Introduction
In an era where cyber threats are prevalent across the internet, dark web monitoring stands out as a vital defense mechanism for businesses. This proactive strategy not only reveals illicit activities related to stolen data but also enables organizations to respond promptly to potential breaches, thereby protecting their reputation and financial integrity. As the landscape of cybercrime continues to evolve, businesses must consider how to effectively navigate the complexities of dark web surveillance to safeguard their sensitive information.
Understand Dark Web Monitoring and Its Importance
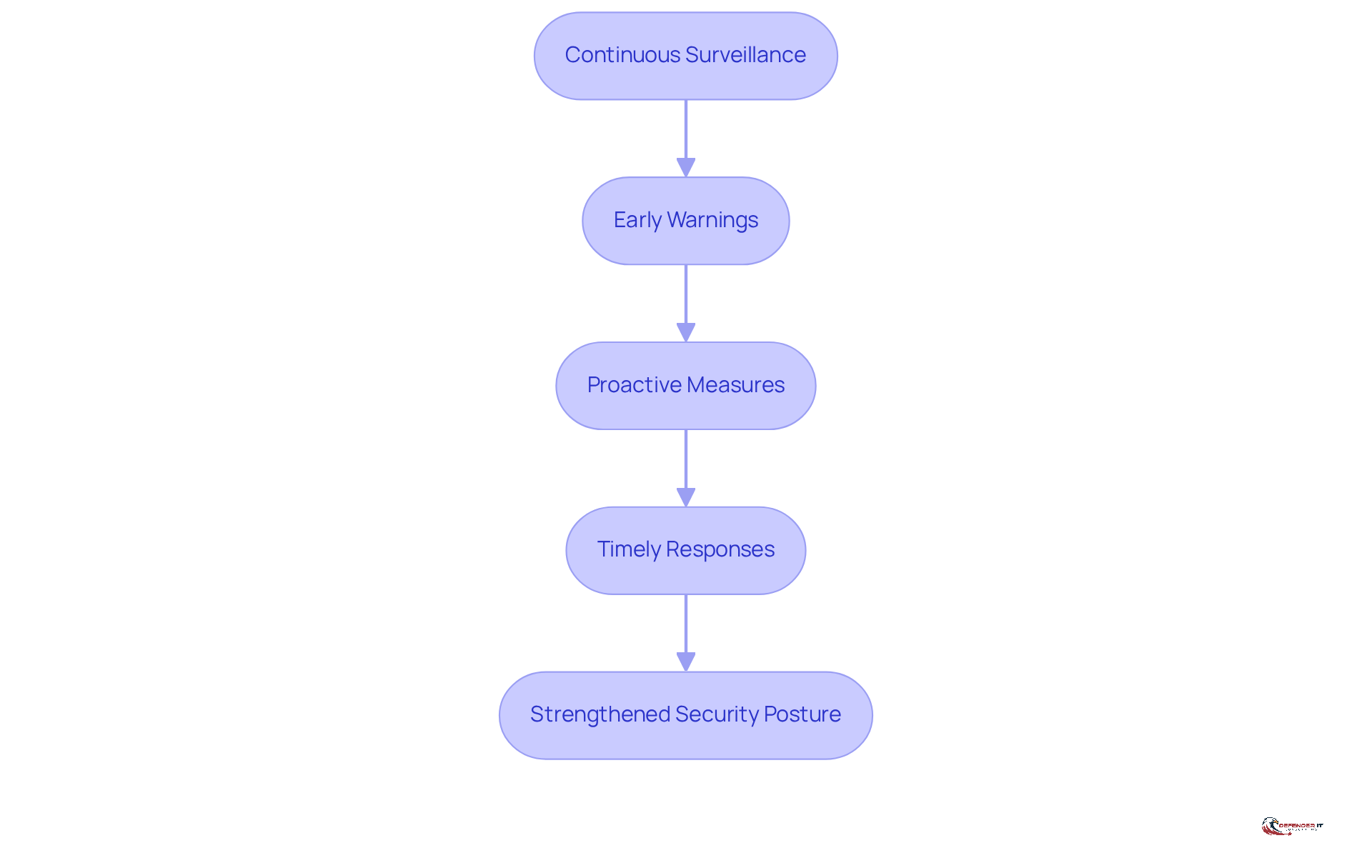
Dark web monitoring for business is essential, as it involves continuous surveillance of hidden segments of the internet where illicit activities, such as the sale of stolen data, occur. This practice provides early warnings when sensitive information – like employee credentials or customer data – emerges in criminal marketplaces. Organizations that conduct deep web surveillance can significantly reduce the risk of cyber attacks by detecting threats early, such as exposed credentials or planned exploits. This enables them to implement preventive measures before any harm occurs. In 2023 alone, 409 million records were exposed globally, highlighting the urgent need for businesses to adopt proactive strategies.
The significance of dark web monitoring for business extends beyond immediate threat identification; it plays a crucial role in safeguarding a company’s reputation and financial stability. By facilitating timely responses to emerging threats, organizations can mitigate the potential fallout from data breaches, which often result in identity theft, financial fraud, and reputational damage. As cybercriminals increasingly target sensitive personal and financial information, the demand for dark web monitoring for business becomes even more pressing. By 2026, advancements in hidden web tracking tools are expected to include additional automated functions, such as AI-driven detection and real-time alerts, further enhancing their effectiveness in protecting businesses.
Furthermore, alerts from dark web surveillance services should be viewed as strategic opportunities to secure data before exploitation occurs. As one specialist noted, “Your business should employ continuous, 24/7 observation instead of relying on monthly or annual scans.” This proactive approach not only aids in identifying potential breaches but also strengthens the overall security posture of the organization, ensuring resilience against the evolving landscape of cyber threats.
Identify Essential Features of Dark Web Monitoring Solutions
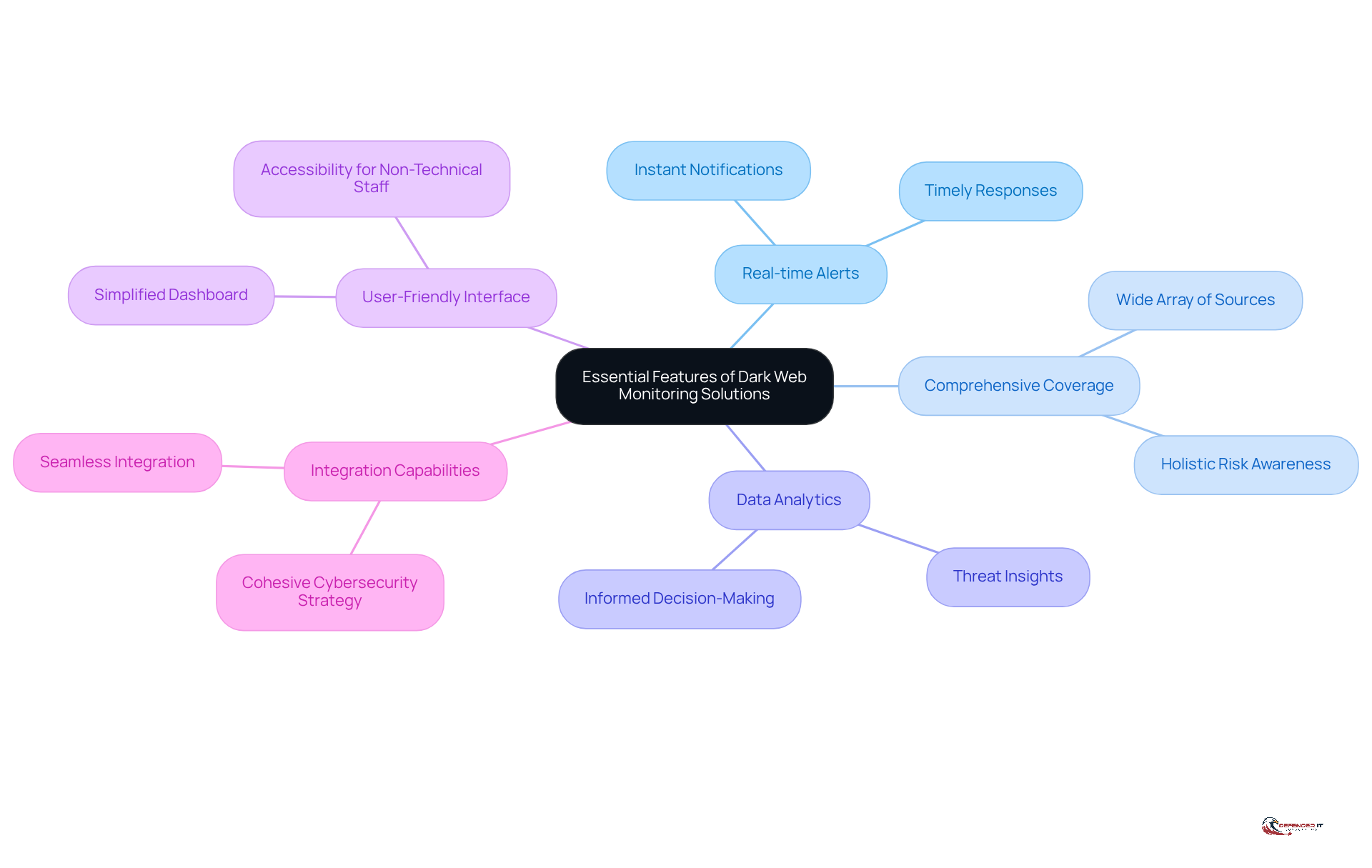
When selecting a dark web monitoring solution, businesses should prioritize several essential features to enhance their cybersecurity posture:
- Real-time Alerts: Instant notifications are crucial when sensitive data is discovered on the hidden web. This allows organizations to take prompt measures to mitigate potential breaches. Cybersecurity experts emphasize that the best tools send alerts within minutes of detection, making timely responses vital.
- Comprehensive Coverage: Effective solutions must monitor a wide array of dark web sources, including forums, marketplaces, and social media platforms. This comprehensive approach captures a holistic view of potential dangers, ensuring that organizations remain aware of various risks.
- Data Analytics: Advanced tools should provide insights into the nature of identified threats, assisting organizations in understanding the context and potential impact of these risks. Such analytics are essential for informed decision-making and proactive risk management.
- User-Friendly Interface: A simplified dashboard is essential for oversight and reporting, ensuring accessibility for non-technical staff and facilitating quicker responses. A user-friendly interface can significantly enhance the efficiency of security teams.
- Integration Capabilities: The ability to seamlessly integrate with existing security systems is vital for creating a cohesive cybersecurity strategy that enhances overall protection. Integration enables a more streamlined approach to risk management and response.
By concentrating on these features, businesses can significantly enhance their oversight efforts through dark web monitoring for business and protect sensitive information against evolving cyber threats.
Implement Effective Strategies for Dark Web Monitoring
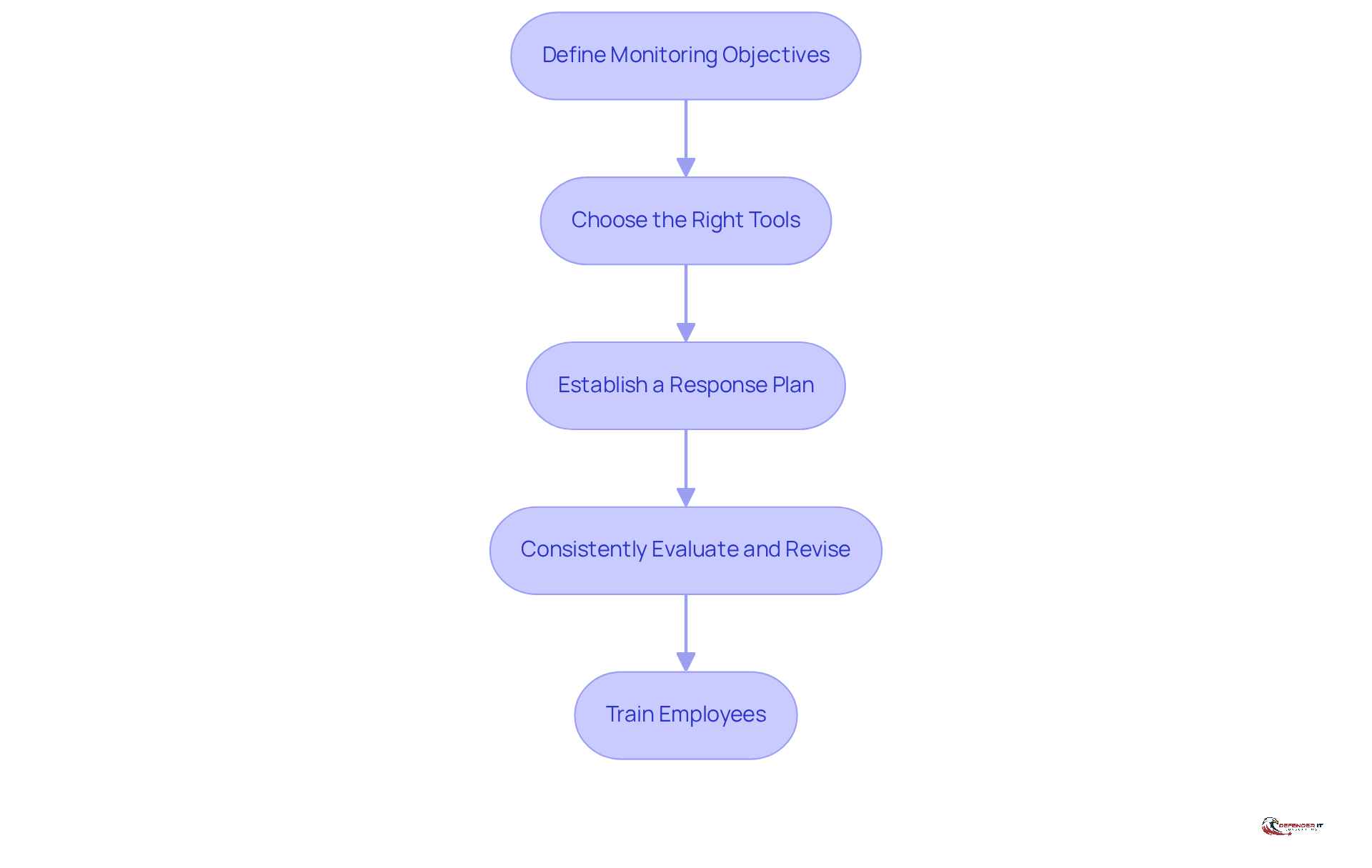
To implement effective dark web monitoring, businesses should adopt the following strategies:
- Define Monitoring Objectives: Clearly outline the specific data to be monitored, including employee emails, customer information, and proprietary data. This targeted approach ensures that oversight efforts are focused and relevant. According to EMPIST, dark web monitoring for business is no longer optional – it’s a necessity.
- Choose the Right Tools: Select monitoring solutions that align with your defined objectives and offer essential features such as real-time alerts and comprehensive coverage of potential risks. Effective tools should integrate seamlessly with existing security frameworks. Statistics indicate that oversight of the hidden web can reduce the time needed to identify breaches, thereby narrowing the opportunity for malicious actors.
- Establish a Response Plan: Develop a clear protocol for responding to alerts, detailing who will be notified and the specific actions to be taken. A well-structured response plan ensures prompt action and minimizes disruptions when a breach is detected. EMPIST emphasizes, “A well-structured response plan ensures quick action and minimizes disruptions when a breach is detected, reducing downtime and financial losses.”
- Consistently Evaluate and Revise: Continuously assess the effectiveness of your surveillance strategy, making necessary adjustments to address emerging risks. Regular updates to surveillance tools and methods are essential for staying aligned with the evolving characteristics of the hidden web. As highlighted in case studies, organizations that prioritize frequent updates are better prepared to manage new challenges.
- Train Employees: Educate staff on the importance of concealed web surveillance and how to identify potential threats. Regular training sessions and simulated cyberattack drills can significantly reduce human error, a major security risk for businesses. EMPIST notes that “regular training sessions and simulated cyberattack drills can reduce human error.”
By implementing these strategies, organizations can cultivate a proactive cybersecurity stance that effectively mitigates risks associated with dark web monitoring for business activities. Furthermore, avoiding common pitfalls, such as neglecting routine updates and training, will enhance the overall effectiveness of deep web surveillance initiatives.
Recognize Challenges and Limitations of Dark Web Monitoring
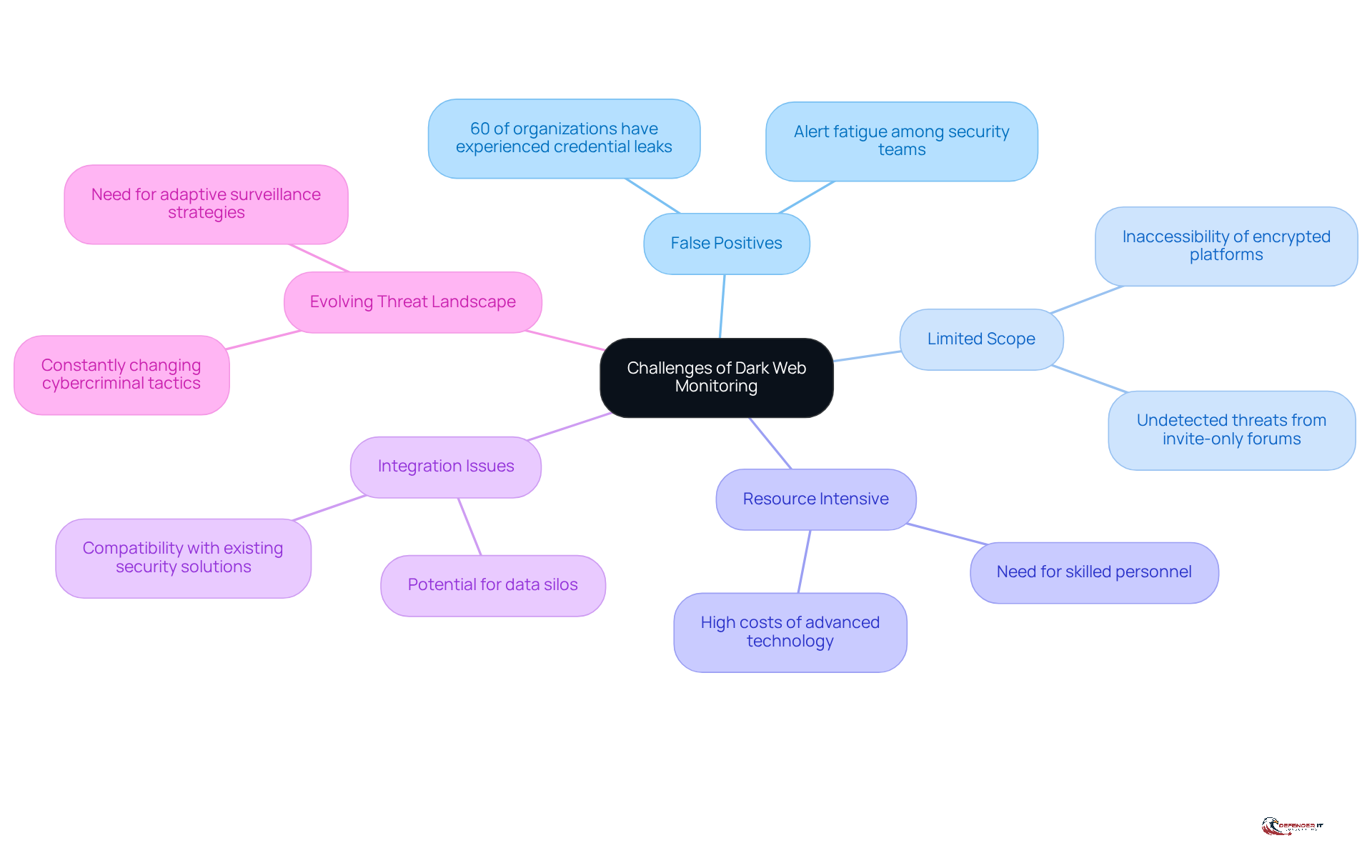
While dark web monitoring serves as a valuable tool, businesses must recognize its challenges and limitations:
- False Positives: Monitoring tools frequently generate alerts for irrelevant or non-actionable data, resulting in alert fatigue among security teams. Notably, 60% of organizations have experienced employee credentials being revealed on the shadow web, underscoring the prevalence of false alerts and their impact on critical alert management.
- Limited Scope: The effectiveness of monitoring is constrained by the inability to track all concealed web activities. Certain threats may go undetected due to the inaccessibility of specific encrypted platforms or invite-only forums, leaving organizations exposed to emerging risks.
- Resource Intensive: Effective dark web surveillance demands dedicated resources, including skilled personnel and advanced technology. Organizations with limited IT resources encounter significant challenges in implementing and managing these tools, which can be costly and may result in delays in incident response.
- Integration Issues: The incorporation of oversight solutions with existing security frameworks can pose considerable challenges. Poor integration may lead to data silos or security blind spots, thereby diminishing the overall effectiveness of cybersecurity measures. It is advisable to select oversight tools with flexible APIs and to collaborate with suppliers that provide consultation and technical assistance to facilitate smoother integration.
- Evolving Threat Landscape: Cybercriminal tactics are in a constant state of flux, necessitating the ongoing adaptation of surveillance strategies. As Jon Clay, VP of Threat Intelligence at Trend Micro, states, ‘Dark web monitoring for business has become an essential aspect of proactive cyber defense strategies.’ Organizations must remain vigilant and proactive to keep pace with these changes and effectively mitigate risks.
By acknowledging these challenges, organizations can better prepare and enhance their overall cybersecurity posture, ensuring they are equipped to respond to the complexities of the dark web.
Conclusion
Dark web monitoring is essential, serving as a critical element of a comprehensive cybersecurity strategy for businesses. By actively surveilling hidden segments of the internet, organizations can detect and respond to potential threats before they escalate into significant breaches. The urgency for such measures has never been clearer, particularly in light of the staggering number of records exposed in recent years and the increasing sophistication of cybercriminals targeting sensitive data.
Effective dark web monitoring practices include:
- Implementing real-time alerts
- Ensuring comprehensive coverage of various dark web sources
- Employing advanced data analytics
Furthermore, businesses must establish clear monitoring objectives, select appropriate tools, and develop robust response plans to ensure prompt action against potential threats. Continuous evaluation and employee training further enhance the effectiveness of these strategies, enabling organizations to stay ahead of emerging risks.
In an ever-evolving digital landscape, the significance of dark web monitoring cannot be overstated. Organizations are encouraged to prioritize these practices not only to safeguard their sensitive information but also to protect their reputation and financial stability. By adopting a proactive approach and leveraging the right tools and strategies, businesses can significantly mitigate risks associated with the dark web and foster a more secure operational environment.
Frequently Asked Questions
What is dark web monitoring for businesses?
Dark web monitoring for businesses involves continuous surveillance of hidden segments of the internet where illicit activities occur, such as the sale of stolen data. It provides early warnings when sensitive information, like employee credentials or customer data, appears in criminal marketplaces.
Why is dark web monitoring important for organizations?
Dark web monitoring is important because it helps organizations detect threats early, such as exposed credentials or planned exploits, which can significantly reduce the risk of cyber attacks. It also safeguards a company’s reputation and financial stability by facilitating timely responses to emerging threats.
What are the potential consequences of not implementing dark web monitoring?
Without dark web monitoring, organizations may face increased risks of identity theft, financial fraud, and reputational damage due to data breaches. The lack of proactive threat identification can lead to severe fallout from cyber attacks.
How many records were exposed globally in 2023, highlighting the need for dark web monitoring?
In 2023, 409 million records were exposed globally, underscoring the urgent need for businesses to adopt proactive strategies like dark web monitoring.
What advancements in dark web monitoring tools are expected by 2026?
By 2026, advancements in hidden web tracking tools are expected to include additional automated functions, such as AI-driven detection and real-time alerts, which will enhance their effectiveness in protecting businesses.
How should alerts from dark web surveillance services be viewed?
Alerts from dark web surveillance services should be viewed as strategic opportunities to secure data before it can be exploited, enabling organizations to take preventive measures.
What is the recommended approach for dark web monitoring?
The recommended approach is to employ continuous, 24/7 observation rather than relying on monthly or annual scans. This proactive strategy aids in identifying potential breaches and strengthens the overall security posture of the organization.
List of Sources
- Understand Dark Web Monitoring and Its Importance
- Dark Web Intelligence: Why Monitoring Matters In 2026 (https://cyble.com/blog/dark-web-intelligence-monitoring-guide)
- Dark Web Threat Intelligence: 7 Key Risks in 2026 | Darknetsearch.com (https://darknetsearch.com/knowledge/news/en/dark-web-threat-intelligence-7-key-risks-in-2026)
- Dark Web Monitoring: A 2026 Guide for UK Business Leaders – HJS Technology Ltd (https://hjstechnology.co.uk/dark-web-monitoring-a-2026-guide-for-uk-business-leaders)
- Dark Web Monitoring 2026 Trends Every Enterprise Must Know (https://cyble.com/knowledge-hub/dark-web-monitoring-trends)
- Google to Shut down Dark Web Monitoring Tool in February 2026. – STP (https://smartteacherplatform.ca/google-to-shut-down-dark-web-monitoring-tool-in-february-2026)
- Identify Essential Features of Dark Web Monitoring Solutions
- Dark Web Intelligence: Why Monitoring Matters In 2026 (https://cyble.com/blog/dark-web-intelligence-monitoring-guide)
- Google just launched a new Gemini-powered dark web monitoring service (https://itpro.com/security/google-just-launched-a-new-gemini-powered-dark-web-monitoring-service)
- 15 Best Dark Web Monitoring Tools & Services (https://breachsense.com/blog/best-dark-web-monitoring-tools)
- Dark Web Monitoring 2026 Trends Every Enterprise Must Know (https://cyble.com/knowledge-hub/dark-web-monitoring-trends)
- Best Dark Web Monitoring Tools for Businesses in 2026 (https://preyproject.com/blog/best-dark-web-monitoring-tools)
- Implement Effective Strategies for Dark Web Monitoring
- Dark Web Monitoring for Business: What CEOs Need to Know (https://empist.com/dark-web-monitoring-for-business-what-ceos-need-to-know)
- Deep and Dark Web Monitoring for Business | Cyber Risk | Kroll (https://kroll.com/en/publications/cyber/deep-dark-web-monitoring-business-uncovering-hidden-risks)
- Dark Web Monitoring for Business: Complete Guide (https://breachsense.com/blog/dark-web-monitoring-for-business)
- How to set up dark web monitoring for organizations (https://preyproject.com/blog/how-to-set-up-dark-web-monitoring-for-organizations)
- The Growing Role of Dark Web Monitoring in Cybersecurity for Businesses – SwiftTech Solutions (https://swifttechsolutions.com/swifttech-blog/the-growing-role-of-dark-web-monitoring-in-cybersecurity-for-businesses)
- Recognize Challenges and Limitations of Dark Web Monitoring
- The Cost of False Positives: Why Cybersecurity Accuracy Matters | UpGuard (https://upguard.com/blog/false-positives)
- 5 Key Challenges in Implementing Dark Web Monitoring Tools – SwiftTech Solutions (https://swifttechsolutions.com/swifttech-blog/5-key-challenges-in-implementing-dark-web-monitoring-tools)
- What Is Dark Web Monitoring? Benefits, Limitations, And How To Protect Your Personal Data (https://onerep.com/blog/what-is-dark-web-monitoring)
- What Is Dark Web Monitoring? (https://trendmicro.com/en_us/what-is/dark-web/dark-web-monitoring.html)