Introduction
Organizations struggle to navigate the complexities of cybersecurity threats, making the selection of a penetration testing service provider a critical decision. To make informed decisions, organizations should explore best practices for selecting penetration testing service providers, focusing on:
- Defining clear objectives
- Emphasizing manual testing
- Aligning findings with business impacts
Choosing the right provider is not just about compliance; it is about safeguarding the organization’s future.
Define Clear Objectives and Scope Upfront
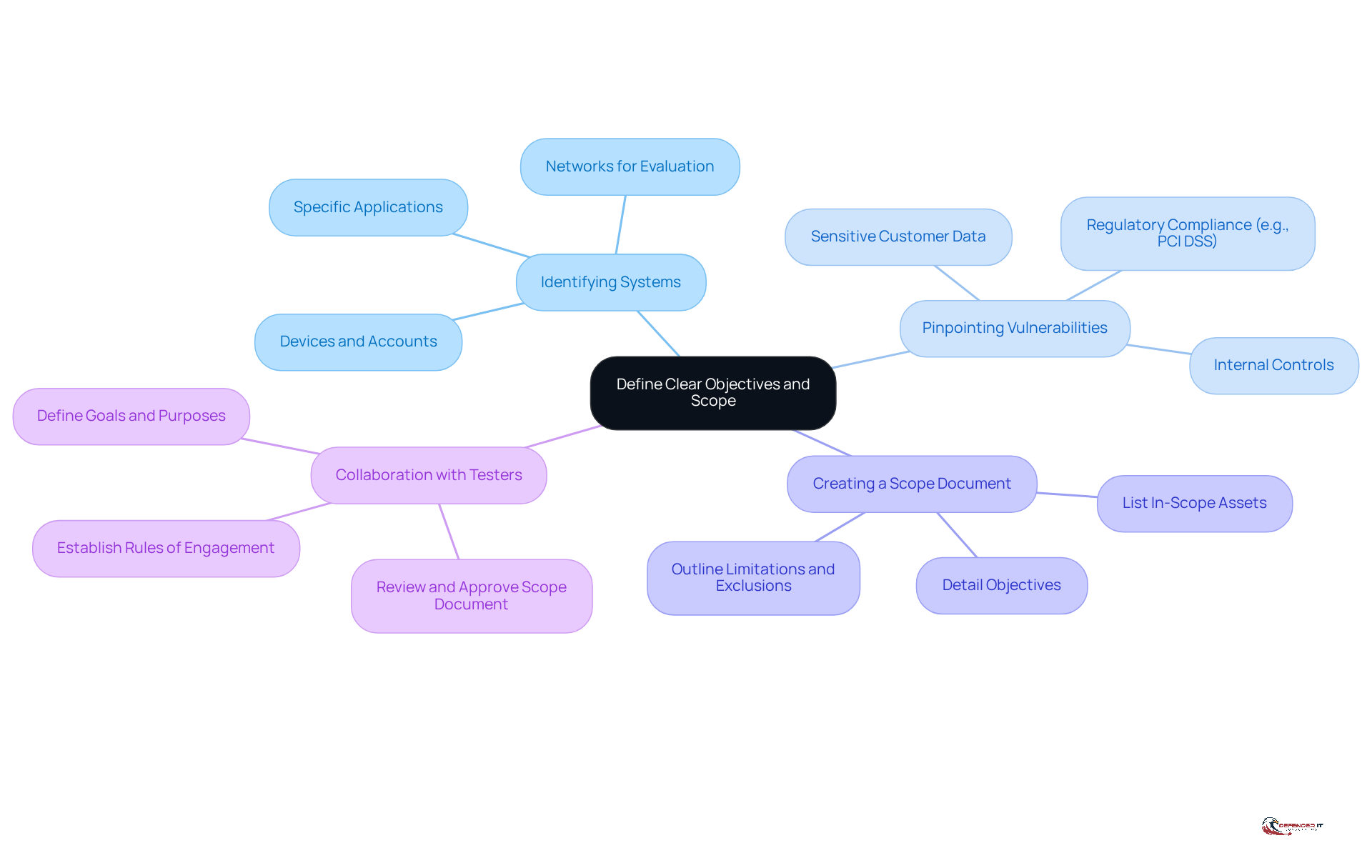
Before engaging pen test service providers, it is essential to establish clear objectives and scope to ensure a focused evaluation. This process involves identifying the specific systems, applications, or networks for evaluation. Additionally, it includes pinpointing vulnerabilities of particular concern. For instance, organizations in the financial sector should prioritize areas that manage sensitive customer data or adhere to regulations such as PCI DSS.
A clearly defined scope prevents scope creep, where additional areas are examined without prior agreement. This can lead to unexpected costs and delays. Furthermore, it enhances communication with the evaluation team. This alignment ensures that all parties understand the goals and expectations of the engagement.
Creating a comprehensive scope document is essential. This document should detail the objectives, list in-scope assets, and outline any limitations or exclusions. It’s important for all stakeholders to review and approve this document before testing begins. A clearly defined scope significantly affects the effectiveness of the assessment performed by pen test service providers, as it outlines the boundaries of the evaluation and assists organizations in achieving their protection goals efficiently. Moreover, collaborating with vulnerability testers during this process is essential. This ensures that the scope aligns with the organization’s protection objectives and compliance requirements.
Choose Providers That Emphasize Manual Testing
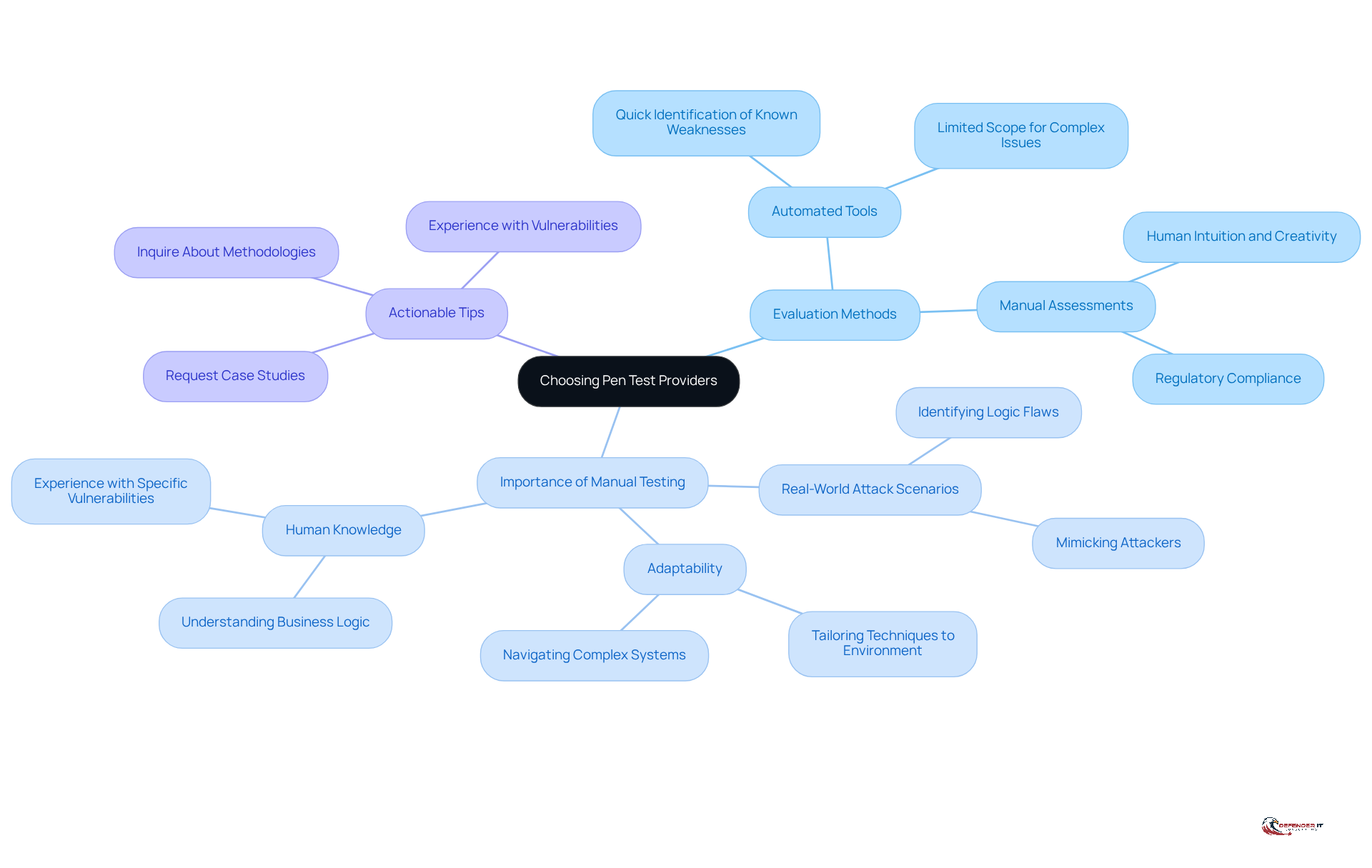
Choosing a pen test service providers requires careful consideration of their evaluation methods, particularly the emphasis on manual assessments. While automated tools can quickly identify known weaknesses, they often miss complex issues that demand human intuition and creativity. For entities in regulated sectors, manual penetration evaluation is essential for regulatory compliance, ensuring a thorough assessment of protective measures.
Manual testers are adept at mimicking real-world attack scenarios, allowing them to adjust their techniques based on the specific environment and potential threat vectors. This adaptability is vital for uncovering vulnerabilities that automated tools may overlook, including logic flaws or misconfigurations specific to your organization. Furthermore, human participation in security evaluation is crucial, as tools are only as effective as the knowledge behind them.
Actionable Tip: Ask potential providers about their evaluation methodologies, particularly how they balance automated and manual assessments. Additionally, inquire about their experience with specific vulnerabilities, such as logic flaws or session handling, which are challenging for automated tools. Request case studies or examples demonstrating the manual testing capabilities of pen test service providers to ensure you select a provider that can effectively meet your security needs while considering the financial advantages of thorough manual assessments. Ultimately, the right provider will not only enhance your security posture but also safeguard your organization from potential financial repercussions.
Align Findings with Business Impact and Actionable Remediation
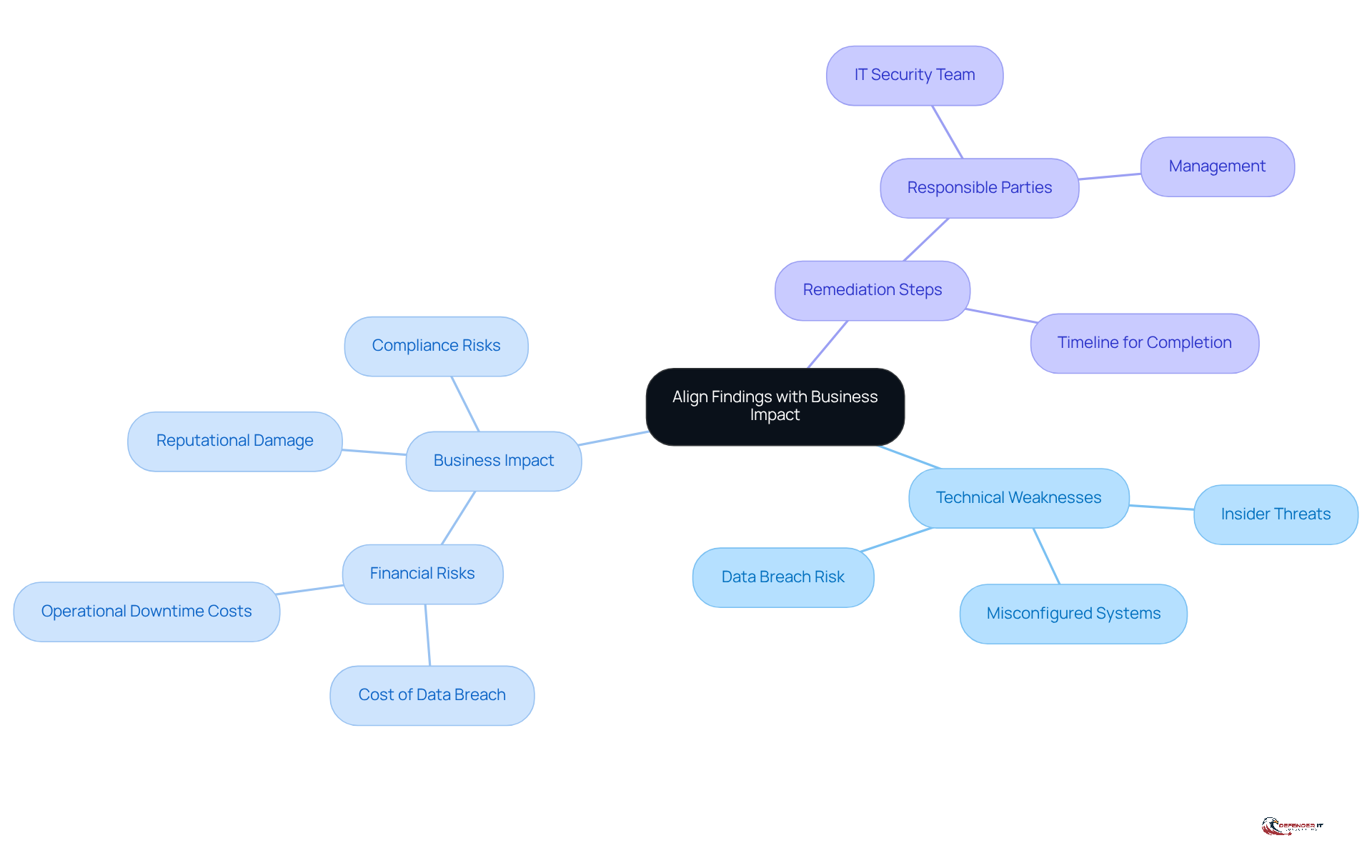
Aligning penetration test findings with business impact is essential for effective risk management. This involves translating technical weaknesses into comprehensible terms for stakeholders, emphasizing potential impacts on operations, reputation, and compliance, supported by relevant data. For example, a vulnerability that could result in a data breach of sensitive customer information poses significant financial risks, with the average cost of such breaches reaching $4.4 million in 2024, alongside potential reputational damage.
Additionally, it is important to provide clear, prioritized remediation steps for effectively addressing each identified weakness. Developing a report that categorizes weaknesses based on their potential business impact is essential. This report should include:
- A remediation plan that specifies who is responsible for addressing each issue.
- A timeline for completion.
Conducting regular safety briefings for the C-suite and board of directors can significantly improve communication strategies and prioritize security measures. By prioritizing vulnerabilities in a business context, organizations can significantly mitigate risks and enhance their security posture.
Build Strong Communication and Collaboration
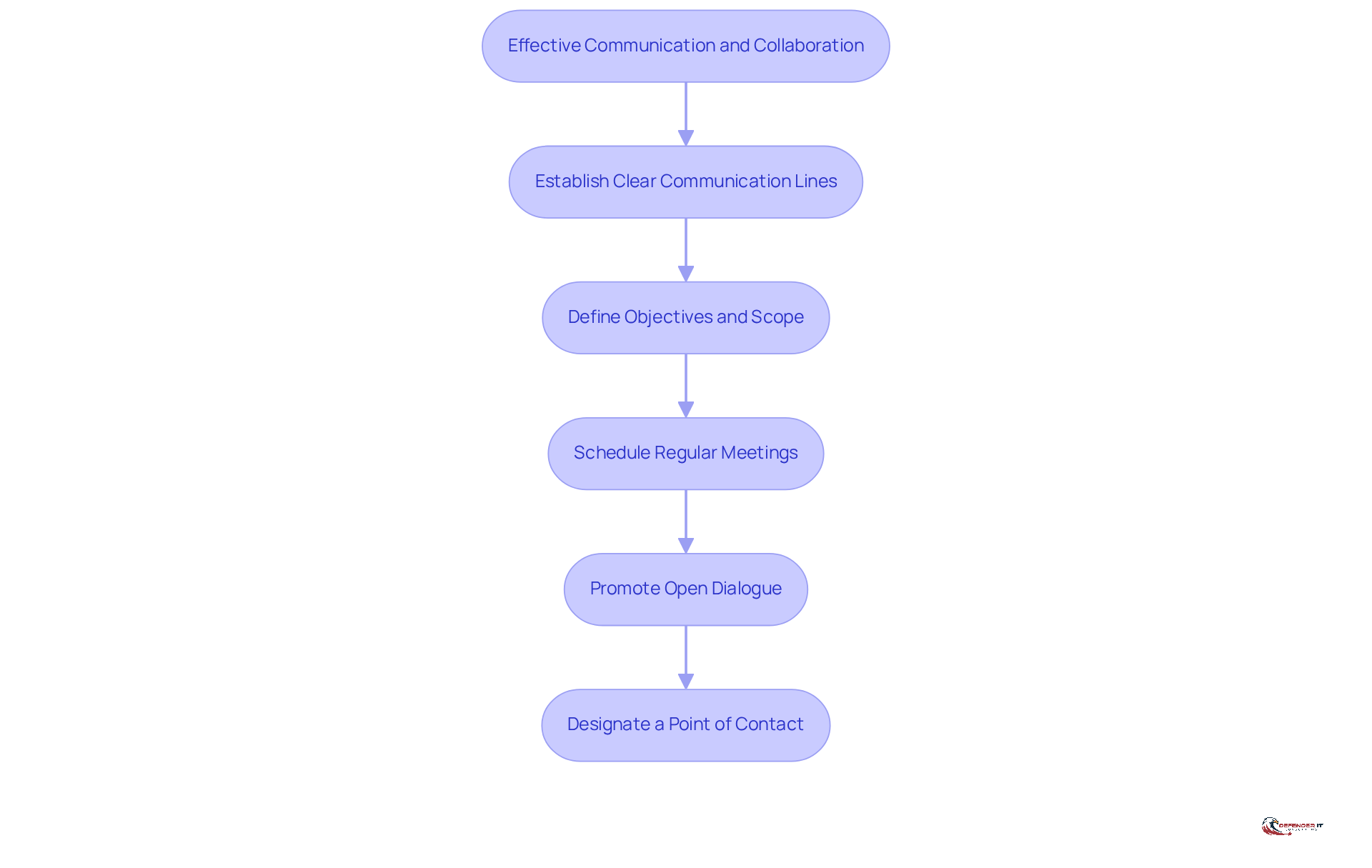
Effective penetration examinations hinge on robust communication and collaboration between organizations and assessment teams. This requires establishing clear communication lines and defining objectives and scope to guide the engagement. Regular updates ensure the evaluation team has the necessary information for a thorough assessment. Promoting open dialogue allows for real-time feedback and adjustments to the evaluation approach. A designated point of contact within your organization is crucial for coordinating with pen testers and ensuring smooth communication. Such collaboration enhances [[[[[vulnerability identification and contextual understanding](https://defenderit.consulting/4-best-practices-for-effective-vulnerability-scanning-solutions/)](https://plurilock.com/blog/uncovering-hidden-threats-the-crucial-role-of-penetration-testing-in-cybersecurity)](https://plurilock.com/blog/uncovering-hidden-threats-the-crucial-role-of-penetration-testing-in-cybersecurity)](https://plurilock.com/blog/uncovering-hidden-threats-the-crucial-role-of-penetration-testing-in-cybersecurity)](https://plurilock.com/blog/uncovering-hidden-threats-the-crucial-role-of-penetration-testing-in-cybersecurity).
Actionable Tip: Schedule regular meetings with the evaluation team to discuss progress and challenges during the assessment. Encourage an open exchange of ideas and feedback to enhance the overall effectiveness of the engagement, especially when critical issues arise.
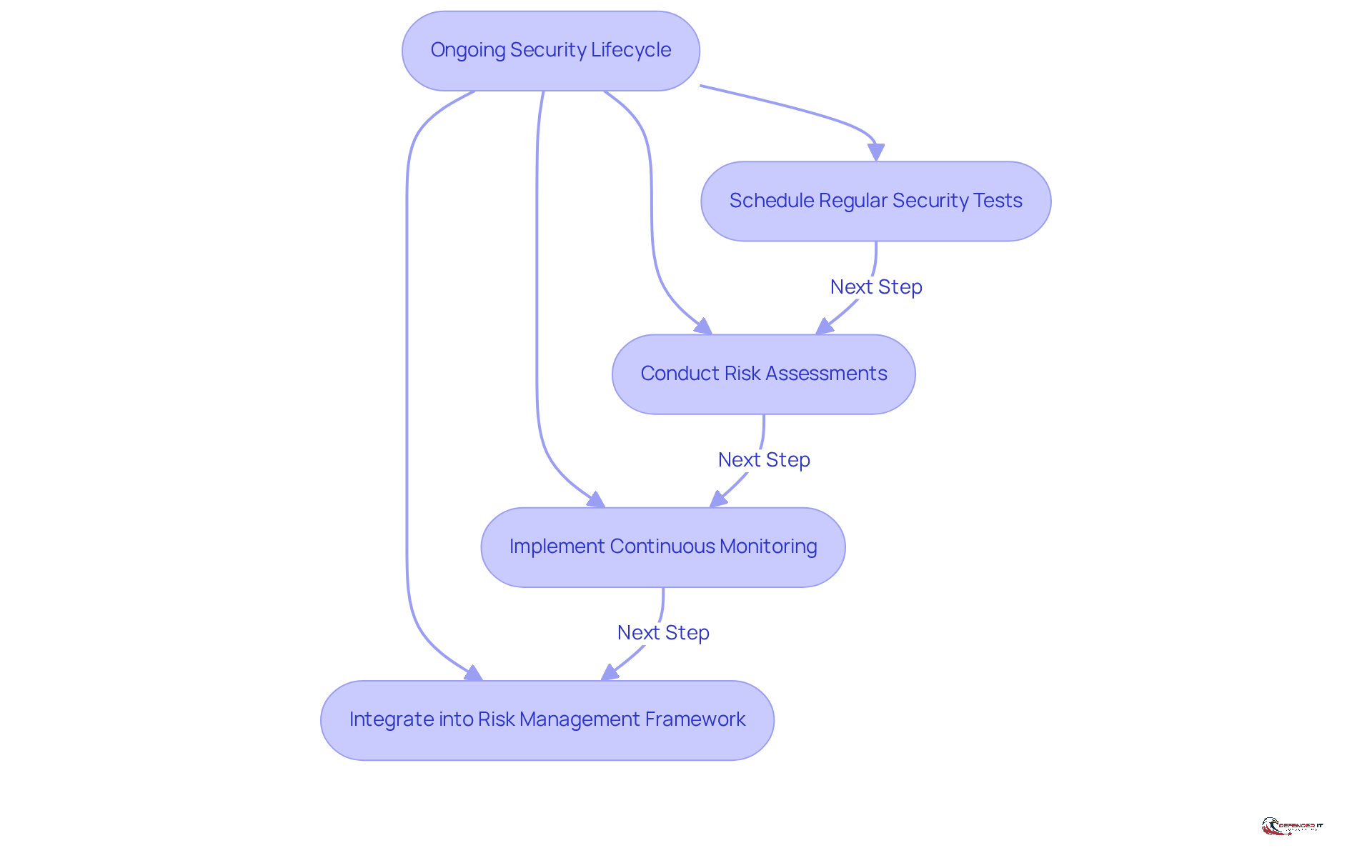
Integrate Testing into Your Ongoing Security Lifecycle
Viewing penetration testing as an ongoing necessity rather than a one-time task is crucial for maintaining robust security. Regularly incorporating security assessments into your strategy is essential for evaluating and enhancing your security posture.
This approach can involve scheduling regular security tests, conducting risk assessments, and implementing continuous monitoring practices. Organizations that conduct assessments only annually or quarterly expose themselves to significant risks. By adopting ongoing assessments, organizations can swiftly identify and mitigate vulnerabilities, reducing their risk exposure.
Statistics indicate that most organizations perform security assessments annually or quarterly, which can leave extended windows of risk. Ongoing security assessments, however, significantly lessen exposure between evaluation cycles, enabling organizations to identify exploitable vulnerabilities more swiftly. Integrating continuous assessments into your security strategy not only fortifies defenses but also positions your organization to respond proactively to emerging threats.
Actionable Tip: Create a timetable for routine penetration evaluations and vulnerability assessments, and incorporate these tasks into your comprehensive risk management framework with the help of pen test service providers. Consider using automated tools for continuous monitoring to complement periodic manual testing, ensuring a comprehensive security strategy.
Conclusion
Selecting the right penetration testing service providers is critical for establishing a robust security posture. Organizations must prioritize clarity in their objectives and scope, ensuring that evaluations are focused and relevant to their specific security needs. This clarity helps companies streamline the testing process and improves communication with assessment teams, leading to better outcomes.
The article outlines several best practices for choosing pen test service providers, including:
- The importance of manual testing
- Aligning findings with business impact
- Fostering strong communication
Emphasizing manual assessments allows for a more nuanced understanding of vulnerabilities, while translating technical findings into business terms ensures that stakeholders comprehend the risks involved. Additionally, integrating penetration testing into an ongoing security lifecycle is crucial for proactive risk management and timely vulnerability mitigation.
In conclusion, organizations must recognize that selecting a penetration testing provider is not merely a checkbox exercise but a strategic decision that significantly impacts their overall security. By implementing these best practices-like defining clear objectives and prioritizing manual testing-businesses can protect their assets more effectively. Ultimately, this strategic decision can fortify an organization’s defenses against evolving threats, ensuring long-term security and stability.
Frequently Asked Questions
Why is it important to define clear objectives and scope before engaging pen test service providers?
Defining clear objectives and scope is crucial to ensure a focused evaluation, prevent scope creep, enhance communication with the evaluation team, and align the assessment with organizational protection goals and compliance requirements.
What should be included in a comprehensive scope document for penetration testing?
A comprehensive scope document should detail the objectives, list in-scope assets, and outline any limitations or exclusions. It is important for all stakeholders to review and approve this document before testing begins.
How does a clearly defined scope affect the effectiveness of a penetration test?
A clearly defined scope significantly affects the effectiveness of the assessment by outlining the boundaries of the evaluation, which helps organizations achieve their protection goals efficiently.
What is the advantage of choosing pen test service providers that emphasize manual testing?
Providers that emphasize manual testing can identify complex vulnerabilities that automated tools may miss, as manual testers can mimic real-world attack scenarios and adapt their techniques based on the specific environment and threat vectors.
Why is human participation crucial in security evaluations?
Human participation is crucial because tools are only as effective as the knowledge behind them, and manual testers can uncover vulnerabilities such as logic flaws or misconfigurations that automated tools often overlook.
What should organizations inquire about when selecting a pen test service provider?
Organizations should ask potential providers about their evaluation methodologies, how they balance automated and manual assessments, their experience with specific vulnerabilities, and request case studies or examples demonstrating their manual testing capabilities.
How can choosing the right pen test provider impact an organization?
The right provider can enhance an organization’s security posture and safeguard it from potential financial repercussions by ensuring a thorough and effective assessment of protective measures.
List of Sources
- Define Clear Objectives and Scope Upfront
- Why Defining Penetration Testing Scope is Important? – ASTRA (https://getastra.com/blog/penetration-testing/scope)
- Why is the Scope of a Penetration Test so Important? » Triaxiom Security (https://triaxiomsecurity.com/blog/why-is-the-scope-of-a-penetration-test-so-important)
- The Importance of a Clearly Defined Pentesting Scope (https://guidepointsecurity.com/blog/the-importance-of-a-clearly-defined-pentesting-scope)
- How to Plan and Prepare for Penetration Testing (https://thehackernews.com/2024/09/how-to-plan-and-prepare-for-penetration.html)
- Penetration testing best practices: Strategies for all test types (https://strikegraph.com/blog/pen-testing-best-practices)
- Choose Providers That Emphasize Manual Testing
- The Future of Manual Security Testing – PlexTrac (https://plextrac.com/the-future-of-manual-security-testing)
- 7 Reasons Why You Need a Manual Penetration Test (https://kirkpatrickprice.com/blog/7-reasons-why-you-need-a-manual-penetration-test)
- Why Manual Penetration Testing Yields Better Results (https://serabrynn.com/resources/why-manual-pen-tests-yield-better-results)
- The Value of Manual Penetration Testing – Beyond Automated Scans | EliteSec Blog (https://elitesec.io/blog/manual-penetration-testing)
- Why Manual Testing Still Matters in an AI World | ImpactQA (https://impactqa.com/blog/why-manual-testing-still-matters-in-an-ai-world-how-to-modernize-it)
- Align Findings with Business Impact and Actionable Remediation
- Annual Penetration Testing Is a Business Advantage – Drummond Group (https://drummondgroup.com/blog/annual-penetration-testing-is-a-business-advantage)
- Spot Risks With Penetration Testing Services | Northern Technologies Group (https://ntgit.com/penetration-testing-services-spot-risks-before-they-disrupt-your-business)
- How to Communicate the Business Impact of Vulnerabilities | Cobalt (https://cobalt.io/blog/how-to-communicate-the-business-impact-of-vulnerabilities)
- Aligning Offensive Testing With Business Risk – Canary Trap (https://canarytrap.com/blog/offensive-testing)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Build Strong Communication and Collaboration
- Communication Skills are Critical for Successful Pentesting (https://softsideofcyber.com/why-communication-is-your-most-undervalued-skill-as-a-pentester)
- Uncovering Hidden Threats: The Crucial Role of Penetration Testing in Cybersecurity – Plurilock (https://plurilock.com/blog/uncovering-hidden-threats-the-crucial-role-of-penetration-testing-in-cybersecurity)
- The Role of Collaboration and Communication in the Success of a Pentest Team (https://siemba.io/blogs/the-role-of-collaboration-and-communication-in-the-success-of-a-pentest-team)
- The Facts About Continuous Penetration Testing and Why It’s Important (https://thehackernews.com/2024/08/the-facts-about-continuous-penetration.html)
- Navigating Successful Penetration Testing Engagements – Level19 (https://level19.com/navigating-successful-penetration-testing-engagements)
- Integrate Testing into Your Ongoing Security Lifecycle
- Continuous Penetration Testing for Proactive Security (https://bitlyft.com/resources/continuous-penetration-testing-for-proactive-security)
- Integrating Continuous Pentesting into Your DevOps Pipeline: Benefits and Best Practices | SISA Blog (https://sisainfosec.com/blogs/integrating-continuous-pentesting-into-your-devops-pipeline-benefits-and-best-practices)
- XBOW Embeds Continuous, AI-Driven Penetration Testing in the Microsoft Security Ecosystem (https://xbow.com/news/xbow-penetration-testing-microsoft-security-ecosystem)
- Why Continuous Penetration Testing is replacing traditional One-Time Pentests (https://evolvesecurity.com/blog-posts/continuous-penetration-testing-why-one-time-pentests-are-becoming-old-school)
- The 2026 State of Pentesting: How Modern Teams Manage and Deliver Results (https://thehackernews.com/expert-insights/2026/01/the-2026-state-of-pentesting-how-modern.html)