Introduction
The landscape of cybersecurity is increasingly complex, with organizations confronting a multitude of evolving threats that necessitate robust defensive measures. Penetration testing tools have become essential assets in this ongoing battle, empowering security leaders to identify and mitigate vulnerabilities before they can be exploited. However, the effectiveness of these tools relies heavily on their proper selection and integration. Therefore, organizations must ensure they are employing best practices to maximize their security posture.
Understand the Fundamentals of Penetration Testing Tools
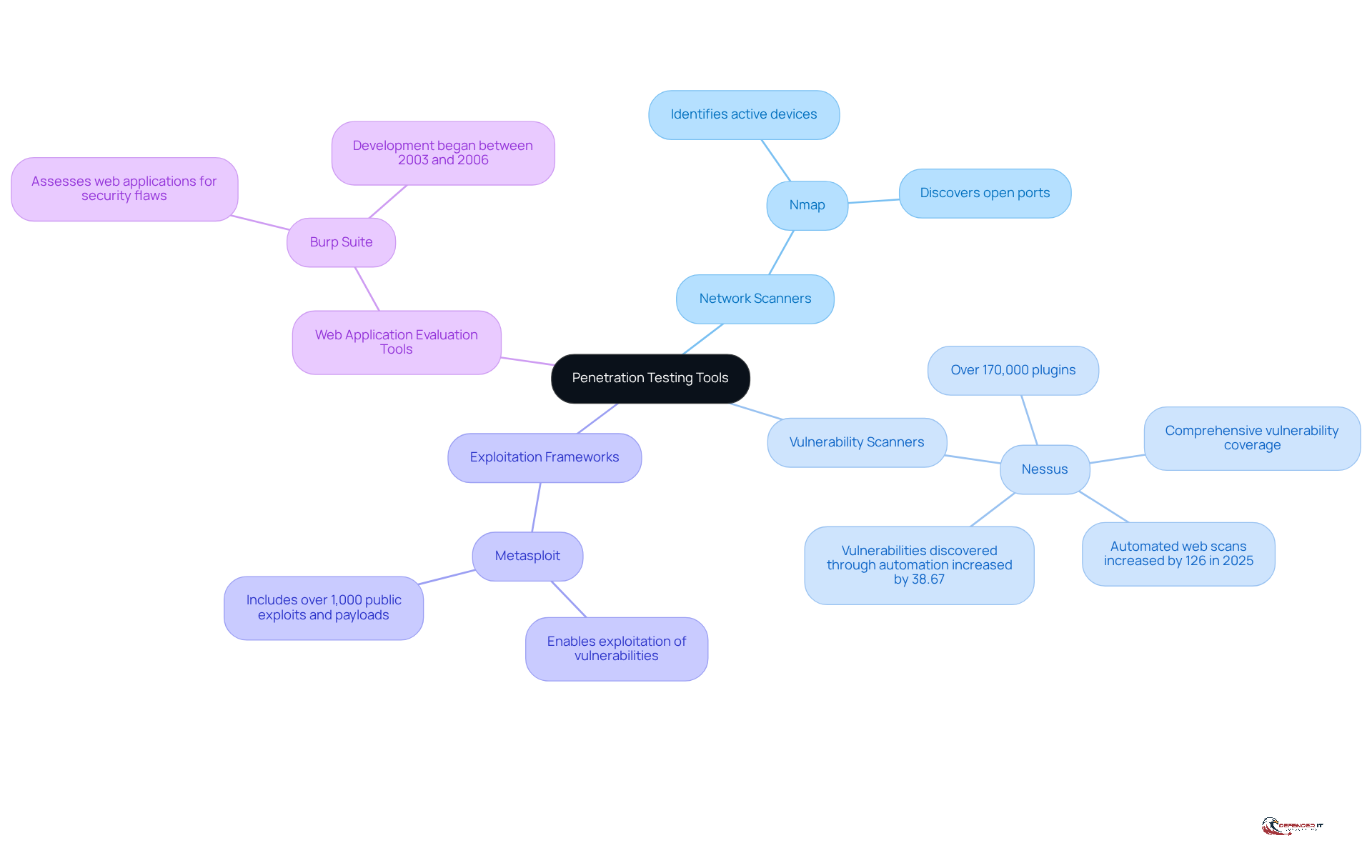
Pen test tools are crucial resources for identifying vulnerabilities within an organization’s IT infrastructure. These tools can be categorized into several key types:
- Network Scanners: Tools such as Nmap are essential for identifying active devices on a network and their open ports, providing a foundational understanding of the network landscape.
- Vulnerability Scanners: Nessus stands out as a leading resource that scans systems for known vulnerabilities, featuring over 170,000 plugins to ensure comprehensive coverage. In 2025, automated web scans surged by 126%, with vulnerabilities discovered through automation increasing by 38.67%. This trend underscores the growing reliance on pen test tools for effective vulnerability detection.
- Exploitation Frameworks: Metasploit is a widely recognized framework that enables professionals to exploit vulnerabilities in a controlled environment, facilitating the evaluation of defenses against real-world attack scenarios. It includes more than 1,000 public exploits and payloads, making it an invaluable asset in security assessments.
- Web Application Evaluation Tools: Burp Suite is extensively employed for assessing web applications for security flaws, allowing for detailed analysis and remediation of vulnerabilities. Its development, which began between 2003 and 2006, has established it as a staple in the cybersecurity toolkit.
Looking ahead to 2026, the market for security evaluation instruments is evolving, with a notable shift towards continuous assessments integrated with CI/CD pipelines. This approach enables organizations to reduce exposure more rapidly and achieve remediation timelines that exceed industry benchmarks by weeks. The leading pen test tools in 2026 include Metasploit, Burp Suite, Nmap, and Nessus, all recognized for their reliability in verifying vulnerabilities across contemporary systems.
Real-world examples illustrate the effectiveness of these tools. For instance, proactive protection evaluations in 2025 prevented an estimated $2.88 billion in potential losses, particularly from vulnerabilities in web and API exposures. This highlights the essential role that assessment instruments play in safeguarding organizational assets.
As cybersecurity experts emphasize, incorporating these tools into protective practices is vital for effective vulnerability evaluation and management. The continuous evolution of threats necessitates that safety leaders remain vigilant and proactive in their vulnerability assessment strategies. Moreover, it is critical to avoid common pitfalls, such as treating vulnerability assessments as mere checkbox tasks rather than as ongoing strategic components of protective practices.
Establish Criteria for Selecting Pen Test Tools
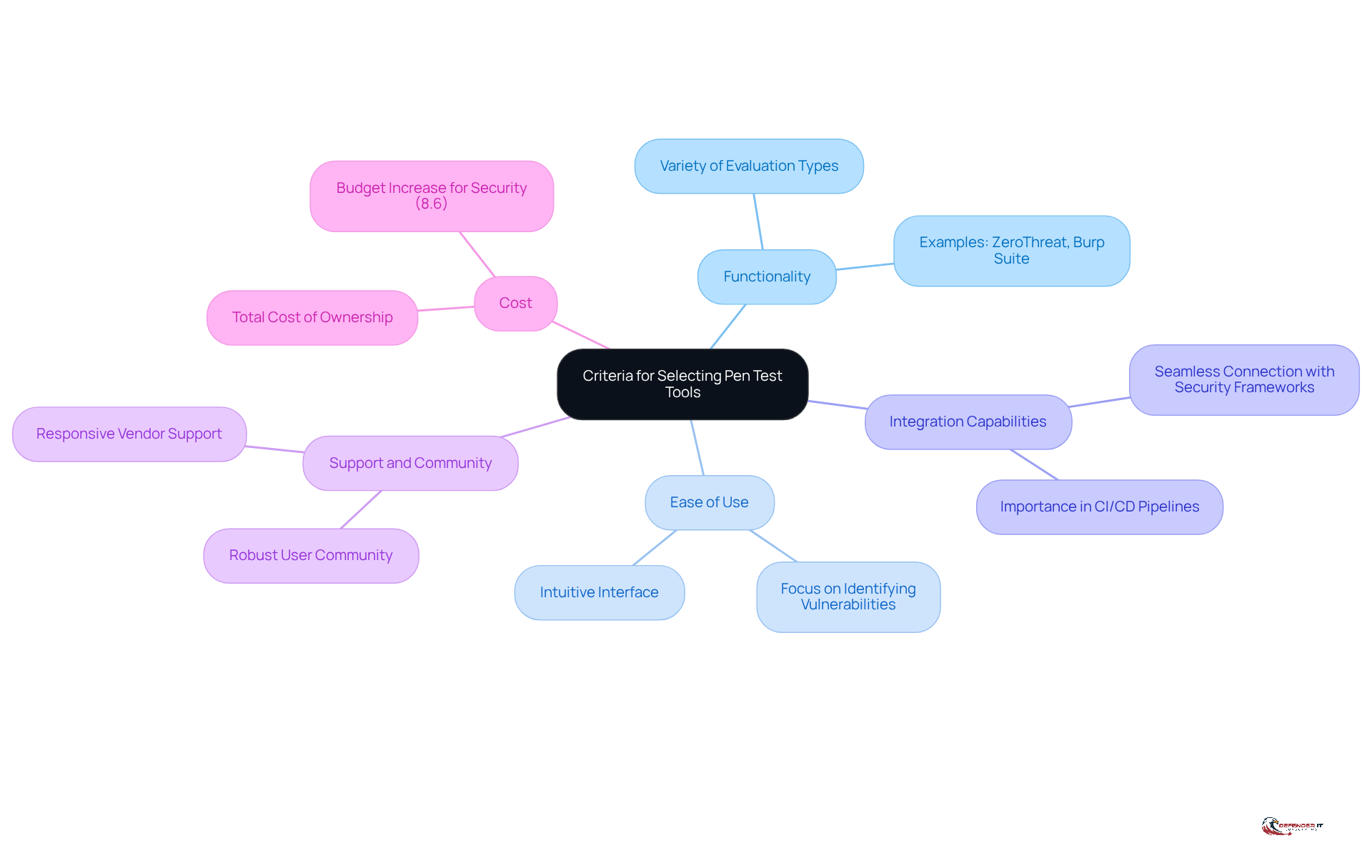
When selecting penetration testing tools, organizations should prioritize several critical criteria to ensure they effectively meet their security needs:
- Functionality: The tool must encompass a variety of evaluation types, including network and web application assessments, to address diverse security challenges. Resources such as ZeroThreat and Burp Suite Enterprise are recognized for their extensive capabilities in this domain.
- Ease of Use: An intuitive interface is essential for facilitating efficient evaluation processes. This allows teams to concentrate on identifying vulnerabilities rather than grappling with complex software.
- Integration Capabilities: The ability to seamlessly connect with existing security frameworks and resources is vital for maintaining a cohesive security posture and enhancing overall effectiveness. This integration becomes increasingly important as organizations adopt continuous evaluation practices within their CI/CD pipelines.
- Support and Community: A robust user community and responsive vendor support can significantly enhance the system’s effectiveness. They provide valuable resources and shared knowledge that assist in troubleshooting and optimization. As highlighted in industry discussions, a strong community can be pivotal in maximizing the effectiveness of pen test tools.
- Cost: Organizations should meticulously evaluate the total cost of ownership, which encompasses not only licensing fees but also training and maintenance expenses. This ensures that the investment aligns with their budgetary constraints. Notably, companies have increased their budget for security by approximately 8.6% over the past five years, underscoring the growing importance of investing in effective resources.
By applying these criteria, organizations can make informed decisions that enhance their evaluation capabilities and ultimately strengthen their defenses against evolving cyber threats.
Integrate and Optimize Pen Test Tools within Security Frameworks
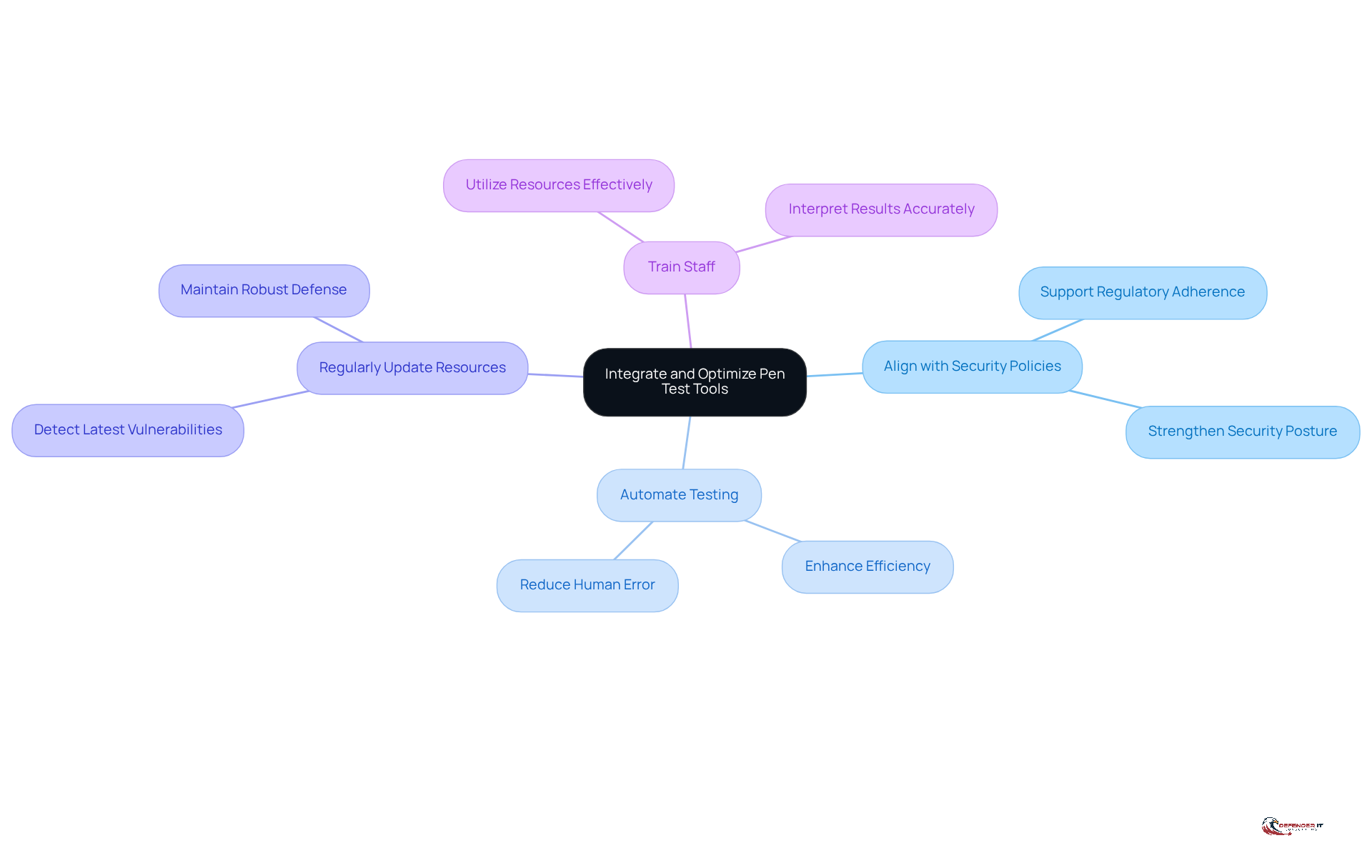
To effectively integrate penetration testing tools into security frameworks, organizations should prioritize the following key practices:
- Align with Security Policies: It is essential to ensure that the use of pen test tools aligns with organizational security policies and compliance requirements. This alignment not only supports regulatory adherence but also strengthens the overall security posture.
- Automate Testing: Where feasible, organizations should automate penetration testing processes. Automation enhances efficiency and significantly reduces the potential for human error, which allows pen test tools to deliver more consistent and reliable testing outcomes.
- Regularly Update Resources: Keeping resources updated is crucial. This practice ensures that the tools can effectively detect the latest vulnerabilities and threats, thereby maintaining a robust defense against emerging risks.
- Train Staff: Providing comprehensive training for personnel on how to utilize these resources effectively is vital. Staff should be equipped to interpret results accurately, which is essential for informed decision-making regarding security measures.
By adhering to these practices, organizations can enhance their security stance and ensure that assessment instruments contribute significant value to their overall security strategy.
Continuously Evaluate and Adapt Pen Test Tools
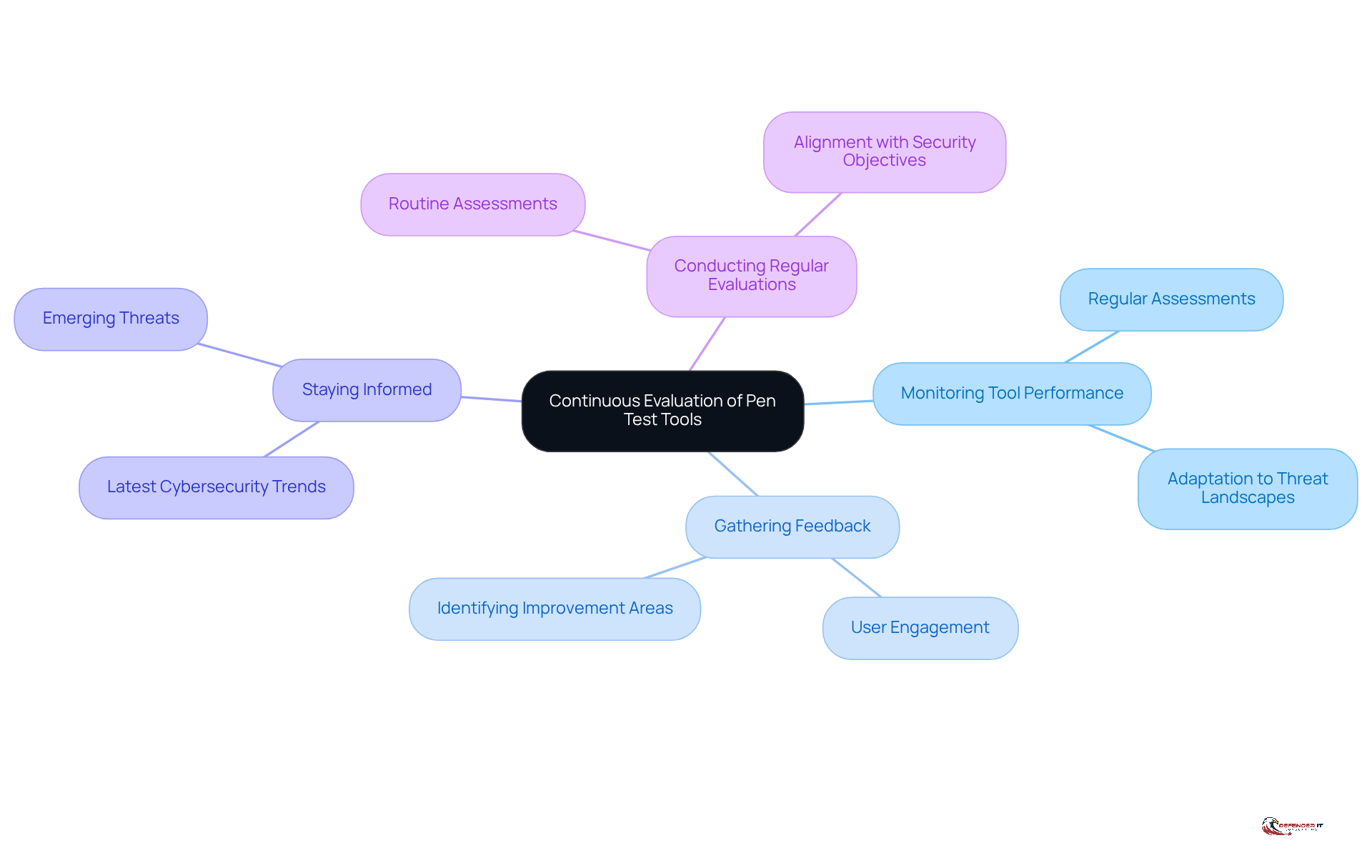
Organizations should implement a continuous evaluation process for their pen test tools to enhance their effectiveness and relevance. This process can be structured around several key components:
- Monitoring Tool Performance: Regular assessments of the tools’ effectiveness in identifying vulnerabilities are essential. This ensures that organizations can adapt to changing threat landscapes.
- Gathering Feedback: Collecting user feedback is crucial for identifying areas that require improvement. Engaging with users provides insights that can lead to more effective tool utilization.
- Staying Informed: Keeping abreast of the latest [cybersecurity trends and threats](https://sentinelone.com/cybersecurity-101/cybersecurity/cybersecurity-metrics) is vital. This knowledge allows organizations to ensure that their resources remain relevant and effective against emerging challenges.
- Conducting Regular Evaluations: Routine assessments of resource effectiveness and relevance to the organization’s protection needs should be arranged. This proactive approach ensures that the use of pen test tools in penetration testing efforts aligns with security objectives.
By adopting this structured approach to tool evaluation, organizations can maintain the effectiveness of their penetration testing initiatives and ensure alignment with their overarching security goals.
Conclusion
Mastering penetration testing tools is crucial for security leaders who seek to safeguard their organizations against the ever-evolving landscape of cyber threats. The effective use of these tools not only identifies vulnerabilities but also strengthens defenses through a proactive and strategic approach to cybersecurity.
Understanding various penetration testing tools – such as network scanners, vulnerability scanners, exploitation frameworks, and web application evaluation tools – is essential. Key criteria for selecting these tools include:
- Functionality
- Ease of use
- Integration capabilities
- Support
- Cost
These factors serve as a foundation for making informed decisions. Moreover, integrating and optimizing these tools within existing security frameworks is vital for enhancing overall security posture. Continuous evaluation ensures that organizations remain adaptive to the dynamic threat landscape.
In conclusion, the cybersecurity landscape is in constant flux, necessitating that organizations stay vigilant in their vulnerability assessment strategies. By adopting best practices for selecting, integrating, and continuously evaluating penetration testing tools, security leaders can significantly bolster their defenses and mitigate risks. Embracing these practices not only protects organizational assets but also cultivates a culture of proactive security that is essential in today’s digital environment.
Frequently Asked Questions
What are penetration testing tools and why are they important?
Penetration testing tools are essential resources used to identify vulnerabilities within an organization’s IT infrastructure, helping to enhance security and protect assets.
What types of penetration testing tools are commonly used?
Common types of penetration testing tools include: – Network Scanners (e.g., Nmap) – Vulnerability Scanners (e.g., Nessus) – Exploitation Frameworks (e.g., Metasploit) – Web Application Evaluation Tools (e.g., Burp Suite)
How does a network scanner like Nmap function?
Nmap is used to identify active devices on a network and their open ports, providing a foundational understanding of the network landscape.
What is the role of vulnerability scanners in penetration testing?
Vulnerability scanners, such as Nessus, scan systems for known vulnerabilities and feature extensive plugins (over 170,000) for comprehensive coverage. They have seen increased reliance for effective vulnerability detection.
What is Metasploit and how is it utilized in penetration testing?
Metasploit is an exploitation framework that allows professionals to exploit vulnerabilities in a controlled environment, aiding in the evaluation of defenses against real-world attack scenarios.
How does Burp Suite assist in web application security assessments?
Burp Suite is used to assess web applications for security flaws, providing detailed analysis and remediation options for identified vulnerabilities.
What trends are expected in the penetration testing tools market by 2026?
The market is expected to evolve towards continuous assessments integrated with CI/CD pipelines, allowing organizations to reduce exposure rapidly and improve remediation timelines.
Can you provide an example of the effectiveness of penetration testing tools?
In 2025, proactive protection evaluations utilizing these tools prevented an estimated $2.88 billion in potential losses, particularly from vulnerabilities in web and API exposures.
What is the importance of incorporating penetration testing tools into security practices?
Incorporating these tools is vital for effective vulnerability evaluation and management, as they help organizations remain vigilant and proactive against evolving threats.
What common pitfalls should organizations avoid when conducting vulnerability assessments?
Organizations should avoid treating vulnerability assessments as mere checkbox tasks and instead view them as ongoing strategic components of protective practices.
List of Sources
- Understand the Fundamentals of Penetration Testing Tools
- At RSAC 2026, AI Redefines the Future of Penetration Testing (https://securityboulevard.com/2026/04/at-rsac-2026-ai-redefines-the-future-of-penetration-testing)
- Top 15 Penetration Testing Tools In 2026 | CloudSEK (https://cloudsek.com/knowledge-base/top-penetration-testing-tools)
- The 2026 State of Pentesting: How Modern Teams Manage and Deliver Results (https://thehackernews.com/expert-insights/2026/01/the-2026-state-of-pentesting-how-modern.html)
- Penetration Testing Trends 2026: Insights & Predictions (https://getastra.com/blog/penetration-testing/trends)
- The Most Popular Penetration Testing Tools in 2026 – PlexTrac (https://plextrac.com/the-most-popular-penetration-testing-tools-this-year)
- Establish Criteria for Selecting Pen Test Tools
- 7 Expert Tips to Choose Pen Testing Software for Businesses (https://zerothreat.ai/blog/tips-to-choose-pentesting-software)
- Top 10 Considerations for Choosing a Penetration Testing Vendor | CISO Global (https://ciso.inc/blog-posts/top-10-considerations-for-choosing-a-penetration-testing-vendor)
- Top 5 penetration testing tools every security professional must master (https://community.trustcloud.ai/article/top-5-penetration-testing-tools-every-security-pro-must-have)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Integrate and Optimize Pen Test Tools within Security Frameworks
- How Pentesting Fits Into a 2026 Security Game Plan – Blog – NopSec (https://nopsec.com/blog/how-pentesting-fits-into-a-2026-security-game-plan)
- The 2026 State of Pentesting: How Modern Teams Manage and Deliver Results (https://thehackernews.com/expert-insights/2026/01/the-2026-state-of-pentesting-how-modern.html)
- The 2026 State of Pentesting: Why delivery and follow-through matter more than ever – Help Net Security (https://helpnetsecurity.com/2026/01/21/plextrac-pentest-programs-reporting)
- 83 Penetration Testing Statistics: Key Facts and Figures (https://getastra.com/blog/penetration-testing/statistics)
- 100+ essential penetration testing statistics [2023 edition] (https://pentest-tools.com/blog/penetration-testing-statistics)
- Continuously Evaluate and Adapt Pen Test Tools
- At RSAC 2026, AI Redefines the Future of Penetration Testing (https://securityboulevard.com/2026/04/at-rsac-2026-ai-redefines-the-future-of-penetration-testing)
- The 2026 State of Pentesting: How Modern Teams Manage and Deliver Results (https://thehackernews.com/expert-insights/2026/01/the-2026-state-of-pentesting-how-modern.html)
- Cybersecurity Metrics & KPIs: What to Track in 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cybersecurity-metrics)
- 3 Predictions for Continuous Pentesting in 2026 – BreachLock (https://breachlock.com/resources/blog/3-predictions-for-continuous-pentesting-in-2026)
- 20 Cybersecurity Metrics & KPIs to Track in 2025 – SecurityScorecard (https://securityscorecard.com/resources/learning-center/9-cybersecurity-metrics-kpis-to-track)