Introduction
NIST 800-171 Rev 3 serves as a vital framework for organizations responsible for protecting Controlled Unclassified Information (CUI). As compliance becomes increasingly critical for securing federal contracts, understanding this guide is essential. It outlines the streamlined requirements of the latest revision, providing organizations with a pathway to enhance their cybersecurity posture while navigating the complexities of compliance.
Despite its importance, the average implementation rate stands at a concerning 39%, indicating that many entities encounter significant challenges in achieving full adherence. To address these issues, organizations must adopt effective strategies that not only fulfill these requirements but also safeguard their sensitive information against evolving threats.
Understand NIST 800-171 Rev 3
provides essential guidelines for protecting Controlled Unclassified Information (CUI) in non-federal systems. This framework comprises 97 requirements categorized into 17 families, addressing essential areas such as access control, incident response, and system integrity. Adherence to these requirements is vital for entities managing CUI, particularly as compliance is often a prerequisite for federal contracts.
Recent updates in Revision 3 reflect a streamlined approach, reducing the total number of requirements from 110 in the previous version while enhancing clarity and specificity. Notably, the introduction of 45 mandates that entities specify particular values for their security controls, ensuring a tailored approach to compliance.
Despite these advancements, the current regulatory landscape indicates that no organizations have achieved full adherence to 800-171 controls, with an average implementation rate of only 39%. This statistic underscores the ongoing challenges faced by many, particularly in sectors such as healthcare and construction, which exhibit lower adherence rates compared to manufacturing and software development. Small to mid-sized companies, on average, have implemented only 34% of the controls, highlighting the resource constraints they encounter.
Experts stress the . A recent analysis suggested that had the 800-171 controls been effectively applied, numerous or their impacts significantly mitigated. This underscores the necessity for companies to .
Real-world examples further illustrate the effectiveness of these guidelines. A defense contractor based in New England improved its adherence from 35% to a ‘low-risk rating’ following a , demonstrating the tangible benefits of implementing 800-171 controls.
In summary, understanding and applying the is crucial for entities that process, store, or transmit CUI. By doing so, they not only enhance their cybersecurity posture but also align with federal compliance mandates, ultimately protecting sensitive information from unauthorized access and loss.
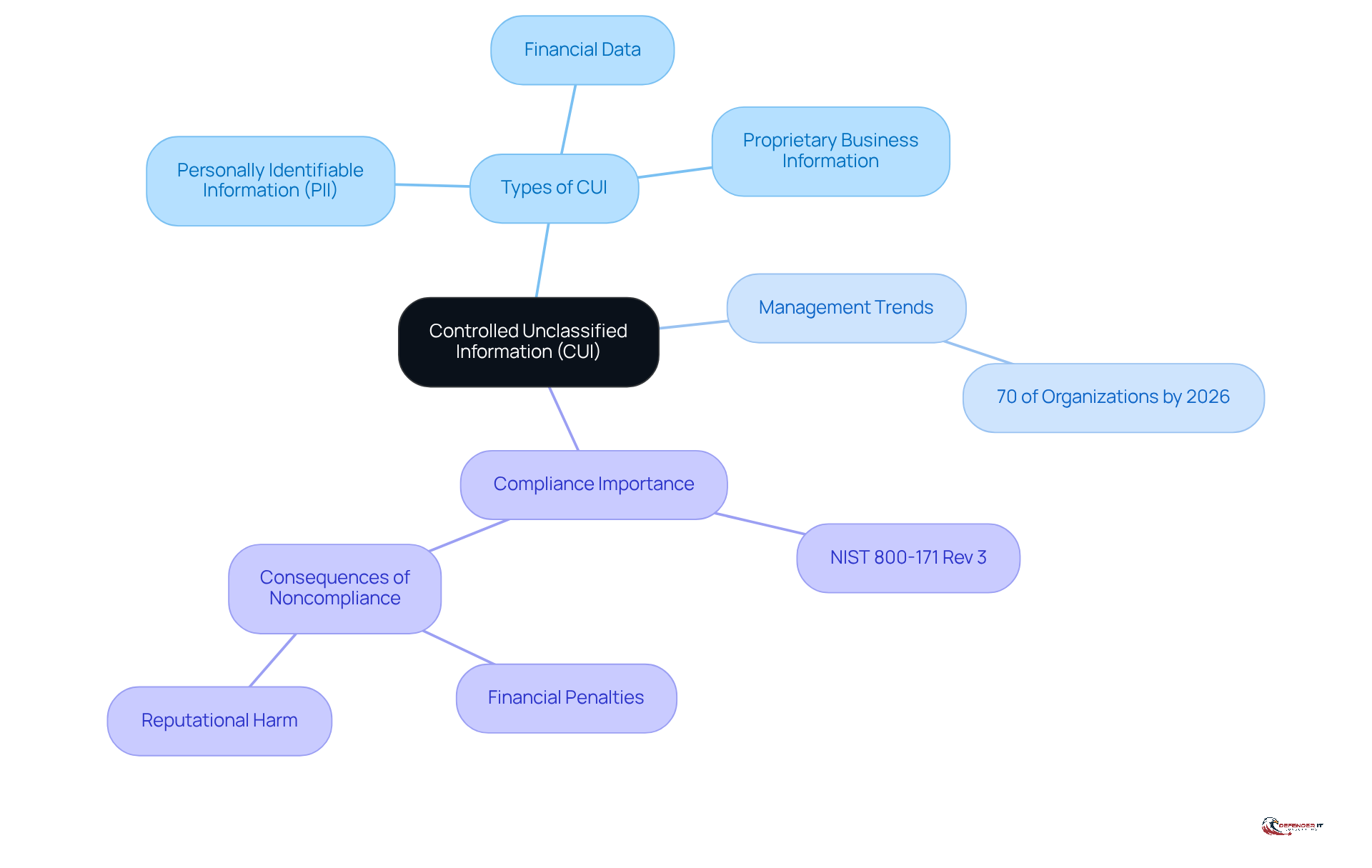
Define Controlled Unclassified Information (CUI)
is sensitive information that necessitates . It encompasses various types of data, including:
- Personally identifiable information (PII)
- Financial data
- Proprietary business information
By 2026, it is anticipated that around 70% of organizations, especially those in regulated sectors, will be managing CUI.
To effectively implement , organizations must first identify and categorize CUI. The , provided by the National Archives, offers detailed information on different categories and instances of CUI, ensuring compliance with . As cybersecurity expert Emil Sayegh points out, “For federal contractors, is no longer a theoretical risk.” This statement underscores the urgent need for organizations to recognize that failing to protect this information can result in severe consequences, including .
for adhering to demonstrate . Such measures not only enhance their defense posture but also bolster operational resilience.
Identify NIST 800-171 Compliance Requirements
Achieving requires implementing 97 requirements categorized into 14 families. The key areas include:
- : Access to Controlled Unclassified Information (CUI) must be restricted to authorized personnel only. This is crucial for protecting sensitive data from unauthorized access. Notably, 60% of small businesses that experience a cyberattack go out of business within six months.
- Awareness and Training: Comprehensive instruction for all personnel on protection policies and procedures is essential to foster a culture of safety awareness.
- Audit and Accountability: Maintaining detailed logs of access and modifications to CUI is vital for accountability and forensic analysis in the event of a breach.
- Configuration Management: Establishing and maintaining baseline configurations for systems ensures consistent protection settings across the organization.
- : Developing and implementing a robust is necessary. This plan should outline procedures for detecting, responding to, and recovering from security incidents.
Organizations should review the for a complete list of requirements and consider conducting a to identify areas needing enhancement. This analysis is critical, as it helps entities understand their current adherence status; 52% of public entities cite . Involving can provide valuable insights into effectively applying these protective measures. As Emily Bonnie, a Digital Marketing Strategist, notes, simplifying complex regulatory subjects is essential for businesses. Furthermore, entities should recognize that the time required to achieve compliance with can vary significantly based on existing security protocols and assets. Specific examples of entities successfully implementing and incident response can further illustrate effective strategies for compliance.
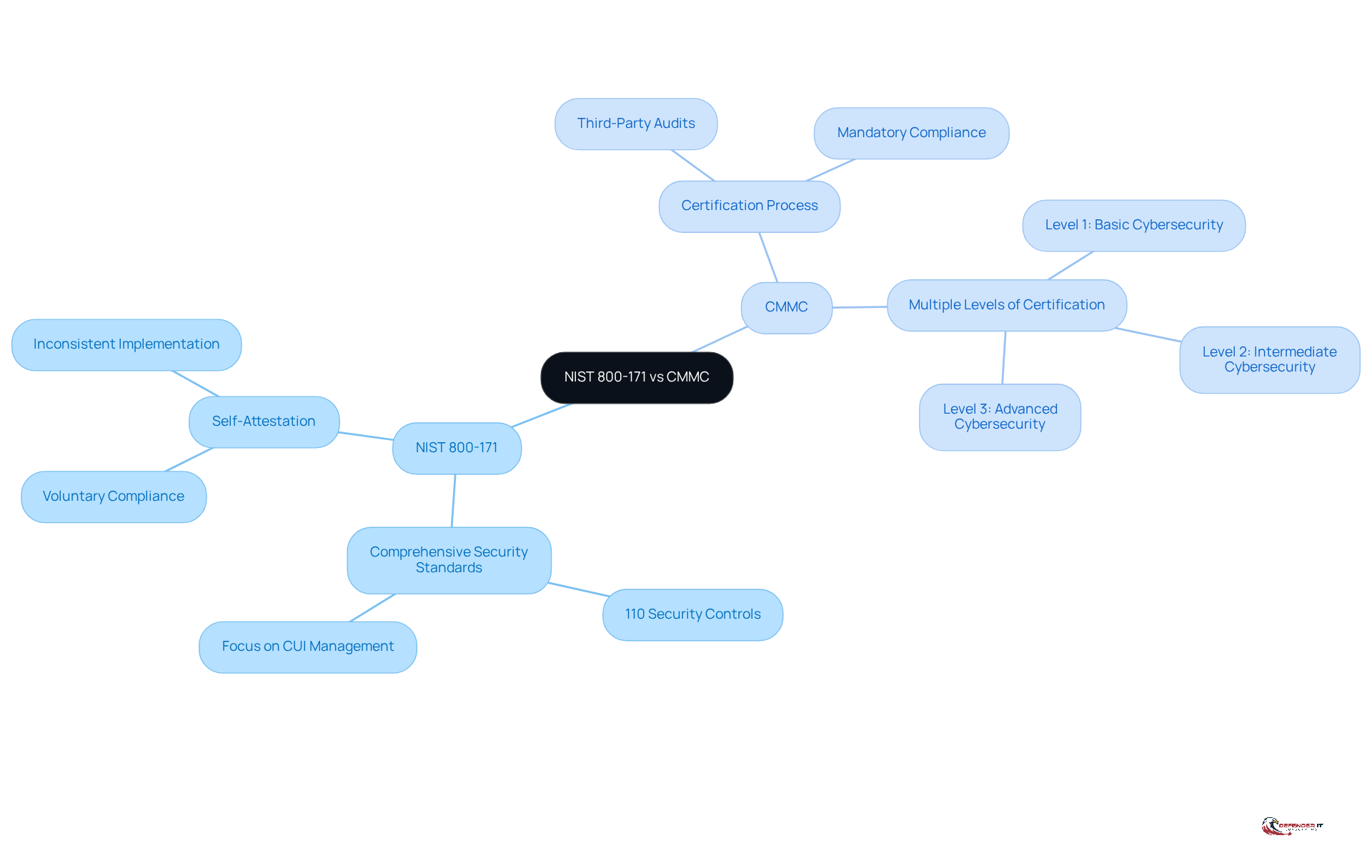
Differentiate NIST 800-171 from CMMC
The and the are essential frameworks for , with each serving distinct functions.
The provides a comprehensive set of security standards for organizations that manage CUI. In contrast, CMMC is a certification process that assesses an organization’s compliance with these standards. Notably, , with higher levels imposing more rigorous controls.
Understanding these distinctions is crucial for and with .
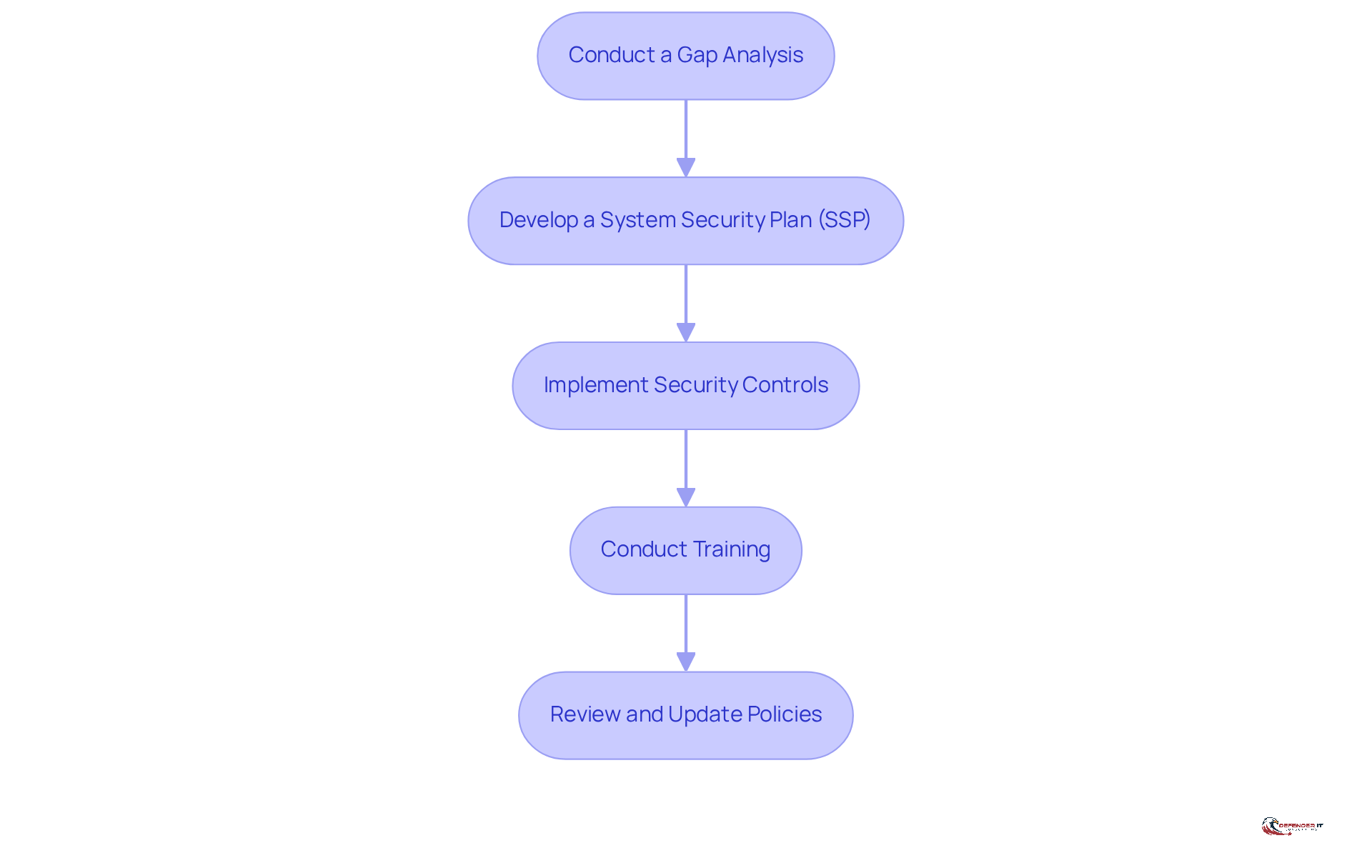
Utilize the NIST 800-171 Compliance Checklist
A conformity checklist serves as an essential tool for organizations striving to meet the standards. Below is a streamlined checklist designed to guide your efforts:
- Conduct a : Assess your existing protective measures against . This step is vital, as experts emphasize that a thorough identifies vulnerabilities and areas needing improvement. Organizations typically invest an average of 12-18 months on this analysis to ensure comprehensive conformity. As Kay Pang noted, “Boards must recognize , not just an IT issue,” underscoring the significance of this analysis within the broader context of organizational risk management.
- Develop a (SSP): Document how you will meet each requirement, detailing the specific controls and processes in place. This plan should also include any unimplemented protection requirements, which must be documented separately in the SSP.
- Implement : Apply the necessary technical and administrative controls to safeguard (CUI).
- Conduct Training: Ensure all employees are well-informed about their roles in maintaining safety, as awareness is crucial for effective adherence.
- Review and Update Policies: Regularly revisit your to ensure they remain effective and aligned with evolving standards.
Utilize materials from trusted institutions to download that can assist in simplifying your adherence process. Involving regulatory specialists can also enhance your initiatives, particularly if your organization lacks internal cybersecurity expertise. It is important to remember that failing to comply with can lead to , including contract termination and fines.
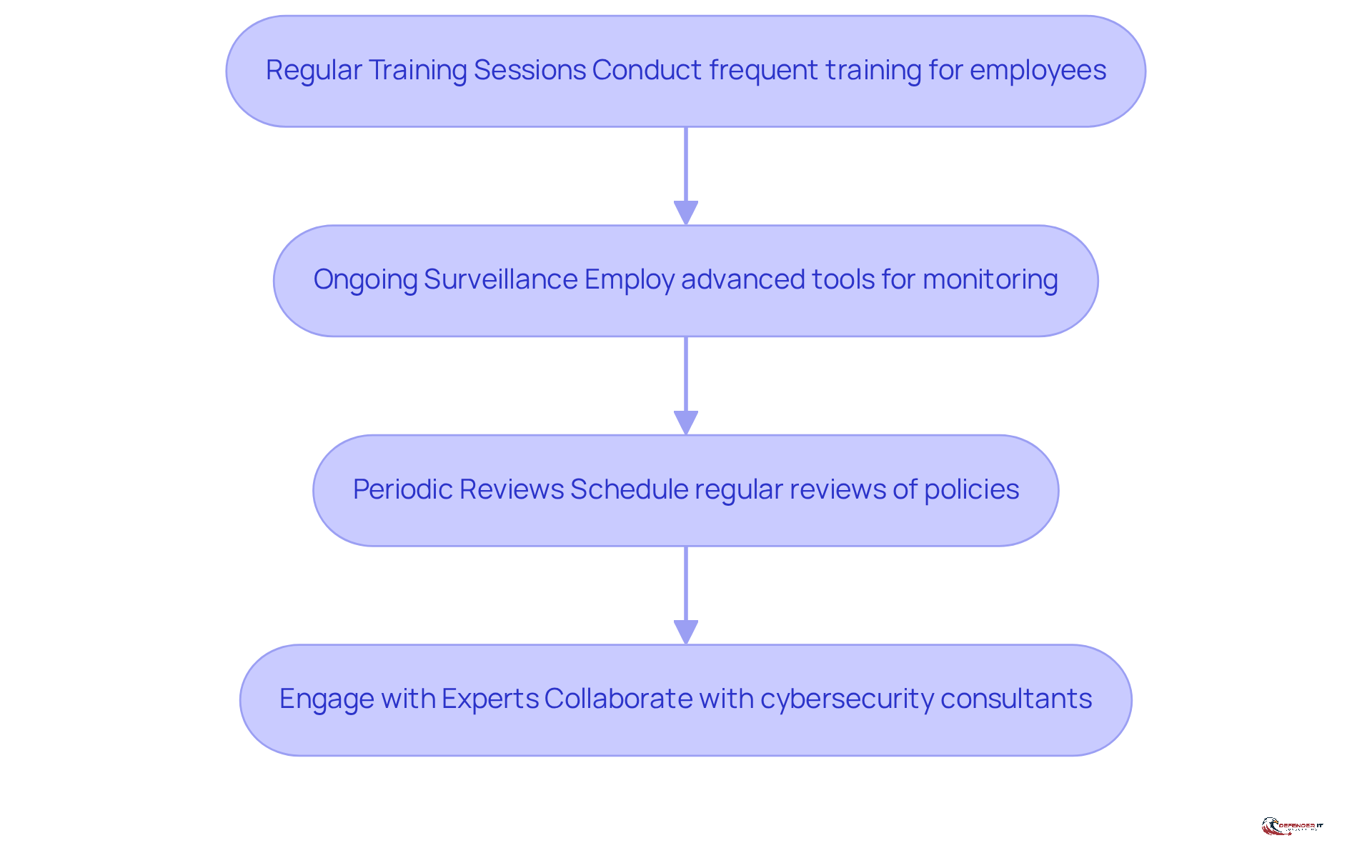
Implement Ongoing Support and Training
Achieving compliance with NIST 800-171 rev 3 requires an ongoing commitment to continuous support and training. To ensure sustained compliance, consider the following essential steps:
- : Conduct frequent training for employees on best practices regarding safety and updates to policies. Research indicates that approximately 73% of organizations that hold experience a significant reduction in compliance-related incidents.
- Ongoing Surveillance: Employ advanced tools to consistently monitor adherence and swiftly identify potential breach incidents. not only enhances visibility but also allows organizations to address regulatory gaps in real time, reducing the average detection time from 197 days to under 24 hours. Companies that implement report a 60% faster incident response time and a 40% decrease in compliance-related costs compared to traditional audit methods.
- : Schedule regular reviews of security policies and procedures to adapt to evolving threats. This proactive approach helps businesses stay ahead of regulatory demands and mitigates risks associated with outdated practices. The Digital Operational Resilience Act (DORA), effective January 2025, mandates [continuous monitoring](https://firemon.com/blog/continuous-compliance-monitoring) for financial services organizations, underscoring the necessity for ongoing compliance efforts.
- : Collaborate with cybersecurity consultants for . Their expertise can provide valuable insights into maintaining compliance and strengthening protective measures. As one cybersecurity expert noted, “Continuous monitoring provides real-time insight into adherence status, allowing for prompt identification and resolution of issues as they arise.”
By cultivating a culture of security awareness and continuous improvement, organizations can effectively protect their (CUI) and comply with NIST 800-171 Rev 3. Furthermore, it is crucial for organizations to recognize the substantial financial repercussions of non-compliance, as illustrated by the Equifax data breach, which incurred costs exceeding $700 million due to insufficient compliance measures.
Conclusion
Prioritizing compliance with NIST 800-171 Rev 3 is essential for organizations managing Controlled Unclassified Information (CUI). This framework not only delineates critical security requirements but also aligns with federal compliance mandates, ensuring sensitive data is adequately protected. As cybersecurity threats evolve, adherence to these guidelines becomes increasingly vital for safeguarding information and maintaining trust in organizational operations.
Key points throughout the article underscore the significance of NIST 800-171 Rev 3. These include:
- Streamlined requirements
- The necessity of tailored security measures
- The ongoing challenges organizations encounter in achieving compliance
With an average implementation rate of only 39%, it is evident that many entities, particularly small to mid-sized companies, face resource constraints. Furthermore, the article highlights the preventive potential of these controls in mitigating data breaches and emphasizes the need for continuous training and monitoring to uphold compliance.
Organizations must recognize that compliance with NIST 800-171 Rev 3 is not merely a regulatory obligation; it is a crucial investment in their cybersecurity posture. By fostering a culture of security awareness, conducting regular training, and engaging with cybersecurity experts, organizations can bolster their resilience against potential threats. Taking proactive steps toward compliance will not only protect sensitive information but also ensure long-term operational success in an increasingly regulated environment.
Frequently Asked Questions
What is NIST 800-171 Rev 3?
NIST 800-171 Rev 3 provides guidelines for protecting Controlled Unclassified Information (CUI) in non-federal systems. It includes 97 requirements across 17 families, focusing on areas like access control, incident response, and system integrity.
How has NIST 800-171 Rev 3 changed from previous versions?
Revision 3 has streamlined the framework by reducing the number of requirements from 110 to 97, enhancing clarity and specificity. It also introduces 45 Organizationally Defined Parameters (ODPs) that require entities to specify values for their security controls.
What is the current compliance status with NIST 800-171 controls?
As of now, no organizations have achieved full compliance with NIST 800-171 controls, with an average implementation rate of only 39%. Sectors like healthcare and construction show lower adherence rates compared to manufacturing and software development.
What is Controlled Unclassified Information (CUI)?
Controlled Unclassified Information (CUI) is sensitive data that requires protection but is not classified. It includes personally identifiable information (PII), financial data, and proprietary business information.
Why is it important for organizations to comply with NIST 800-171 Rev 3?
Compliance is crucial as it enhances cybersecurity measures and aligns with federal mandates, helping to protect sensitive information from unauthorized access. Noncompliance can lead to financial penalties and reputational damage.
What resources are available to help organizations manage CUI?
The CUI Registry provided by the National Archives offers detailed information on different categories of CUI, which is essential for compliance with NIST 800-171 Rev 3.
Can you provide an example of successful adherence to NIST 800-171?
A defense contractor in New England improved its compliance from 35% to a ‘low-risk rating’ after a successful audit by the Department of Defense, demonstrating the benefits of implementing NIST 800-171 controls.
What are the potential consequences of failing to protect CUI?
Organizations that fail to safeguard CUI may face severe consequences, including financial penalties and damage to their reputation.