Introduction
In an era where cyber threats are increasingly prevalent, organizations must prioritize effective incident management and comprehensive digital forensics. The integration of these two essential functions not only bolsters immediate response capabilities but also strengthens long-term security strategies. Despite this necessity, many organizations face challenges in developing a cohesive approach to incident response and digital forensics. This raises an important question: how can businesses prepare to navigate the ever-evolving landscape of cybersecurity threats? This article explores best practices that enable organizations to respond with agility and precision, thereby safeguarding their assets and reputation.
Define Incident Response and Digital Forensics
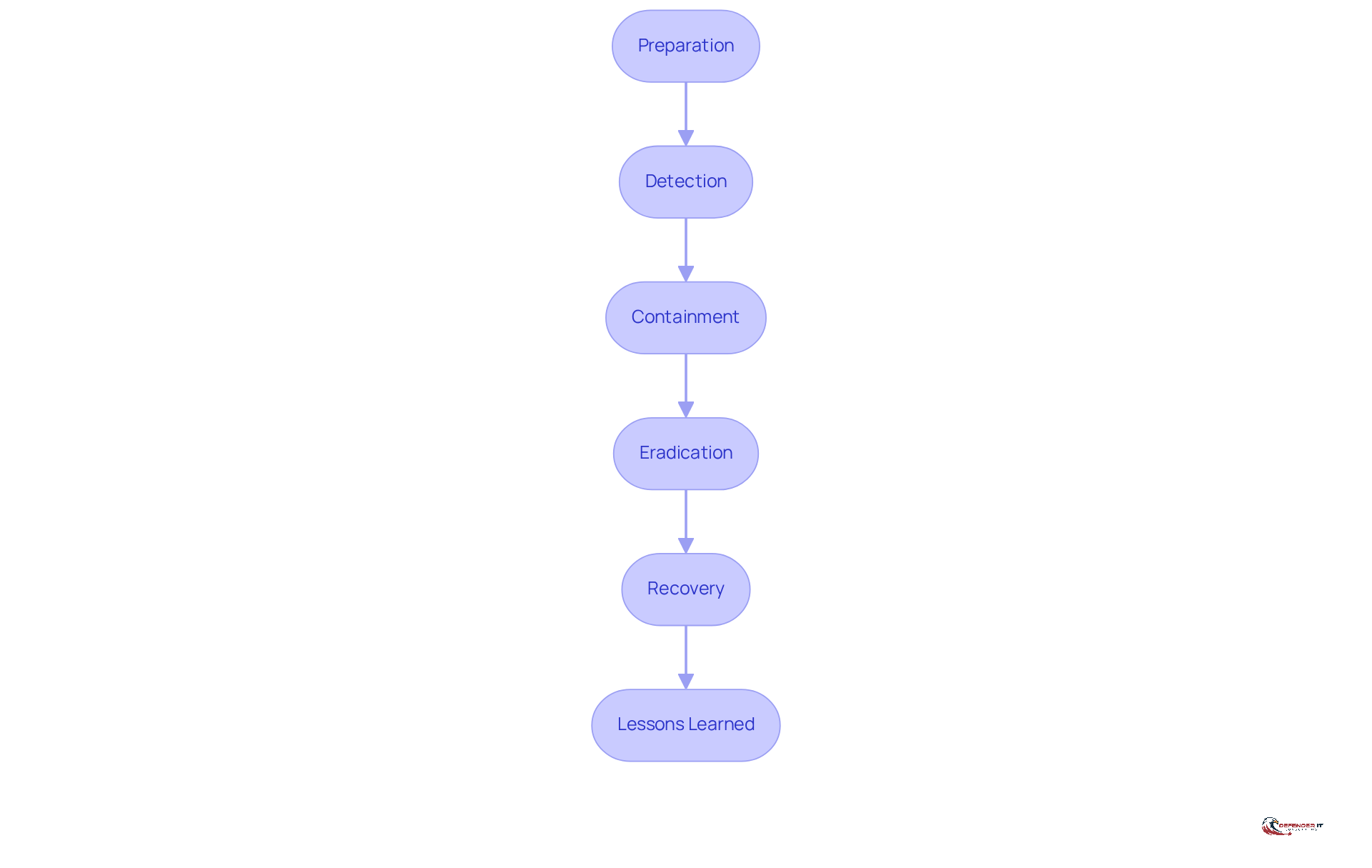
Crisis management represents a systematic approach that organizations employ to prepare for, identify, control, and recover from cybersecurity events. This methodology encompasses a series of well-defined steps aimed at minimizing damage and swiftly restoring normal operations. Key components of effective occurrence management include:
- Preparation
- Detection
- Containment
- Eradication
- Recovery
- Lessons learned
as outlined in the NIST framework. Each stage is vital for ensuring a robust response to potential threats.
Incident response and digital forensics significantly enhance response efforts by focusing on the collection, preservation, examination, and presentation of electronic evidence in a legally acceptable manner. This process is crucial for understanding the specifics of an event, identifying the attackers, and implementing strategies to prevent future breaches. For instance, during investigations, computer forensics specialists analyze various data sources, such as log files and memory dumps, to reconstruct the timeline of events leading up to the incident. This analysis not only supports immediate response efforts but also informs long-term security strategies.
The integration of crisis management and electronic investigation empowers organizations to respond to cyber threats with both speed and precision. By adopting a systematic approach, businesses can reduce attacker dwell time, minimize data loss, and enhance their overall security posture. Real-world examples demonstrate that organizations employing a cohesive incident response and digital forensics strategy can recover from security incidents more rapidly and effectively prosecute threat actors through meticulous evidence collection. In an era where cyberattacks are increasingly sophisticated, the synergy between crisis management and incident response and digital forensics is not just beneficial; it is essential for maintaining organizational resilience. Furthermore, many organizations lack the internal expertise to develop effective DFIR plans, highlighting the necessity for external assistance. The market for event management and electronic forensics capabilities is projected to grow at a compound annual growth rate (CAGR) of 12%, underscoring the increasing importance of these services. Legal compliance in electronic forensics processes is also critical, particularly for organizations operating in regulated environments, ensuring that evidence is admissible in legal proceedings.
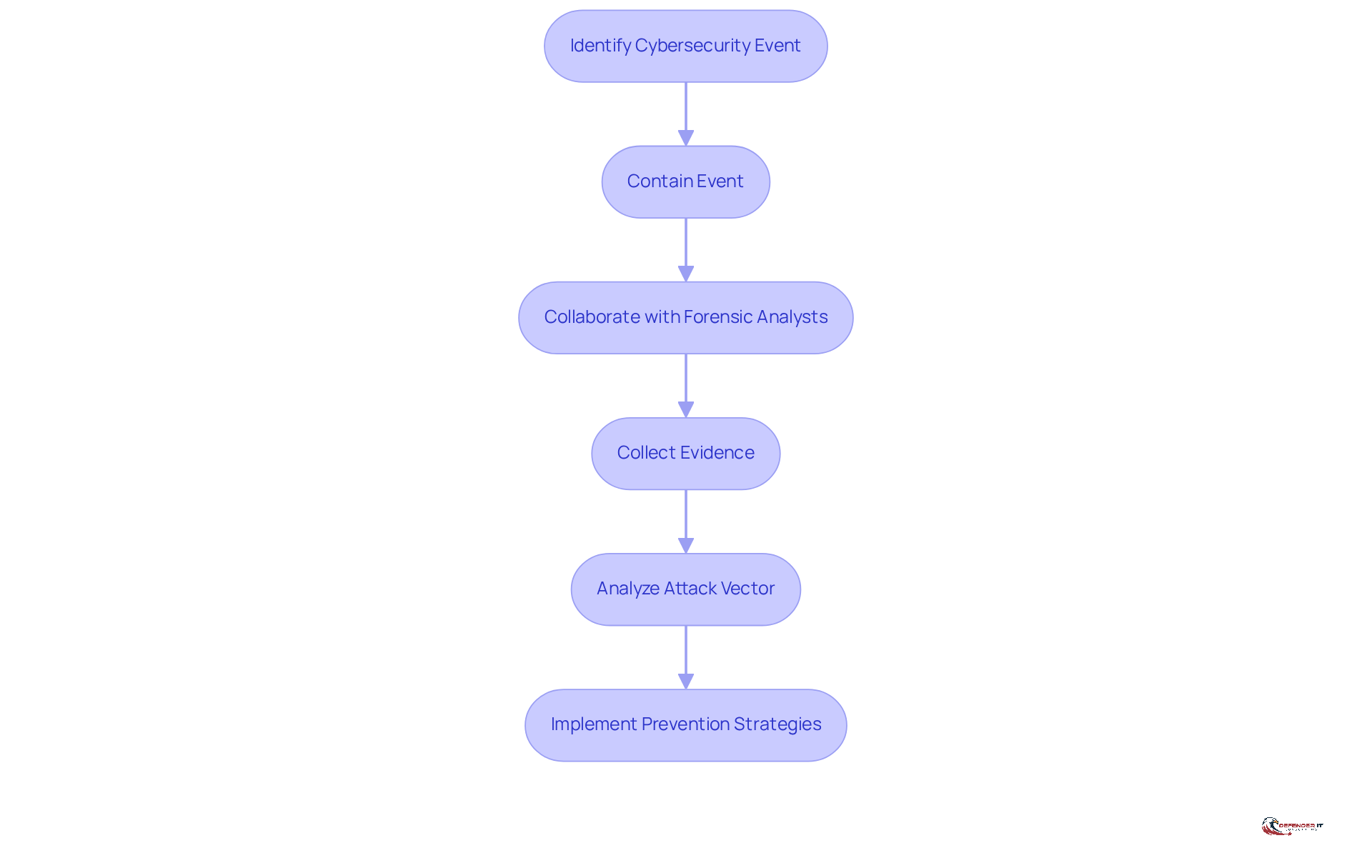
Integrate Incident Response with Digital Forensics
To effectively manage cybersecurity events, organizations must integrate their [[incident response and digital forensics](https://hivesecurity.gitlab.io/blog/dfir-incident-response-complete-guide-2026)](https://hivesecurity.gitlab.io/blog/dfir-incident-response-complete-guide-2026) efforts. This integration ensures that as events are identified and contained, incident response and digital forensics are conducted simultaneously, allowing for the collection of vital evidence and a comprehensive understanding of the attack vector. For example, during a data compromise, responders involved in incident response and digital forensics collaborate closely with forensic analysts to gather logs and other electronic evidence, revealing the breach’s origins and techniques. This collaborative approach not only aids in immediate containment but also informs future prevention strategies by identifying vulnerabilities and attack patterns.
Case studies demonstrate the effectiveness of this integration. In one instance, a manufacturing firm experienced a ransomware attack outside business hours, significantly impacting operations. By having response teams and forensic analysts work together, the organization promptly identified the attack vector and restored systems from clean backups, minimizing downtime and financial loss. Another case involved a financial institution that successfully managed a complex breach by utilizing a combined team of crisis management and cyber forensics specialists, resulting in a swift recovery and an improved security posture.
The benefits of merging event management with incident response and digital forensics are substantial. Organizations can achieve quicker problem resolution, enhanced evidence collection, and a deeper understanding of threats. This synergy not only improves immediate incident response and digital forensics capabilities but also strengthens long-term security strategies, making it essential for businesses in regulated or security-sensitive markets. However, the shortage of skilled expertise in forensics and crisis management poses a significant challenge, impacting the efficiency of these strategies. Moreover, the critical nature of evidence collection and preservation cannot be overstated, as improperly collected evidence may be inadmissible in court or lost. With the event management and digital forensics services market projected to reach USD 144.90 billion by 2030, and a CAGR of 20.97% anticipated, the necessity for companies to incorporate these functions is clear, particularly in light of regulatory pressures such as the NIS2 Directive, which imposes penalties for delayed reporting of breaches.
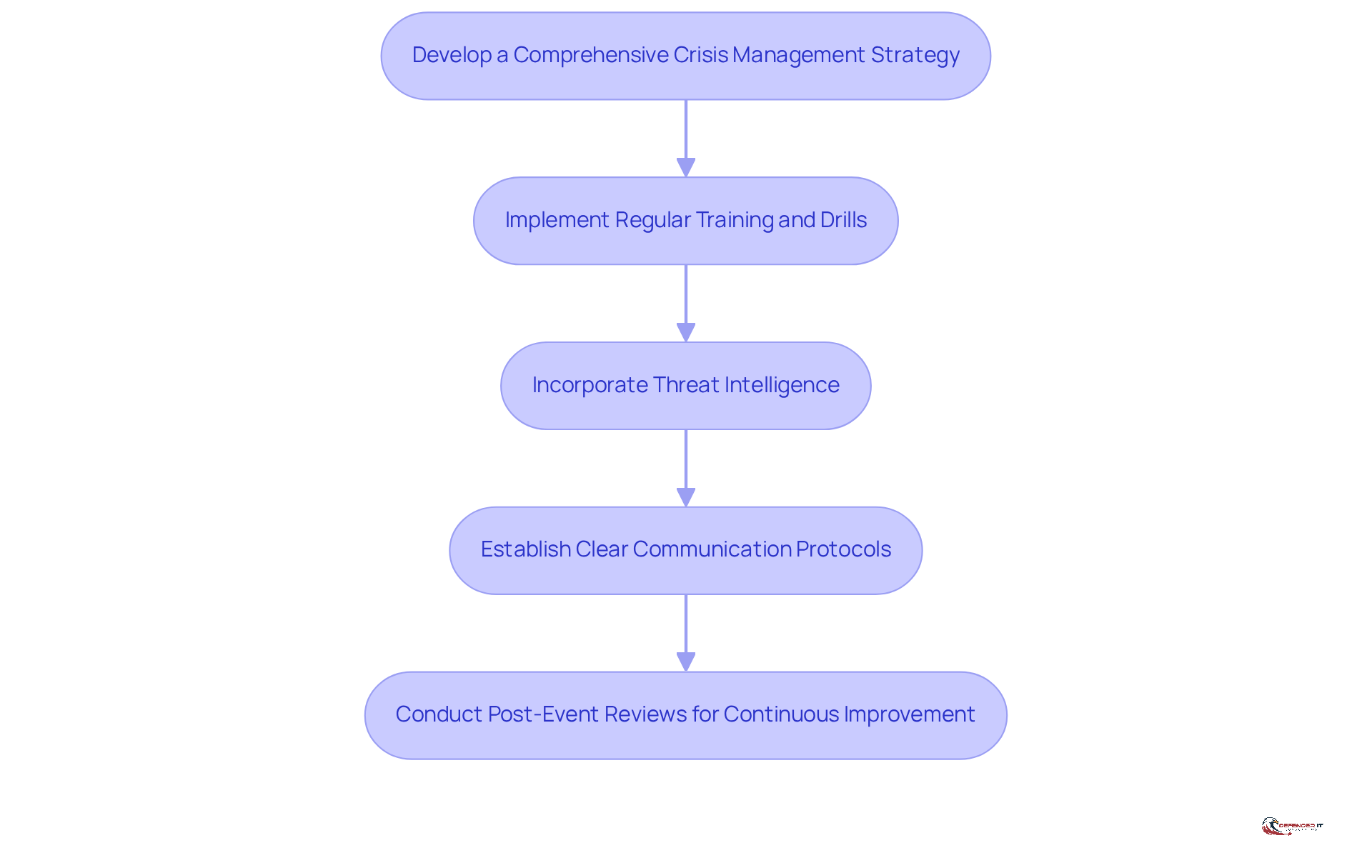
Implement Best Practices for Effective Incident Response
- Develop a Comprehensive Crisis Management Strategy: A robust crisis management strategy is essential for organizations to effectively navigate cyber incidents. This strategy must clearly outline roles, responsibilities, and procedures for addressing various types of events. Regular updates and assessments through simulations are crucial, as only 45% of organizations currently have a contingency plan. Notably, 88% of organizations with crisis management strategies also carry cyber insurance, highlighting the connection between preparedness and risk management.
- Implement Regular Training and Drills: It is vital for all team members to be familiar with the emergency action plan. Ongoing training and exercises not only reinforce procedures but also significantly improve response times during actual incidents. Research shows that organizations that engage in regular training are better equipped to handle crises, enabling them to respond decisively and efficiently under pressure.
- Incorporate Threat Intelligence: Integrating threat intelligence into your response strategy represents a proactive approach that keeps organizations informed about emerging threats and vulnerabilities. This strategy allows teams to anticipate potential incidents and implement mitigations before attacks occur, thereby enhancing overall security posture.
- Establish Clear Communication Protocols: Defining communication protocols, including established communication routes and escalation paths for both internal and external stakeholders during an incident, is critical. Effective communication ensures coordinated action and maintains transparency with affected parties, which is vital for preserving trust and minimizing reputational damage.
- Conduct Post-Event Reviews for Continuous Improvement: Following the resolution of an incident, conducting a thorough assessment is essential to identify lessons learned and areas for improvement. This continuous improvement process is crucial for refining response strategies over time, ensuring that organizations adapt to the evolving threat landscape and strengthen their resilience against future incidents.
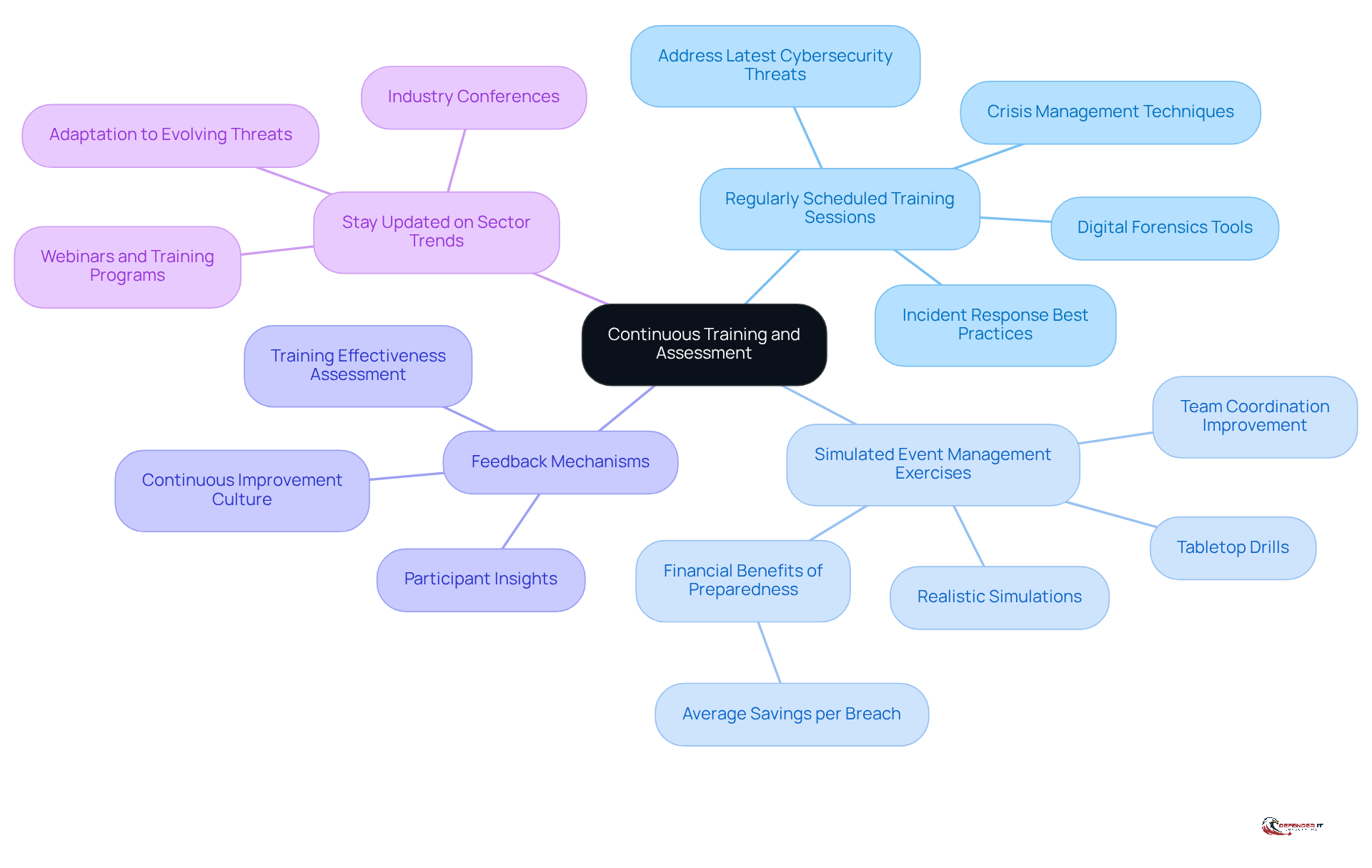
Ensure Continuous Training and Assessment
To maintain a proficient emergency management capability, organizations must prioritize ongoing training and evaluation. This includes:
- Regularly Scheduled Training Sessions: Organizations should conduct training sessions that address the latest cybersecurity threats, crisis management techniques, and tools. Given that 78% of organizations experienced significant impacts from cybersecurity breaches in the past year, it is essential for effective defense to stay updated with best practices in incident response and digital forensics.
- Simulated Event Management Exercises: Implementing tabletop drills and simulations to rehearse event management scenarios is crucial. These exercises not only enhance team skills but also improve coordination during actual events. Organizations with well-evaluated crisis management strategies can save an average of $2.22 million per breach, underscoring the financial benefits of preparedness.
- Feedback Mechanisms: Establishing feedback loops allows team members to share insights and suggestions for improving event management processes. Regular assessments and participant feedback are vital for validating training effectiveness and identifying areas for enhancement, fostering a culture of continuous improvement.
- Stay Updated on Sector Trends: Encourage team members to participate in industry conferences, webinars, and training programs to remain informed about the latest advancements in cybersecurity and crisis management strategies. As cyber threats evolve, organizations must adapt their training to reflect real incidents faced by their teams, ensuring relevance and effectiveness in their incident response and digital forensics capabilities.
Conclusion
The integration of incident response and digital forensics is essential in today’s cybersecurity landscape. Organizations must embrace a comprehensive approach to crisis management that includes:
- Preparation
- Detection
- Containment
- Eradication
- Recovery
- The critical lessons learned from each incident
By effectively combining these elements, businesses can respond swiftly to threats and enhance their security posture, ensuring resilience against future cyberattacks.
Key practices highlighted throughout this article include:
- The development of a robust crisis management strategy
- Regular training and drills
- The incorporation of threat intelligence
- The establishment of clear communication protocols
Each of these practices contributes to a well-rounded incident response plan, enabling organizations to navigate the complexities of cybersecurity incidents with greater efficiency. Furthermore, the emphasis on continuous training and assessment ensures that teams remain adept at handling evolving threats, reinforcing the importance of preparedness in mitigating risks.
In conclusion, the significance of integrating incident response with digital forensics cannot be overstated. As cyber threats become increasingly sophisticated, organizations must prioritize these best practices to protect their assets and comply with regulatory requirements. By fostering a culture of continuous improvement and collaboration, businesses can better equip themselves to face the challenges of the digital age, ultimately safeguarding their operations and maintaining stakeholder trust.
Frequently Asked Questions
What is incident response in cybersecurity?
Incident response is a systematic approach that organizations use to prepare for, identify, control, and recover from cybersecurity events. It includes steps such as preparation, detection, containment, eradication, recovery, and lessons learned, as outlined in the NIST framework.
How does digital forensics enhance incident response?
Digital forensics focuses on the collection, preservation, examination, and presentation of electronic evidence in a legally acceptable manner. This process helps understand the specifics of an event, identify attackers, and implement strategies to prevent future breaches.
What are the key stages of effective incident response?
The key stages of effective incident response include: – Preparation – Detection – Containment – Eradication – Recovery – Lessons learned
Why is the integration of crisis management and digital forensics important?
The integration empowers organizations to respond to cyber threats with speed and precision, reducing attacker dwell time, minimizing data loss, and enhancing overall security posture.
How can organizations benefit from a cohesive incident response and digital forensics strategy?
Organizations that employ a cohesive strategy can recover from security incidents more rapidly and effectively prosecute threat actors through meticulous evidence collection.
What challenges do organizations face in developing effective DFIR plans?
Many organizations lack the internal expertise to develop effective Digital Forensics and Incident Response (DFIR) plans, highlighting the necessity for external assistance.
What is the projected growth rate for event management and electronic forensics capabilities?
The market for event management and electronic forensics capabilities is projected to grow at a compound annual growth rate (CAGR) of 12%.
Why is legal compliance critical in electronic forensics?
Legal compliance in electronic forensics processes is crucial, particularly for organizations in regulated environments, to ensure that evidence is admissible in legal proceedings.
List of Sources
- Define Incident Response and Digital Forensics
- DFIR Guide: Importance Of Digital Forensics And Incident Response (https://netwitness.com/blog/digital-forensics-and-incident-response)
- The Role of Digital Forensics in Cybersecurity Incident Response (https://cyfor.co.uk/the-role-of-digital-forensics-in-cybersecurity-incident-response)
- 2026 Industry Trends: How Digital Forensics is Redefining Public Safety (https://cellebrite.com/en/resources/webinars/2026-industry-trends-how-digital-forensics-is-redefining-public-safety)
- Digital Forensics and Incident Response (DFIR) | CrowdStrike (https://crowdstrike.com/en-us/cybersecurity-101/exposure-management/digital-forensics-and-incident-response-dfir)
- 2026 State of Enterprise DFIR Report (https://magnetforensics.com/blog/state-of-enterprise-dfir-report-the-top-trends-shaping-digital-investigations-in-2026)
- Integrate Incident Response with Digital Forensics
- 2026 Unit 42 Global Incident Response Report (https://paloaltonetworks.com/resources/research/unit-42-incident-response-report)
- CISA Shares Lessons Learned from an Incident Response Engagement | CISA (https://cisa.gov/news-events/cybersecurity-advisories/aa25-266a)
- DFIR in 2026: A Complete Guide to Digital Forensics and Incident Response — Hive Security (https://hivesecurity.gitlab.io/blog/dfir-incident-response-complete-guide-2026)
- Incident Response And Digital Forensics Services Market Size, Share & 2030 Growth Trends Report (https://mordorintelligence.com/industry-reports/incident-response-and-digital-forensics-services-market)
- 2026 State of Enterprise DFIR Report (https://magnetforensics.com/blog/state-of-enterprise-dfir-report-the-top-trends-shaping-digital-investigations-in-2026)
- Implement Best Practices for Effective Incident Response
- How to Build an Effective Cyber Incident Response Plan for 2026 (https://cm-alliance.com/cybersecurity-blog/how-to-build-an-effective-cyber-incident-response-plan)
- Incident Response Statistics: How Do You Compare? | FRSecure (https://frsecure.com/blog/incident-response-statistics-how-do-you-compare)
- CISA Shares Lessons Learned from an Incident Response Engagement | CISA (https://cisa.gov/news-events/cybersecurity-advisories/aa25-266a)
- Cybersecurity Best Practices That Actually Work in 2026 (https://linkedin.com/pulse/cybersecurity-best-practices-actually-work-2026-urtif)
- Top 10 Incident Management Best Practices For IT Teams 2026 (https://cyble.com/knowledge-hub/top-10-incident-management-best-practices)
- Ensure Continuous Training and Assessment
- Incident Response Training for Security Teams | Sygnia (https://sygnia.co/blog/incident-response-training)
- Managing Cyber Risk in 2026 With Incident Response Training and Drills (https://cm-alliance.com/cybersecurity-blog/managing-cyber-risk-in-2026-with-incident-response-training-and-drills)
- Why Cybersecurity Training is the Smartest Investment for Organization in 2026 (https://uscsinstitute.org/cybersecurity-insights/blog/why-cybersecurity-training-is-the-smartest-investment-for-organization-in-2026)
- Incident Response Training | CISA (https://cisa.gov/resources-tools/programs/Incident-Response-Training)
- Top 7 Cybersecurity Incident Response Training Platforms in 2026 (https://uptimelabs.io/learn/best-cybersecurity-incident-response-training-platforms)