Introduction
The landscape of cloud service security is increasingly complex, as organizations encounter mounting pressure to comply with stringent federal standards. Central to this challenge is the critical role of Third-Party Assessment Organizations (3PAOs). Their audits not only validate compliance but also enhance the security posture of cloud service providers. However, navigating the intricacies of the 3PAO audit process can be daunting.
What are the essential steps, and how can organizations prepare effectively to ensure a successful outcome? This article explores the key components of mastering the 3PAO audit, offering invaluable insights and best practices for organizations aiming to safeguard sensitive data and strengthen their compliance efforts.
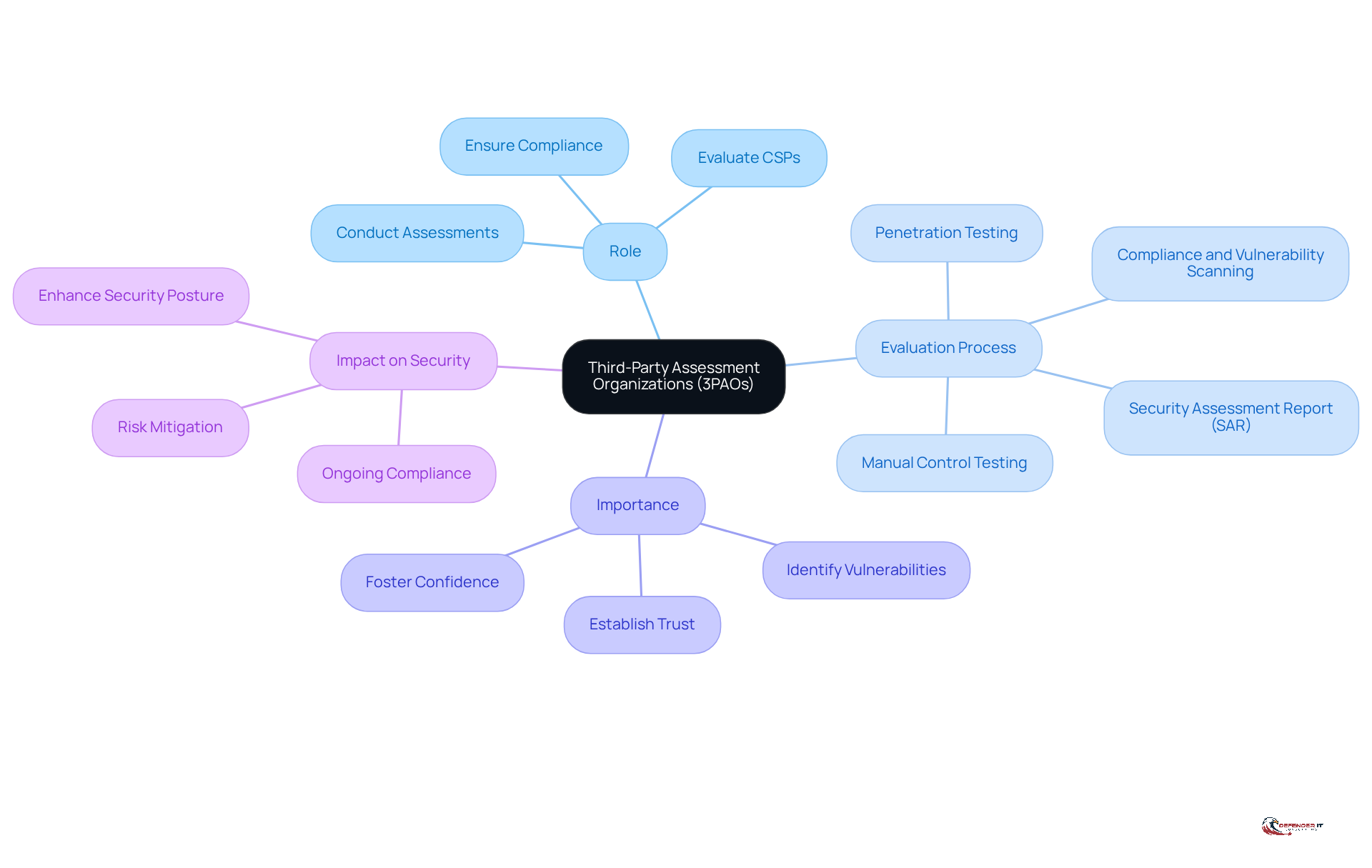
Define Third-Party Assessment Organizations (3PAOs) and Their Importance
Third-Party Assessment Organizations (3PAOs) serve as independent entities accredited by the FedRAMP Program Management Office. Their primary role is to evaluate cloud service providers (CSPs) for compliance with federal protection standards. By conducting thorough assessments of a CSP’s protective measures, the 3PAO audit ensures that these providers meet the essential criteria required for FedRAMP authorization.
This evaluation process is critical in establishing trust and credibility in the protection of cloud services, particularly for organizations that handle sensitive government data. Through impartial assessments, the 3PAO audit helps organizations and improve their overall security posture. This not only aids in compliance but also fosters confidence in the integrity of cloud services utilized by federal entities.
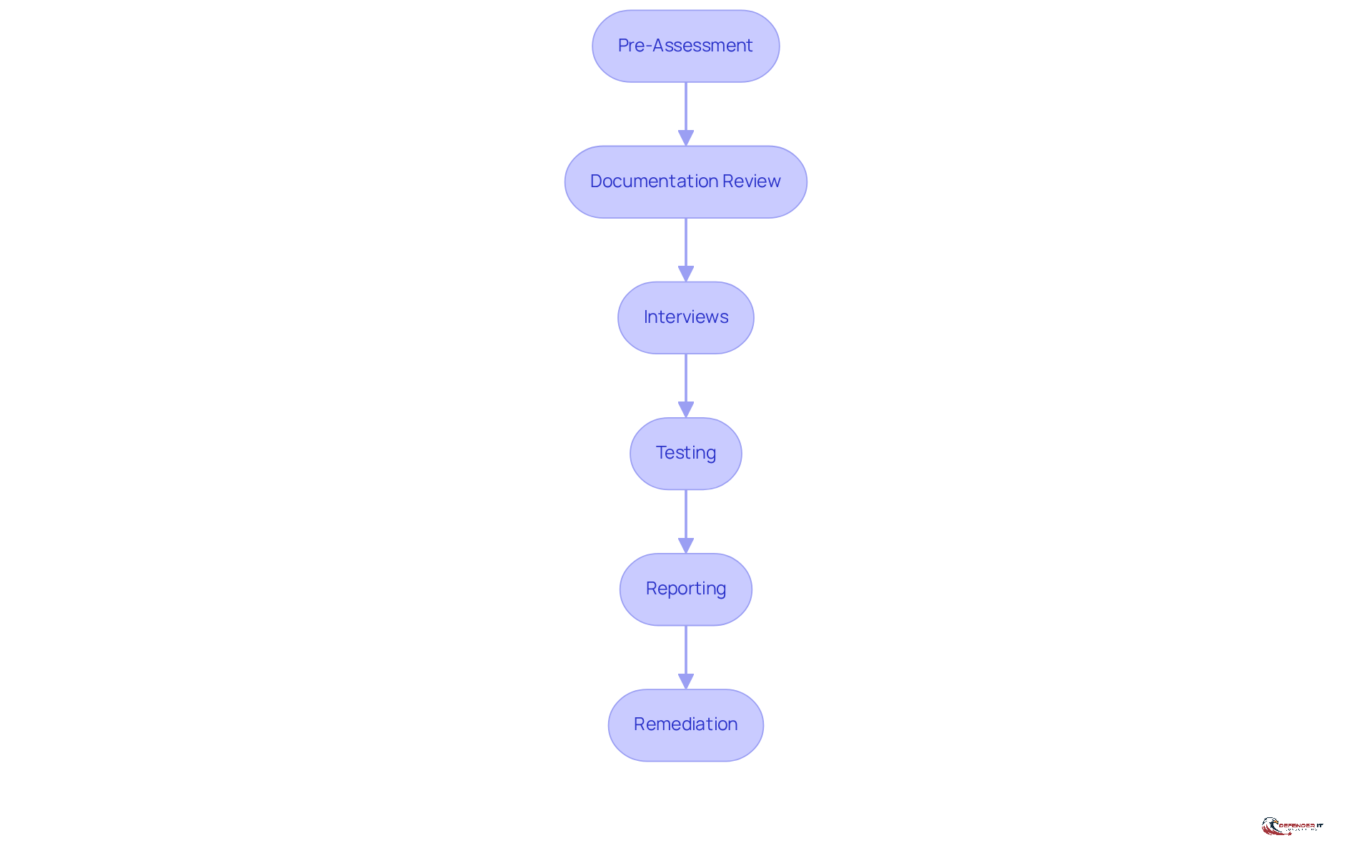
Outline the Steps in the 3PAO Audit Process
The 3PAO audit process consists of several key steps designed to ensure a thorough evaluation and compliance with federal security requirements:
- Pre-Assessment: Organizations begin the process with a self-assessment to identify potential compliance gaps, laying the groundwork for a successful audit.
- Documentation Review: The 3PAO conducts a meticulous examination of the organization’s System Security Plan (SSP), Security Assessment Plan (SAP), and Readiness Assessment Report (RAR) to verify their completeness and accuracy, ensuring that all necessary information is present.
- Interviews: Key personnel are interviewed to gain insights into the implementation of protective measures, providing essential context and clarity to the documentation.
- Testing: This phase involves conducting vulnerability scans and penetration assessments to evaluate the effectiveness of current protective measures. By simulating real-world cyber threats, this testing validates the strength of defenses under pressure, making penetration testing a critical component.
- Reporting: Findings are compiled into a Security Assessment Report (SAR), detailing the organization’s adherence status and highlighting any identified vulnerabilities that require attention.
- Remediation: Organizations must address any issues outlined in the SAR before proceeding with the FedRAMP authorization process, ensuring that all risks are effectively mitigated.
The duration of a 3PAO audit can vary significantly. Simple evaluations may be completed in a few weeks, while more complex environments might require additional time to ensure a comprehensive assessment and adherence. This variability is influenced by the complexity of the organization’s security environment and the resources available.
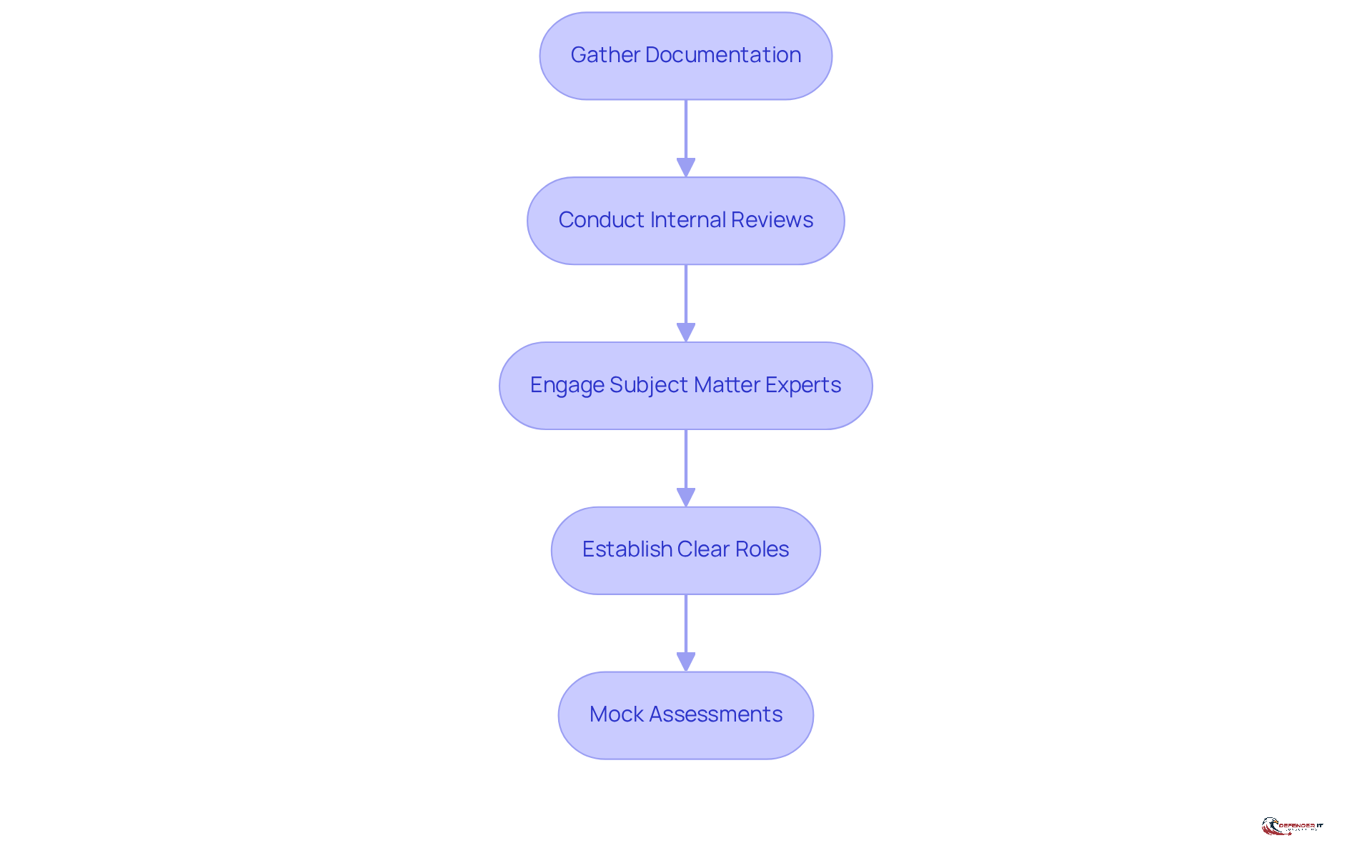
Prepare for the 3PAO Audit: Documentation and Readiness
Preparation for a 3PAO audit is essential, involving several critical steps to ensure compliance and readiness:
- Gather Documentation: Compile all necessary documents, including the System Security Plan (SSP), Incident Response Plan, and relevant policies. Keeping these documents current and readily available is vital for a seamless review process. Organizations that maintain comprehensive records are 30% more likely to succeed in their evaluations on the first attempt.
- Conduct Internal Reviews: Perform thorough internal audits to identify and address any regulatory gaps before the 3PAO assessment. Ongoing observation is crucial for upholding regulations and safeguarding against emerging threats. A case study from Optro indicates that companies conducting regular internal reviews reduced their compliance gaps by 40% prior to their 3PAO assessments.
- Engage Subject Matter Experts (SMEs): Ensure that SMEs are present during the evaluation to address technical inquiries. Their expertise can significantly enhance the credibility of your documentation and responses. As Shehan Jayakody, Director of ITRC Advisory at Optro, notes, “By meticulously evaluating CSPs’ security measures, 3PAOs help uncover vulnerabilities and protect sensitive data.”
- Establish Clear Roles: Clearly define responsibilities for each team member involved in the evaluation process. This clarity fosters effective communication and operational efficiency throughout the evaluation.
- Mock Assessments: Conduct practice evaluations to familiarize your team with the evaluation process. These mock assessments can help and build confidence in your team’s preparedness. A structured mock assessment can lead to a 25% increase in team readiness, as evidenced by organizations that have implemented this practice.
For a successful 3PAO audit, documentation readiness is paramount. Organizations prioritizing thorough documentation and internal reviews are better positioned to meet the stringent compliance standards set by frameworks like FedRAMP. By applying best practices and leveraging technology, businesses can enhance their regulatory efforts, transforming potential challenges into strategic advantages.
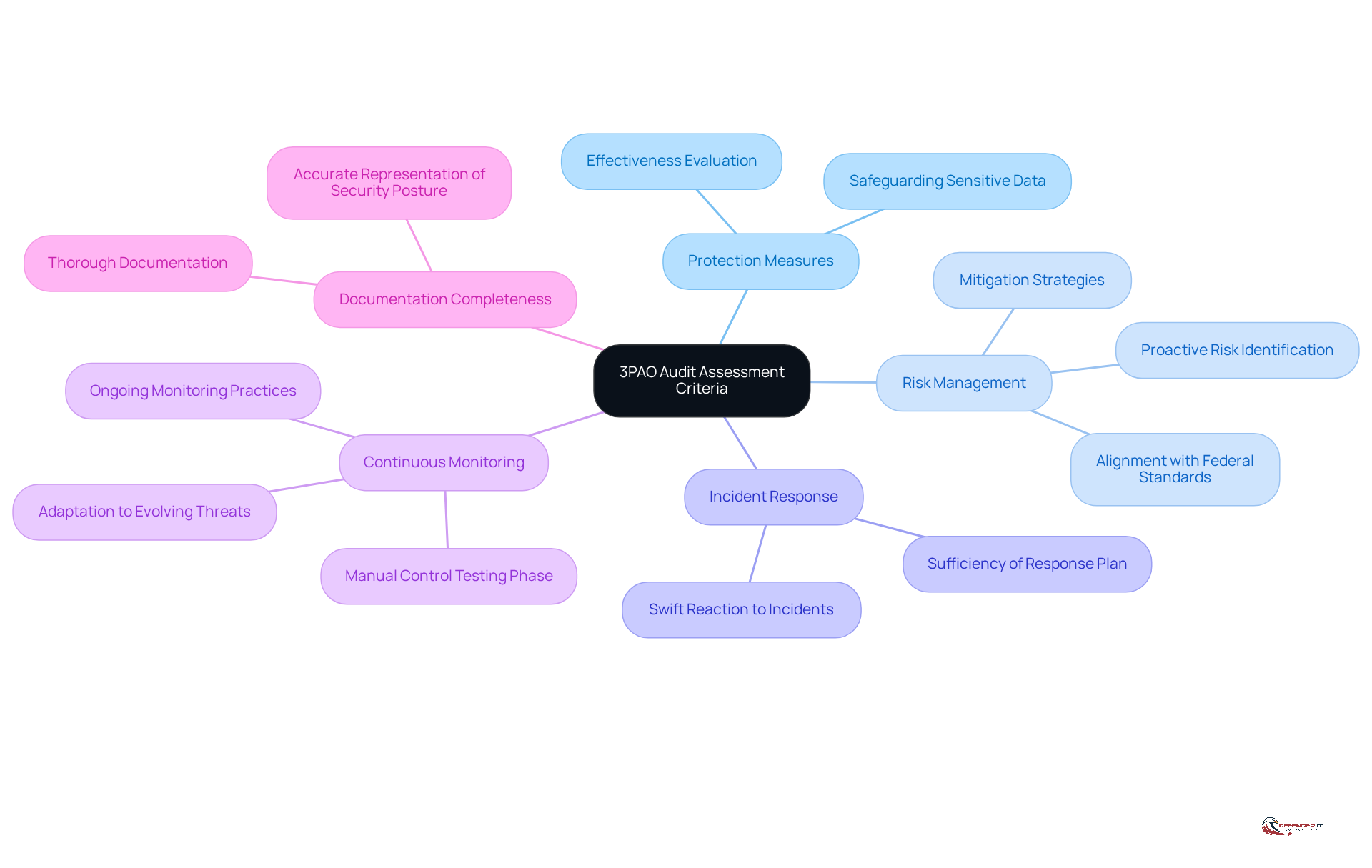
Evaluate and Validate: Key Assessment Criteria in the 3PAO Audit
During the 3PAO audit, several critical assessment criteria are evaluated to ensure compliance with FedRAMP standards and enhance overall security posture:
- Protection Measures: The effectiveness of implemented protection measures is rigorously evaluated against FedRAMP requirements, ensuring they adequately safeguard sensitive data.
- Risk Management: Organizations’ risk management practices are assessed to confirm alignment with federal standards, emphasizing the necessity of proactive risk identification and mitigation strategies. Investing in risk management is essential for any business to effectively mitigate risks.
- Incident Response: The sufficiency of the incident response plan is evaluated, ensuring that organizations can react swiftly and efficiently to incidents, thereby reducing potential harm.
- Continuous Monitoring: The 3PAO audit checks for ongoing monitoring practices, which are essential for maintaining the effectiveness of protective measures over time and adapting to evolving threats. Assessors spend several weeks reviewing protective measures during the Manual Control Testing phase, highlighting the thoroughness of this process.
- Documentation Completeness: All necessary documentation must be thorough and accurately represent the entity’s security posture, as this is vital for demonstrating compliance and aiding the evaluation process.
These criteria not only assist in identifying weaknesses but also ensure that entities are well-prepared to defend against cyber threats, which are anticipated to rank as a significant concern. The 3PAO audit is essential for ensuring compliance.
Post-Audit Actions: Reporting and Continuous Improvement
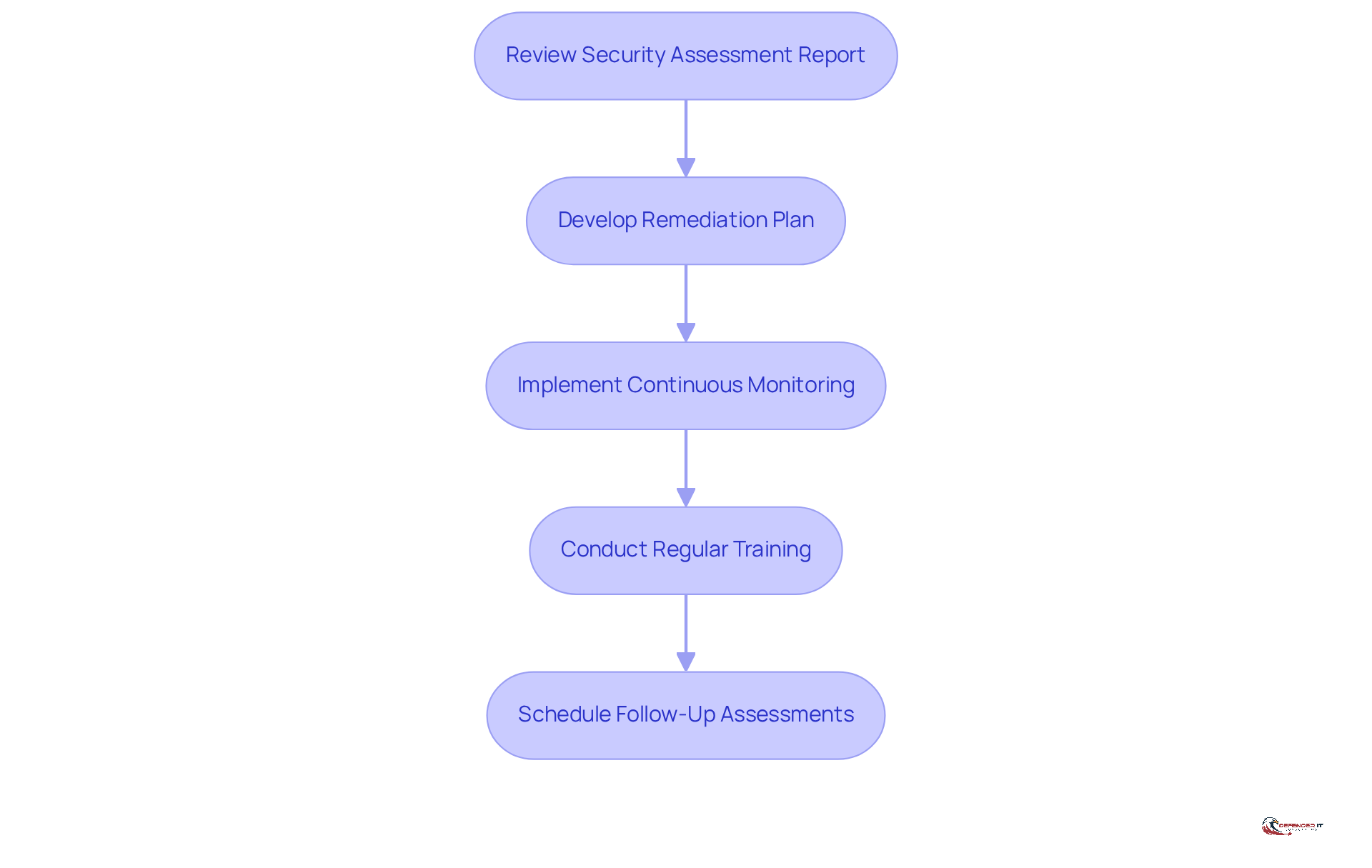
After the 3PAO audit, organizations should take the following actions:
- Review the Security Assessment Report (SAR): Analyze the findings and recommendations provided by the 3PAO. This document serves as a roadmap for addressing vulnerabilities and regulatory gaps.
- Develop a Remediation Plan: Address any identified vulnerabilities or compliance gaps as outlined in the SAR. This plan should prioritize actions based on the severity of the issues highlighted in the report, particularly considering the operational pressures imposed by the updated AS 1215, which reduces the deadline for completing audit workpapers from 45 days to 14 days.
- Implement Continuous Monitoring: Establish ongoing monitoring practices to ensure that protective measures remain effective and compliant over time. This involves regular evaluations of protective measures and adjustments to new threats as they arise.
- Conduct Regular Training: Provide continuous training for staff to ensure they are informed of guidelines and procedures. This training should be updated regularly to reflect changes in the safety environment and organizational protocols.
- Schedule Follow-Up Assessments: Plan for regular assessments to maintain compliance and adapt to evolving security threats. These assessments help ensure that remediation efforts are effective and that the entity remains resilient against potential cyber threats.
Statistics indicate that organizations often take significant time to implement remediation plans post-audit, with many exceeding 13 weeks to rotate passwords alone. This underscores the importance of to effectively mitigate risks. Furthermore, it is crucial to document all actions taken as part of the monitoring and remediation process, as emphasized by the necessity of compliance with documentation standards outlined in AS 2901.
Conclusion
Mastering the 3PAO audit process is crucial for organizations aiming to comply with federal security standards and enhance their cybersecurity posture. Understanding the pivotal role of Third-Party Assessment Organizations (3PAOs) in evaluating cloud service providers enables organizations to navigate the complexities of the audit process more effectively, ultimately safeguarding sensitive data.
This tutorial outlined the structured steps involved in the 3PAO audit, encompassing:
- Pre-assessment
- Documentation review
- Testing
- Remediation
It underscored the significance of thorough preparation, including the engagement of subject matter experts and the execution of mock assessments, which can greatly improve the chances of a successful outcome. Furthermore, the article highlighted the critical assessment criteria evaluated during the audit, such as:
- Protection measures
- Risk management
- Incident response capabilities
In summary, the importance of the 3PAO audit transcends mere compliance; it serves as a vital mechanism for protecting sensitive information against cyber threats. Organizations are urged to adopt a proactive stance by implementing continuous monitoring and regular training, ensuring resilience in the face of evolving security challenges. By committing to these best practices, organizations can transform the 3PAO audit from a regulatory obligation into a strategic advantage, fostering trust and confidence in their cloud services.
Frequently Asked Questions
What are Third-Party Assessment Organizations (3PAOs)?
Third-Party Assessment Organizations (3PAOs) are independent entities accredited by the FedRAMP Program Management Office that evaluate cloud service providers (CSPs) for compliance with federal protection standards.
Why are 3PAOs important?
3PAOs are crucial for establishing trust and credibility in the protection of cloud services, especially for organizations handling sensitive government data. Their impartial assessments help identify vulnerabilities, improve security posture, and foster confidence in the integrity of cloud services used by federal entities.
What are the steps involved in the 3PAO audit process?
The 3PAO audit process includes the following steps:
- Pre-Assessment: Organizations conduct a self-assessment to identify compliance gaps.
- Documentation Review: The 3PAO reviews the System Security Plan (SSP), Security Assessment Plan (SAP), and Readiness Assessment Report (RAR) for completeness and accuracy.
- Interviews: Key personnel are interviewed to gain insights into the implementation of protective measures.
- Testing: Vulnerability scans and penetration assessments are conducted to evaluate the effectiveness of protective measures.
- Reporting: Findings are compiled into a Security Assessment Report (SAR) detailing adherence status and vulnerabilities.
- Remediation: Organizations address issues identified in the SAR before proceeding with FedRAMP authorization.
How long does a 3PAO audit take?
The duration of a 3PAO audit can vary significantly. Simple evaluations may take a few weeks, while more complex environments might require additional time for a comprehensive assessment, influenced by the complexity of the security environment and compliance thoroughness.
List of Sources
- Define Third-Party Assessment Organizations (3PAOs) and Their Importance
- The Ultimate Guide to the 3PAO Assessment (https://optro.ai/blog/3pao-assessment)
- What It Means to Be a FedRAMP 3PAO: Insight Assurance’s Next Step in Supporting Secure Federal Cloud Adoption (https://insightassurance.com/insights/blog/what-it-means-to-be-a-fedramp-3pao-insight-assurances-next-step-in-supporting-secure-federal-cloud-adoption)
- All You Ever Wanted to Know About FedRAMP 3PAOs (https://zengrc.com/blog/what-is-fedramp-3pao)
- What is a third party assessment organization (3PAO)? (https://help.fedramp.gov/hc/en-us/articles/27704392312347-What-is-a-third-party-assessment-organization-3PAO)
- Outline the Steps in the 3PAO Audit Process
- The Ultimate Guide to the 3PAO Assessment (https://optro.ai/blog/3pao-assessment)
- FedRAMP 3PAO Assessment Services (https://coalfire.com/services/assessment)
- What It Means to Be a FedRAMP 3PAO: Insight Assurance’s Next Step in Supporting Secure Federal Cloud Adoption (https://insightassurance.com/insights/blog/what-it-means-to-be-a-fedramp-3pao-insight-assurances-next-step-in-supporting-secure-federal-cloud-adoption)
- Prepare for the 3PAO Audit: Documentation and Readiness
- The Ultimate Guide to the 3PAO Assessment (https://optro.ai/blog/3pao-assessment)
- 3PAO Assessment Preparation Strategies for a Smooth Audit | Cadra posted on the topic | LinkedIn (https://linkedin.com/posts/cadra-compliance_securitycompliance-auditpreparation-cyberrisk-activity-7435337749139824640-a_s9)
- Evaluate and Validate: Key Assessment Criteria in the 3PAO Audit
- The Ultimate Guide to the 3PAO Assessment (https://optro.ai/blog/3pao-assessment)
- Risk Management Quotes by Warren Buffett, Keynes, and More | Seno Teguh Kuncoro posted on the topic | LinkedIn (https://linkedin.com/posts/seno-kuncoro_riskmanagement-quotes-activity-7380884593018802176-fcML)
- 50 Risk Management Quotes: Wisdom for Smart Decision-making | ITD World (https://itdworld.com/blog/leadership/risk-management-quotes)
- azquotes.com (https://azquotes.com/quotes/topics/risk-management.html)
- Post-Audit Actions: Reporting and Continuous Improvement
- What to know about the new PCAOB auditing standards for 2026 (https://tax.thomsonreuters.com/blog/what-to-know-about-the-new-pcaob-auditing-standards)
- mark43.com (https://mark43.com/press/solutions-review-cybersecurity-awareness-month-quotes-from-industry-experts-in-2024)