Introduction
In an era marked by frequent data breaches and cyberattacks, the necessity of robust encryption methods is paramount. Symmetric key algorithms emerge as a critical component of cybersecurity, providing an effective means to safeguard sensitive information through efficient encoding and decoding processes. As organizations seek to strengthen their defenses, several pertinent questions arise:
- How can they implement these algorithms effectively to counteract evolving threats?
- What best practices should be adopted to ensure optimal security?
This article explores the intricacies of symmetric key algorithms, examining their significance, various types, and essential strategies for effective deployment and management.
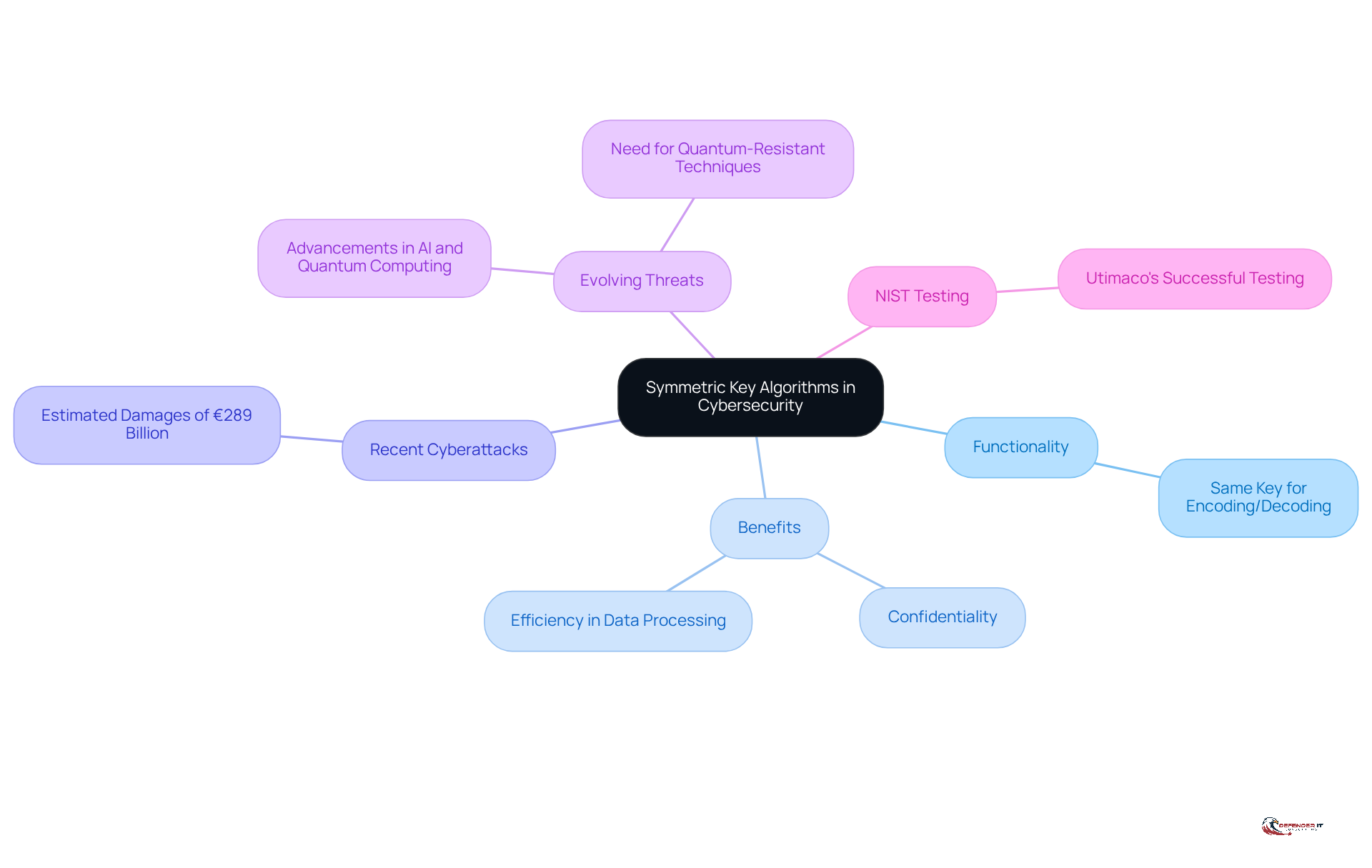
Understand Symmetric Key Algorithms and Their Importance in Cybersecurity
are crucial cryptographic techniques that use the same key for encoding and decoding processes. This approach is crucial in cybersecurity, as it protects data from unauthorized access, thereby ensuring confidentiality. The efficiency of symmetric coding facilitates the rapid processing of large data volumes, making it particularly beneficial in high-speed environments such as financial transactions and real-time communications.
Recent cyberattacks on German companies have resulted in estimated damages of €289 billion over the past year, highlighting the risks of insufficient security measures. Organizations that implement a symmetric key algorithm can significantly enhance their data protection. Furthermore, as threats evolve alongside advancements in technologies like artificial intelligence and quantum computing, the integration of new techniques into symmetric encryption methods is becoming increasingly vital.
As noted by Utimaco, a leader in cybersecurity solutions, the successful completion of NIST testing for their algorithms underscores the effectiveness of these methods in protecting sensitive information. Understanding and applying the symmetric key algorithm techniques is imperative for organizations committed to maintaining security in an ever-changing threat landscape.
Explore Different Types of Symmetric Key Algorithms and Their Applications
The symmetric key algorithm methods are essential in cybersecurity, each presenting unique characteristics and applications. The is the most widely adopted method, recognized for its robust security and efficiency. Cybersecurity expert Chris Painter emphasizes this importance, stating, “,” which underscores AES’s role in maintaining data integrity and confidentiality across sectors such as finance and healthcare. In contrast, older algorithms like the and its successor, Triple DES (3DES), are less secure and primarily utilized in legacy systems, which can introduce vulnerabilities.
are notable alternatives that provide versatility and speed, making them suitable for applications requiring rapid encoding and decoding. Organizations that prioritize performance without compromising security often implement Blowfish due to its quick processing capabilities. Similarly, Twofish is preferred for its adaptability across various environments, facilitating efficient encryption in real-time applications. For instance, a manufacturing company effectively employed Blowfish to enhance its data processing speed while ensuring robust protection.
The can be demonstrated through comparative statistics. AES is recognized for its resilience against brute-force attacks, with a key length of 128 bits offering a level of protection that is currently deemed unbreakable by traditional methods. Conversely, Blowfish, while faster, has a maximum key length of 448 bits, which, although secure, does not provide the extensive protection framework that AES offers. Cybersecurity leader Adam Fletcher notes, “.”
As organizations navigate the complexities of cybersecurity in 2026, understanding the applications and advantages of these techniques is vital for selecting the most appropriate encryption methods tailored to their specific needs. Integrating AES and other symmetric key algorithms into security protocols not only enhances but also fortifies overall organizational resilience against evolving cyber threats.
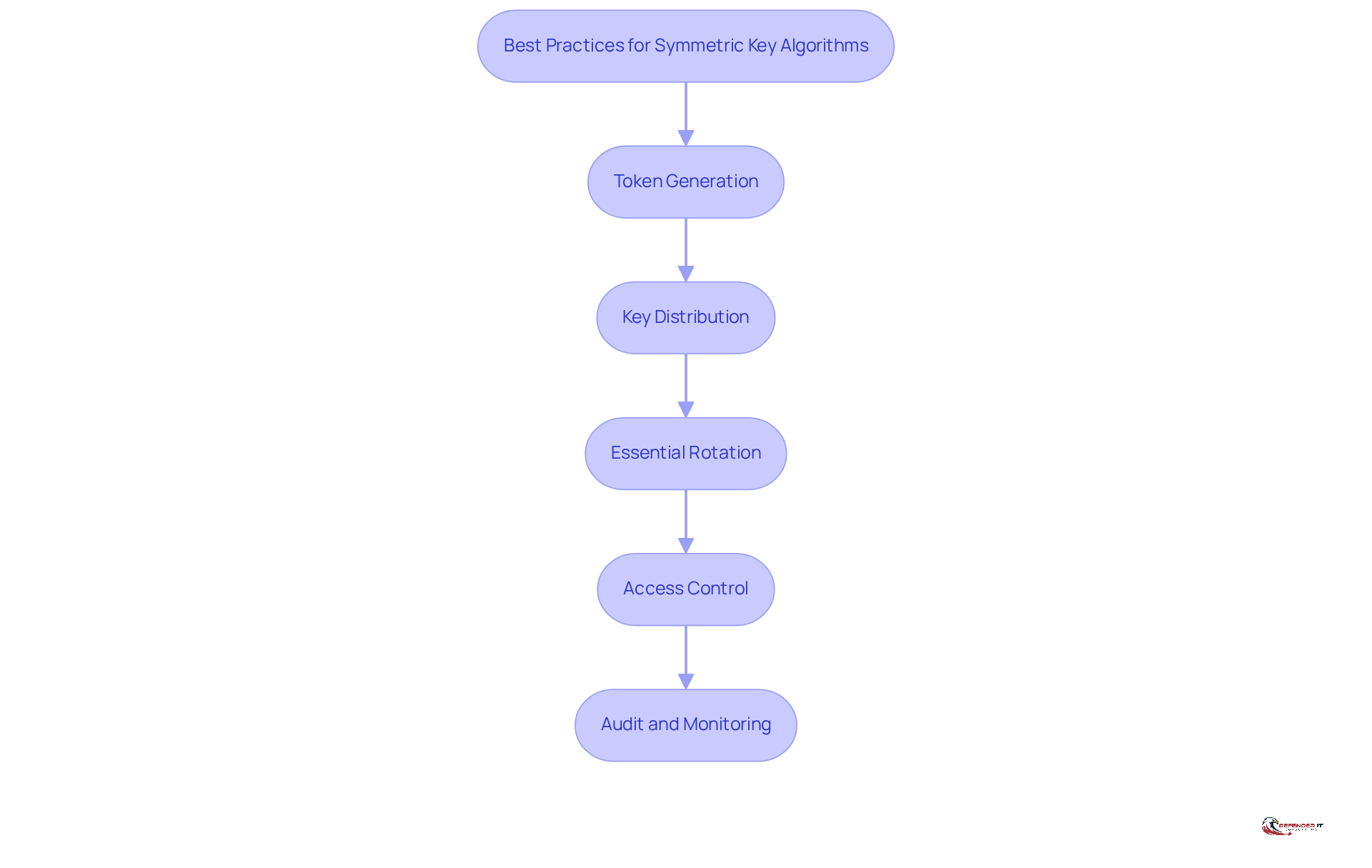
Implement Best Practices for Deploying and Managing Symmetric Key Algorithms
To effectively deploy and manage symmetric key algorithms, organizations should adhere to the following best practices:
- Token Generation: Utilize cryptographic methods to produce tokens, ensuring they are unpredictable.
- Secure Key Exchange: Implement secure channels for key exchange to prevent interception.
- Essential Rotation: Regularly change encryption codes to limit the impact of potential code compromise.
- Access Control: Restrict access to keys to authorized personnel only, minimizing insider threats.
- Audit and Monitoring: Continuously monitor key usage and access logs to detect any unauthorized attempts to access sensitive data.
By following these practices, organizations can significantly improve security with the implementation of a symmetric key algorithm.
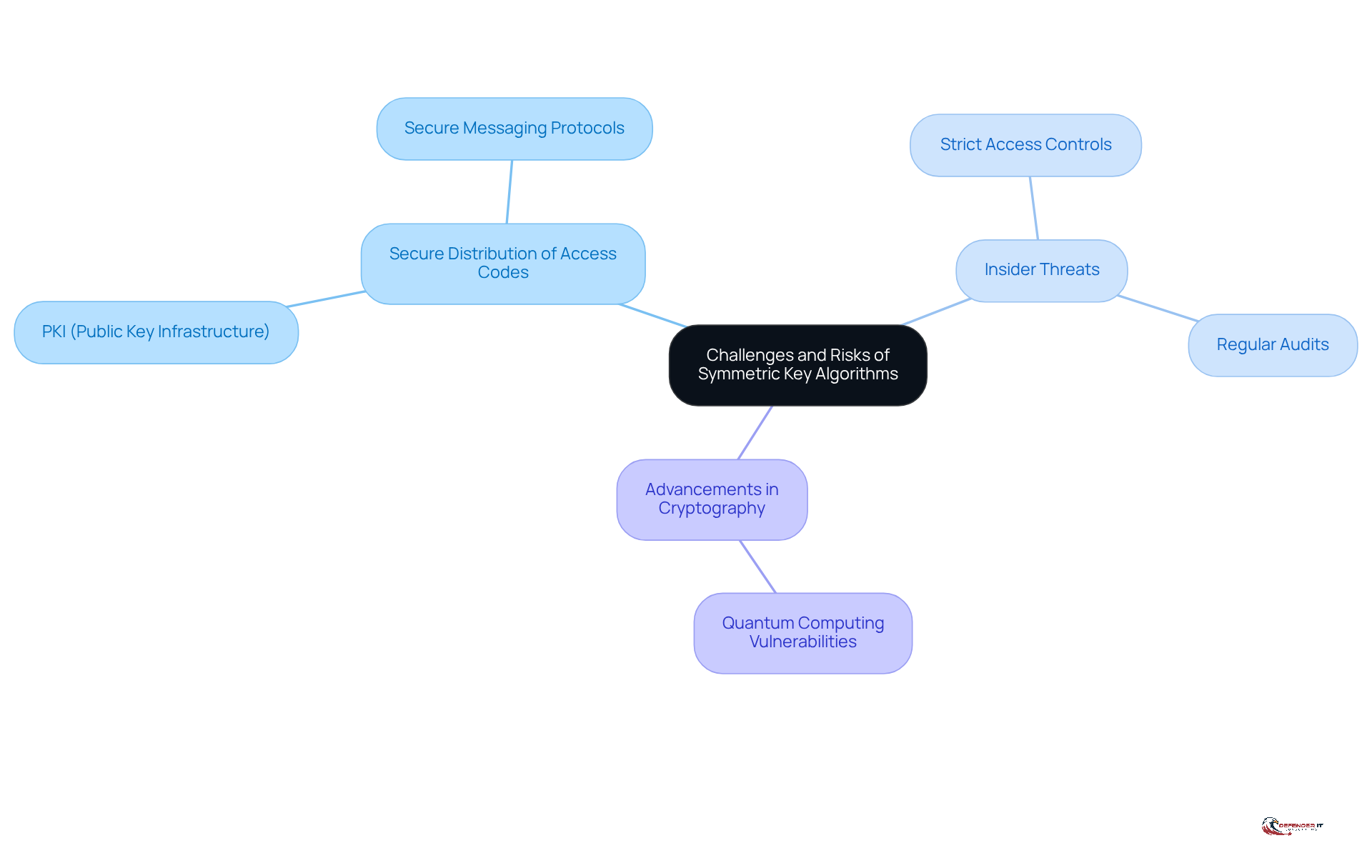
Address Challenges and Risks in Using Symmetric Key Algorithms
While symmetric key algorithms offer strong encryption, they also present several challenges. A primary concern is the risk of interception. If a code is intercepted during transmission, an attacker can easily decrypt sensitive data. To mitigate this risk, organizations must employ secure methods for key management, such as public key infrastructure (PKI) or secure messaging protocols.
Another significant risk arises from insider threats. Employees with access to encryption keys may misuse them, leading to potential data breaches. To address this issue, implementing strict access controls and conducting regular audits are essential strategies that can help safeguard sensitive information.
Finally, organizations must remain vigilant regarding advancements in cryptography and security protocols, particularly those associated with emerging technologies. Staying informed allows organizations to adapt their security strategies effectively, ensuring continued protection against evolving threats.
Conclusion
Mastering symmetric key algorithms is crucial for organizations seeking to strengthen their cybersecurity measures. These algorithms not only guarantee the confidentiality of sensitive data but also improve the speed and efficiency of data processing across various sectors. As cyber threats grow increasingly sophisticated, implementing robust encryption methods has transitioned from an option to a necessity for protecting information against unauthorized access.
This article explores the significance of symmetric key algorithms, detailing various types such as:
- AES
- Blowfish
- Twofish
along with their specific applications and strengths. Best practices for deploying these algorithms – including secure token generation, key distribution, and access control – are essential for mitigating risks associated with key management. Additionally, the challenges posed by insider threats and the evolving landscape of cyber threats, particularly with the advent of quantum computing, highlight the need for organizations to remain vigilant and adaptable.
Ultimately, adopting the best practices outlined for symmetric key algorithms can significantly bolster an organization’s cybersecurity posture. As the digital landscape continues to evolve, prioritizing effective encryption techniques will not only safeguard sensitive information but also establish a resilient framework capable of withstanding future cyber challenges. Organizations are urged to take proactive measures in implementing these strategies to ensure their data security remains uncompromised in an increasingly complex threat environment.
Frequently Asked Questions
What are symmetric key algorithms?
Symmetric key algorithms are cryptographic techniques that use the same key for both encoding and decoding data, ensuring confidentiality and protection of sensitive information.
Why are symmetric key algorithms important in cybersecurity?
They protect sensitive information from unauthorized access, which is crucial for maintaining confidentiality. Their efficiency allows for rapid processing of large volumes of data, making them particularly useful in high-speed environments like financial transactions and real-time communications.
What recent events highlight the need for effective cybersecurity measures?
Recent cyberattacks on German companies have resulted in estimated damages of €289 billion over the past year, emphasizing the financial consequences of inadequate cybersecurity.
How can organizations enhance their data security posture?
Organizations can significantly enhance their data security by implementing symmetric key algorithms, which help protect against unauthorized access and data breaches.
What challenges do evolving cyber threats pose to symmetric key algorithms?
As cyber threats evolve with advancements in technologies like artificial intelligence and quantum computing, it is becoming increasingly important to integrate quantum-resistant techniques into symmetric encryption methods.
What is the significance of NIST testing for symmetric key algorithms?
The successful completion of NIST testing for symmetric key algorithms, as noted by cybersecurity leader Utimaco, underscores the effectiveness of these methods in protecting sensitive information.
Why is it imperative for organizations to understand and apply symmetric key algorithms?
Understanding and applying symmetric key algorithm techniques is essential for organizations committed to maintaining strong protective measures in an ever-changing threat landscape.
List of Sources
- Understand Symmetric Key Algorithms and Their Importance in Cybersecurity
- Digital security at a turning point: three critical security trends for 2026 (https://utimaco.com/news/press-releases/digital-security-turning-point-three-critical-security-trends-2026)
- Explore Different Types of Symmetric Key Algorithms and Their Applications
- Cybersecurity Quotes That Define the Future of Digital Protection (https://medium.com/@cyberpromagazine/cybersecurity-quotes-that-define-the-future-of-digital-protection-64897c07bfc6)
- The Top 20 Expert Quotes On Cyber Risk and Security (https://surtech.co.za/20-expert-quotes-on-cyber-risk-and-security)
- diligent.com (https://diligent.com/resources/blog/top-20-quotes-cyber-risk-virtual-summit)
- 41 Cybersecurity Quotes to Protect Your Digital Life (https://acecloudhosting.com/blog/cybersecurity-quotes)
- Cybersecurity Awareness Month Quotes and Commentary from Industry Experts in 2025 (https://solutionsreview.com/cybersecurity-awareness-month-quotes-and-commentary-from-industry-experts-in-2025)
- Implement Best Practices for Deploying and Managing Symmetric Key Algorithms
- atera.com (https://atera.com/blog/best-cybersecurity-quotes)
- Address Challenges and Risks in Using Symmetric Key Algorithms
- diligent.com (https://diligent.com/resources/blog/top-20-quotes-cyber-risk-virtual-summit)
- 41 Cybersecurity Quotes to Protect Your Digital Life (https://acecloudhosting.com/blog/cybersecurity-quotes)
- Data Privacy Statistics: US 2025 | Infrascale (https://infrascale.com/data-privacy-statistics-usa)
- The 20 Best Quotes from Cyber Risk Leaders (https://revival-holdings.com/20-best-quotes-from-cyber-risk-leaders)
- Cybersecurity Quotes That Define the Future of Digital Protection (https://medium.com/@cyberpromagazine/cybersecurity-quotes-that-define-the-future-of-digital-protection-64897c07bfc6)