Introduction
Manufacturers face escalating cyber threats that jeopardize their operations, necessitating the establishment of a robust Security Operations Center (SOC). By focusing on core components such as skilled personnel, standardized processes, and advanced technologies, organizations can significantly enhance their cybersecurity posture.
To address these challenges, manufacturers must adopt best practices for building and maintaining a resilient SOC tailored to their unique demands. This article outlines best practices for establishing and sustaining a resilient SOC that meets the specific needs of the manufacturing sector.
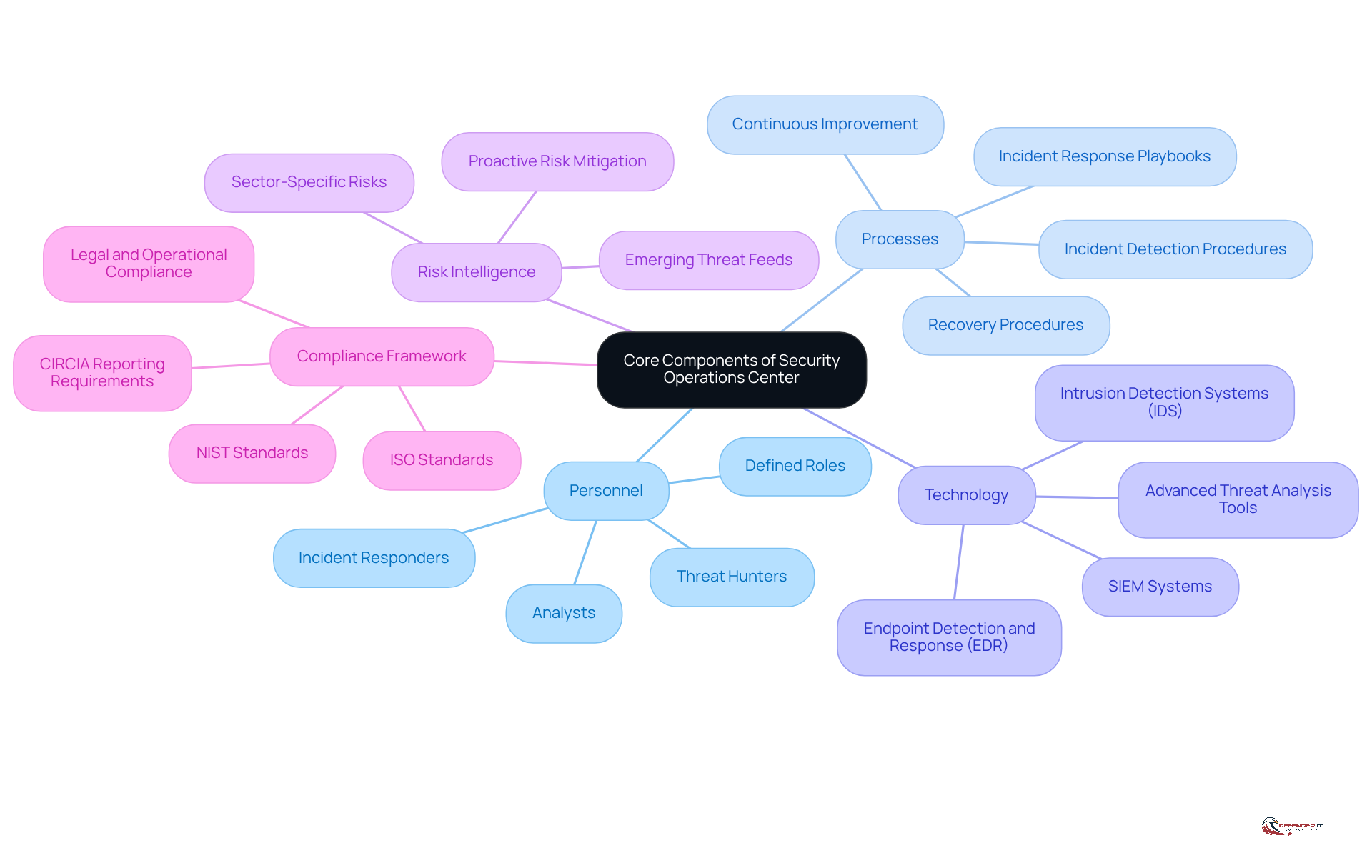
Establish Core Components of Your Security Operations Center
To effectively safeguard manufacturing environments, establishing a robust security operation centre is essential. Organizations should focus on the following core components:
- Personnel: Assemble a skilled team that includes analysts, incident responders, and danger hunters. Each role must be clearly defined to ensure accountability and efficiency. Effective cybersecurity hinges on skilled personnel, well-defined processes, and the right mindset, with technology enhancing these foundations. The effectiveness of a security operation centre is significantly influenced by its personnel, as strong cybersecurity begins with people and disciplined processes.
- Processes: Develop standardized procedures for incident detection, response, and recovery. This includes creating playbooks that outline steps for various types of incidents, reinforcing the idea that effective cybersecurity is a continuous process rather than a one-time solution. With 85% of businesses and 86% of charities reporting phishing as their primary breach, the absence of robust processes can lead to significant vulnerabilities.
- Technology: Invest in essential tools such as Security Information and Event Management (SIEM) systems, intrusion detection systems (IDS), and endpoint detection and response (EDR) solutions. These tools play a crucial role in keeping an eye on security incidents and analyzing potential threats, enabling a proactive stance against emerging dangers. The increase in malware and a sharp 124% rise in IoT attacks reported by SonicWall in 2025 further underscores the need for advanced technological defenses.
- Risk Intelligence: Incorporate risk intelligence feeds to remain aware of emerging dangers specific to the manufacturing sector. This proactive approach helps in anticipating and mitigating risks before they escalate, aligning with the understanding that cybersecurity is about foresight and resilience.
- Compliance Framework: Establish a compliance framework that aligns with industry regulations, such as NIST or ISO standards, to ensure that the SOC meets legal and operational requirements. Notably, CIRCIA requires U.S. critical infrastructure operations to report qualifying cyber incidents within 72 hours. Failure to comply with these regulations can jeopardize not only operational integrity but also the organization’s reputation in the industry.
By concentrating on these elements, manufacturing firms can establish a security operation centre that is efficient in identifying and addressing risks while also being robust against upcoming challenges. Ongoing alertness and collective responsibility are crucial to remain proactive against cyber risks, as neglecting cybersecurity can lead to costs that far exceed the necessary investments in protective measures.
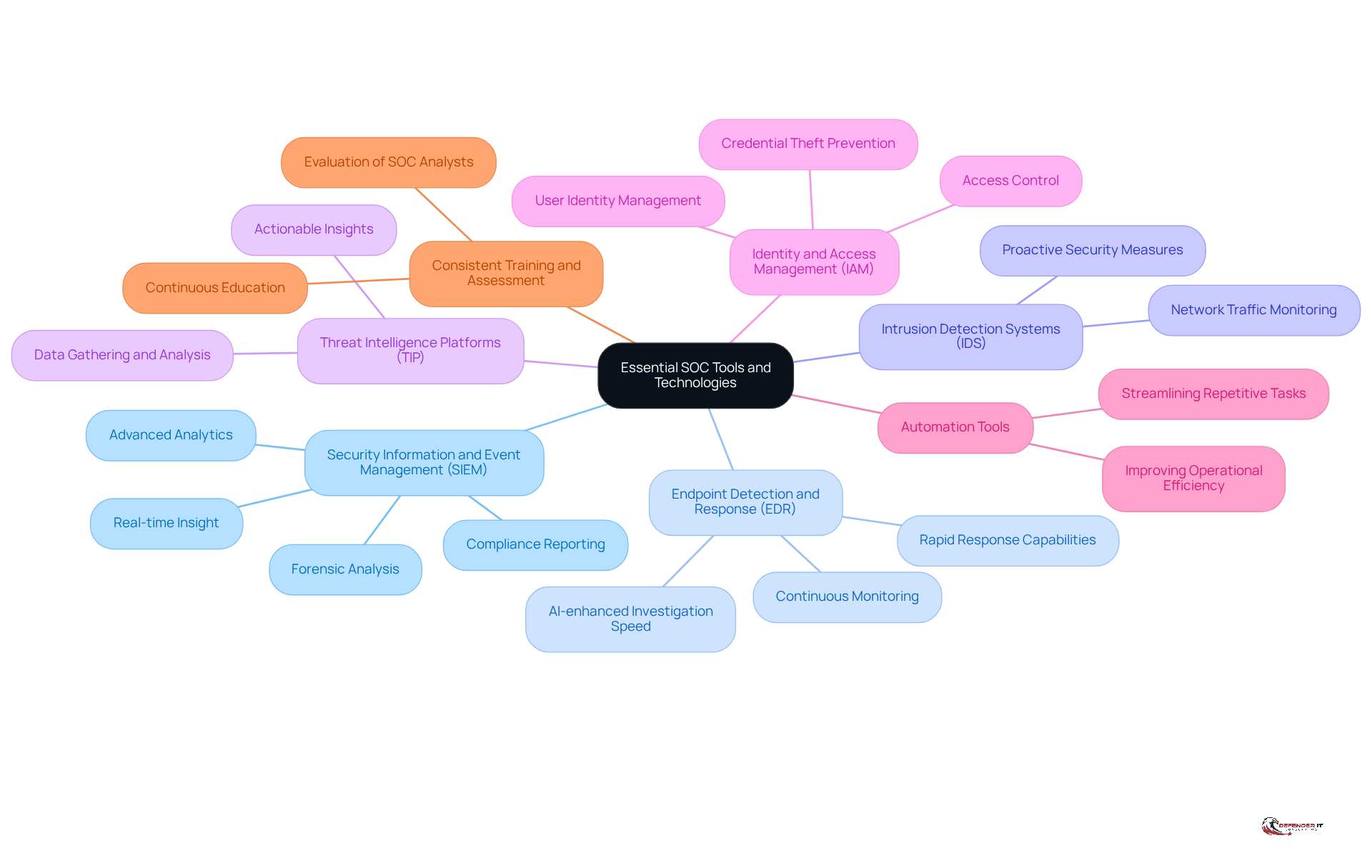
Implement Essential SOC Tools and Technologies
To enhance the effectiveness of your Security Operations Center (SOC), it is crucial to implement essential tools and technologies that address current cybersecurity challenges:
- Security Information and Event Management (SIEM): A SIEM system consolidates and examines security data from throughout the organization, offering real-time insight into possible risks. Look for solutions that provide advanced analytics and machine learning capabilities to improve detection rates. SIEM solutions are essential for enabling compliance reporting and assisting forensic analysis, allowing SOC teams to concentrate on significant threats.
- Endpoint Detection and Response (EDR): EDR solutions continuously monitor endpoint devices for suspicious activity and offer rapid response capabilities. In manufacturing, endpoints often include industrial control systems (ICS). Therefore, the effectiveness of EDR solutions is crucial. Organizations often experience a 5x to 10x improvement in investigation speed with AI-enhanced EDR solutions, significantly reducing the mean time to investigate (MTTI) and mean time to resolve (MTTR).
- Intrusion Detection Systems (IDS): Deploy IDS to monitor network traffic for signs of malicious activity. This tool plays a vital role in spotting potential breaches before they lead to serious damage, ensuring proactive security measures are in place.
- Threat Intelligence Platforms (TIP): Utilize TIPs to gather and analyze data on emerging threats. These platforms provide actionable insights that help teams at the security operation centre prioritize their response efforts based on the most relevant risks, enhancing overall situational awareness.
- Identity and Access Management (IAM): Implement IAM solutions to manage user identities and control access to resources within your IT environment. Effective IAM implementation improves protection by ensuring that only authorized individuals can access sensitive information, thereby diminishing the risk of credential theft and unauthorized access.
- Automation Tools: Implement automation solutions to streamline repetitive tasks, such as alert triage and incident response. Automation can significantly reduce response times and free up analysts to focus on more complex issues, improving operational efficiency.
- Consistent Training and Assessment: Ensure that SOC analysts receive continuous education and evaluation to effectively utilize the resources and react to changing risks. This is crucial for maintaining a robust security posture.
Incorporating these resources not only strengthens your security operation centre but also prepares your organization to proactively combat evolving cyber threats.
Integrate SOC Tools for Enhanced Operational Efficiency
To enhance operational efficiency within your Security Operations Center (SOC), implementing strategic integration methods is essential:
- Centralized Dashboard: Create a centralized dashboard that consolidates data from all SOC resources. This method offers analysts a thorough perspective on incidents, enabling faster decision-making and response times. Centralized dashboards are crucial for improving situational awareness and streamlining incident management. Organizations that utilize centralized dashboards can significantly reduce incident response times by up to 30%.
- API Integrations: Utilize APIs to link various protective systems, enabling seamless data sharing and communication. Effective API integrations automate workflows. This significantly reduces the time spent on manual data entry and minimizes the risk of human error. Statistics indicate that organizations leveraging API integrations experience a 25% improvement in operational efficiency and faster incident response times. As Piyush Sharma, CEO of Tuskira, notes, “When CISOs want to tame tool sprawl, they should start by focusing on integration and consolidation, rather than adding more tools.”
- Unified Threat Management (UTM): Consider adopting UTM solutions that integrate multiple protection functions into a single platform. This integration simplifies management and enhances the overall effectiveness of your security operation centre, allowing for a more cohesive defense strategy against cyber threats. Incorporating vulnerability management resources into your security operation centre operations proactively tackles potential weaknesses, decreasing the chances of successful attacks.
- Regular Tool Audits: Conduct periodic audits of your SOC tools to ensure optimal functionality and effective integration. Frequent evaluations assist in recognizing deficiencies in coverage or performance problems, allowing prompt actions to improve protective stance. Ineffective integration can create barriers to data flow, heightening security vulnerabilities, making these audits essential.
- Cross-Training Staff: Ensure that SOC personnel receive training on all integrated resources. Cross-training promotes teamwork and guarantees that team members can efficiently use the complete variety of resources available to them, improving the SOC’s overall responsiveness to risks.
By embracing these integration strategies, organizations can significantly bolster their cybersecurity posture and resilience against emerging threats.
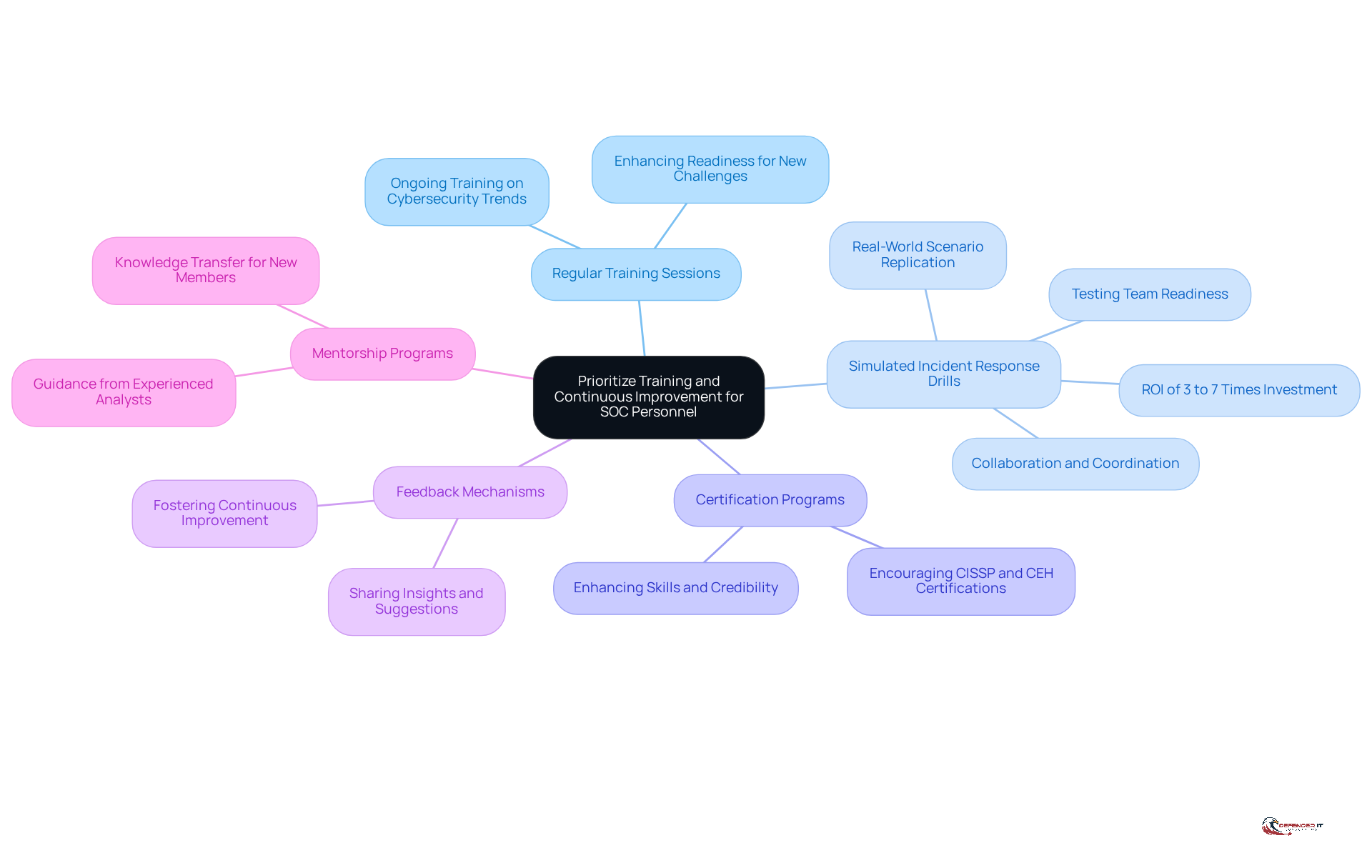
Prioritize Training and Continuous Improvement for SOC Personnel
To enhance the effectiveness of your Security Operations Center (SOC), it is crucial to prioritize targeted training and continuous improvement initiatives:
- Regular Training Sessions: Schedule ongoing training sessions that address the latest cybersecurity trends, tools, and techniques. This keeps SOC personnel informed and ready to address new challenges.
- Simulated Incident Response Drills: Conduct simulated incident response drills that replicate real-world scenarios relevant to the manufacturing sector. These exercises are essential for testing the team’s readiness and identifying areas for improvement. Research shows that organizations participating in regular simulations significantly enhance their incident response capabilities. Effective training programs can yield returns of 3 to 7 times the investment. Furthermore, simulations foster collaboration and coordination among team members, enabling them to work together seamlessly to address the simulated threat scenario.
- Certification Programs: Encourage SOC personnel to pursue relevant certifications, such as Certified Information Systems Security Professional (CISSP) or Certified Ethical Hacker (CEH). These credentials not only enhance their skills but also bolster the team’s credibility and effectiveness in managing cybersecurity incidents.
- Feedback Mechanisms: Implement feedback mechanisms that allow SOC personnel to share insights and suggestions for improving processes and tools. This fosters a culture of continuous improvement and innovation, which is vital for adapting to the fast-paced cybersecurity landscape.
- Mentorship Programs: Establish mentorship programs where experienced SOC analysts can guide and support newer team members. Transferring knowledge in this way is crucial for developing a strong, capable team, ensuring that all members are equipped to handle the complexities of cybersecurity in manufacturing.
Investing in these training and continuous improvement initiatives can significantly enhance the capabilities of personnel in the security operation centre, leading to a more effective and resilient security posture. In a landscape where phishing attacks have surged by 202%, the need for ongoing training and preparedness is more critical than ever.
Conclusion
In an era marked by escalating cyber threats, establishing a Security Operations Center (SOC) in manufacturing is essential for safeguarding operations. By focusing on:
- Skilled personnel
- Standardized processes
- Advanced technology
- Risk intelligence
- Compliance frameworks
organizations can establish a robust defense mechanism. These foundational elements enhance the SOC’s ability to detect and respond to incidents while fostering a culture of continuous improvement and vigilance.
Key insights from the article highlight the importance of integrating essential tools and technologies, such as:
- SIEM systems
- EDR solutions
- Threat intelligence platforms
to bolster operational efficiency. Furthermore, emphasizing training and continuous development for SOC personnel ensures that teams remain agile and well-equipped to tackle evolving threats. Regular simulations and feedback mechanisms play a vital role in refining processes and enhancing team collaboration, ultimately leading to a more resilient security posture.
The establishment of a well-structured SOC is crucial, particularly given the sophistication and prevalence of modern cyber threats. Organizations must prioritize the establishment and enhancement of their SOCs, not just to comply with regulations but to protect their operational integrity and reputation. Ultimately, the proactive establishment of a SOC is not merely a regulatory requirement; it is a strategic imperative for safeguarding the future of manufacturing operations.
Frequently Asked Questions
What is the purpose of establishing a Security Operations Center (SOC) in manufacturing environments?
The purpose of establishing a SOC in manufacturing environments is to effectively safeguard against cyber threats by implementing a robust framework that includes skilled personnel, standardized processes, advanced technology, risk intelligence, and compliance with industry regulations.
What personnel roles are essential for a Security Operations Center?
Essential personnel roles for a SOC include analysts, incident responders, and danger hunters. Each role should be clearly defined to ensure accountability and efficiency in cybersecurity efforts.
Why are standardized processes important in a Security Operations Center?
Standardized processes are important because they provide clear procedures for incident detection, response, and recovery, reinforcing the idea that cybersecurity is a continuous effort rather than a one-time solution.
What types of technology should organizations invest in for their Security Operations Center?
Organizations should invest in essential tools such as Security Information and Event Management (SIEM) systems, intrusion detection systems (IDS), and endpoint detection and response (EDR) solutions to monitor security incidents and analyze potential threats.
How does risk intelligence contribute to a Security Operations Center?
Risk intelligence contributes by providing feeds that keep organizations aware of emerging dangers specific to the manufacturing sector, allowing them to anticipate and mitigate risks before they escalate.
What is the significance of establishing a compliance framework for a Security Operations Center?
Establishing a compliance framework is significant as it ensures that the SOC aligns with industry regulations, such as NIST or ISO standards, and meets legal requirements, which is crucial for maintaining operational integrity and protecting the organization’s reputation.
What are the potential consequences of neglecting cybersecurity in manufacturing?
Neglecting cybersecurity can lead to significant costs that far exceed necessary investments in protective measures, jeopardizing operational integrity and the organization’s reputation in the industry.
List of Sources
- Establish Core Components of Your Security Operations Center
- 41 Cybersecurity Quotes to Protect Your Digital Life (https://acecloudhosting.com/blog/cybersecurity-quotes)
- The New Rules of Manufacturing Cybersecurity: What to Know in 2026 – Decypher Technologies (https://decyphertech.com/the-new-rules-of-manufacturing-cybersecurity-what-to-know-in-2026)
- Implement Essential SOC Tools and Technologies
- Cybersecurity 2026: AI, CISA, manufacturing sector all in the hot seat (https://cybersecuritydive.com/news/cyber-trends-outlook-2026/810708)
- 7 Essential Security Operations Center Tools for 2025 (https://swimlane.com/blog/security-operations-center-tools)
- Key SOC Tools Every Security Operations Center Needs | Prophet Security (https://prophetsecurity.ai/blog/key-soc-tools-every-security-operations-center-needs)
- Essential security operations center (SOC) tools and technologies | Red Canary (https://redcanary.com/cybersecurity-101/security-operations/soc-tools)
- 10 SIEM Benefits You Need to Know (https://sentinelone.com/cybersecurity-101/data-and-ai/siem-benefits)
- Integrate SOC Tools for Enhanced Operational Efficiency
- Essential security operations center (SOC) tools and technologies | Red Canary (https://redcanary.com/cybersecurity-101/security-operations/soc-tools)
- 20 Quotes Proving The Need for Security Integrations (https://synqly.com/moving-from-ok-to-best-in-class-20-quotes-from-experts-proving-the-need-for-security-integrations)
- Prioritize Training and Continuous Improvement for SOC Personnel
- Incident Response Simulations vs Exercise: Which Strengthens Your Defense? (https://sans.org/blog/enhancing-your-cyber-defense-comparing-simulations-and-tabletop-exercises)
- Cybersecurity training and events for 2026 | CMS Information Security and Privacy Program (https://security.cms.gov/posts/cybersecurity-training-and-events-2026)
- Security Awareness Training: USA 2025 Statistics | Infrascale (https://infrascale.com/security-awareness-training-statistics-usa)
- Security Awareness Training Statistics 2025 [100+ Studies] | Brightside AI Blog (https://brside.com/blog/security-awareness-training-statistics-2025-100-studies)