Introduction
In an era where retail businesses increasingly depend on digital transactions, the threat of cyberattacks has become more pronounced. Implementing effective cybersecurity practices is not merely a precaution; it is essential for protecting sensitive customer information and preserving trust. This article explores five critical cybersecurity strategies that retail establishments can adopt to strengthen their defenses against evolving threats. As companies work to enhance their security measures, a pressing question arises: are they doing enough to safeguard themselves and their customers from the persistent risk of cybercrime?
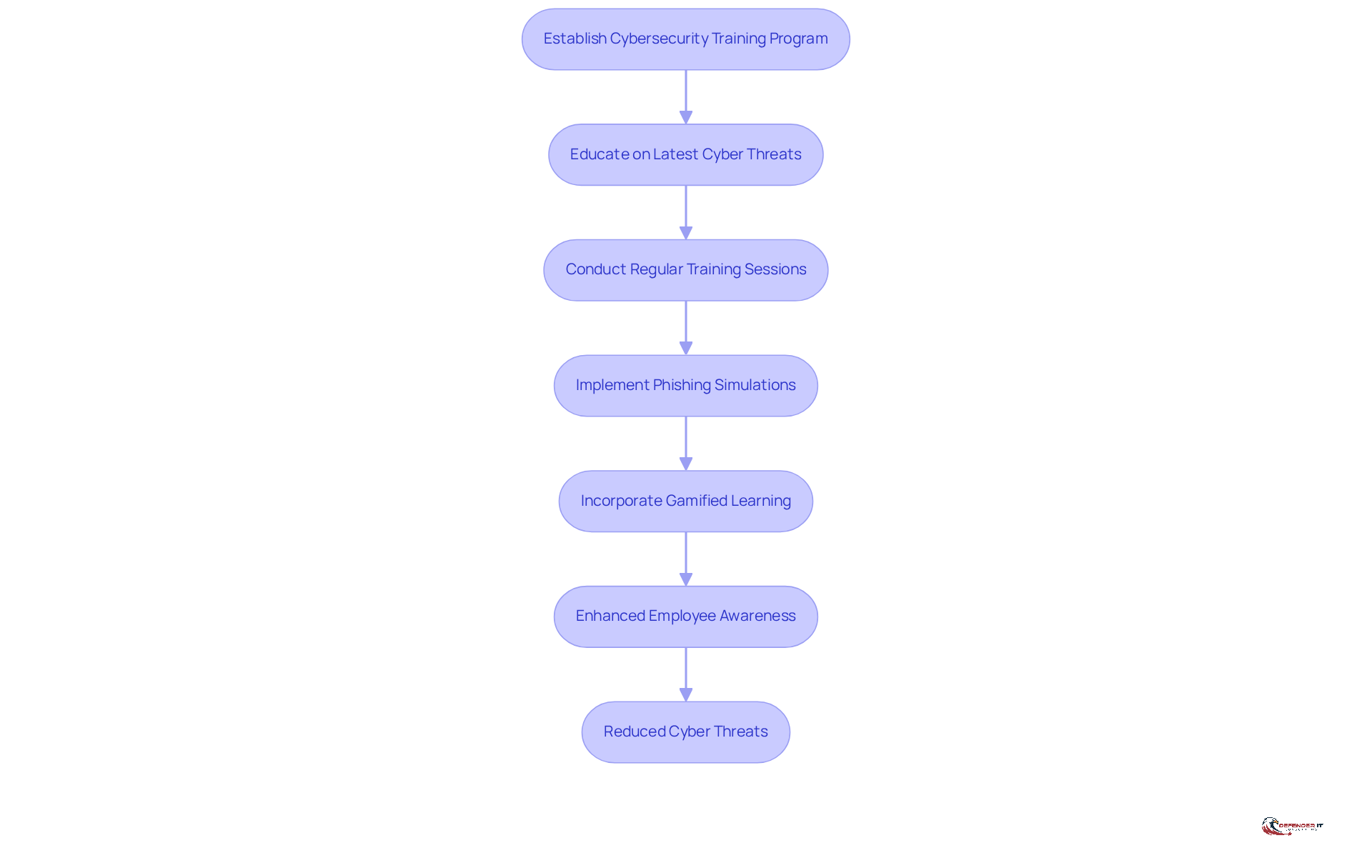
Train Employees on Cybersecurity Principles
Establishing a robust cyber security retail training program is essential for retail establishments. It is imperative that employees are educated on the latest cyber threats, safe online practices, and the critical importance of reporting suspicious activities related to cyber security retail. Regular training sessions, workshops, and simulations significantly enhance their awareness and preparedness.
For example, a retail chain that implemented phishing simulations reported a 40% decrease in successful phishing attempts following employee training on recognizing such threats. This statistic underscores the effectiveness of targeted training initiatives.
Furthermore, incorporating gamified learning experiences can substantially increase engagement and retention of information. Utilizing platforms such as KnowBe4 or Cybrary can provide comprehensive training resources that are both effective and accessible.
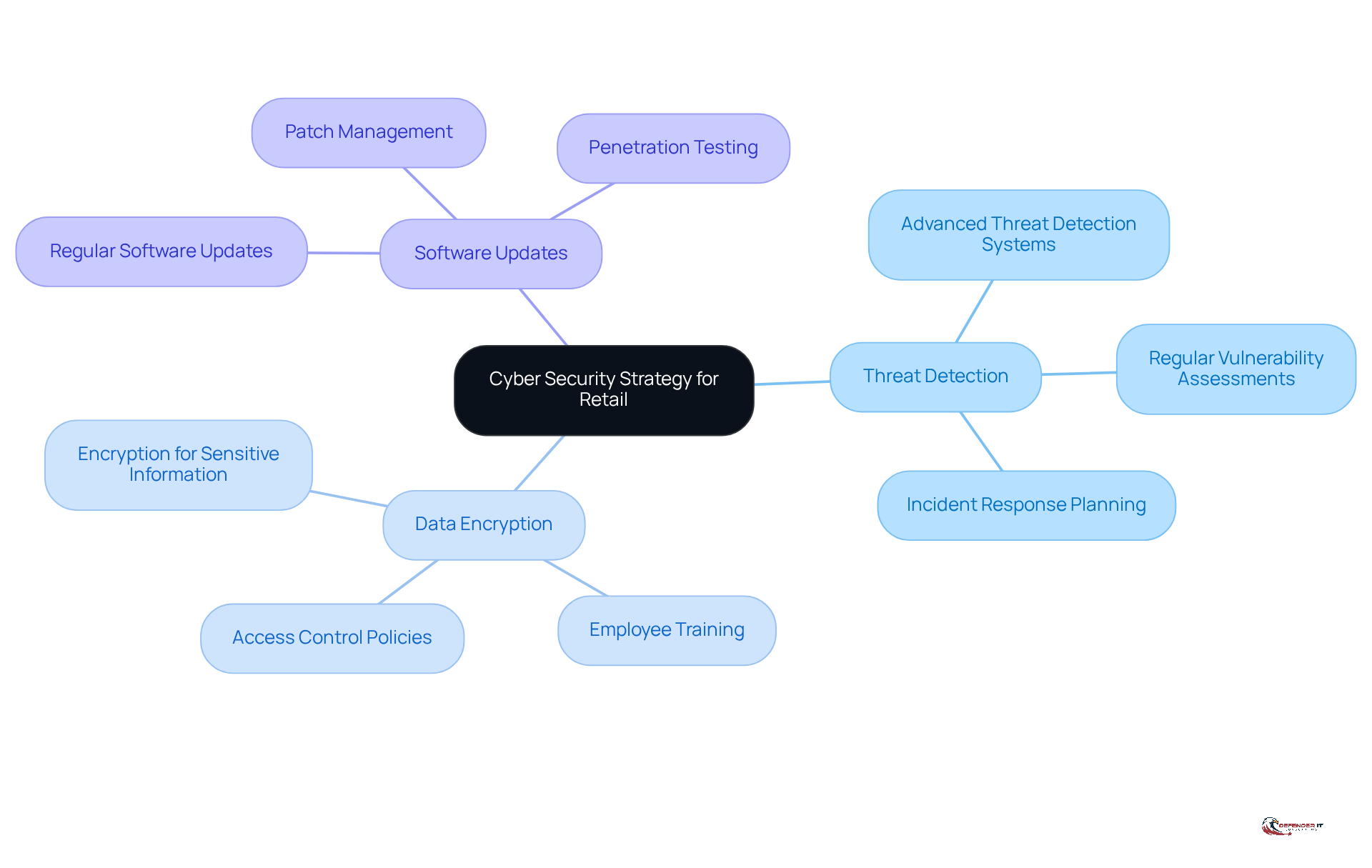
Protect Information and Systems from Cyber Attacks
To safeguard their information and systems, retail businesses must implement a multi-layered cyber security retail strategy. This approach includes:
- Advanced threat detection systems
- Encryption for sensitive information
- Regular software updates to address vulnerabilities
Statistics indicate that 80% of retailers experienced issues related to cyber security retail in the past year, highlighting the urgency of this strategy. For instance, a major retailer that adopted an intrusion detection system (IDS) successfully identified and mitigated a potential breach before any data was compromised.
Additionally, conducting regular vulnerability assessments is crucial for pinpointing weaknesses within the system, enabling prompt remediation and enhancing overall resilience. As Lynne Murray, Director of Product Marketing for Data Protection, states, “For retailers to thrive, it is essential to prioritize robust data protection and create a seamless, privacy-respecting user experience.” Integrating these practices into the core strategy is vital for maintaining a strong defense in cyber security retail against potential attacks.
However, organizations must be mindful of common pitfalls, such as neglecting employee training on protective protocols, which can undermine the effectiveness of their multi-layered approach.
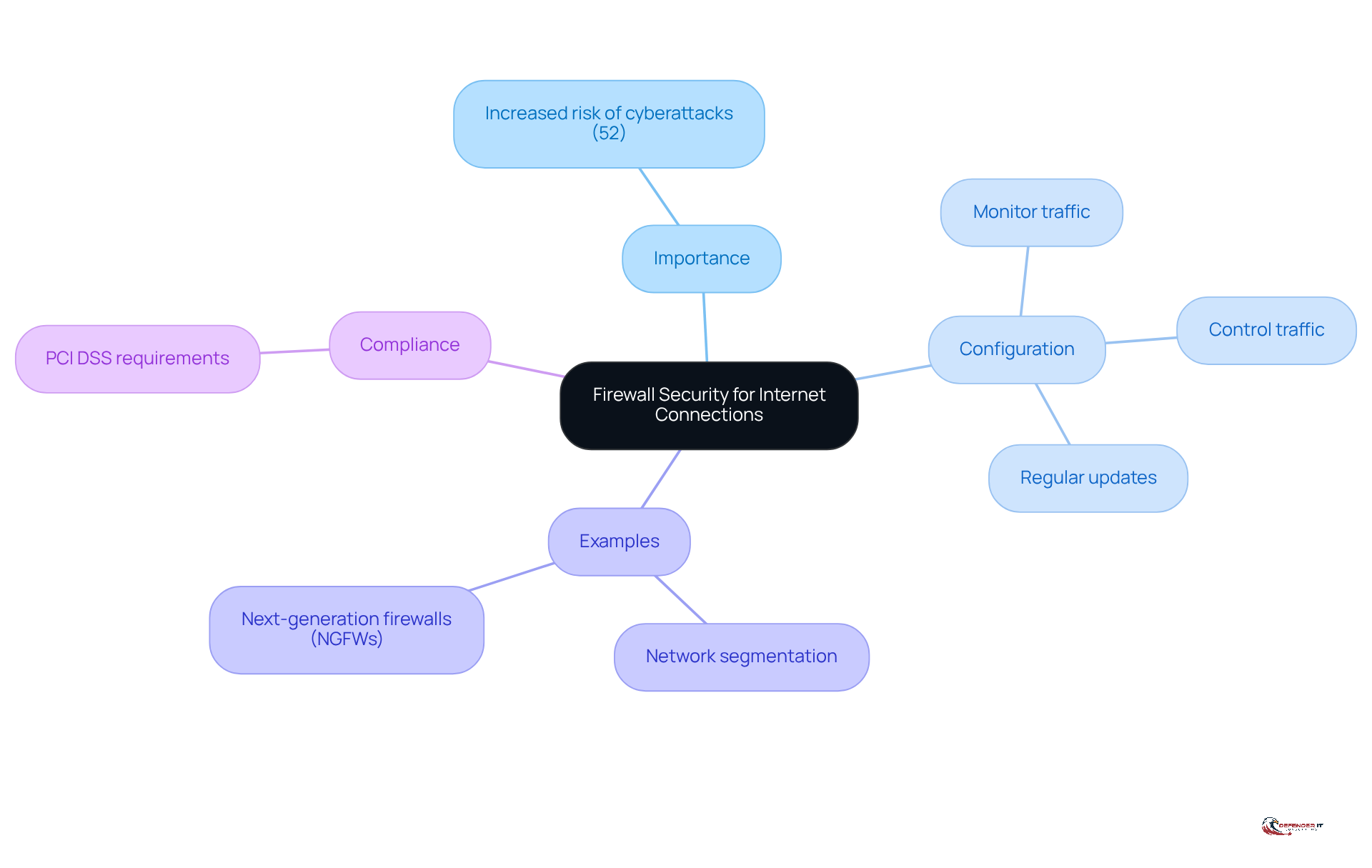
Implement Firewall Security for Internet Connections
Creating a robust firewall is essential for any commerce business, especially considering that 52% of merchants report an increased risk of cyberattacks. Firewalls should be configured to monitor and control incoming and outgoing network traffic based on established security protocols. Regular updates to firewall settings and conducting audits are critical for maintaining effectiveness against evolving threats.
For example, a retail company that segmented its network with firewalls experienced a notable reduction in the impact of a ransomware attack, as the malware could not propagate throughout the entire network. Additionally, employing next-generation firewalls (NGFWs) that incorporate intrusion prevention systems (IPS) significantly enhances protection. NGFWs can identify early signs of ransomware activity and thwart attacks before they escalate, making them an indispensable element of a comprehensive cyber security retail strategy.
Moreover, compliance with the Payment Card Industry Security Standard (PCI DSS) is crucial for safeguarding payment information, further underscoring the necessity of strong firewall protections.
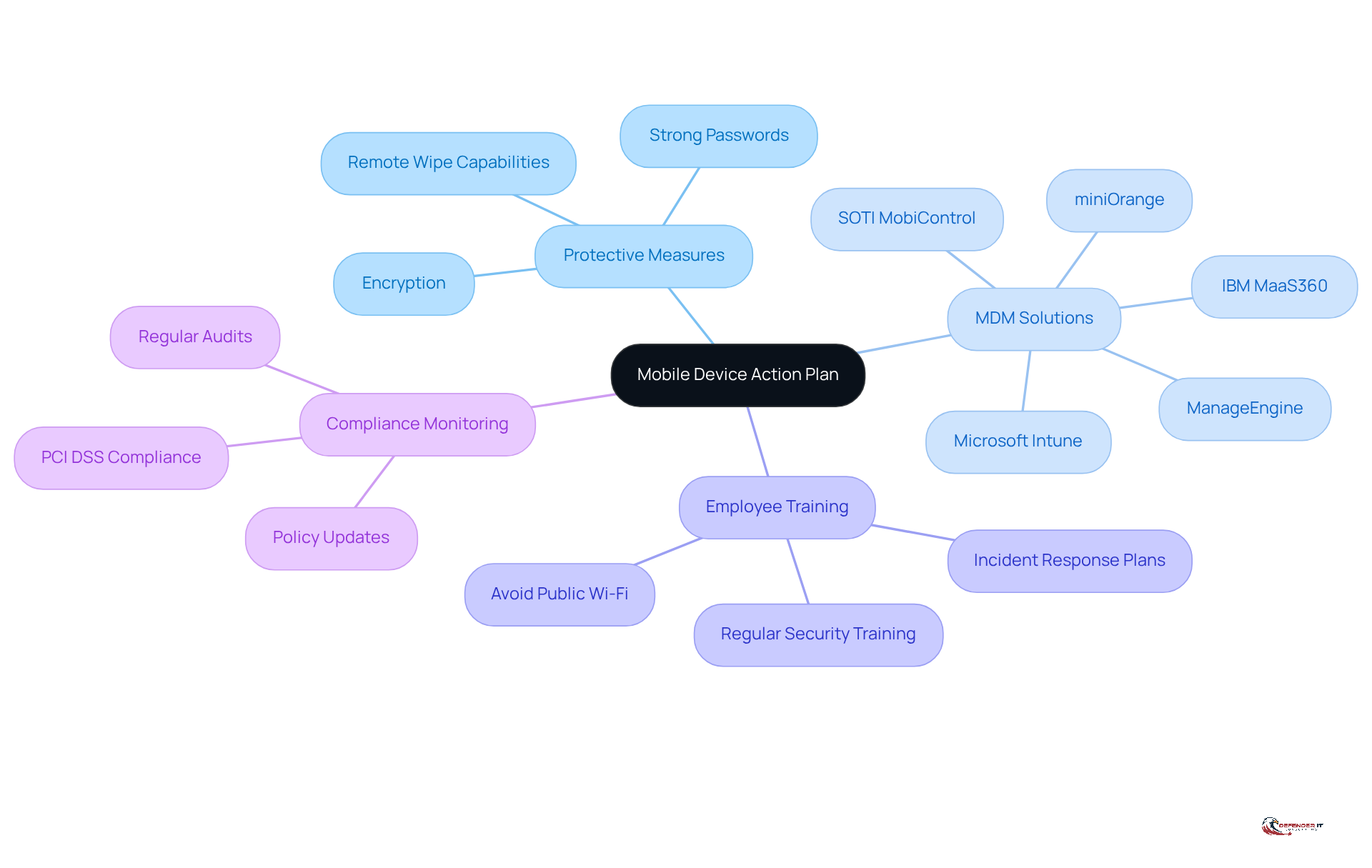
Create a Mobile Device Action Plan
Retail companies must develop a comprehensive mobile device strategy that delineates protective measures for devices accessing sensitive company information. Implementing mobile device management (MDM) solutions is essential for enforcing robust security protocols, such as requiring strong passwords and enabling encryption. Industry projections indicate significant growth in the global MDM market, underscoring the increasing importance of these solutions. For instance, a retail chain that adopted an MDM solution successfully established remote information wiping features for lost or stolen devices, thereby substantially mitigating the risk of data breaches.
Furthermore, training employees on secure mobile practices, including the avoidance of public Wi-Fi for sensitive transactions, is critical for sustaining a secure operational environment. As Rob Halik, a Senior Analyst at Tellennium, observes, “Without proper oversight, companies can face inefficiencies, spiraling costs.” Regular audits and updates to these protocols can further bolster security in the cyber security retail sector, ensuring that business operations remain resilient against evolving cyber threats.
Moreover, compliance monitoring for regulations such as PCI DSS is vital for stores managing sensitive customer information, highlighting the necessity of a thorough mobile device action strategy.
Make Regular Backup Copies of Important Data
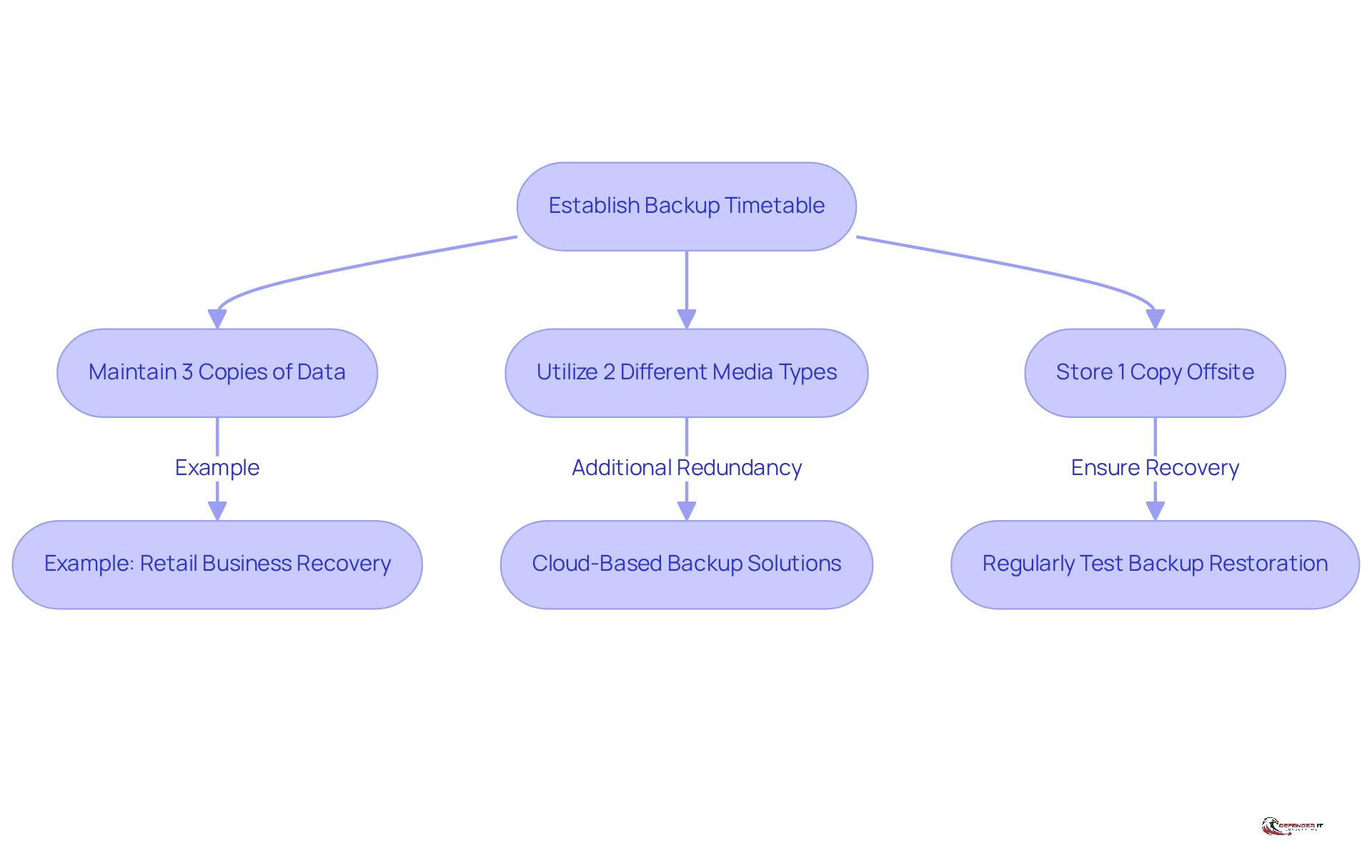
Establishing a consistent backup timetable is crucial for companies in the commerce sector. Adhering to the 3-2-1 backup rule is recommended:
- Maintain three copies of your data.
- Utilize two different media types.
- Store one copy offsite.
For example, a retail business that faced a ransomware attack was able to restore its operations swiftly due to its commitment to regular backups. Furthermore, routinely testing backup restoration processes is essential to ensure that data can be recovered efficiently when necessary. [Cloud-based backup solutions](https://impossiblecloud.com/en-us/magazine/3-2-1-backup-rule-v2-2-new) offer additional redundancy and security, making them an increasingly viable option for many retailers in the realm of cyber security retail.
Conclusion
Implementing effective cybersecurity practices is essential for retail businesses to safeguard their operations and customer data. Investing in comprehensive training for employees, establishing robust protective measures, and maintaining regular data backups are critical components of a successful cybersecurity strategy. By prioritizing these elements, retailers can significantly reduce their vulnerability to cyber threats and foster a safer shopping environment.
Key strategies highlighted include:
- The importance of employee training in recognizing cyber threats
- The necessity of multi-layered security systems
- The implementation of strong firewall protections
- The development of a mobile device action plan
Each of these practices contributes to a holistic approach to cybersecurity that not only protects sensitive information but also enhances overall operational resilience. Statistics and real-world examples underscore the effectiveness of these measures, reinforcing their significance in the retail sector.
As the landscape of cyber threats continues to evolve, retail businesses must remain vigilant and proactive in their cybersecurity efforts. Embracing these best practices is not merely a defensive measure; it is a crucial investment in the future of the business. By fostering a culture of security awareness and resilience, retailers can protect their assets and build trust with their customers, ensuring long-term success in an increasingly digital marketplace.
Frequently Asked Questions
Why is training employees on cybersecurity principles important for retail establishments?
Training employees on cybersecurity principles is crucial as it educates them about the latest cyber threats, safe online practices, and the importance of reporting suspicious activities. Regular training sessions and simulations enhance their awareness and preparedness.
What impact can targeted training initiatives have on phishing attempts?
Targeted training initiatives, such as phishing simulations, can significantly reduce successful phishing attempts. For example, a retail chain that implemented such training reported a 40% decrease in successful phishing attempts.
How can gamified learning experiences benefit employee training in cybersecurity?
Gamified learning experiences can increase engagement and retention of information, making training more effective and enjoyable for employees.
What are some platforms that provide comprehensive cybersecurity training resources?
Platforms like KnowBe4 and Cybrary offer effective and accessible training resources for enhancing cybersecurity awareness among employees.
What are the key components of a multi-layered cybersecurity strategy for retail businesses?
A multi-layered cybersecurity strategy should include advanced threat detection systems, encryption for sensitive information, and regular software updates to address vulnerabilities.
What statistics highlight the urgency of implementing cybersecurity measures in retail?
Statistics indicate that 80% of retailers experienced issues related to cybersecurity in the past year, emphasizing the need for robust cybersecurity strategies.
Can you provide an example of a successful cybersecurity measure implemented by a retailer?
A major retailer that adopted an intrusion detection system (IDS) successfully identified and mitigated a potential breach before any data was compromised.
Why are regular vulnerability assessments important for retail businesses?
Regular vulnerability assessments are crucial for identifying weaknesses within the system, enabling prompt remediation, and enhancing overall resilience against cyber threats.
What common pitfalls should organizations avoid to maintain an effective cybersecurity strategy?
Organizations should avoid neglecting employee training on protective protocols, as this can undermine the effectiveness of their multi-layered cybersecurity approach.
List of Sources
- Train Employees on Cybersecurity Principles
- Best Cybersecurity Training for Employees in 2026 | Huntress (https://huntress.com/cybersecurity-training-guide/best-cybersecurity-training-for-employees)
- Security Awareness Training: USA 2025 Statistics | Infrascale (https://infrascale.com/security-awareness-training-statistics-usa)
- [Updated 2026] Security Awareness Training Statistics – Keepnet (https://keepnetlabs.com/blog/security-awareness-training-statistics)
- 2025 Security Awareness Report: Why Training Works and Where Organizations Still Fall Short | Fortinet Blog (https://fortinet.com/blog/industry-trends/2025-security-awareness-report-why-training-works-and-where-organizations-still-fall-short)
- 70 Cybersecurity Quotes Every Leader Should Know (https://deliberatedirections.com/cybersecurity-quotes)
- Protect Information and Systems from Cyber Attacks
- Inside the 2025 Retail Cybersecurity Threat Landscape: What Retailers Must Know (https://cpl.thalesgroup.com/blog/data-security/changing-retail-cybersecurity-threat-landscape)
- How to Build a Multi-Layered Cybersecurity Strategy That Actually Works (https://vennote.com/multi-layered-cybersecurity-strategy-that-actually-works)
- Mann IT Releases New Security Layers to Combat Latest Cyberthreats (https://palmbeachdailynews.com/press-release/story/29664/mann-it-releases-new-security-layers-to-combat-latest-cyberthreats)
- Top Retail Cybersecurity Threats and How to Combat Them in 2026 (https://riskaware.io/retail-cybersecurity-threats)
- Groupe Rocher CISO on strengthening a modern retail cybersecurity strategy – Help Net Security (https://helpnetsecurity.com/2026/02/11/jerome-etienne-groupe-rocher-retail-cybersecurity-strategy)
- Implement Firewall Security for Internet Connections
- Next Generation Firewall (NGFW) Companies (https://cybersecurityventures.com/next-generation-firewall-vendors)
- Latest Retail Cybersecurity Statistics | Fortinet (https://fortinet.com/solutions/industries/retail/retail-cybersecurity-statistics)
- Retail Cybersecurity Stats, Threats, and Solutions for 2026 (https://vikingcloud.com/blog/retail-cybersecurity-stats-threats-and-solutions)
- Cyber Protection Using Next-Gen Firewalls – Verus (https://veruscorp.com/next-generation-firewalls-against-cyber-threats)
- Why Firewall & Network Protection Is Essential in 2026 (https://bluechipit.com.au/why-firewall-network-protection-is-essential-in-2026)
- Create a Mobile Device Action Plan
- Beyond the Checkout: Why MDM in Retail is the Need of the Hour (https://42gears.com/blog/mdm-in-retail)
- 2026 Best Practices for Mobile Device Security & Encryption (https://soti.net/resources/blog/2026/cybersecurity-best-practices-for-mobile-security-encryption)
- Top 6 Tips for Securing Mobile Devices in Business (https://tellennium.com/top-6-tips-for-securing-mobile-devices-in-business)
- Top 10 Mobile Device Management Solutions and Alternatives in 2026 (https://venn.com/learn/byod/mobile-device-management-solutions)
- 5 Best Mobile Device Management (MDM) Software Solutions in 2026 (https://miniorange.com/blog/best-mobile-device-management-mdm-solutions)
- Make Regular Backup Copies of Important Data
- The 3-2-1 Backup Rule: What It Is and How It Works in 2026 (https://flosum.com/blog/3-2-1-backup-rule)
- World Backup Day: Is the 3-2-1 backup rule still relevant? (https://blog.barracuda.com/2026/03/31/world-backup-day–is-the-3-2-1-backup-rule-still-relevant-)
- Data Backup Solutions Statistics: USA 2025 / Infrascale (https://infrascale.com/data-backup-solutions-statistics-usa)
- Backup Statistics By Users, Companies, Frequency, Country And Technology Adoption (2025) (https://electroiq.com/stats/backup-statistics)
- The 3-2-1 Backup Rule Modernized | Impossible Cloud (https://impossiblecloud.com/en-us/magazine/3-2-1-backup-rule-v2-2-new)