Introduction
In an era where cyber threats are increasingly sophisticated, organizations face significant challenges in identifying vulnerabilities within their systems. Security penetration testing, or pen testing, is a vital tool that enables organizations to uncover weaknesses before malicious actors can exploit them. Many organizations struggle to effectively conduct penetration tests, leading to unaddressed vulnerabilities. This oversight can leave organizations exposed to significant cyber threats. To safeguard their assets, businesses must not only identify vulnerabilities but also implement comprehensive strategies that fortify their cybersecurity defenses.
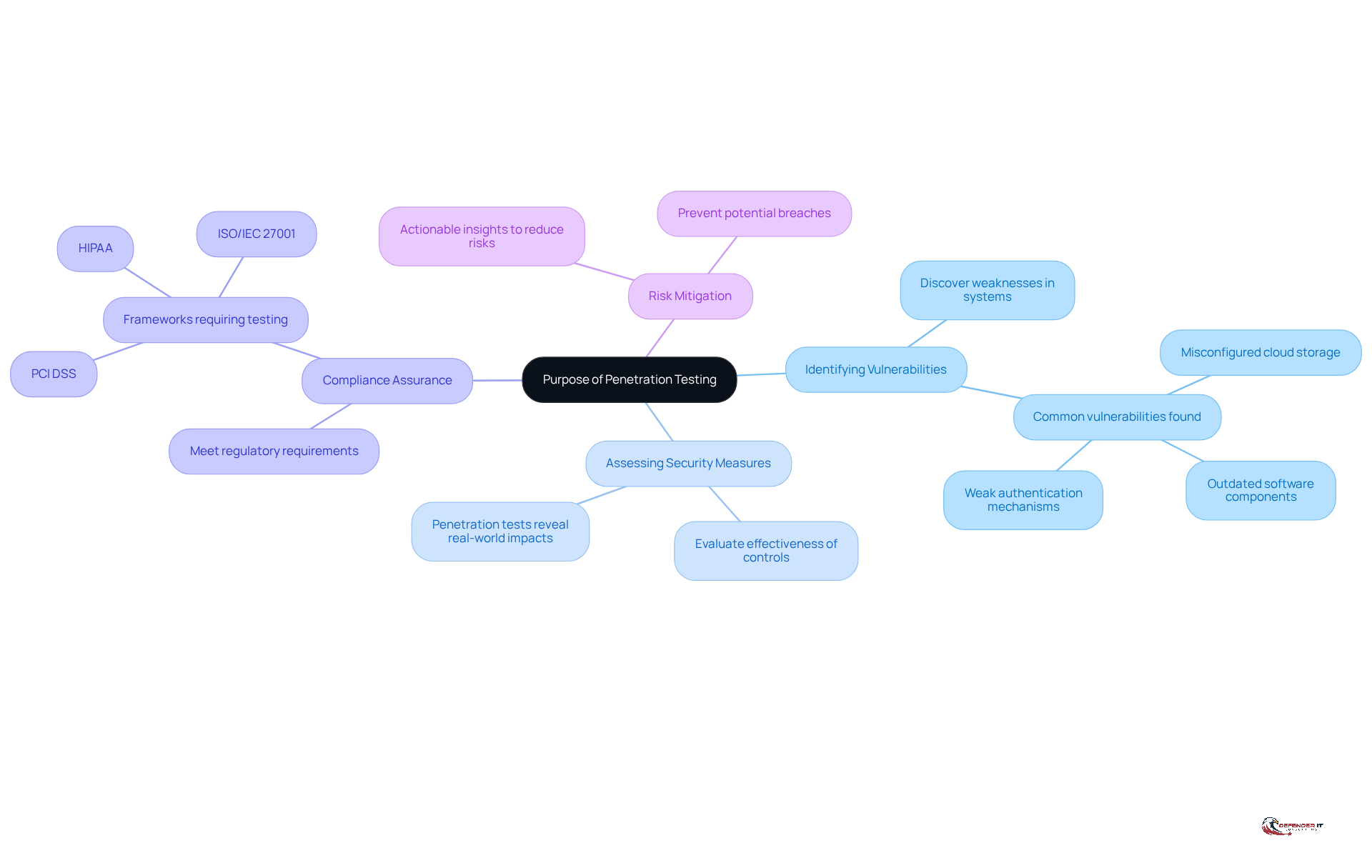
Understand the Purpose of Penetration Testing
Many organizations remain unaware of critical vulnerabilities that could be exploited by cyber attackers. A security penetration test, commonly known as ‘pen testing,’ simulates a cyber attack on your computer system to identify exploitable vulnerabilities. The primary goals of penetration testing include:
- Identifying Vulnerabilities: Discovering weaknesses in systems, networks, and applications that could be exploited by attackers.
- Assessing Security Measures: Evaluating the effectiveness of existing security controls and protocols.
- Compliance Assurance: Ensuring that the organization meets regulatory requirements and industry standards.
- Risk Mitigation: Providing actionable insights to reduce the risk of data breaches and cyber attacks.
By understanding these objectives, organizations can better recognize the importance of performing regular security penetration tests as part of their overall cybersecurity strategy. Regular security penetration tests are essential for safeguarding against the ever-evolving landscape of cyber threats.
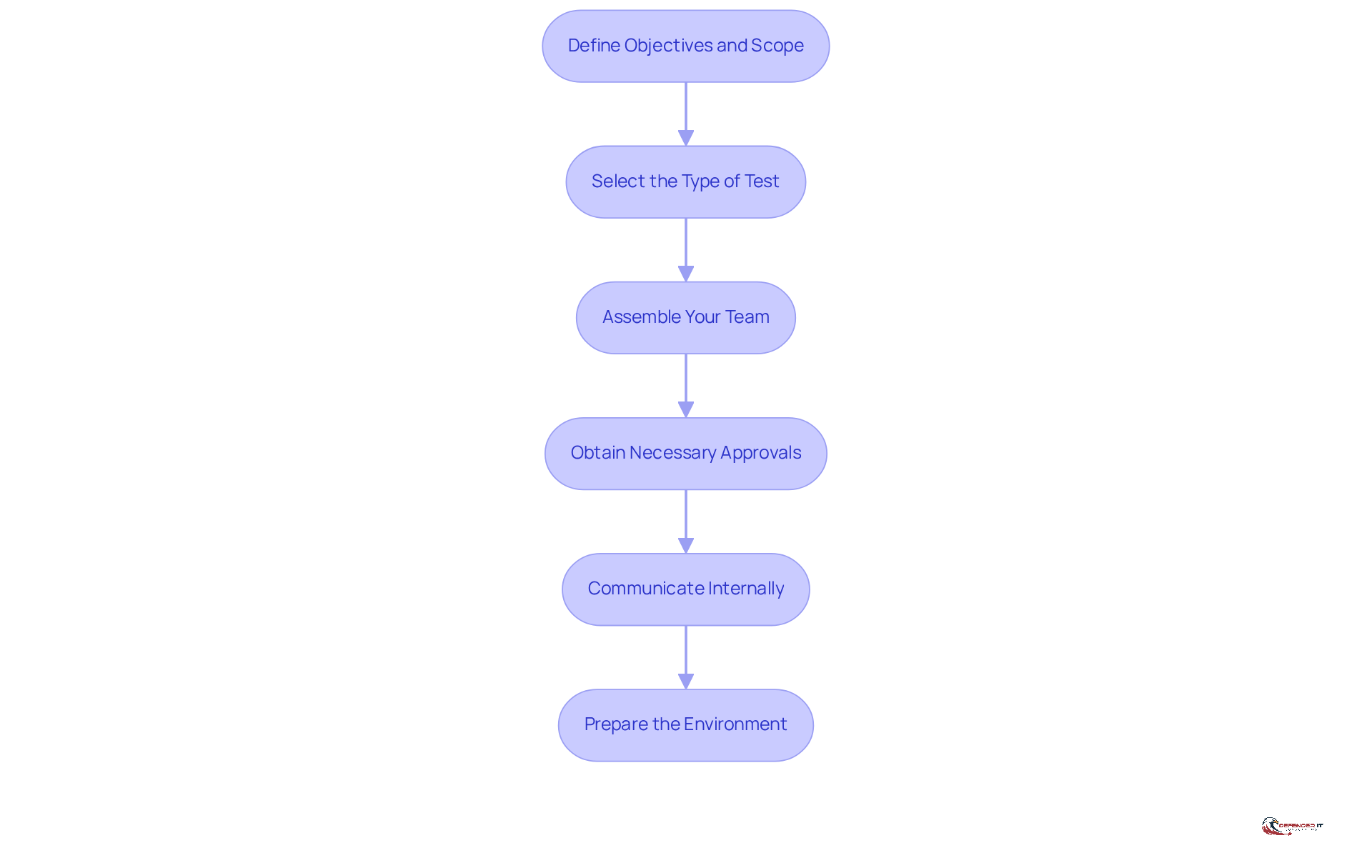
Prepare for the Penetration Test
Effective preparation for a security penetration test is essential to ensure compliance with regulatory standards and achieve meaningful results. The following steps outline the critical components of this process:
- Define Objectives and Scope: Clearly outline the goals of the penetration evaluation, specifying which systems, applications, or networks will be assessed. Without clear objectives, organizations risk misaligned expectations and ineffective security penetration tests. As noted by cybersecurity expert Cindy Kaplan, “Defining clear objectives is crucial for aligning the testing process with organizational goals and compliance requirements.”
- Select the Type of Test: Choose between black-box, white-box, or gray-box testing based on your objectives and the level of information you wish to provide to the testers. Each type serves different purposes and can yield varying insights into security vulnerabilities.
- Assemble Your Team: Gather a team of qualified professionals, either in-house or external, who possess the necessary skills and experience in penetration testing. Bringing in specialists ensures that the security penetration test runs smoothly and delivers actionable results.
- Obtain Necessary Approvals: Ensure that all stakeholders are informed and that you have the required permissions to carry out the assessment, especially if it involves sensitive data or critical systems. This step is vital for upholding adherence to regulations like GDPR and PCI DSS, which stress the significance of recorded protective measures.
- Communicate Internally: Notify pertinent departments (e.g., IT, safety, legal) about the forthcoming evaluation to prevent confusion and guarantee collaboration. Effective communication fosters a collaborative environment that can enhance the testing process.
- Prepare the Environment: Set up a controlled environment for testing, which may include staging servers or isolated networks to minimize risks to production systems. This preparation helps in accurately assessing vulnerabilities without impacting operational continuity.
By following these steps, organizations can significantly enhance their security posture and ensure compliance with industry regulations.
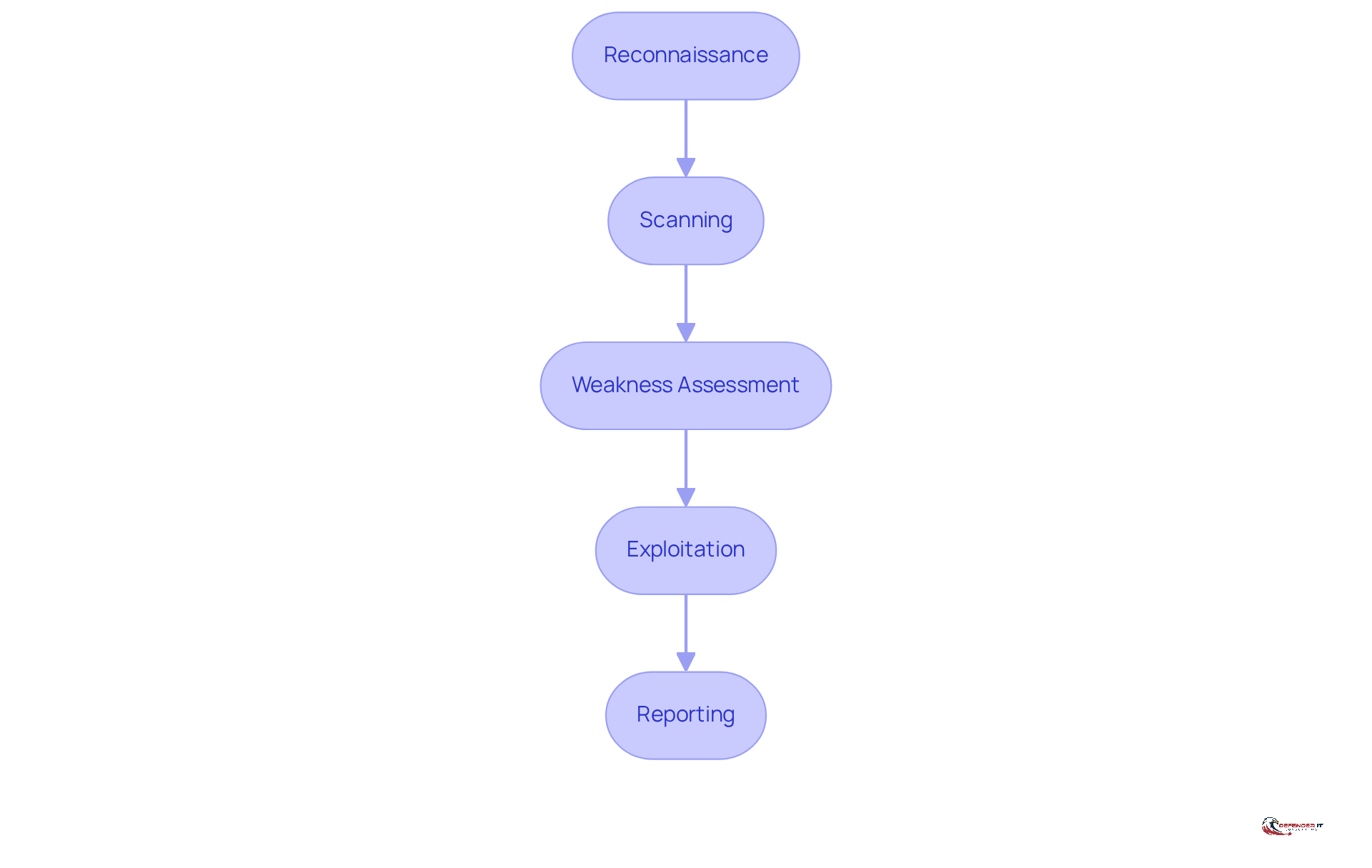
Execute the Penetration Test Phases
A systematic approach to penetration testing is essential for effectively identifying and addressing security vulnerabilities. The execution of a penetration test typically involves several distinct phases that are crucial for identifying and mitigating security vulnerabilities:
- Reconnaissance: This initial stage concentrates on collecting comprehensive details regarding the target system, including IP addresses, domain names, and network architecture. Tools like Nmap and WHOIS are essential in this stage, enabling testers to conduct both active and passive reconnaissance. Active reconnaissance involves direct interaction with the target, while passive reconnaissance utilizes publicly available information to minimize detection risk.
- Scanning: Following reconnaissance, the scanning stage aims to identify open ports and services running on the target system. Commonly, testers rely on tools such as Nessus and OpenVAS to effectively map the attack surface. This stage is essential as it uncovers possible access points for intruders, allowing a clearer insight into the system’s weaknesses.
- Weakness Assessment: This phase involves analyzing the information collected during reconnaissance and scanning to pinpoint potential weaknesses. This may involve automated tools or manual testing methods to assess the severity of the flaws, often using the Common Vulnerability Scoring System (CVSS) for evaluation. Furthermore, materials from the National Vulnerability Database (NVD) can be employed to further evaluate the seriousness of identified issues. Identifying weaknesses can be challenging due to the varying severity of flaws and the need for thorough analysis.
- Exploitation: The exploitation stage evaluates the effectiveness of security measures by trying to take advantage of recognized weaknesses. Ethical hackers use tools like Metasploit to simulate real-world attacks, gaining unauthorized access or escalating privileges. This careful approach ensures that the testing process remains ethical and focused on improving security measures. Failure to execute this stage carefully may lead to unintended consequences, including system compromise.
- Reporting: The final stage involves [documenting the findings, including discovered vulnerabilities](https://thehackernews.com/search/label/Penetration Testing), methods used, and recommendations for remediation. A well-organized report is crucial for conveying results to stakeholders, offering actionable insights that can improve the organization’s defense stance. Ultimately, the insights gained from these evaluations are vital for strengthening an organization’s cybersecurity posture against evolving threats.
By following these stages, organizations can carry out comprehensive and efficient penetration evaluations, providing valuable insights into their security weaknesses and overall resilience against cyber threats.
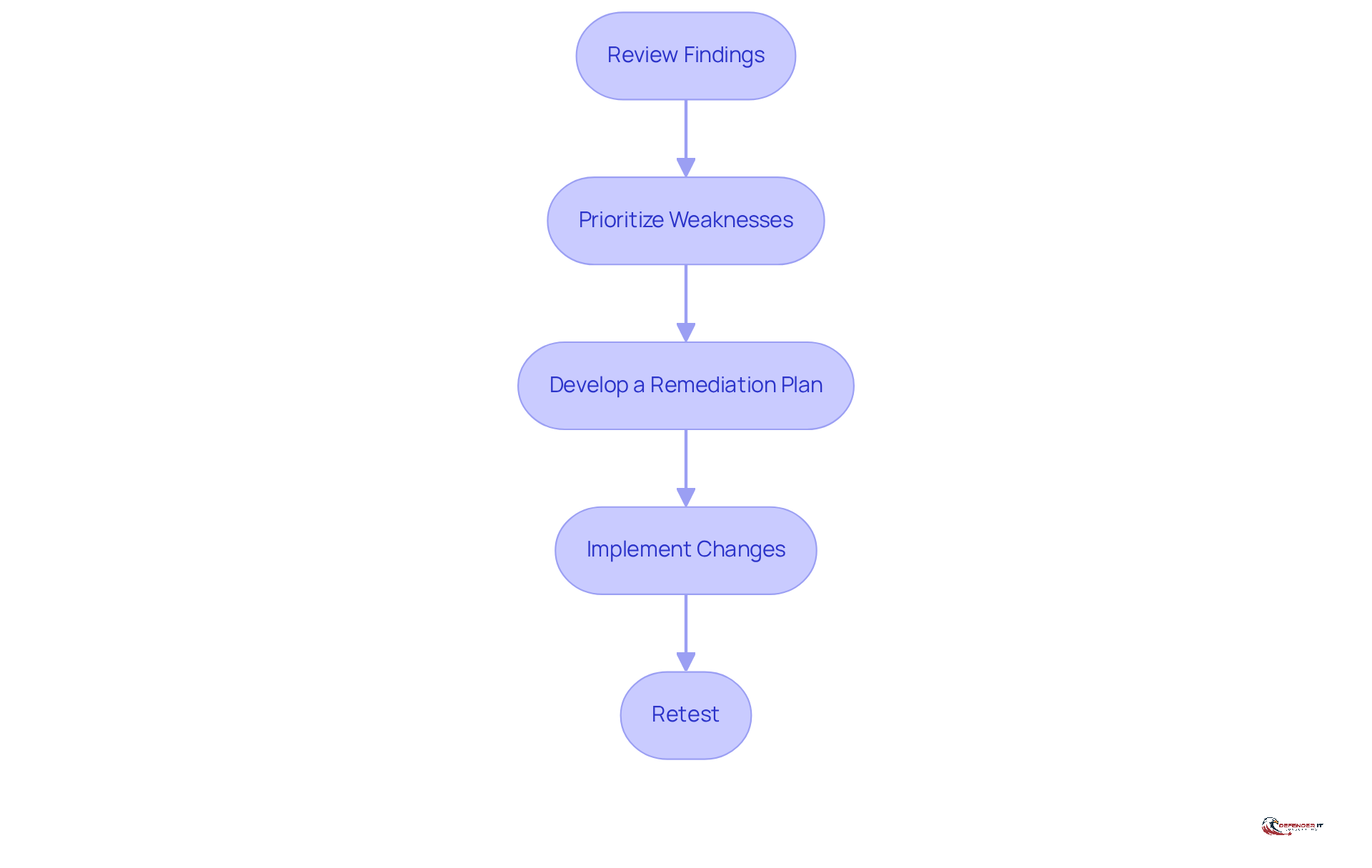
Analyze Results and Implement Remediation
Identifying vulnerabilities is only the first step; the real challenge lies in effectively addressing them to safeguard organizational assets. After completing the penetration test, it is essential to analyze the results and implement remediation strategies:
- Review Findings: Carefully examine the security penetration test report, focusing on identified weaknesses, their severity, and potential impact on the organization.
- Prioritize Weaknesses: Not all weaknesses are created equal. Use a risk-based method to prioritize which weaknesses to address first, considering factors such as exploitability and potential damage.
- Develop a Remediation Plan: Create a structured strategy to address identified weaknesses. This may involve patching software, updating configurations, and improving protective measures.
- Implement Changes: Execute the remediation plan, ensuring that all changes are documented and communicated to relevant stakeholders.
- Retest: After remediation, conduct a follow-up test to confirm that weaknesses have been effectively addressed and that no new issues have been introduced.
Organizations often struggle to effectively address identified vulnerabilities due to resource constraints and competing priorities. Failure to act on these vulnerabilities can expose organizations to severe risks, including data breaches and financial loss. Ultimately, proactive remediation not only fortifies security but also enhances organizational resilience against future threats.
Conclusion
Organizations face increasing challenges in safeguarding their digital assets against sophisticated cyber threats. Mastering security penetration testing is essential for identifying vulnerabilities, assessing security measures, and implementing necessary remediation strategies. Taking this proactive approach not only helps meet regulatory standards but also strengthens the organization’s overall security framework.
Throughout the article, key aspects of penetration testing have been highlighted. Understanding the purpose of these tests, preparing adequately, executing the test phases, and analyzing results are all essential components. Each phase – from reconnaissance to reporting – plays a pivotal role in uncovering weaknesses and ensuring that organizations are not only aware of their vulnerabilities but also equipped to address them effectively.
In light of the ever-evolving landscape of cyber threats, it is imperative for organizations to prioritize regular penetration testing as part of their cybersecurity strategy. Embracing this proactive approach not only mitigates risks but also cultivates a culture of security awareness and resilience. Failing to conduct regular penetration tests can leave organizations vulnerable to significant security breaches. Organizations are encouraged to implement the insights gained from penetration testing to continuously improve their defenses and stay one step ahead of potential attackers.
Frequently Asked Questions
What is penetration testing?
Penetration testing, or ‘pen testing,’ is a simulated cyber attack on a computer system to identify vulnerabilities that could be exploited by cyber attackers.
What are the primary goals of penetration testing?
The primary goals of penetration testing include identifying vulnerabilities, assessing security measures, ensuring compliance with regulatory requirements, and providing insights for risk mitigation.
How does penetration testing help in identifying vulnerabilities?
Penetration testing helps discover weaknesses in systems, networks, and applications that could be exploited by attackers.
Why is assessing security measures important in penetration testing?
Assessing security measures is crucial to evaluate the effectiveness of existing security controls and protocols in protecting against cyber threats.
How does penetration testing ensure compliance?
Penetration testing helps organizations meet regulatory requirements and industry standards, ensuring that they are compliant with necessary cybersecurity protocols.
In what way does penetration testing contribute to risk mitigation?
Penetration testing provides actionable insights that organizations can use to reduce the risk of data breaches and cyber attacks.
Why should organizations perform regular penetration tests?
Regular penetration tests are essential for safeguarding against the evolving landscape of cyber threats, helping organizations stay aware of and address potential vulnerabilities.
List of Sources
- Understand the Purpose of Penetration Testing
- Penetration Testing Trends 2026: Insights & Predictions (https://getastra.com/blog/penetration-testing/trends)
- Why Penetration Testing is Important for Your Business in 2026 (https://brightdefense.com/resources/why-penetration-testing-is-important)
- 120+ Penetration Testing Statistics for 2026 (https://brightdefense.com/resources/penetration-testing-statistics)
- 83 Penetration Testing Statistics: Key Facts and Figures (https://getastra.com/blog/penetration-testing/statistics)
- 100+ essential penetration testing statistics [2023 edition] (https://pentest-tools.com/blog/penetration-testing-statistics)
- Prepare for the Penetration Test
- Penetration Testing Requirement: What U.S. Rules Mandate It in 2026? (https://halock.com/penetration-testing-requirement-what-u-s-rules-mandate-it-in-2026)
- 2026 GDPR Cybersecurity Requirements & Penetration Testing – Netragard (https://netragard.com/blog/gdpr-cybersecurity-requirements-and-penetration-testing)
- The Complete Guide to External Penetration Testing (2026) – Triaxiom Security (https://triaxiomsecurity.com/blog/the-complete-guide-to-external-penetration-testing-2026)
- The 2026 State of Pentesting: How Modern Teams Manage and Deliver Results (https://thehackernews.com/expert-insights/2026/01/the-2026-state-of-pentesting-how-modern.html)
- Penetration Testing Best Practices in 2026 | Iterasec (https://iterasec.com/blog/4-tips-to-maximize-application-pentest-value)
- Execute the Penetration Test Phases
- The 5 essential phases of penetration testing (https://beaglesecurity.com/blog/article/penetration-testing-phases.html)
- Learn About The Five Penetration Testing Phases | Pentesting | EC-Council (https://eccouncil.org/cybersecurity-exchange/penetration-testing/penetration-testing-phases)
- Pentesting Statistics 2026: Key Insights and Emerging Trends (https://zerothreat.ai/blog/emerging-penetration-testing-statistics)
- Penetration Testing — Latest News, Reports & Analysis | The Hacker News (https://thehackernews.com/search/label/Penetration Testing)
- 100+ essential penetration testing statistics [2023 edition] (https://pentest-tools.com/blog/penetration-testing-statistics)
- Analyze Results and Implement Remediation
- The Remediation Gap is now a Remediation crisis: why vendors are failing and what needs to change (https://vicarius.io/articles/the-remediation-gap-is-now-a-remediation-crisis-why-vendors-are-failing-and-what-needs-to-change)
- Latest Vulnerability news (https://bleepingcomputer.com/tag/vulnerability)
- 83 Penetration Testing Statistics: Key Facts and Figures (https://getastra.com/blog/penetration-testing/statistics)
- AI Security Findings Outpace Cybersecurity Remediation in 2025 | HackerOne (https://hackerone.com/blog/ai-security-cybersecurity-remediation-gap)
- Pentesting Statistics 2026: Key Insights and Emerging Trends (https://zerothreat.ai/blog/emerging-penetration-testing-statistics)