Introduction
Navigating the landscape of CMMC compliance is crucial for contractors working with the Department of Defense, particularly as the stakes in cybersecurity continue to escalate. This article presents a comprehensive checklist aimed at guiding organizations through the necessary steps to achieve and maintain CMMC compliance, thereby ensuring the protection of sensitive information.
With deadlines approaching and the complexity of the compliance framework increasing, contractors must prepare effectively to meet these stringent requirements without falling behind.
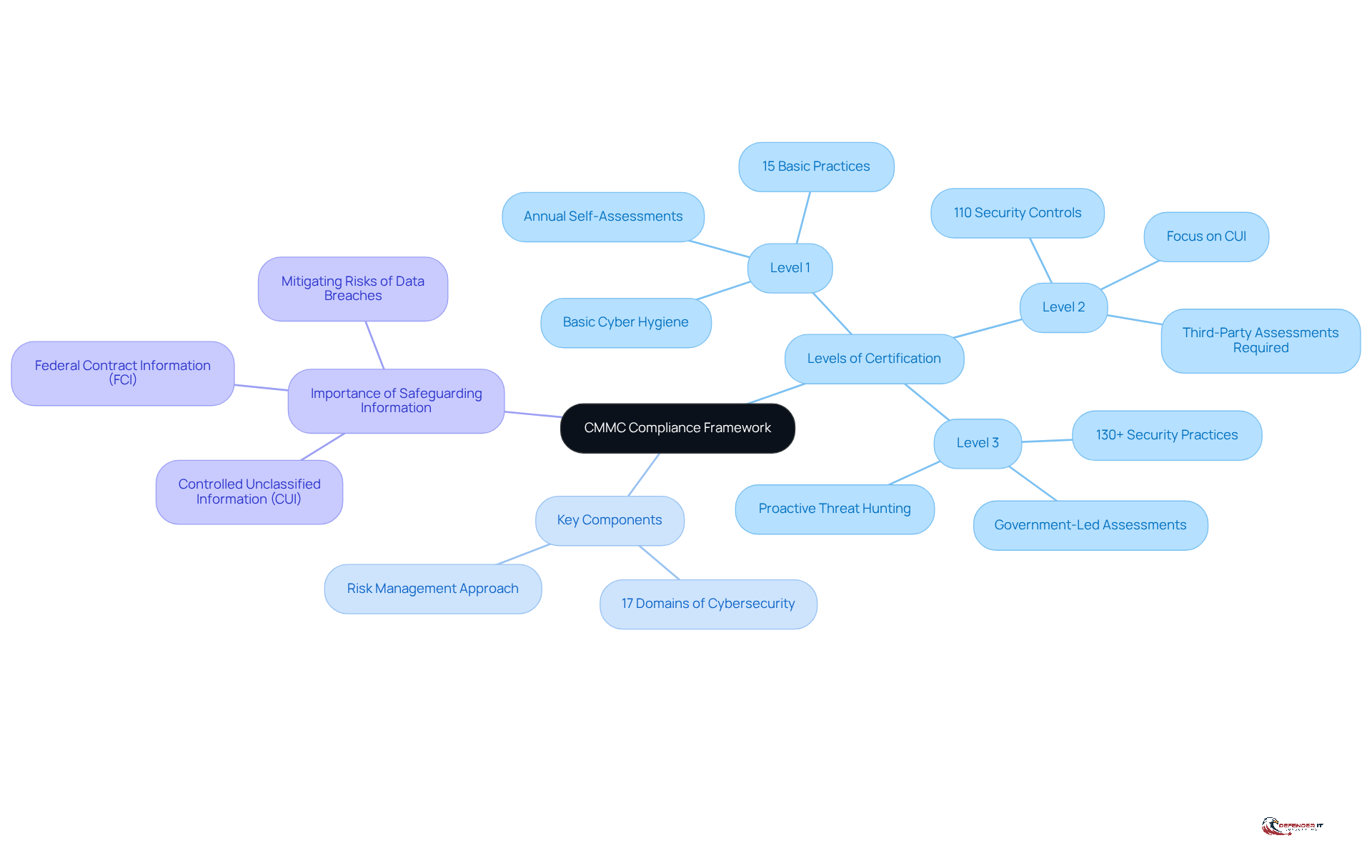
Understand CMMC Compliance Framework
Familiarize yourself with CMMC compliance for DOD contractors, which is based on the Cybersecurity Maturity Model Certification framework consisting of three levels of certification tailored to the sensitivity of the information handled by contractors. Level 1 emphasizes basic cyber hygiene, while Levels 2 and 3 necessitate more stringent controls and assessments.
Review the key components of the framework, which encompass 17 domains addressing various aspects of cybersecurity. This ensures a comprehensive approach to risk management.
Recognize the critical importance of safeguarding Controlled Unclassified Information (CUI) and Federal Contract Information (FCI). With the increasing scrutiny on cybersecurity adherence, organizations must prioritize these protections to and nonconformity, which can lead to significant financial and reputational damage. As noted by Alston & Bird, organizations seeking CMMC compliance for DOD contractors should already be reviewing the data they process on behalf of the DoD.
Examine the staged execution schedule, which mandates adherence for new solicitations and contracts starting November 10, 2026. This highlights the urgency for contractors to prepare and align their security practices with relevant standards. The transition to CMMC will be finalized by November 10, 2028.
Utilize resources from the Department of Defense and cybersecurity experts to enhance your understanding of the framework. Engaging with Certified Third-Party Assessment Organizations (C3PAOs) can provide valuable insights and assistance in navigating regulatory challenges, ensuring that organizations are well-prepared to meet the evolving cybersecurity landscape. Furthermore, contractors must conduct annual assessments of their compliance and post results to the Supplier Performance Risk System (SPRS) to maintain eligibility for contract awards.
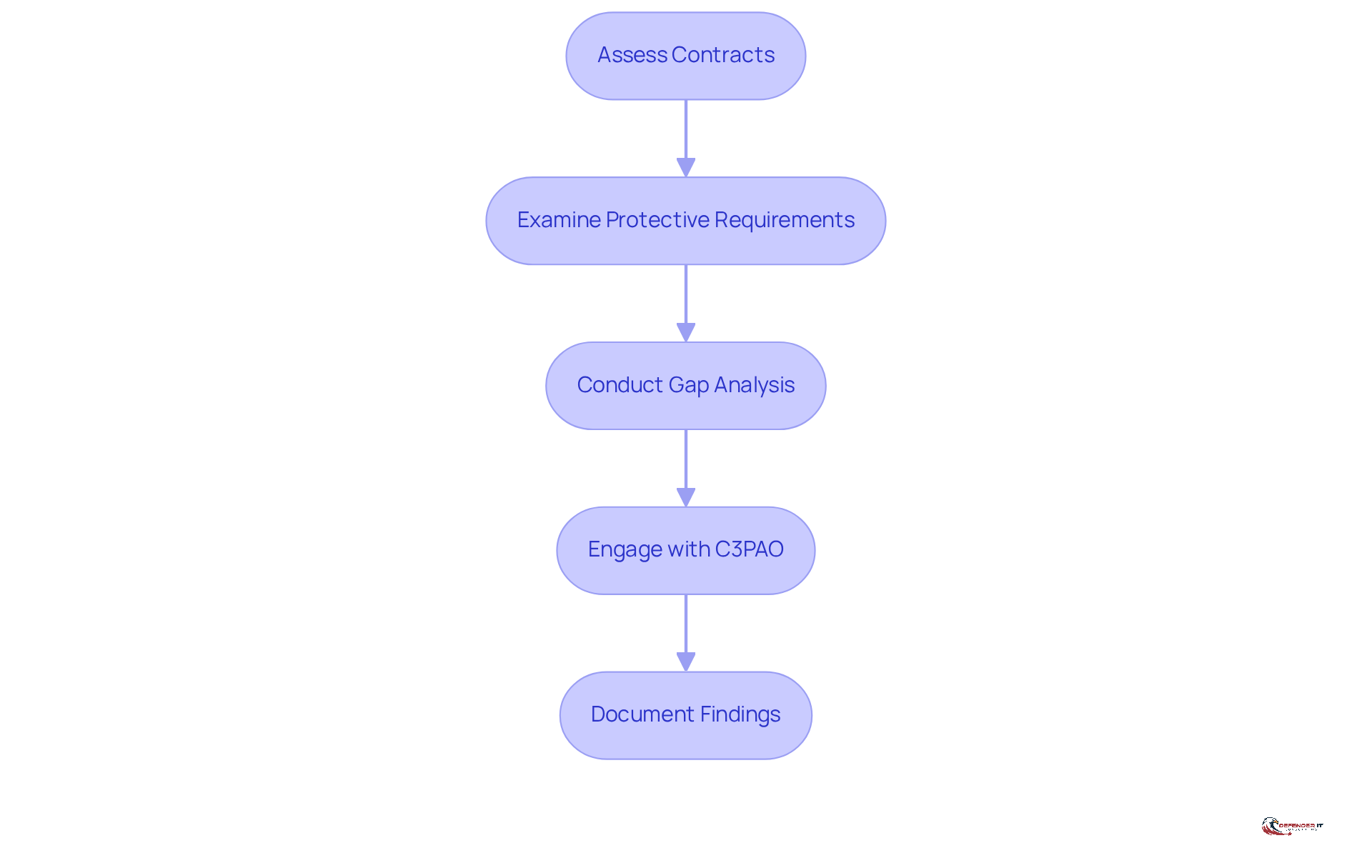
Identify Required CMMC Compliance Levels
- Assess the contracts you are bidding on to determine the required [CMMC compliance for DOD contractors](https://defenderit.consulting), which may be Level 1, 2, or 3.
- Examine the specific associated with each tier, including the number of measures that must be implemented.
- Conduct a gap analysis to identify current security practices in relation to the required controls for achieving CMMC compliance for DOD contractors at your designated level.
- Engage with a Certified Third-Party Assessment Organization (C3PAO) to clarify any uncertainties regarding adherence levels.
- Document your findings to develop a comprehensive plan for achieving the required standard.
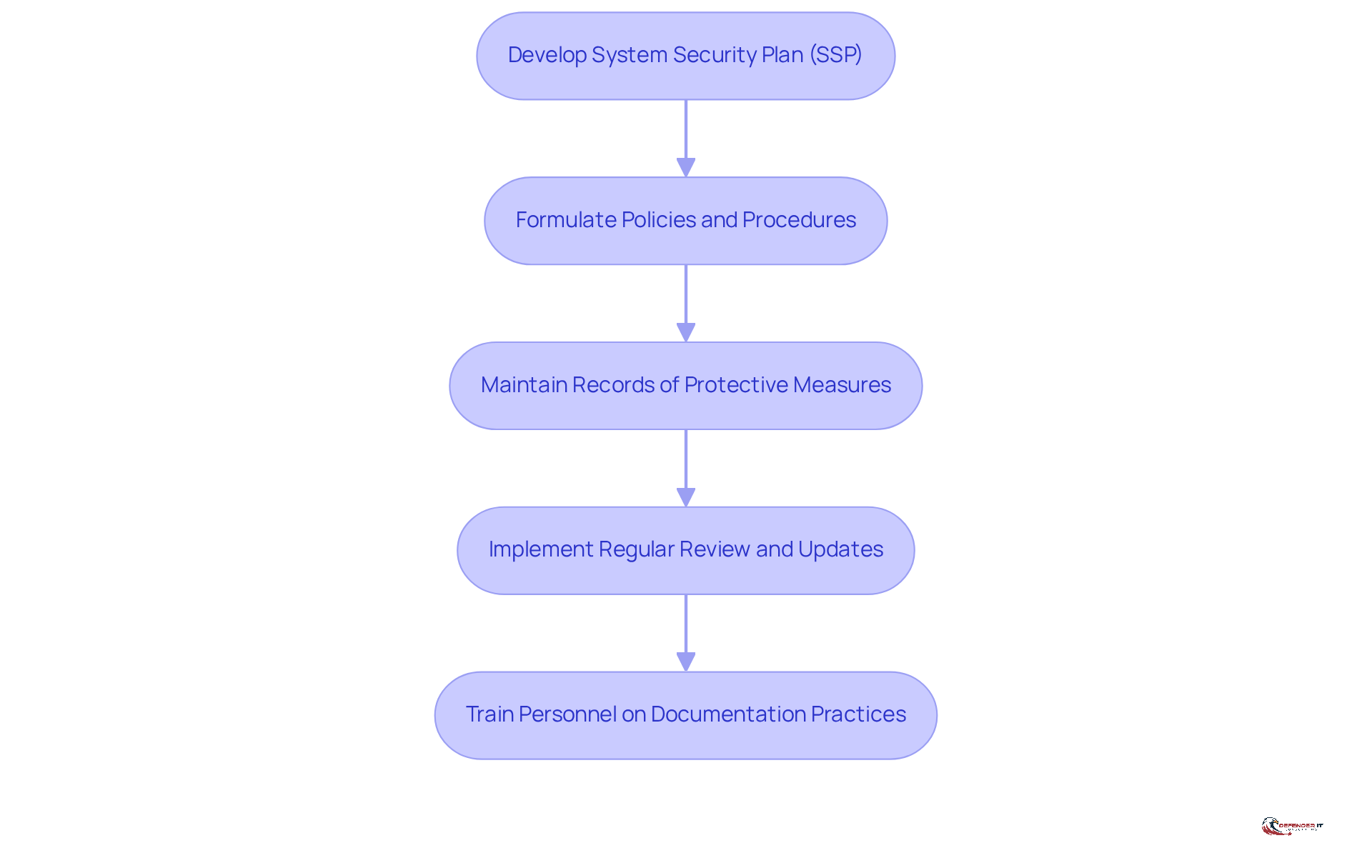
Prepare Documentation and Processes for Compliance
- Develop a comprehensive System Security Plan (SSP) that articulates your organization’s security practices and demonstrates compliance with relevant requirements. This document serves as the foundation for compliance and must detail the implementation of each of the 110 measures outlined in NIST SP 800-171. It is crucial to recognize that inaccuracies in your SSP can adversely affect all subsequent processes.
- Formulate specific policies and procedures that address each of the 17 domains within the CMMC framework. Clarity is paramount; for instance, policies should explicitly define access management strategies and incident response protocols to eliminate any ambiguity during evaluations.
- Maintain meticulous records of all protective measures enacted, including evidence of compliance and documentation of evaluations conducted. This documentation must be directly aligned with the assessment objectives to ensure transparency and prevent discrepancies. Your SSP should reflect what is , rather than what is merely planned or partially implemented.
- Implement a systematic approach for the regular review and updating of documentation to capture any changes in protective measures or regulatory requirements. SSPs should be revised at least annually to ensure they remain relevant and effective.
- Ensure that all pertinent personnel receive adequate training on documentation practices and comprehend their responsibilities in upholding compliance. Training should emphasize the importance of aligning documented policies with actual practices to reduce audit findings and enhance overall security measures.
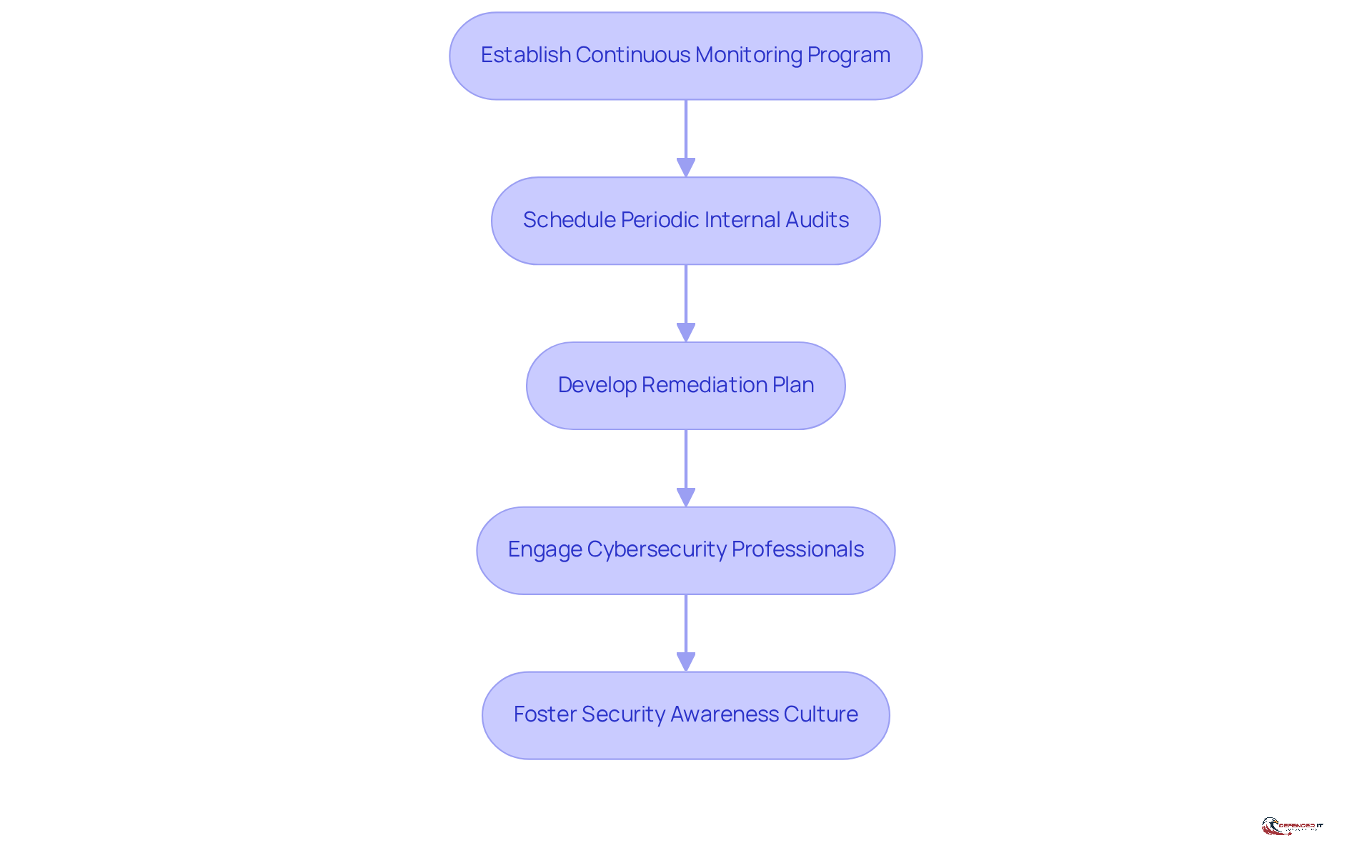
Establish Continuous Assessment and Remediation Plans
- Establish a continuous monitoring program to regularly evaluate the effectiveness of protective measures and identify potential weaknesses. This proactive approach ensures that any vulnerabilities are promptly addressed, thereby enhancing overall security posture.
- Schedule periodic internal audits to assess adherence to CMMC compliance for DOD contractors and to identify areas for improvement. These audits serve as a critical tool for maintaining CMMC compliance for DOD contractors and fostering a culture of accountability within the organization.
- Develop a remediation plan that outlines steps to address any identified deficiencies, including timelines and responsible parties. This structured approach facilitates timely resolution of issues and reinforces .
- Engage with cybersecurity professionals to conduct regular penetration testing and vulnerability assessments. Such assessments are essential for identifying potential threats and ensuring that protective measures are effective against evolving risks.
- Foster a culture of security awareness within the organization to ensure all employees understand their role in maintaining compliance. By prioritizing security education, organizations can empower their workforce to contribute actively to compliance efforts.
Conclusion
Fulfilling CMMC compliance for DoD contractors is not just a regulatory obligation; it is a crucial commitment to safeguarding sensitive information and enhancing cybersecurity resilience. This structured framework, which encompasses three certification levels, provides a clear pathway for organizations to align their practices with essential security standards. By prioritizing the protection of Controlled Unclassified Information (CUI) and Federal Contract Information (FCI), contractors can effectively mitigate risks and position themselves favorably in a competitive landscape.
Key steps in achieving compliance include:
- Understanding the CMMC framework
- Identifying required compliance levels
- Preparing thorough documentation
- Establishing ongoing assessment and remediation plans
Each of these components plays a vital role in not only meeting regulatory demands but also fostering a culture of security awareness and accountability within organizations. Engaging with Certified Third-Party Assessment Organizations (C3PAOs) and utilizing available resources will further enhance the compliance journey.
Ultimately, transitioning to CMMC compliance represents an opportunity for DoD contractors to strengthen their cybersecurity posture and instill confidence in their capabilities. As the deadline approaches, proactive measures and continuous improvement should be at the forefront of every contractor’s strategy, ensuring they are well-prepared to meet the evolving demands of the cybersecurity landscape. Embracing these steps now will not only facilitate compliance but also secure a competitive edge in future government contracting opportunities.
Frequently Asked Questions
What is the CMMC compliance framework?
The CMMC compliance framework is designed for Department of Defense (DOD) contractors and is based on the Cybersecurity Maturity Model Certification. It consists of three certification levels tailored to the sensitivity of the information handled, with Level 1 focusing on basic cyber hygiene and Levels 2 and 3 requiring more stringent controls and assessments.
What are the key components of the CMMC framework?
The CMMC framework encompasses 17 domains that address various aspects of cybersecurity, ensuring a comprehensive approach to risk management.
Why is safeguarding Controlled Unclassified Information (CUI) and Federal Contract Information (FCI) important?
Safeguarding CUI and FCI is critical due to increasing scrutiny on cybersecurity adherence. Organizations must prioritize these protections to mitigate risks associated with data breaches and nonconformity, which can lead to significant financial and reputational damage.
When does adherence to CMMC compliance become mandatory for new contracts?
Adherence to CMMC compliance for new solicitations and contracts becomes mandatory starting November 10, 2026, with the transition to CMMC being finalized by November 10, 2028.
What resources are available to help organizations understand the CMMC framework?
Organizations can utilize resources from the Department of Defense and cybersecurity experts. Engaging with Certified Third-Party Assessment Organizations (C3PAOs) can provide valuable insights and assistance in navigating regulatory challenges.
What is required for contractors to maintain eligibility for contract awards?
Contractors must conduct annual assessments of their compliance with the CMMC framework and post the results to the Supplier Performance Risk System (SPRS) to maintain eligibility for contract awards.
List of Sources
- Understand CMMC Compliance Framework
- CMMC: New Era of Cybersecurity Compliance for Defense Contractors | Alston & Bird (https://alston.com/en/insights/publications/2025/11/cmmc-cybersecurity-compliance-defense)
- CMMC Basics: A Practical 2026 Roadmap for CMMC Compliance (https://securitymetrics.com/blog/cmmc-compliance-roadmap)
- Federal News Network’s Risk & Compliance Exchange 2026 | Federal News Network (https://federalnewsnetwork.com/cme-event/exchanges/federal-news-networks-risk-compliance-exchange-2026)
- GSA’s New CUI Requirements: What Government Contractors Need to Know | Insights | Holland & Knight (https://hklaw.com/en/insights/publications/2026/03/gsas-new-cui-security-requirements-what-government-contractors)
- GSA Issues New Framework for Protecting CUI in Contractor Systems – Government Contracts Navigator (https://governmentcontractsnavigator.com/2026/02/02/gsa-issues-new-framework-for-protecting-cui-in-contractor-systems)
- Identify Required CMMC Compliance Levels
- CMMC Levels Explained: What Contractors Need to Know in 2026 (https://blogs.usfcr.com/cmmc-levels-2025)
- Planning Your 2026 CMMC Compliance Roadmap (https://cybersheath.com/resources/blog/planning-your-2026-cmmc-compliance-roadmap)
- The Inevitable Shift: Why CMMC Compliance is Now a Non-Negotiable for DoD Contractors (https://iquasar.com/blog/the-inevitable-shift-why-cmmc-compliance-is-now-a-non-negotiable-for-dod-contractors)
- CMMC Basics: A Practical 2026 Roadmap for CMMC Compliance (https://securitymetrics.com/blog/cmmc-compliance-roadmap)
- CMMC Phase 1 Begins November 10, Raising Complex Compliance and Enforcement Risks for Federal Defense Contractors (https://dorsey.com/newsresources/publications/client-alerts/2025/11/cmmc)
- Prepare Documentation and Processes for Compliance
- Planning Your 2026 CMMC Compliance Roadmap (https://cybersheath.com/resources/blog/planning-your-2026-cmmc-compliance-roadmap)
- What Should Be in Your System Security Plan (SSP) for CMMC Level 2? (https://isidefense.com/blog/what-should-be-in-your-system-security-plan-ssp-for-cmmc-level-2)
- Preparing for a CMMC Audit: The System Security Plan | Insights | Greenberg Traurig LLP (https://gtlaw.com/en/insights/2025/10/preparing-for-a-cmmc-audit-the-system-security-plan)
- The Definitive Guide to CMMC in 2026 (https://strikegraph.com/blog/cmmc-overview)
- CMMC 2.0 in 2026: What’s New and What Organizations Must Know – Accorian (https://accorian.com/cmmc-2-0-in-2026-whats-new-and-what-organizations-must-know)
- Establish Continuous Assessment and Remediation Plans
- Watchdog urges DOD to address external factors affecting CMMC implementation (https://defensescoop.com/2026/03/12/cmmc-implementation-gao-report-kirsten-davies-dod-cio)
- Federal News Network’s Risk & Compliance Exchange 2026 | Federal News Network (https://federalnewsnetwork.com/cme-event/exchanges/federal-news-networks-risk-compliance-exchange-2026)
- Navigating CMMC Compliance Now That It’s 2026 – Helixstorm (https://helixstorm.com/compliance/navigating-cmmc-compliance-now-that-its-2026)
- Navigating CMMC Changes in 2026: What You Need to Know (https://vc3.com/blog/navigating-cmmc-changes-in-2026)
- CMMC 2026: Continuous Monitoring — The Discipline That Sustains Affirmation (https://linkedin.com/pulse/cmmc-2026-continuous-monitoring-discipline-sustains-cissp-pmp-mba-0yhqe)