Introduction
In an era marked by rapidly evolving cyber threats, organizations face relentless pressure to protect their digital assets. Vulnerability scanning stands out as a vital strategy in this context, providing a systematic method to identify and rectify security weaknesses before they can be exploited. As organizations work to bolster their cybersecurity posture, a critical question arises: how effective are these scans in genuinely mitigating risks, and what challenges do they encounter during implementation?
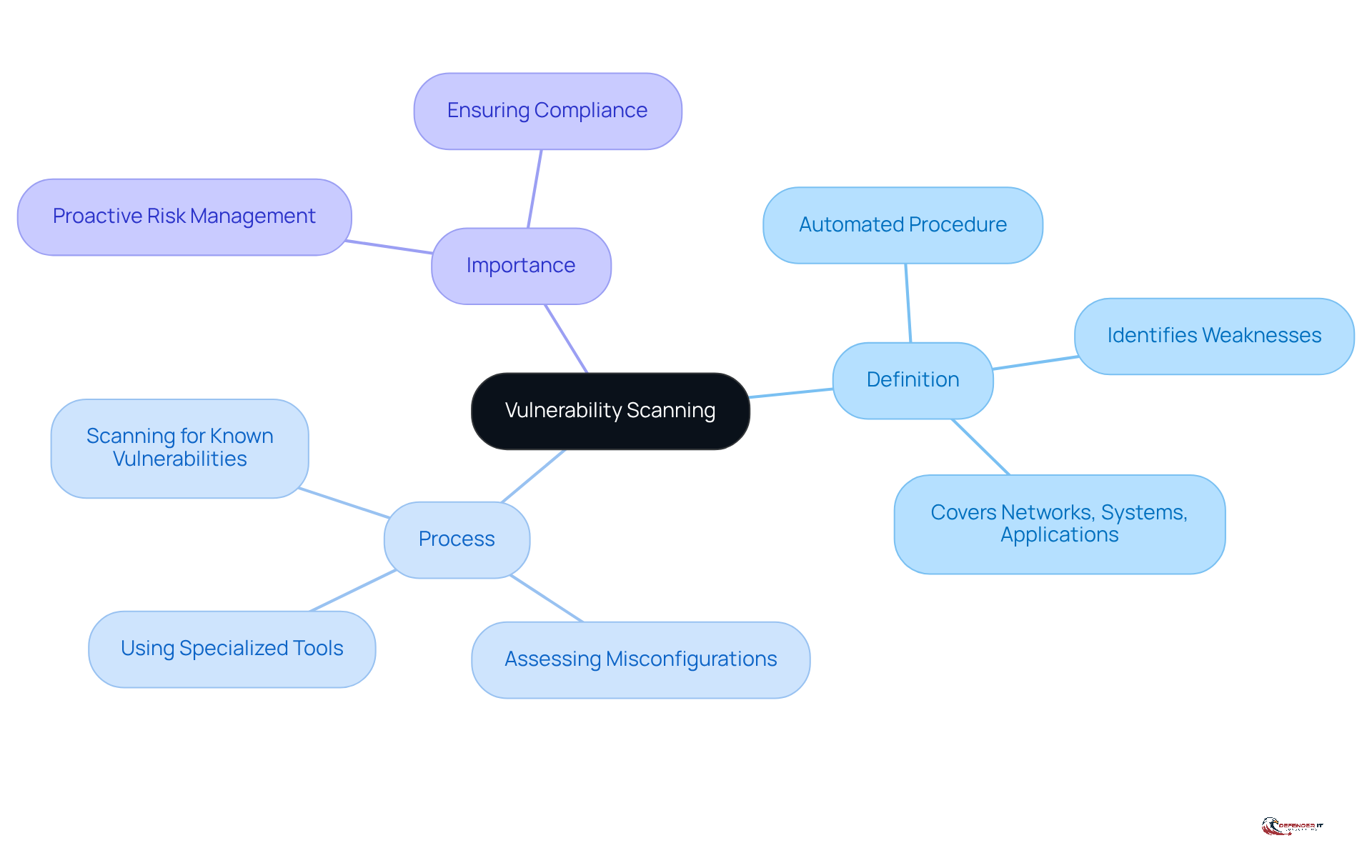
Define Vulnerability Scanning
What is vulnerability scanning? It serves as an automated procedure designed to identify, assess, and report weaknesses within an entity’s IT infrastructure, encompassing networks, systems, and applications. This essential process involves identifying vulnerabilities, misconfigurations, and potential weaknesses that cybercriminals might exploit. By employing specialized tools, organizations can systematically evaluate their security posture and prioritize remediation efforts effectively.
What is vulnerability scanning, and how does it serve as a critical component of a cybersecurity strategy by facilitating risk management and ensuring compliance with regulations? By identifying vulnerabilities before they can be exploited, organizations can bolster their defenses and safeguard sensitive information.
Context and Importance in Cybersecurity
In today’s digital landscape, organizations face an ever-changing array of threats that pose significant financial and reputational risks. What is vulnerability scanning, and why is it essential for identifying and mitigating these threats while offering a comprehensive view of security posture? Regular security assessments not only help organizations stay ahead of potential risks but also enable swift remediation, thereby significantly reducing the likelihood of breaches. Alarmingly, 59% of companies experienced a successful cyber attack in the past year, with 79% of managers reporting similar incidents, often stemming from unresolved vulnerabilities.
Additionally, industries such as finance and healthcare are subject to stringent regulatory requirements that mandate vulnerability assessments, making this practice vital for compliance. By incorporating risk assessment into their security strategies, businesses can bolster their overall defense, mitigate risks, and build trust with stakeholders.
Case studies reveal that organizations conducting regular evaluations, including nearly 1,000 assets assessed through grey box penetration testing campaigns, have effectively reduced their exposure to threats. This underscores the critical need for vulnerability scanning in our interconnected environment. As cybersecurity experts note, “Cyber threats show no sign of slowing down. ‘They have turned into a persistent background sound,’ emphasizing the urgency of addressing vulnerabilities.”
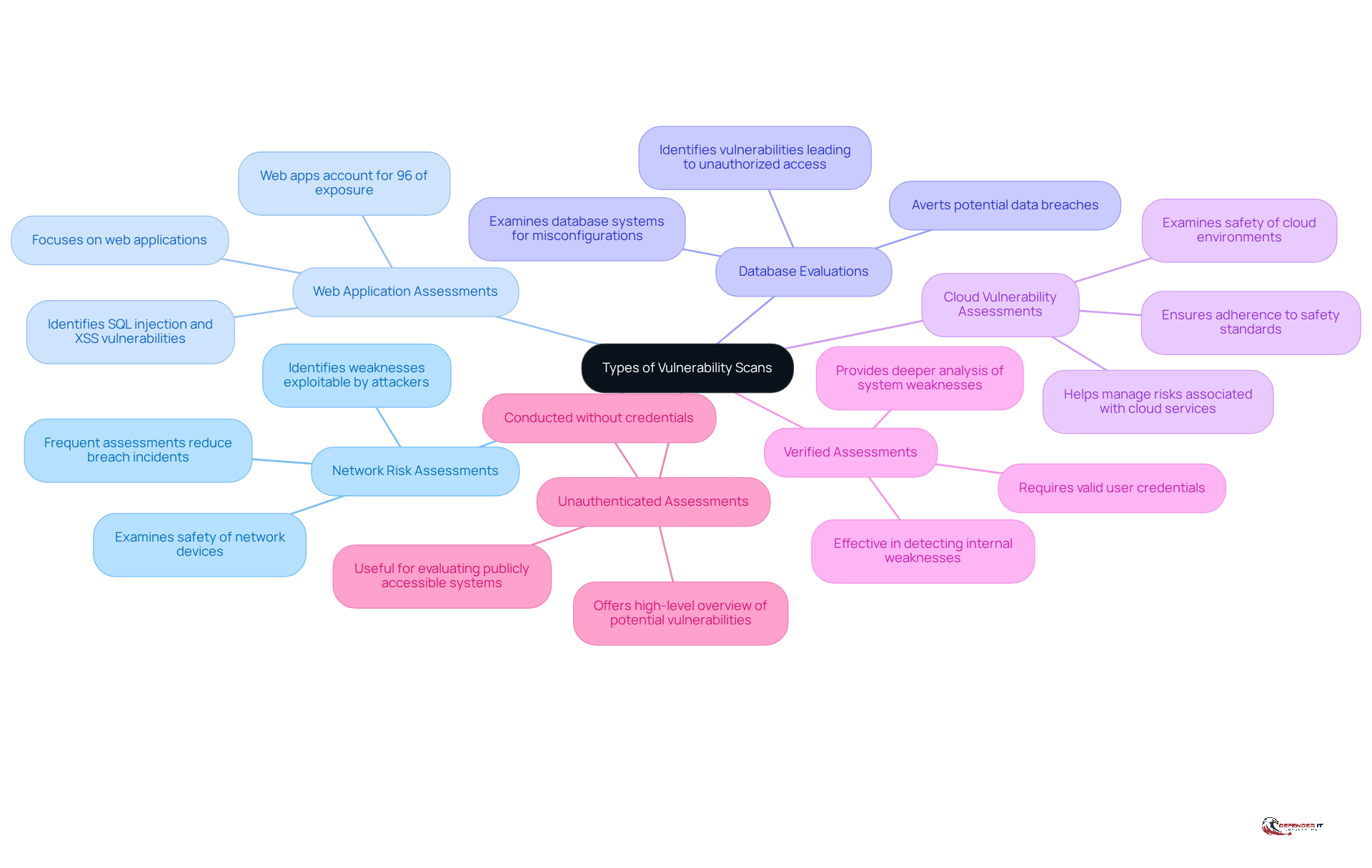
Types of Vulnerability Scans
There are several types of scans, each designed to address specific security needs:
- Network Risk Assessments: These evaluations examine the safety of network devices, such as routers and switches, identifying weaknesses that could be exploited by attackers. Organizations that conduct assessments often experience a notable decrease in incidents of breaches.
- Web Application Scans: Centered on web applications, these evaluations identify vulnerabilities such as SQL injection and cross-site scripting (XSS) that could endanger user data. Given that web applications represent 96% of all exposure, regular scanning is essential for preserving safety.
- Database Security Scans: These assessments examine database systems for misconfigurations and vulnerabilities that could result in unauthorized access or data breaches. By recognizing flaws in database protection, entities can avert possible data breaches.
- Cloud Security Scans: As organizations progressively embrace cloud services, these evaluations examine the safety of cloud environments, ensuring adherence to safety standards. Organizations that perform assessments can better manage risks associated with cloud services.
- Verified Assessments: These evaluations necessitate valid user credentials to deliver a deeper analysis of weaknesses within systems, providing a more comprehensive perspective of security posture. This kind of examination is especially efficient in detecting internal weaknesses that might not be apparent through unauthenticated assessments.
- Unauthenticated Assessments: Conducted without credentials, these evaluations offer a high-level overview of potential vulnerabilities visible from an external perspective. They are useful for evaluating the safety of publicly accessible systems.
Every type of examination, such as what is vulnerability scanning, serves a distinct function and can be chosen according to the entity’s particular security needs. As Mohammed Khalil stresses, “You can’t protect what you aren’t aware of,” underscoring the importance of comprehensive scanning to safeguard digital assets. Moreover, entities that can address critical weaknesses within 48-72 hours can prevent most widespread exploitation, highlighting the importance of performing these scans consistently.
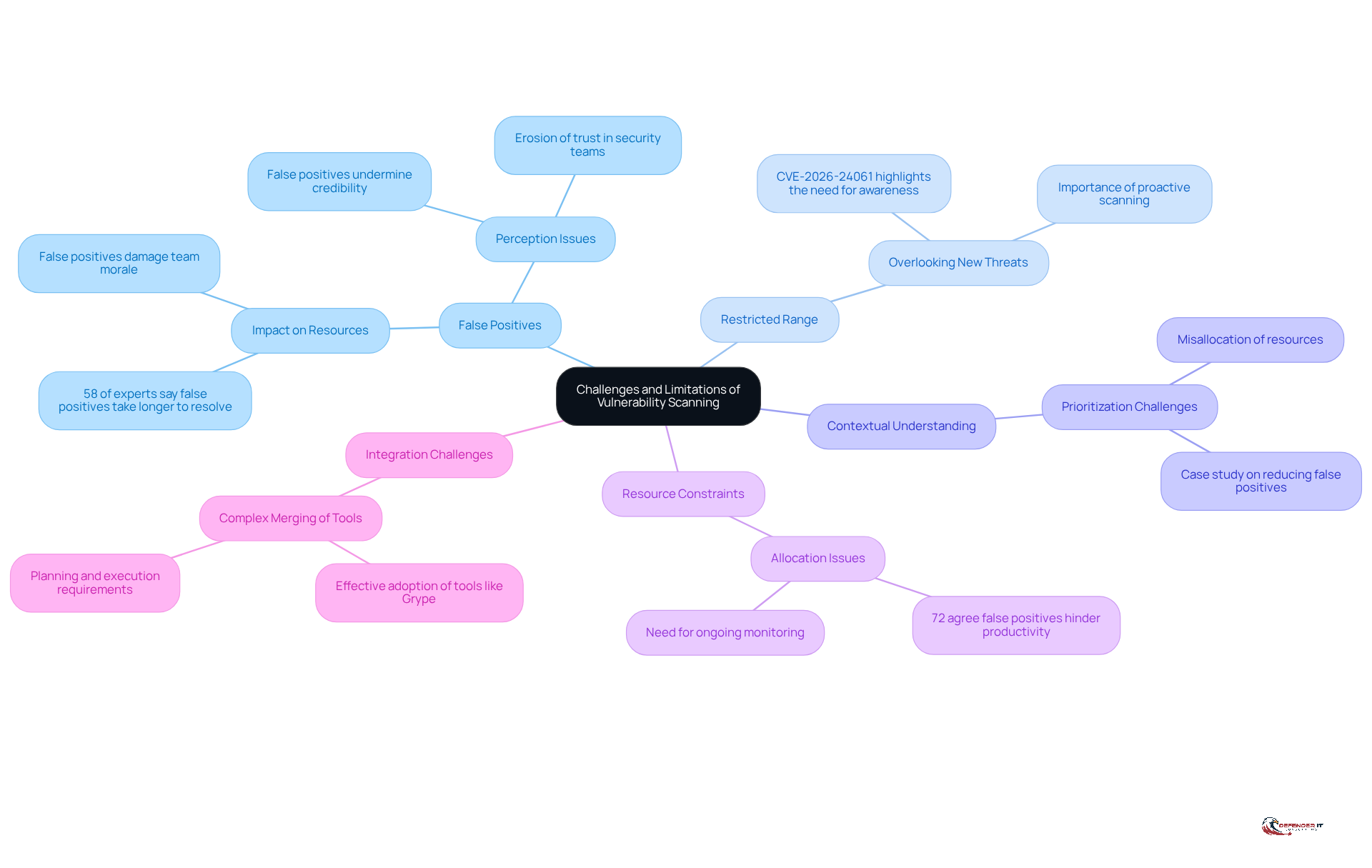
Challenges and Limitations of Vulnerability Scanning
While vulnerability scanning serves as a powerful tool for enhancing cybersecurity, it presents several challenges and limitations that organizations must navigate:
- False Positives: Scanners frequently report vulnerabilities that do not exist, consuming valuable resources on unnecessary remediation efforts. A survey revealed that 58% of safety experts indicated that false positives take longer to resolve than true positives, detracting from productive activities such as software development. As noted by OP Innovate, this issue highlights the broader impact on security operations.
- Restricted Range: Vulnerability scanners generally concentrate on recognized weaknesses, potentially overlooking novel or developing threats that have yet to be documented. For instance, the recent CVE-2026-24061 underscores the critical importance of staying informed about vulnerabilities that may not be captured in standard scans. Entities that have effectively addressed similar weaknesses emphasize the significance of proactive monitoring.
- Contextual Understanding: Many scanners lack the ability to evaluate the business context, complicating the prioritization of remediation based on business impact. This limitation can lead to a misallocation of resources, as organizations may address less critical weaknesses while neglecting more severe threats. A case study on the impact of reducing false negatives demonstrates how prioritizing essential vulnerabilities can free up time for strategic initiatives.
- Resource Constraints: Organizations often struggle to allocate sufficient resources for regular scanning and remediation, particularly when faced with competing priorities. This challenge is intensified by the need for ongoing monitoring and prompt responses to newly identified vulnerabilities. A statistic from the recent evaluation indicates that 72% of respondents agreed that resource limitations hinder effective vulnerability management, further emphasizing the necessity for efficient processes.
- Integration Challenges: Merging security scanning tools with existing security frameworks can be complex, requiring thorough planning and execution. Organizations that effectively adopt tools like Grype have reported enhanced precision in vulnerability detection, showcasing the advantages of a well-integrated approach.
To maximize the effectiveness of vulnerability scanning, organizations should adopt a holistic strategy that includes regular updates, continuous monitoring, and a commitment to promptly addressing identified vulnerabilities. By focusing on reducing false positives and enhancing the accuracy of scanning tools, organizations can improve their overall security posture and better allocate resources to critical areas.
Conclusion
Vulnerability scanning is not just a best practice; it is a necessity in today’s interconnected digital landscape. This essential component of modern cybersecurity strategies serves as a proactive measure to identify and mitigate weaknesses within an organization’s IT infrastructure. By leveraging automated tools to assess networks, systems, and applications, organizations can detect vulnerabilities before they can be exploited by cybercriminals. This approach not only enhances overall security but also helps maintain compliance with industry regulations and builds trust with stakeholders.
The critical role of vulnerability scanning in risk management is underscored by various types of scans, including:
- Network risk assessments
- Web application evaluations
- Cloud vulnerability assessments
Each type serves a specific purpose, enabling organizations to effectively address their unique security needs. However, challenges associated with vulnerability scanning, such as false positives and resource constraints, highlight the importance of a comprehensive security approach that prioritizes continuous monitoring and prompt remediation of identified vulnerabilities.
Organizations must prioritize regular assessments and invest in effective scanning tools to safeguard their sensitive information and reduce the risk of costly data breaches. By staying vigilant and proactive, businesses can enhance their security posture and navigate the complexities of the ever-evolving cyber threat landscape.
Frequently Asked Questions
What is vulnerability scanning?
Vulnerability scanning is an automated procedure designed to identify, assess, and report weaknesses within an entity’s IT infrastructure, including networks, systems, and applications.
What does vulnerability scanning aim to identify?
It aims to identify known vulnerabilities, misconfigurations, and potential weaknesses that cybercriminals might exploit.
How do organizations use vulnerability scanning?
Organizations use specialized tools to systematically evaluate their security posture and prioritize remediation efforts effectively.
Why is vulnerability scanning important for cybersecurity?
It is a critical component of a comprehensive cybersecurity strategy as it facilitates proactive risk management and ensures compliance with regulatory requirements.
How does vulnerability scanning help organizations protect sensitive information?
By identifying vulnerabilities before they can be exploited, organizations can bolster their defenses and safeguard sensitive information.
List of Sources
- Define Vulnerability Scanning
- cisa.gov (https://cisa.gov/news-events/news/end-just-beginning-better-security-enhanced-vulnerability-management-openeox)
- Navigating the Future: Key IT Vulnerability Management Trends (https://thehackernews.com/2025/02/navigating-future-key-it-vulnerability.html)
- The Vulnerability Backlog Crisis: Why 45% of Enterprise Vulnerabilities Never Get Fixed (https://edgescan.com/the-vulnerability-backlog-crisis-why-45-of-enterprise-vulnerabilities-never-get-fixed)
- 35 Cyber Security Vulnerability Statistics, Facts In 2026 (https://getastra.com/blog/security-audit/cyber-security-vulnerability-statistics)
- NIST is rethinking its role in analyzing software vulnerabilities (https://cybersecuritydive.com/news/nist-cve-vulnerability-analysis-nvd-review/810300)
- Context and Importance in Cybersecurity
- Vulnerability Forecast 2026. Threats, Trends and Real-World Risks – Patrowl (https://patrowl.io/en/actualites/vulnerability-forecast-2026-what-organizations-can-expect)
- Ultimate Guide to Vulnerability Assessment: What, Why & How (2026 Edition) (https://acronis.com/en/blog/posts/ultimate-guide-to-vulnerability-assessment-2026)
- Why and How to Perform Cybersecurity Risk Assessments in 2026 (https://maddevs.io/blog/how-to-perform-cybersecurity-risk-assessments)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Types of Vulnerability Scans
- goodreads.com (https://goodreads.com/quotes/tag/cybersecurity)
- Key Cyber Security Statistics for 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-statistics)
- 35 Cyber Security Vulnerability Statistics, Facts In 2026 (https://getastra.com/blog/security-audit/cyber-security-vulnerability-statistics)
- Vulnerabilities Statistics 2025: Record CVE Surge (https://deepstrike.io/blog/vulnerability-statistics-2025)
- Challenges and Limitations of Vulnerability Scanning
- Industry Report: The True Costs of False Positives in Software Security (https://finitestate.io/blog/industry-report-false-positives-software-security)
- False Positives and False Negatives in Vulnerability Scanning: Lessons from the Trenches | Anchore (https://anchore.com/blog/false-positives-and-false-negatives-in-vulnerability-scanning)
- sentinelone.com (https://sentinelone.com/cybersecurity-101/cybersecurity/vulnerability-management-metrics)
- Why False Positives Are Still Killing Security Teams | OP Innovate (https://op-c.net/blog/why-false-positives-killing-security-teams)