameworks. This enhances the ability to detect and respond to emerging threats based on real-time data.
- Monitor and Evaluate Performance: Continuously monitor the performance of the integrated systems and evaluate their effectiveness. Use metrics such as mean time to detect (MTTD) and mean time to respond (MTTR) to assess improvements.
- Foster Collaboration: Encourage collaboration between SOC analysts and EDR teams. Regular meetings and joint training sessions can enhance understanding and improve response strategies.
Ultimately, the effectiveness of SOC and EDR integration can significantly influence an organization’s resilience against cyber threats.
Conclusion
In an era where cyber threats are increasingly sophisticated, integrating Security Operations Centers (SOCs) with Endpoint Detection and Response (EDR) systems is essential for robust cybersecurity. This integration not only enhances threat detection and response capabilities but also fortifies the overall cybersecurity framework of an organization. By aligning SOC functions with EDR functionalities, organizations can create a more resilient defense against increasingly sophisticated cyber attacks.
Key strategies for effective SOC and EDR integration include:
- Establishing clear communication channels
- Utilizing data correlation
- Fostering collaboration between teams
Each of these elements plays a vital role in ensuring that organizations can respond swiftly and effectively to potential threats. Additionally, implementing best practices such as setting clear objectives and developing standard operating procedures can significantly improve the efficiency of incident response efforts.
In essence, integrating SOC and EDR systems is a strategic move that organizations cannot afford to overlook. Organizations must prioritize this integration to stay ahead of evolving threats and protect their digital assets. Embracing these best practices will not only bolster cybersecurity defenses but also ensure compliance and operational integrity in a landscape where cyber threats continue to grow in complexity and frequency. Prioritizing this integration is crucial for organizations aiming to safeguard their digital assets against the evolving landscape of cyber threats.
Frequently Asked Questions
What is the primary role of Security Operations Centers (SOCs) in cybersecurity?
SOCs serve as the critical hub for safeguarding digital assets by providing continuous monitoring, detection, analysis, and response to security incidents.
How do SOCs ensure continuous protection?
SOCs operate 24/7, which allows for real-time detection and response to threats, significantly reducing the time between an incident occurring and its containment.
What are the key functions of a SOC?
The key functions of a SOC include 24/7 monitoring, incident response, risk intelligence, and compliance management.
How do SOC teams respond to security incidents?
Trained SOC teams respond swiftly to security incidents to minimize potential damage and ensure business continuity.
What is the importance of risk intelligence in SOC operations?
Risk intelligence allows SOCs to collect and examine emerging dangers and vulnerabilities, enabling organizations to proactively address risks.
How do SOCs contribute to compliance management?
SOCs ensure adherence to relevant regulations and standards, particularly in highly regulated industries such as finance and healthcare.
What tools do SOCs use to enhance operational efficiency?
SOCs leverage orchestration platforms to automate repetitive tasks such as alert triage, enrichment, and initial response actions.
How do performance metrics for SOCs differ from traditional metrics?
Performance metrics for SOCs focus on outcomes rather than merely alert volume or ticket counts, providing a clearer understanding of their effectiveness.
What challenges do SOCs face in their operations?
SOCs encounter challenges such as alert fatigue and a shortage of skilled professionals, which can hinder their effectiveness.
How do SOC EDR solutions enhance SOC capabilities?
The combination of SOCs with SOC EDR solutions allows organizations to utilize advanced technologies for better risk detection and incident management, strengthening cybersecurity defenses and enhancing compliance efforts.
List of Sources
- Define the Role of Security Operations Centers in Cybersecurity
- Modern SOC Operations in 2026 Practical Guide | ManageX (https://managex.ae/what-modern-security-operations-centers-soc-actually-do-in-2026)
- Security Operations Center SOC Explained For 2026 | Netwitness (https://netwitness.com/blog/security-operations-modern-soc-strategy)
- The security operations center (SOC) of the future (https://leidos.com/insights/security-operations-center-soc-future)
- The 2026 Playbook: 10 High-growth Opportunities in Cybersecurity and Commercial & Public Security (https://frost.com/growth-opportunity-news/security/cybersecurity/the-2026-playbook-10-high-growth-opportunities-in-cybersecurity-and-commercial-public-security-sec02_tg02_top10gossecurity_mar26_cim-ms)
- Explain the Functionality of Endpoint Detection and Response Systems
- Endpoint Protection Failures: Why EDR Is Your Last Line of Defense Against Zero-Day Exploits – IP Services (https://ipservices.com/2026/03/18/edr-last-defense-zero-day-exploits)
- The 2026 Ultimate Guide to Endpoint Detection and Response (https://techday.co.uk/tag/endpoint-detection-and-response)
- What Is Endpoint Detection and Response (EDR)? How Does It Work? | Fortinet (https://fortinet.com/resources/cyberglossary/what-is-edr)
- Endpoint Detection and Response Market Size, Industry Share, Forecast to 2034 (https://fortunebusinessinsights.com/endpoint-detection-and-response-market-107235)
- Integrate SOC and EDR for Enhanced Threat Detection and Response
- How EDR Enhances SOC and MSSP Capabilities (https://itbutler.sa/blog/how-edr-enhances-soc-and-mssp-capabilities)
- Fortinet advances its Security Operations Platform with Unified SOC, Agentic AI and expanded Endpoint Security – Intelligent CISO (https://intelligentciso.com/2026/03/23/fortinet-advances-its-security-operations-platform-with-unified-soc-agentic-ai-and-expanded-endpoint-security)
- Fortinet Advances Its Security Operations Platform with Unified SOC, Agentic AI, and Expanded Endpoint Security (https://globenewswire.com/news-release/2026/03/10/3252872/0/en/fortinet-advances-its-security-operations-platform-with-unified-soc-agentic-ai-and-expanded-endpoint-security.html)
- Fortinet Advances Its Security Operations Platform with Unified SOC, Agentic AI, and Expanded Endpoint Security | Fortinet (https://fortinet.com/corporate/about-us/newsroom/press-releases/2026/fortinet-advances-its-security-operations-platform-with-unified-soc-agentic-ai-and-expanded-endpoint-security)
- 12 Security Operations Center (SOC) Best Practices in 2026 | CloudSEK (https://cloudsek.com/knowledge-base/security-operations-center-best-practices)
- Implement Best Practices for SOC and EDR Integration
- Security Operations Center (SOC) Best Practices and Steps in Building Process (https://cioinfluence.com/it-and-devops/security-operations-center-soc-best-practices-and-steps-in-building-process)
- 10 Best Practices to Modernize SOC Operations in 2026 (https://clearnetwork.com/10-best-practices-for-modernizing-soc-operations-in-2026/amp)
- 8 EDR Best Practices You Need to Pay Attention to in 2026 (https://heimdalsecurity.com/blog/edr-best-practices)
- It’s Time to Up-Level Your EDR Solution (https://trendmicro.com/es_mx/research/24/f/upgrade-edr-solution.html)
- 12 Security Operations Center (SOC) Best Practices in 2026 | CloudSEK (https://cloudsek.com/knowledge-base/security-operations-center-best-practices)