Introduction
The increasing sophistication of cyber threats presents a significant challenge for manufacturing leaders. They must navigate a landscape where operational technology and information technology converge. In this context, the IT Security Maturity Model emerges as a vital framework, enabling organizations to systematically assess and enhance their cybersecurity capabilities. As manufacturers strive to comply with stringent regulations and protect sensitive data, a pressing question arises: how can they effectively implement this model? This implementation is crucial not only to fortify their defenses but also to foster a culture of resilience against evolving threats.
Define IT Security Maturity Model
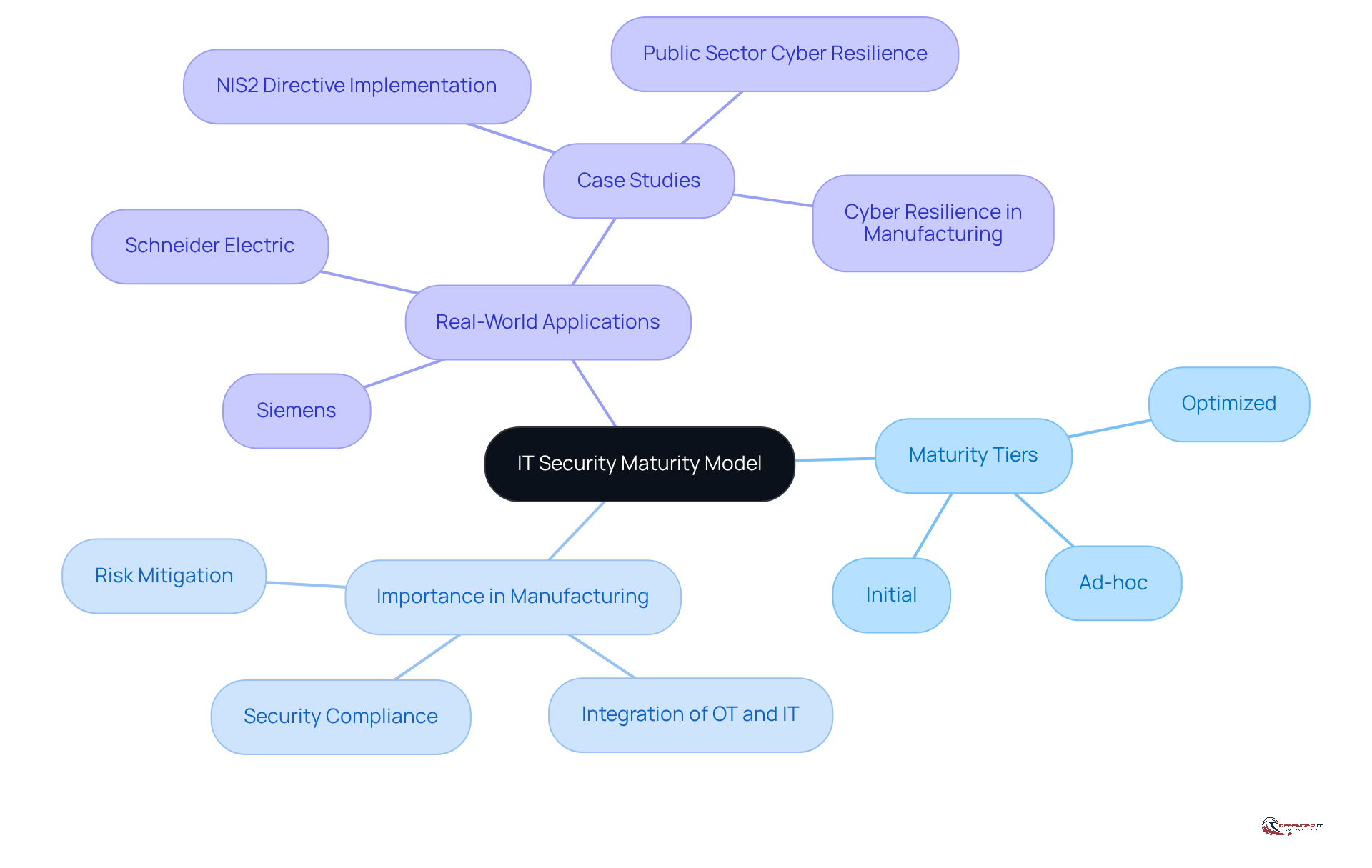
The it security maturity model serves as a structured framework that enables organizations to progressively assess and enhance their cybersecurity capabilities. This model outlines a roadmap for evaluating the effectiveness of protective measures, identifying gaps, and implementing necessary improvements. Typically, these frameworks , ranging from initial, ad-hoc procedures to optimized, fully integrated protective practices. Such a structured progression allows entities to evaluate their preparedness against cyber threats and align their protective strategies with overarching business objectives.
In the manufacturing sector, where the integration of operational technology (OT) and information technology (IT) is vital, this framework acts as an essential tool for maintaining security and compliance. As of 2026, approximately 68% of entities are utilizing the it security maturity model to enhance their cybersecurity posture, reflecting a growing acknowledgment of its significance. Recent advancements in these frameworks, particularly in response to evolving cyber threats, underscore the necessity for ongoing enhancement and adjustment. For example, companies like Siemens and Schneider Electric have effectively implemented these frameworks to strengthen their security measures, showcasing the model’s efficacy in real-world applications. This proactive approach not only mitigates risks but also fosters a culture of awareness and resilience regarding digital security within the manufacturing industry.
Explain the Importance of IT Security Maturity Models
It security maturity model is essential for organizations aiming to systematically assess and enhance their security practices. These frameworks enable companies to evaluate their current protective stance, identify weaknesses, and prioritize areas for improvement. For instance, the manufacturing sector, which currently holds the lowest cybersecurity maturity score of 1.8, stands to benefit significantly from these frameworks by ensuring compliance with stringent industry regulations and standards.
By adopting a maturity framework, organizations can allocate resources more effectively, focusing investments on protective measures that offer the highest return on investment. This not only fortifies defenses but also cultivates resilience against evolving cyber threats. As organizations progress through maturity stages, they enhance both their protective capabilities and their confidence in managing risks.
Recent trends indicate a growing recognition of the importance of these frameworks, with many organizations conducting regular maturity evaluations – ideally every three months or biannually – to track progress and celebrate achievements. A recent case study illustrated how Connectbase improved its security maturity by integrating an Azure-focused DevOps team, resulting in enhanced performance and reduced time to market.
Experts emphasize that implementing an it security maturity model is vital for organizations seeking to navigate the complexities of today’s threat landscape. As one industry leader remarked, “Cyber risk is now a business and governance imperative, requiring proactive strategic cyber resilience.” Furthermore, utilizing Governance, Risk, and Compliance (GRC) platforms can provide actionable insights for proactive risk management, thereby enhancing the effectiveness of maturity models. By leveraging these frameworks, companies can not only protect their assets but also lay a robust foundation for long-term success in an increasingly digital environment.
Outline Key Components of IT Security Maturity Models
Key components of IT Security Maturity Models encompass several essential elements that collectively enhance an organization’s cybersecurity posture:
- Governance: Establishing robust policies and procedures is crucial for guiding protection practices, ensuring alignment with overarching business objectives. Effective governance promotes accountability and transparency in safety initiatives.
- Risk Management: Organizations must identify, assess, and mitigate risks associated with cybersecurity threats. A proactive risk management approach enables businesses to prioritize vulnerabilities and allocate resources effectively, thereby reducing potential impacts on operations. For instance, recent statistics indicate that ransomware incidents surged by 149% in early 2025, underscoring the urgency of effective risk management strategies.
- Security Controls: Implementing both technical and administrative controls is vital for protecting information assets. These controls serve as the first line of defense against cyber threats, ensuring that sensitive data remains secure.
- Incident Response: Developing and maintaining a comprehensive incident response plan is essential for effectively addressing security incidents. This plan should detail procedures for detection, containment, eradication, and recovery, allowing entities to respond swiftly to minimize damage. As William Toll observes, prioritizing rapid detection and response platforms enhances resilience against attacks.
- Training and Awareness: Educating employees about protection policies and practices fosters a culture of safety within the organization. Regular training sessions and awareness campaigns can significantly reduce the likelihood of human error, a leading cause of cyber incidents. Research shows that up to 88% of all cyber incidents are attributed to human errors, highlighting the critical need for ongoing training.
- Continuous Improvement: Organizations should regularly review and update their protective practices to adapt to evolving threats and changes in the business environment. This commitment to ensures that security measures remain effective and relevant. The significance of cooperation between public and private sectors is also vital in enhancing digital security measures, as highlighted by industry specialists.
These components function together to establish a thorough framework that companies can use to assess their IT security maturity model and apply necessary enhancements. By concentrating on governance and risk management, entities can bolster their resilience against cyber threats and align their security strategies with business objectives.
Provide Examples of IT Security Maturity Models
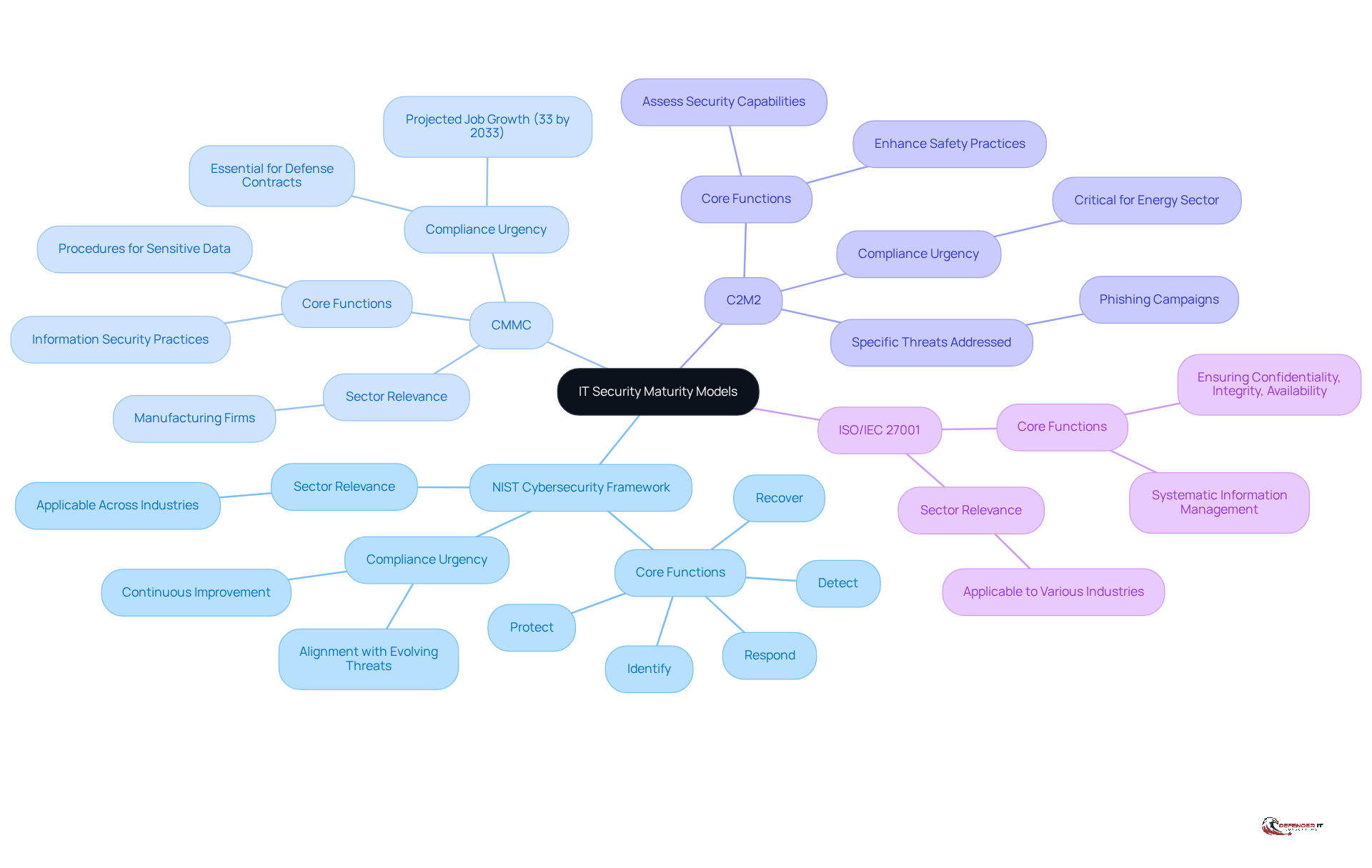
Various IT security maturity model frameworks are utilized across different sectors, each designed to address specific security needs. The most notable among these include:
- NIST Cybersecurity Framework (CSF): This adaptable framework assists organizations in managing and mitigating online security risks through five core functions: Identify, Protect, Detect, Respond, and Recover. The recent updates in 2026 underscore the necessity for continuous improvement and alignment with evolving threats. Dov Goldman emphasizes that adherence to frameworks like NIST is crucial for organizations to effectively navigate the complex security landscape.
- CMMC (Cybersecurity Maturity Model Certification): Developed by the Department of Defense, CMMC outlines essential information security practices and procedures that organizations must adopt to safeguard sensitive data, particularly relevant for manufacturing firms engaged in defense contracts. The urgency of compliance is highlighted by the projected 33% growth in information security jobs by 2033, reflecting the increasing demand for skilled professionals in this domain.
- C2M2 (Cybersecurity Capability Maturity Framework): This framework aids organizations, especially in the energy sector, in assessing their security capabilities and enhancing their safety practices to bolster resilience against cyber threats. The current threat landscape, characterized by phishing-driven campaigns like the Arcane Werewolf targeting manufacturing companies, underscores the critical need for robust protective measures.
- ISO/IEC 27001: This international standard provides a systematic approach to managing sensitive company information, ensuring its confidentiality, integrity, and availability-essential for maintaining trust in manufacturing operations.
These models illustrate the , each tailored to meet the distinct requirements of sectors such as manufacturing, finance, and government, thereby enhancing the overall IT security maturity model.
Conclusion
The IT Security Maturity Model is a crucial framework for organizations, especially in the manufacturing sector, to systematically assess and enhance their cybersecurity capabilities. By implementing this model, businesses can advance through various maturity stages, ensuring the protection of their assets while aligning security practices with broader organizational objectives. This structured approach is vital for navigating the complexities of today’s cyber threat landscape.
Key insights from the article underscore the significance of:
- Governance
- Risk management
- Security controls
- Incident response
- Training
- Continuous improvement
as foundational components of effective IT security maturity models. Organizations that adopt these elements can significantly bolster their defenses, mitigate vulnerabilities, and cultivate a culture of resilience against evolving cyber threats. Real-world examples, such as those from Siemens and Connectbase, demonstrate the practical advantages of implementing these frameworks, illustrating how strategic investments in cybersecurity can yield substantial returns.
Ultimately, the importance of IT security maturity models cannot be overstated. They provide a clear pathway for manufacturers to enhance their cybersecurity posture and highlight the necessity for ongoing evaluation and adaptation in response to emerging threats. As cyber risks increasingly intertwine with business operations, proactive engagement with these frameworks will be essential for ensuring long-term success and safeguarding organizational integrity in an ever-evolving digital landscape.
Frequently Asked Questions
What is the IT Security Maturity Model?
The IT Security Maturity Model is a structured framework that allows organizations to assess and enhance their cybersecurity capabilities progressively. It provides a roadmap for evaluating protective measures, identifying gaps, and implementing improvements.
How does the IT Security Maturity Model categorize maturity levels?
The model categorizes maturity into various tiers, ranging from initial, ad-hoc procedures to optimized, fully integrated protective practices. This structured progression helps organizations evaluate their preparedness against cyber threats.
Why is the IT Security Maturity Model important in the manufacturing sector?
In the manufacturing sector, where operational technology (OT) and information technology (IT) integration is crucial, the model serves as an essential tool for maintaining security and compliance.
What percentage of entities are using the IT Security Maturity Model as of 2026?
As of 2026, approximately 68% of entities are utilizing the IT Security Maturity Model to enhance their cybersecurity posture.
How have recent advancements in the IT Security Maturity Model been influenced?
Recent advancements in these frameworks have been driven by the need to respond to evolving cyber threats, emphasizing the necessity for ongoing enhancement and adjustment.
Can you provide examples of companies that have successfully implemented the IT Security Maturity Model?
Companies like Siemens and Schneider Electric have effectively implemented the IT Security Maturity Model to strengthen their security measures, demonstrating its efficacy in real-world applications.
What are the benefits of adopting the IT Security Maturity Model?
Adopting the model helps mitigate risks and fosters a culture of awareness and resilience regarding digital security within organizations, particularly in the manufacturing industry.