Introduction
In today’s landscape, where data breaches are increasingly prevalent, understanding the complexities of cybersecurity is crucial. The System Security Plan (SSP) serves as a vital document that delineates how organizations safeguard sensitive information while ensuring adherence to regulatory standards. As cyber threats continue to evolve, organizations must consider how to effectively utilize an SSP to protect their assets and enhance their risk management strategies. By examining the components and significance of an SSP, we uncover a structured approach to addressing vulnerabilities and strengthening defenses against a more hostile cyber environment.
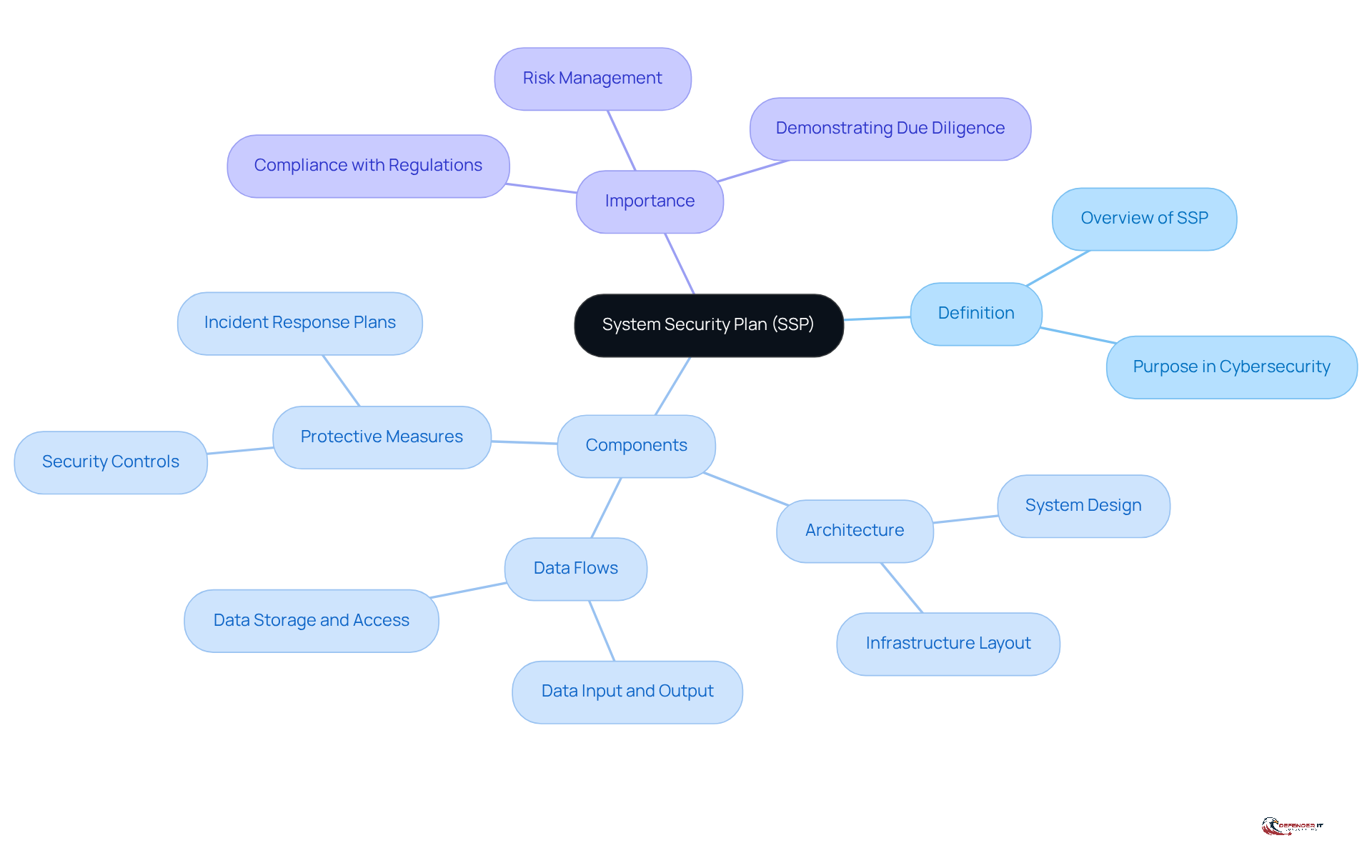
Define System Security Plan (SSP)
What is SSP in cyber security? It is a crucial document that outlines how an organization meets or plans to meet the protection requirements for its information systems. This document serves as a comprehensive framework detailing the safeguards implemented to protect sensitive information and ensure compliance with regulatory standards.
The SSP includes essential information regarding the system’s architecture, data flows, and specific protective measures designed to mitigate threats. For entities operating in regulated sectors, understanding what is SSP in cyber security is particularly vital, as it provides a structured approach to managing cybersecurity risks. Furthermore, the SSP demonstrates [[due diligence in safeguarding information assets](https://defenderit.consulting/4-essential-practices-for-choosing-a-soc-solution-provider/)](https://defenderit.consulting/4-essential-practices-for-choosing-a-soc-solution-provider/), reinforcing the organization’s commitment to security and compliance.
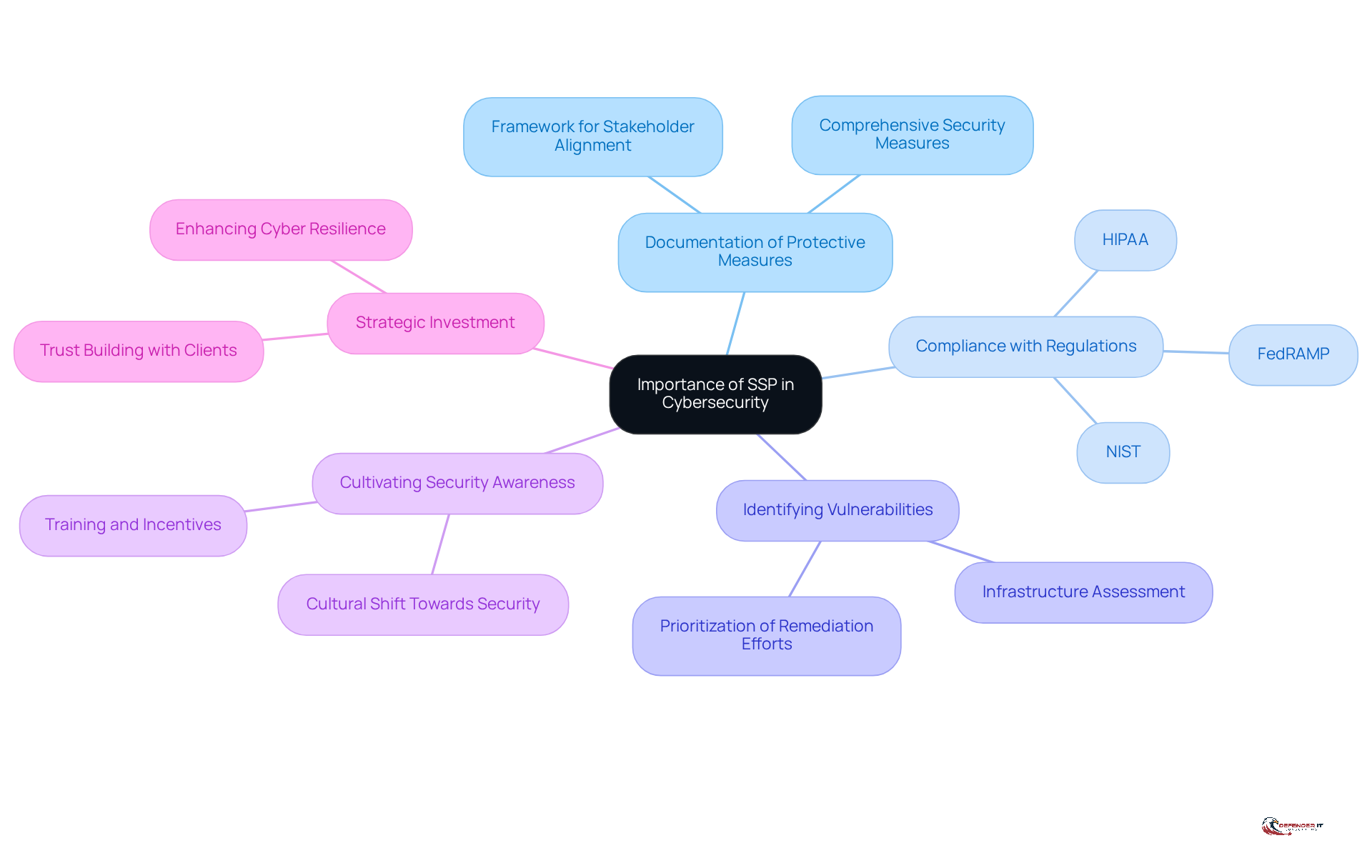
Explain the Importance of an SSP in Cybersecurity
Understanding what is SSP in cyber security is of paramount significance. An SSP serves as a comprehensive framework for organizations to document their protective measures, ensuring that all stakeholders are aligned on the actions taken to safeguard sensitive information. This documentation is essential for compliance with various regulatory frameworks, including NIST, HIPAA, and FedRAMP, which mandate that organizations effectively demonstrate their protective stance.
Furthermore, an SSP is instrumental in identifying vulnerabilities within an organization’s infrastructure, enabling the prioritization of remediation efforts. This proactive approach not only enhances compliance but also cultivates a culture of security awareness among employees, which is vital for maintaining a robust security posture. As Keri Pearlson aptly states, “Understanding where the risk is coming from is the only way we’re going to manage that risk.”
Understanding what is SSP in cyber security allows organizations to significantly bolster their resilience against cyber threats by establishing a well-defined SSP. This systematic approach not only fosters trust with clients and partners but also positions the organization to respond swiftly and effectively to potential threats. In light of the 20% increase in data breaches from 2022 to 2023, implementing an SSP represents a strategic investment in the organization’s overall cybersecurity framework, reinforcing its capacity to withstand and recover from cyber challenges. Moreover, as cybersecurity policy transitions from a focus on ‘defend and recover’ to ‘deter and disrupt,’ understanding what is SSP in cyber security becomes increasingly critical in aligning with these evolving strategies.
Identify Key Components of a System Security Plan
Key components of a System Security Plan (SSP) include:
- System Identification: This section outlines essential information about the system, including its name, purpose, and operational environment. This serves as the foundation for the entire protective framework.
- System Boundaries: Clearly defining the system’s limits is crucial for identifying included elements such as hardware, software, and network components. This aids in assessing vulnerabilities and implementing suitable protective measures.
- Protection Measures: A thorough explanation of the protection measures in place – covering technical, administrative, and physical safeguards – ensures that the system is adequately defended against potential threats.
- Roles and Responsibilities: Specifying who is accountable for implementing and maintaining protective measures fosters a culture of responsibility within the entity, which is vital for effective management.
- Risk Evaluation: Recording the results of risk evaluations is vital for recognizing vulnerabilities and guiding the creation of protective measures, thereby improving the overall resilience posture.
- Compliance Requirements: Listing applicable regulations and standards ensures that the SSP aligns with legal obligations, which is critical for avoiding penalties and maintaining business opportunities.
Together, these components create a robust security structure that helps entities understand what is SSP in cyber security for protecting their information systems. Frequent updates and assessments of the SSP are essential to adapt to changing threats and compliance demands, as entities face increasing pressure to safeguard sensitive information effectively. As noted by Plurilock, “The process of creating and maintaining a plan often reveals gaps, redundancies, or outdated assumptions that might otherwise persist unnoticed.” Furthermore, with annual global damage costs for ransomware multi-stage extortion attacks forecasted to reach USD 74 billion in 2026, the urgency of having a well-maintained SSP cannot be overstated. Organizations must also be aware of challenges such as resource constraints and resistance to change, which can complicate SSP implementation.
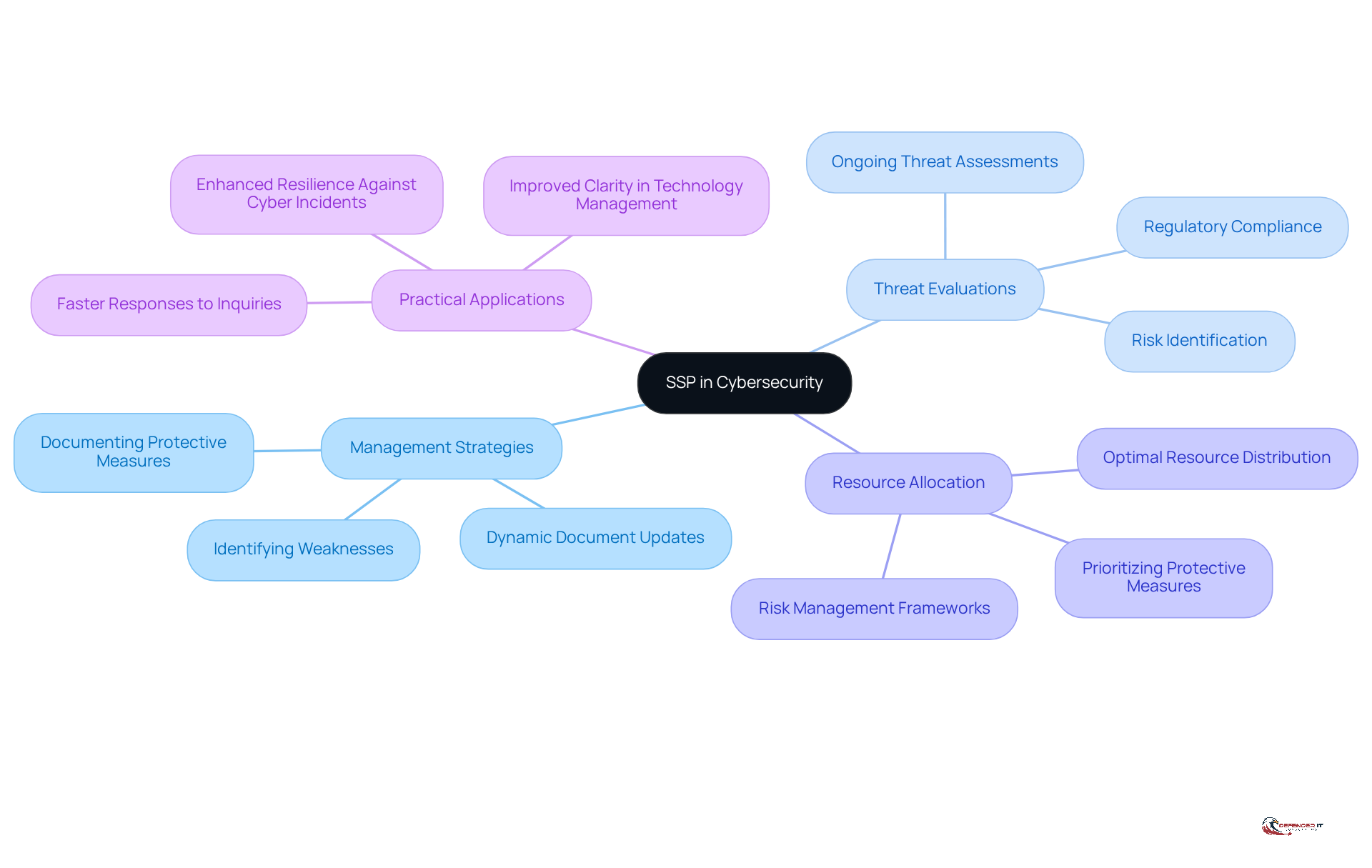
Connect SSPs to Risk Management Strategies
Understanding [[what is SSP in cyber security](https://defenderit.consulting)](https://defenderit.consulting) is essential for enhancing management strategies related to vulnerabilities within organizations. By systematically documenting protective measures and identifying weaknesses, what is SSP in cyber security provides a structured approach for evaluating and addressing threats. This enables organizations to prioritize protective measures based on the potential impact of identified threats, ensuring an optimal allocation of resources.
Moreover, understanding what is SSP in cyber security reveals how SSPs support ongoing threat evaluations and timely updates, allowing organizations to remain agile in response to evolving [[cyber threats and regulatory requirements](https://federalnewsnetwork.com/commentary/2025/08/how-agencies-can-improve-cyber-risk-management-strategies-through-a-risk-operations-center)](https://federalnewsnetwork.com/commentary/2025/08/how-agencies-can-improve-cyber-risk-management-strategies-through-a-risk-operations-center). Integrating what is SSP in cyber security into threat management frameworks not only strengthens a company’s overall security posture but also improves resilience against cyber incidents.
For instance, organizations that have implemented SSPs report improved clarity in technology management and faster responses to leadership inquiries and audit requests. This demonstrates the effectiveness of SSPs in practical applications. As the cybersecurity landscape continues to change, the adaptable nature of SSPs ensures that organizations can effectively modify their risk management strategies, ultimately fostering a more secure operational environment.
Conclusion
In conclusion, a System Security Plan (SSP) is essential for any organization aiming to protect its information systems effectively. It outlines a comprehensive strategy for safeguarding sensitive data, demonstrating a commitment to security and compliance. By clearly defining protective measures, an SSP not only enhances security but also serves as a testament to an organization’s dedication to data protection. This structured approach is crucial in today’s complex cyber landscape, where threats are increasingly sophisticated and regulatory demands are ever-present.
Key points throughout this article highlight the importance of documentation for compliance, the identification of vulnerabilities, and the necessity of regular updates. The components of an SSP – including system identification, risk evaluation, and compliance requirements – work in concert to establish a robust security framework. This proactive nature empowers organizations to prioritize security efforts and respond effectively to emerging threats, fostering a culture of security awareness and resilience.
Given the rising incidents of cyber threats and the significant financial impacts associated with data breaches, investing in a well-structured SSP is not merely a best practice; it is a critical necessity. Organizations must recognize the value of an SSP in enhancing their cybersecurity posture and commit to ongoing evaluation and improvement. By doing so, they not only protect their assets but also build trust with stakeholders, positioning themselves for long-term success in an increasingly digital world.
Frequently Asked Questions
What is a System Security Plan (SSP) in cybersecurity?
An SSP is a crucial document that outlines how an organization meets or plans to meet the protection requirements for its information systems. It serves as a comprehensive framework detailing the safeguards implemented to protect sensitive information and ensure compliance with regulatory standards.
What information is included in an SSP?
The SSP includes essential information regarding the system’s architecture, data flows, and specific protective measures designed to mitigate threats.
Why is understanding the SSP important for organizations in regulated sectors?
Understanding the SSP is vital for entities in regulated sectors as it provides a structured approach to managing cybersecurity risks and demonstrates due diligence in safeguarding information assets.
How does the SSP reinforce an organization’s commitment to security?
The SSP reinforces an organization’s commitment to security and compliance by outlining the safeguards in place to protect sensitive information and by ensuring adherence to regulatory standards.
List of Sources
- Define System Security Plan (SSP)
- White House Releases New Cyber Security Plan and Executive Order on Combatting Cybercrimes (https://naco.org/news/white-house-releases-new-cyber-security-plan-and-executive-order-combatting-cybercrimes)
- Why You Need a System Security Plan for TPRM (https://panorays.com/blog/why-you-need-a-system-security-plan-tprm)
- 45 Cybersecurity Statistics and Facts [2025] (https://onlinedegrees.sandiego.edu/cyber-security-statistics)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Benefits of System Security Plans (https://blogs.oracle.com/security/system-security-plans)
- Explain the Importance of an SSP in Cybersecurity
- White House Releases New Cyber Security Plan and Executive Order on Combatting Cybercrimes (https://naco.org/news/white-house-releases-new-cyber-security-plan-and-executive-order-combatting-cybercrimes)
- Cybersecurity plans should center on resilience | MIT Sloan (https://mitsloan.mit.edu/ideas-made-to-matter/cybersecurity-plans-should-center-resilience)
- Strategic Priorities in the 2026 US Cyber Strategy and Cybercrime Executive Order | Weaver (https://weaver.com/resources/strategic-priorities-in-the-2026-us-cyber-strategy-and-cybercrime-executive-order)
- 110 security and compliance statistics for tech leaders to know in 2025 (https://vanta.com/resources/compliance-statistics)
- The future of cybersecurity compliance in 2026 | FDM Group (https://fdmgroup.com/news-insights/future-of-cybersecurity-compliance-2026)
- Identify Key Components of a System Security Plan
- White House Releases New Cyber Security Plan and Executive Order on Combatting Cybercrimes (https://naco.org/news/white-house-releases-new-cyber-security-plan-and-executive-order-combatting-cybercrimes)
- Key Cyber Security Statistics for 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-statistics)
- System Security Plan – What is a system security plan? (https://plurilock.com/glossary/system-security-plan)
- System Security Plan: Key Components and Implementation – SearchInform (https://searchinform.com/articles/cybersecurity/measures/security-management/system-security-plan)
- Building a Strong System Security Plan Framework | Egnyte (https://egnyte.com/guides/governance/system-security-plan)
- Connect SSPs to Risk Management Strategies
- Benefits of System Security Plans (https://blogs.oracle.com/security/system-security-plans)
- Risk Management Statistics 2025 — 45 Key Figures (https://procurementtactics.com/risk-management-statistics)
- 50+ Risk Management Statistics to Know in 2026 (https://secureframe.com/blog/risk-management-statistics)
- How agencies can improve cyber risk management strategies through a risk operations center | Federal News Network (https://federalnewsnetwork.com/commentary/2025/08/how-agencies-can-improve-cyber-risk-management-strategies-through-a-risk-operations-center)
- Cybersecurity Risk Management Demand Rises as Organizations Respond to Rising Threats (https://einpresswire.com/article/868801552/cybersecurity-risk-management-demand-rises-as-organizations-respond-to-rising-threats)