Introduction
As cyber threats grow increasingly sophisticated, organizations must prioritize robust cybersecurity measures. This article explores best practices for cybersecurity detection and response, providing a structured framework to enhance organizational resilience against breaches.
Organizations face increasing pressure to implement effective cybersecurity measures. Exploring the intricacies of comprehensive frameworks, vulnerability assessments, and incident response plans will reveal not only the strategies to implement but also the common pitfalls that could compromise security efforts.
Organizations must continuously evaluate their defenses to ensure effectiveness and adaptability in the face of evolving cyber risks. Understanding these frameworks is crucial, as neglecting them could expose organizations to devastating security breaches.
Establish a Comprehensive Cybersecurity Framework
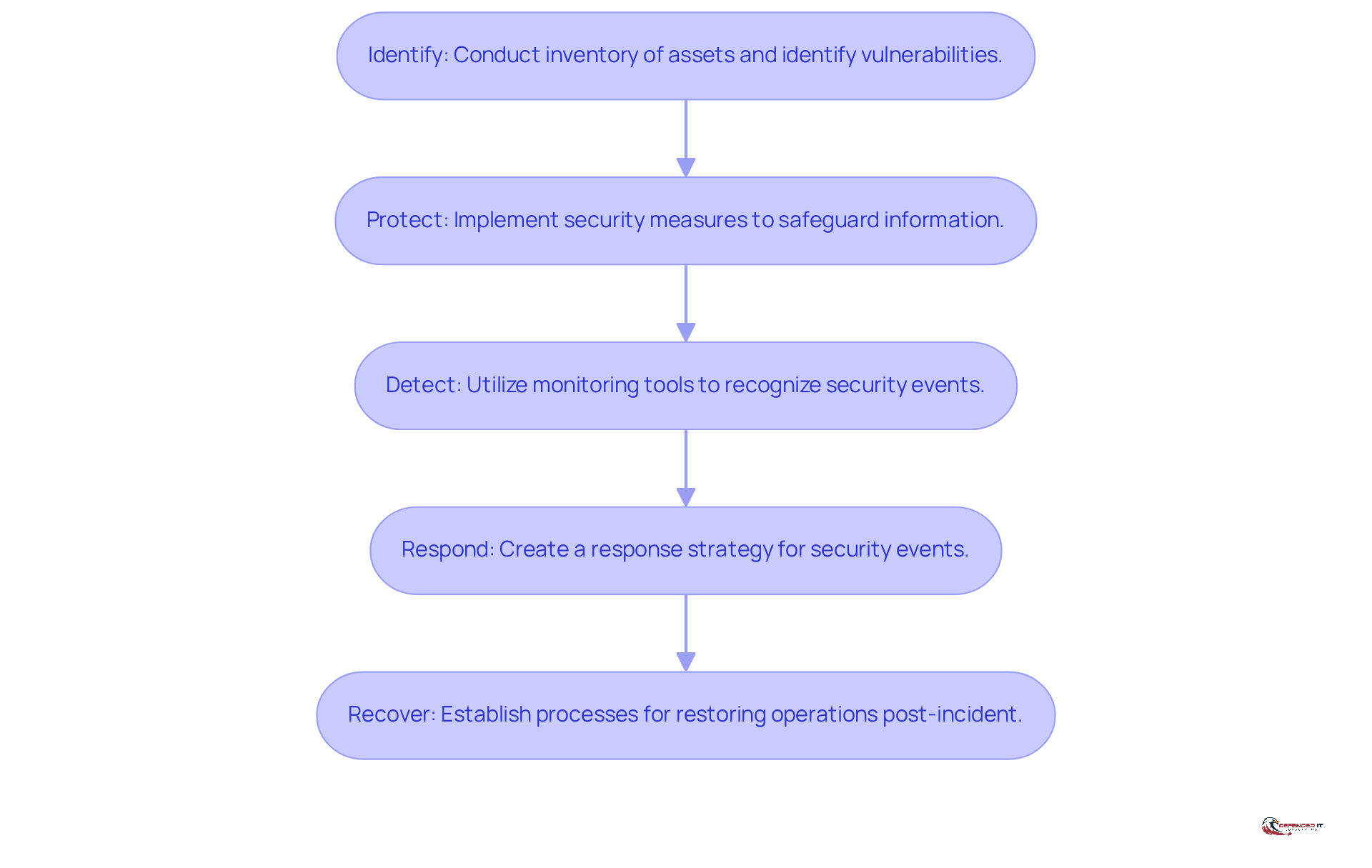
To effectively combat the growing threat of cyber risks, organizations must adopt a comprehensive security framework, such as the NIST Framework, which encompasses five essential functions: Identify, Protect, Detect, Respond, and Recover. This structured approach enables organizations to systematically manage cybersecurity risks through the following steps:
- Identify: Conduct a thorough inventory of all assets, including hardware, software, and data. Identifying vulnerabilities can be a complex task, often requiring specialized tools and expertise. This step is crucial as it lays the foundation for effective risk management.
- Protect: Implement robust security measures such as firewalls, encryption, and access controls to safeguard sensitive information from unauthorized access and breaches. As mentioned by industry leaders, investing in AI-driven security solutions can improve these protective measures, ensuring a proactive defense against new dangers. This ensures that sensitive data remains secure and minimizes the risk of breaches.
- Detect: Utilize advanced monitoring tools to recognize potential security events in real-time, enabling swift action to mitigate threats before they escalate. Given how quickly cyber threats evolve, organizations need to continuously monitor and adapt to new attack vectors. This proactive approach is essential for maintaining a strong security posture.
- Respond: Create a thorough response strategy that details procedures for handling security events, including clear communication protocols and specified roles for team members. This ensures that all team members are prepared to act swiftly and effectively in the face of a security incident.
- Recover: Establish processes for restoring operations and services after a security incident, ensuring minimal disruption to business activities and a swift return to normalcy. This phase is vital for maintaining business continuity and resilience in the face of cyber threats.
By following this framework, entities can greatly improve their resilience against cyber risks while ensuring compliance with industry regulations. It is essential to recognize common pitfalls in implementing the NIST Cybersecurity Framework, such as inadequate asset identification or failure to update response plans, which can undermine the effectiveness of the framework. Ultimately, neglecting to address these common pitfalls can leave organizations vulnerable to cyber threats, jeopardizing their operational integrity and reputation.
Conduct Regular Vulnerability Assessments
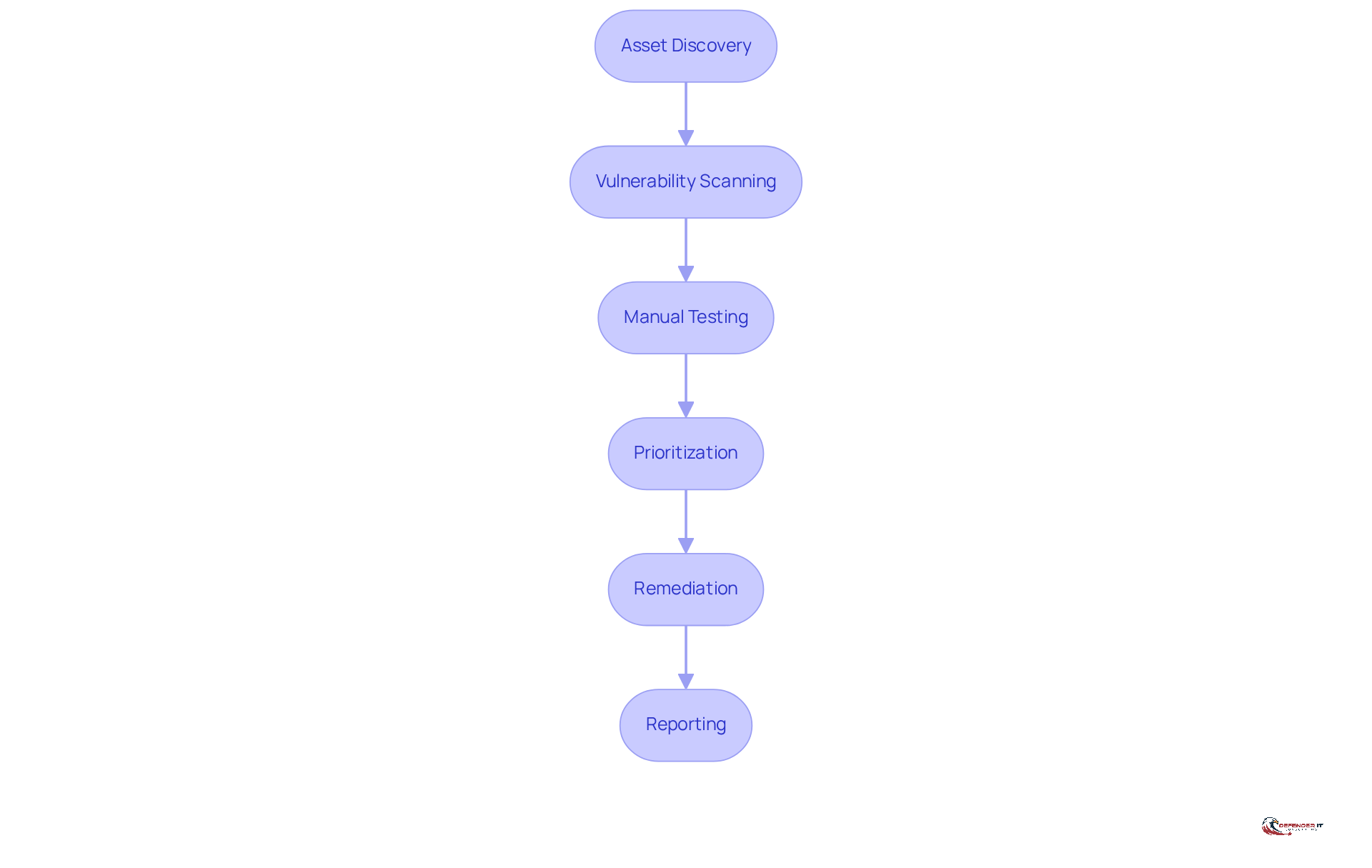
Neglecting routine vulnerability assessments can leave organizations vulnerable to significant cyber threats. Organizations should implement a routine schedule for vulnerability assessments, ideally on a quarterly basis or after significant changes to the IT environment. To effectively assess vulnerabilities, organizations must focus on the following key processes:
- Asset Discovery: Identify all devices and applications within the network to ensure comprehensive coverage.
- Vulnerability Scanning: Use automated tools to scan for known vulnerabilities in systems and applications. Tools like Nessus or Qualys can be effective in this regard.
- Manual Testing: Complement automated scans with manual testing techniques, such as penetration testing, to uncover vulnerabilities that automated tools may miss.
- Prioritization: Classify vulnerabilities according to their severity and potential impact on the entity, focusing remediation efforts on the most critical issues first.
- Remediation: Develop a plan to address identified vulnerabilities, including patch management and configuration changes.
- Reporting: Document findings and remediation efforts to maintain a record of the entity’s security posture and compliance with regulatory requirements.
Ultimately, a proactive approach to vulnerability assessments is essential for safeguarding organizational assets against evolving cyber risks.
Develop an Incident Response Plan
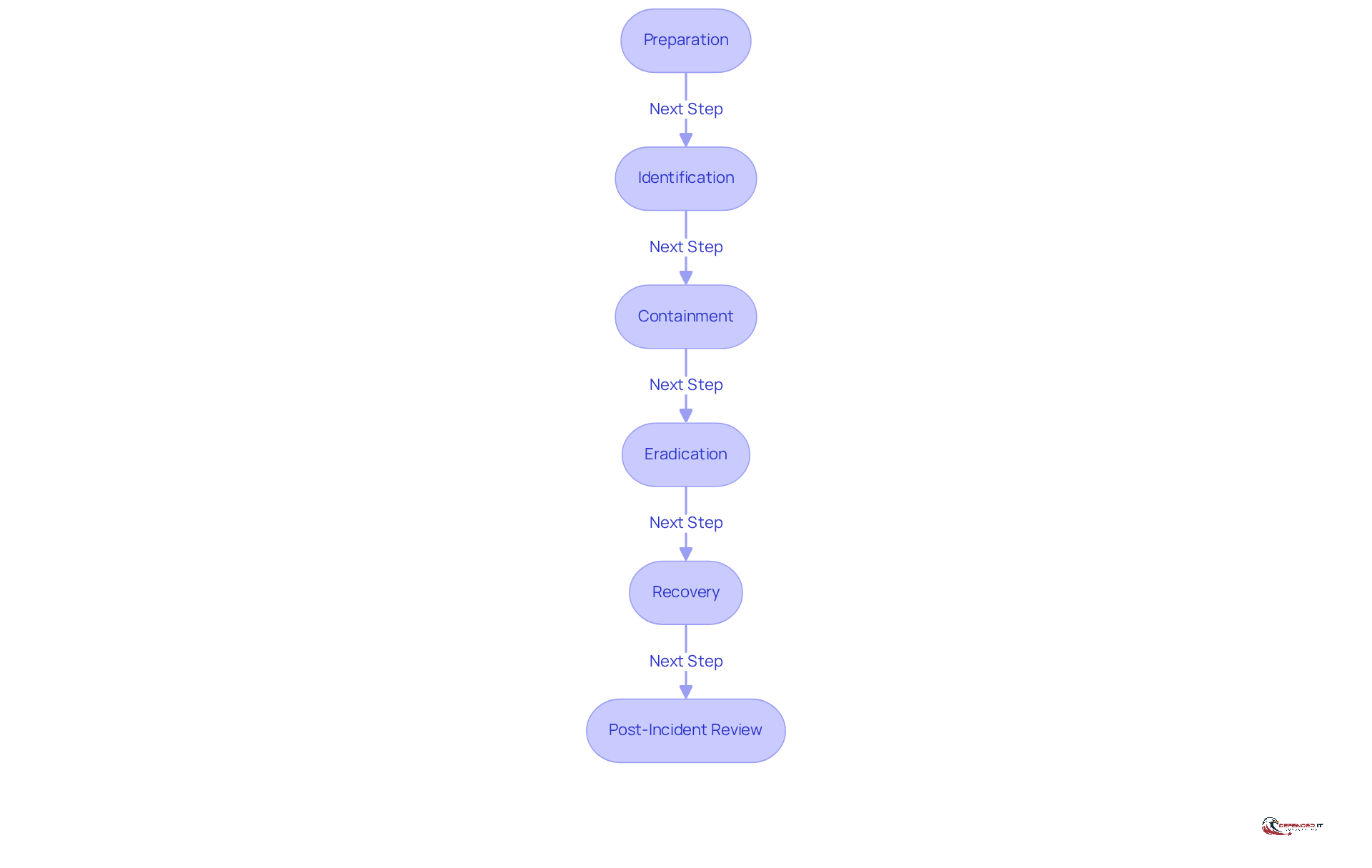
In an era where cyber threats are increasingly sophisticated, having a robust plan for detection and response is not just beneficial; it is essential for safeguarding an organization’s assets and reputation. A well-structured incident response plan should encompass the following key components:
- Preparation: Assemble a response team with defined roles and responsibilities. Ensure team members are trained and equipped with the necessary tools and resources.
- Identification: Establish procedures for detecting and confirming occurrences. Utilize monitoring tools to identify anomalies and possible risks.
- Containment: Develop strategies for managing occurrences to prevent further damage. This may involve isolating affected systems or disabling compromised accounts.
- Eradication: Identify the root cause of the occurrence and eliminate the threat from the environment. This may include removing malware or closing vulnerabilities.
- Recovery: Restore affected systems and services to normal operation. Ensure that systems are patched and secured before bringing them back online.
- Post-Incident Review: Conduct a thorough analysis of the event to identify lessons learned and areas for improvement. Revise the response plan accordingly.
Without a proactive strategy for detection and response, organizations risk facing severe operational disruptions and reputational damage that could take years to recover from.
Implement Continuous Training and Awareness Programs
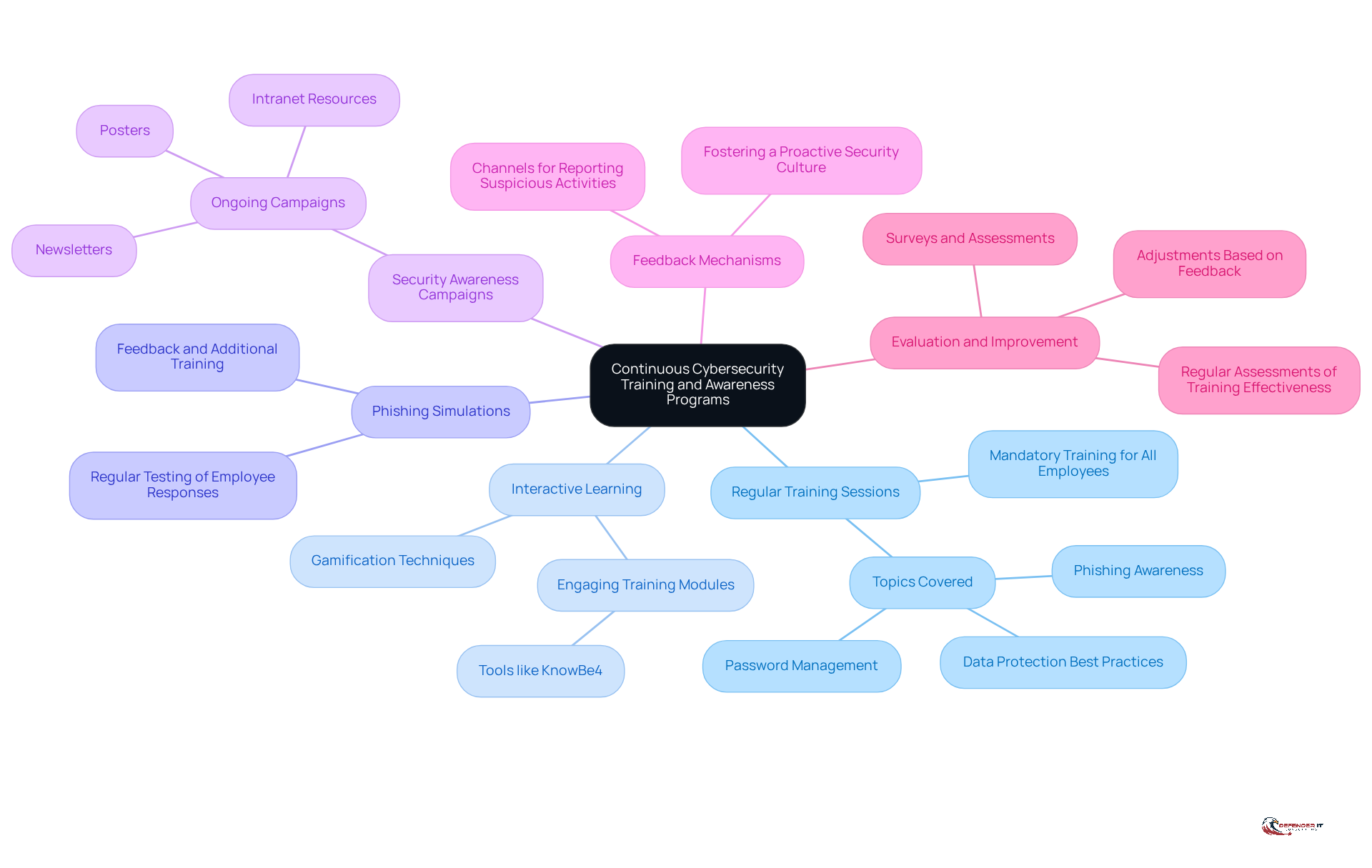
In an era where cyber threats are increasingly sophisticated, organizations must prioritize cybersecurity awareness among their employees. To cultivate a culture of cybersecurity awareness, organizations should implement continuous training and awareness programs that include:
- Regular Training Sessions: Conduct mandatory training sessions for all employees, covering topics such as phishing awareness, password management, and data protection best practices.
- Interactive Learning: Utilize gamification and interactive modules to engage employees and enhance knowledge retention. Tools like KnowBe4 can be effective in delivering engaging training content.
- Phishing Simulations: Regularly conduct phishing simulations to test employees’ ability to recognize and respond to phishing attempts. Provide feedback and additional training based on results.
- Security Awareness Campaigns: Launch ongoing campaigns to promote awareness of security threats, using newsletters, posters, and intranet resources to keep security top of mind.
- Feedback Mechanisms: Establish channels for employees to report suspicious activities or incidents, fostering a proactive security culture.
- Evaluation and Improvement: Regularly assess the effectiveness of training programs through surveys and assessments, making adjustments as necessary to improve engagement and knowledge retention.
Without proper training, employees may fall victim to phishing attacks, jeopardizing organizational security. This proactive approach not only mitigates risks but also fosters a culture of security awareness throughout the organization. Ultimately, a well-informed workforce is the first line of defense against cyber threats, making continuous training essential for organizational resilience.
Conclusion
In an era where cyber threats are increasingly sophisticated, organizations must adopt a comprehensive approach to cybersecurity detection and response. By implementing a structured framework, such as the NIST Framework, organizations can systematically identify, protect, detect, respond to, and recover from cyber threats. This proactive stance not only enhances security posture but also ensures compliance with industry regulations.
This article emphasizes the critical need for:
- Regular vulnerability assessments
- Robust incident response plans
- Continuous employee training
Organizations must prioritize asset identification and risk management while developing a well-defined incident response strategy that includes:
- Preparation
- Identification
- Containment
- Eradication
- Recovery
- Post-incident review
Furthermore, fostering a culture of cybersecurity awareness through ongoing training and engagement is critical, as employees serve as the first line of defense against potential threats.
As cyber threats evolve, organizations must remain vigilant and proactive. They are urged to take action by establishing comprehensive frameworks, conducting regular assessments, and investing in employee training. By prioritizing these strategies, organizations not only safeguard their assets but also play a crucial role in enhancing the overall security of the digital landscape. Embracing these best practices will empower organizations to navigate the complexities of cybersecurity with confidence and resilience.
Frequently Asked Questions
What is a comprehensive cybersecurity framework?
A comprehensive cybersecurity framework is a structured approach to managing cybersecurity risks, such as the NIST Framework, which includes five essential functions: Identify, Protect, Detect, Respond, and Recover.
What does the ‘Identify’ function entail?
The ‘Identify’ function involves conducting a thorough inventory of all assets, including hardware, software, and data, to identify vulnerabilities, which is crucial for effective risk management.
How can organizations protect sensitive information?
Organizations can protect sensitive information by implementing robust security measures such as firewalls, encryption, and access controls. Investing in AI-driven security solutions can enhance these protective measures.
What is the purpose of the ‘Detect’ function in cybersecurity?
The ‘Detect’ function utilizes advanced monitoring tools to recognize potential security events in real-time, allowing organizations to take swift action to mitigate threats before they escalate.
What should a response strategy include?
A response strategy should include detailed procedures for handling security events, clear communication protocols, and specified roles for team members to ensure effective action during a security incident.
What processes are involved in the ‘Recover’ function?
The ‘Recover’ function involves establishing processes for restoring operations and services after a security incident to ensure minimal disruption to business activities and a swift return to normalcy.
Why is it important to follow the NIST Cybersecurity Framework?
Following the NIST Cybersecurity Framework helps organizations improve their resilience against cyber risks and ensures compliance with industry regulations.
What are common pitfalls in implementing the NIST Cybersecurity Framework?
Common pitfalls include inadequate asset identification and failure to update response plans, which can undermine the effectiveness of the framework and leave organizations vulnerable to cyber threats.
List of Sources
- Establish a Comprehensive Cybersecurity Framework
- NIST CSF’s popularity – all about GRC (https://allaboutgrc.com/nist-csfs-popularity)
- White House unveils 2026 cyber strategy (https://fmglaw.com/cyber-privacy-security/white-house-unveils-2026-cyber-strategy)
- 8 Great Cyber Security Quotes From Influencers | Proofpoint US (https://proofpoint.com/us/blog/identity-threat-defense/8-great-cyber-security-quotes-influencers)
- isaca.org (https://isaca.org/resources/news-and-trends/industry-news/2026/the-6-cybersecurity-trends-that-will-shape-2026)
- White House Announces The 2026 Cyber Strategy For America (https://forrester.com/blogs/white-house-announces-the-2026-cyber-strategy-for-america)
- Conduct Regular Vulnerability Assessments
- What the 2026 Vulnerability Statistics Report Tells Us About the State of Security (https://edgescan.com/what-the-2026-vulnerability-statistics-report-tells-us-about-the-state-of-security)
- Why and How to Perform Cybersecurity Risk Assessments in 2026 (https://maddevs.io/blog/how-to-perform-cybersecurity-risk-assessments)
- Threat and Vulnerability Management in 2026 (https://recordedfuture.com/blog/threat-and-vulnerability-management)
- Ultimate Guide to Vulnerability Assessment: What, Why & How (2026 Edition) (https://acronis.com/en/blog/posts/ultimate-guide-to-vulnerability-assessment-2026)
- Vulnerability Statistics 2026: Key Trends & Data | Indusface (https://indusface.com/blog/key-vulnerability-statistics)
- Develop an Incident Response Plan
- Cyberattacks target US infrastructure, and other cybersecurity news (https://weforum.org/stories/2026/04/cyberattacks-target-us-infrastructure-cybersecurity-news)
- 45 Cybersecurity Statistics and Facts [2025] (https://onlinedegrees.sandiego.edu/cyber-security-statistics)
- February 2026: Recent Cyber Attacks, Data Breaches, Ransomware Attacks (https://cm-alliance.com/cybersecurity-blog/february-2026-recent-cyber-attacks-data-breaches-ransomware-attacks)
- 73% of CISOs Unprepared for the Next Big Cyber Attack, Incident Response Readiness Report Reveals (https://finance.yahoo.com/sectors/technology/articles/73-cisos-unprepared-next-big-120000695.html)
- The Disaster Recovery Gap: 110+ Statistics Revealing Why 80% of Orgs Aren’t Prepared & What It’s Costing Them (https://secureframe.com/blog/disaster-recovery-statistics)
- Implement Continuous Training and Awareness Programs
- Pentagon eyes 3-year cyber training requirement, overriding new Army policy (https://defensescoop.com/2026/05/06/pentagon-changing-cybersecurity-training-requirement)
- Why Annual Security Training Isn’t Enough in 2026 | NINJIO (https://ninjio.com/blog/why-cisos-are-moving-beyond-annual-security-awareness-training)
- Cybersecurity Awareness Training for Employees in 2026 (https://uscsinstitute.org/cybersecurity-insights/resources/cybersecurity-awareness-training-for-employees-in-2026)
- US Coast Guard mandates cybersecurity training for personnel with IT, OT access by January 2026 – Industrial Cyber (https://industrialcyber.co/training-development/ics-cyber-security-training/us-coast-guard-mandates-cybersecurity-training-for-personnel-with-it-ot-access-by-january-2026)