Introduction
In an era where cyber threats are increasingly prevalent, the security of medical devices has emerged as a paramount concern for healthcare organizations. Conducting comprehensive medical device security assessments is essential not only for safeguarding patient safety and data integrity but also for ensuring compliance with evolving regulatory standards. Recent high-profile breaches have underscored the challenges many institutions face in implementing effective security measures, leaving them vulnerable to potential attacks.
How can organizations effectively master the art of medical device security assessment to protect both their patients and their reputations?
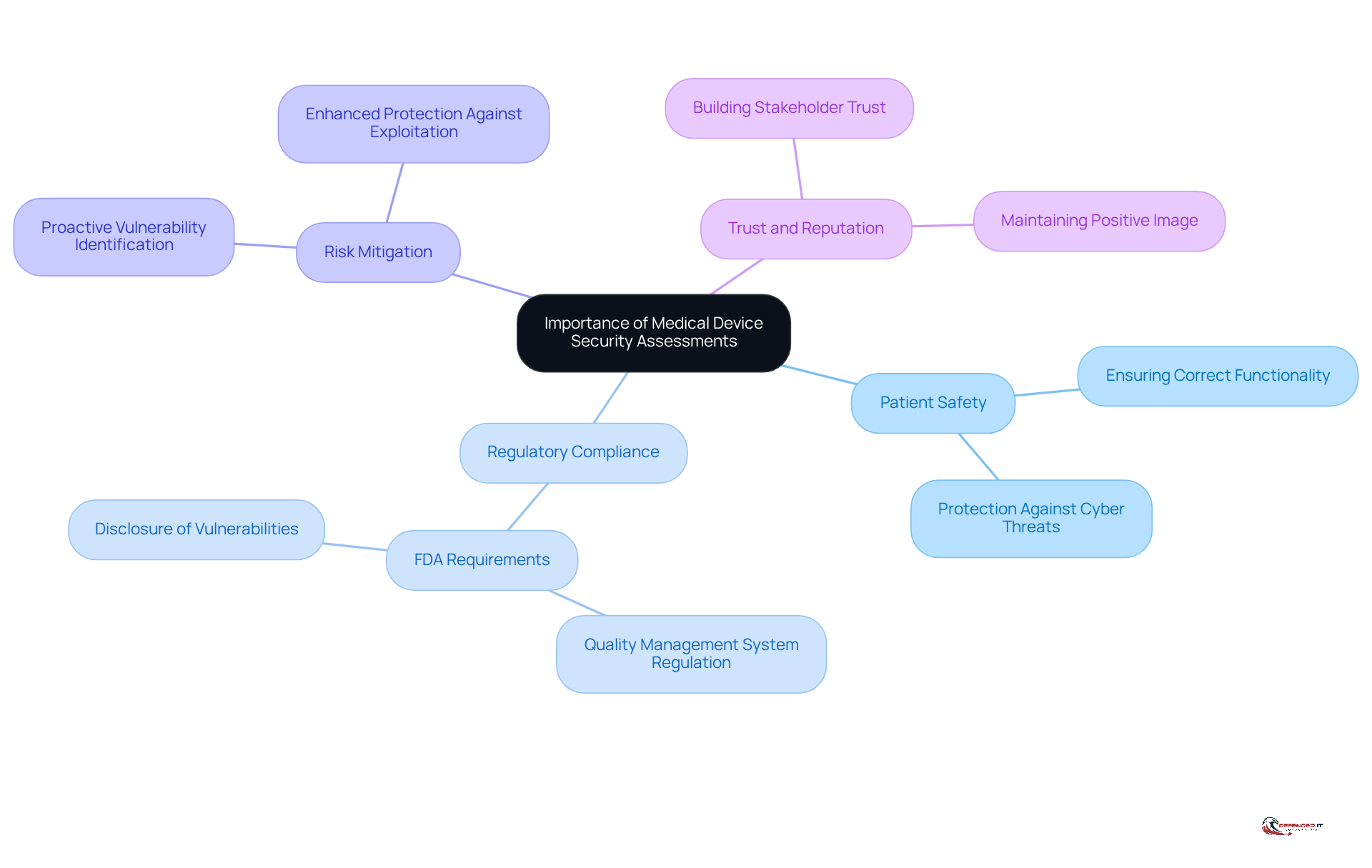
Understand the Importance of Medical Device Security Assessments
Conducting a medical device security assessment is crucial for evaluating medical equipment to identify weaknesses that could jeopardize patient safety and data integrity. These medical device security assessments not only assist organizations in meeting regulatory requirements, such as those set by the FDA, but also provide protection against cyber threats that can lead to significant financial and reputational damage. Understanding the enables stakeholders to prioritize protective measures that safeguard both patients and healthcare providers.
Key Reasons for Conducting Assessments:
- Ensuring patient safety involves performing a medical device security assessment to guarantee that medical devices function correctly and are secure from cyber threats.
- Regulatory Compliance: Compliance with standards established by regulatory bodies, including the revised Quality Management System Regulation effective February 2, 2026, which incorporates ISO 13485, is essential to avoid penalties and maintain market access.
- Risk Mitigation: Proactively identifying and addressing vulnerabilities can prevent exploitation by malicious actors, thereby enhancing overall protection. The FDA mandates that manufacturers disclose uncontrolled vulnerabilities within 30 days, underscoring the urgency of conducting a medical device security assessment.
- Trust and Reputation: Demonstrating a commitment to safety fosters trust among patients and stakeholders, which is critical for maintaining a positive image in the healthcare sector.
Recent incidents, such as the cyberattack on Stryker in 2023 linked to a hacking group associated with Iran, underscore the urgent need for robust cybersecurity measures in healthcare equipment. As the landscape of cyber threats evolves, the implementation of a medical device security assessment becomes increasingly essential to ensure the protection and efficacy of healthcare instruments. Under the new FDA framework, manufacturer liability and risk exposure have significantly increased, further emphasizing the necessity for proactive risk management.
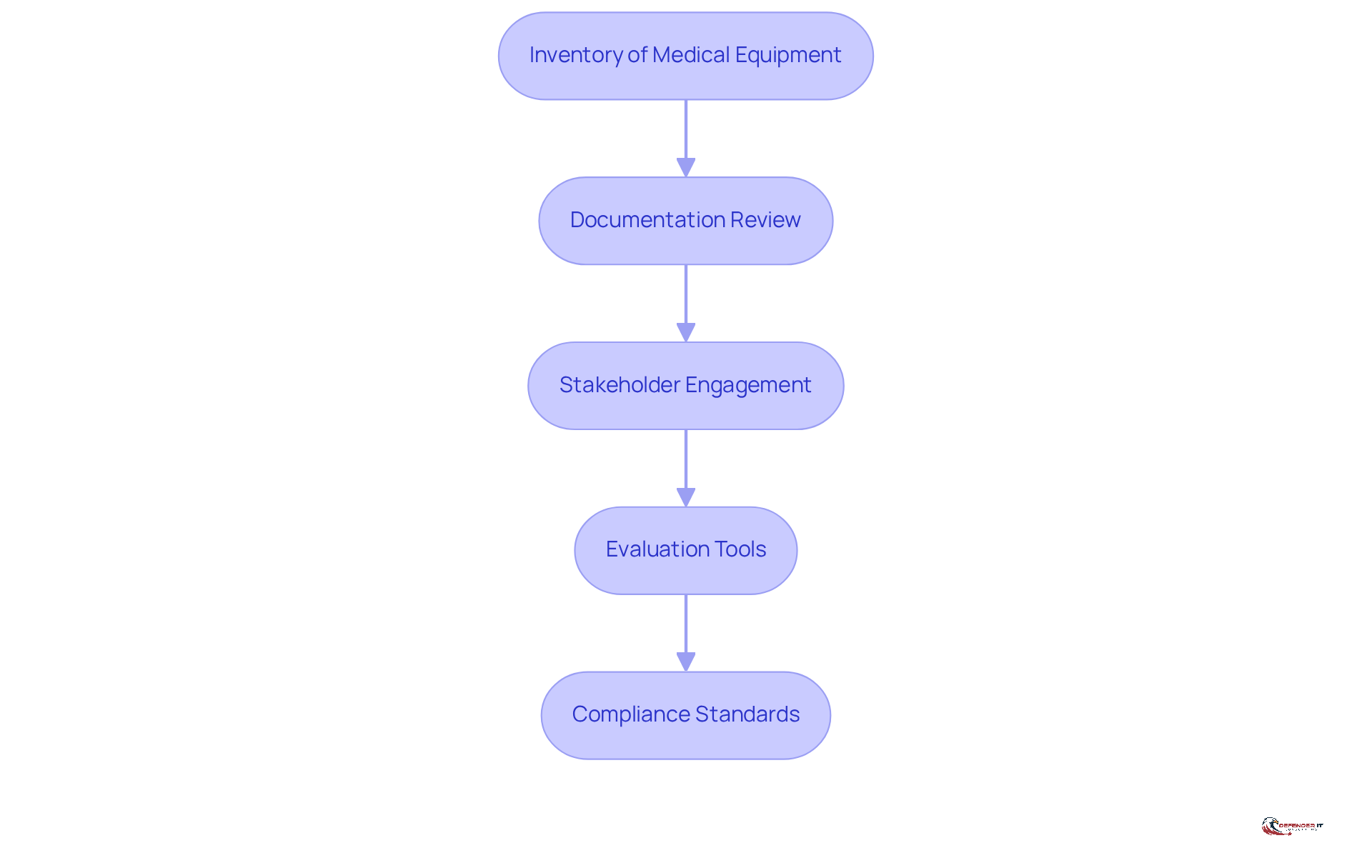
Prepare for the Assessment: Gather Necessary Information and Resources
Before conducting a healthcare instrument evaluation, it is essential to gather all necessary information and resources to ensure a comprehensive review. This preparation phase encompasses several critical steps:
- Inventory of Medical Equipment: Compile a detailed inventory of all medical equipment currently in use, noting their specifications, software versions, and network configurations. This inventory serves as the foundation for conducting a to identify potential vulnerabilities.
- Documentation Review: Collect relevant documentation, including user manuals, safety policies, and previous assessment reports. This review provides context and insight into the operational history and security posture of each unit, particularly focusing on the medical device security assessment.
- Stakeholder Engagement: Actively involve key stakeholders such as IT staff, device manufacturers, and clinical personnel. Their insights are invaluable for understanding the operational environment and ensuring that all perspectives are considered in the evaluation process. Continuous engagement through regular reviews and updates to the Information Security Management System (ISMS) is vital for enhancing measures related to medical device security assessment.
- Evaluation Tools: Select appropriate tools and methodologies for the evaluation, including vulnerability scanning software and risk assessment frameworks. Utilizing the right tools enhances both the accuracy and efficiency of the medical device security assessment.
- Compliance Standards: Familiarize yourself with applicable regulatory standards, such as FDA guidelines, to ensure that the evaluation meets legal requirements and industry best practices. Ongoing oversight of compliance is crucial to adhere to these standards and strengthen the overall protective stance regarding medical device security assessment.
By thoroughly preparing in these areas, organizations can streamline the evaluation process and significantly enhance the effectiveness of their healthcare product evaluations. Furthermore, recognizing the potential financial implications of cyberattacks, such as the estimated costs associated with incidents like the WannaCry attack, underscores the urgency of these preparatory steps.
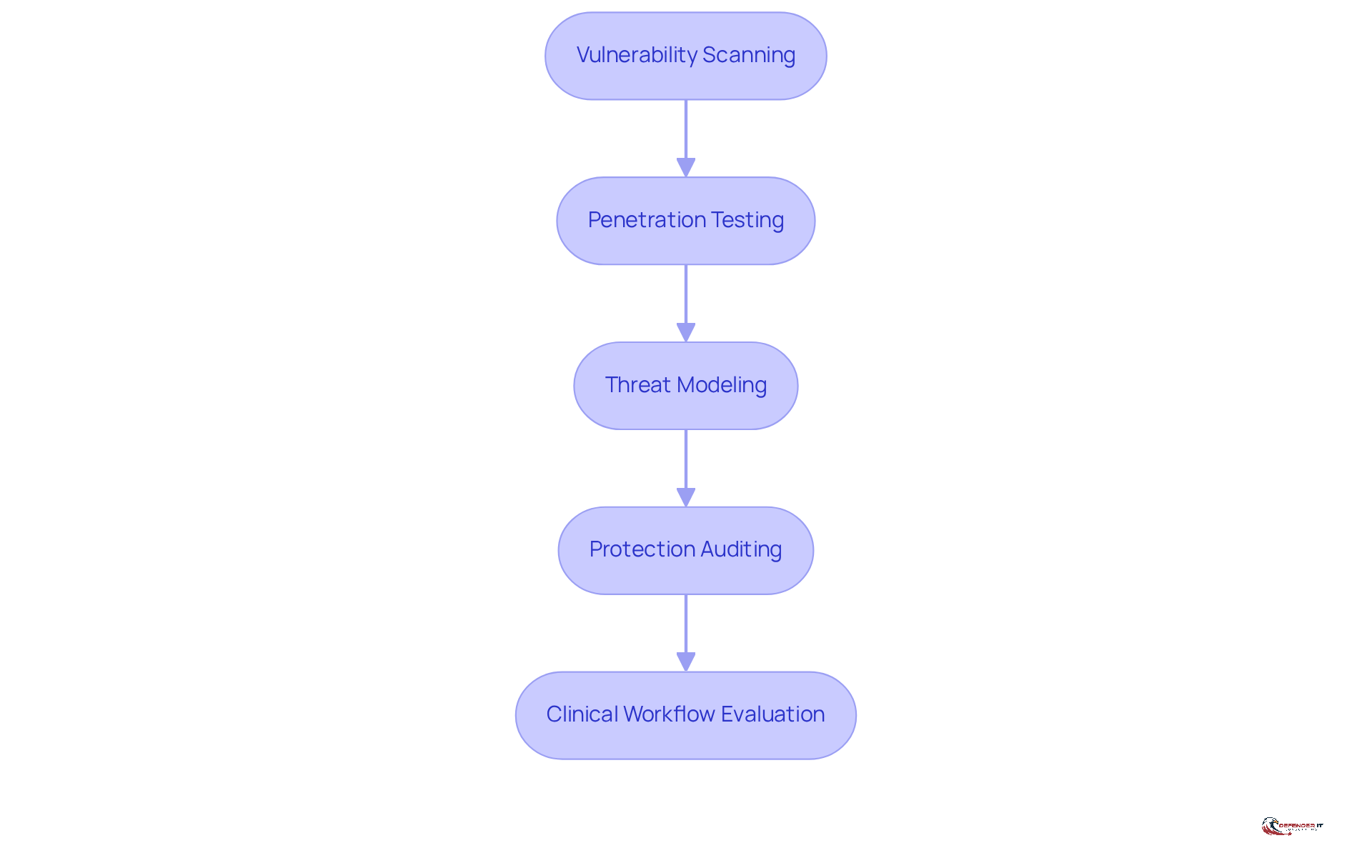
Conduct the Assessment: Evaluate Medical Devices Using Established Methodologies
Organizations should adhere to established methodologies to conduct a thorough medical device security assessment that ensures patient safety and operational resilience.
- [Vulnerability Scanning](https://defenderit.consulting/4-best-practices-for-implementing-mdr-services-in-manufacturing/): Organizations should utilize automated tools to systematically examine equipment for known vulnerabilities. This step is crucial; recent reports indicate that 63% of vulnerabilities listed in CISA’s Known Exploitable Vulnerabilities catalog are present on healthcare networks. This statistic underscores the .
- [Penetration Testing](https://defenderit.consulting/best-practices-for-effective-endpoint-detection-in-manufacturing/): Simulating cyber attacks on medical equipment allows organizations to evaluate defenses and uncover exploitable vulnerabilities. Engaging external cybersecurity firms for penetration testing can significantly enhance a manufacturer’s protective stance, as these specialists can identify blind spots that internal teams might overlook.
- Threat Modeling: Analyzing potential threats to equipment involves considering factors such as functionality, network exposure, and historical data on comparable items. This approach enables organizations to prioritize vulnerabilities based on their potential impact. Notably, there has been a staggering 437% year-over-year increase in Remote Code Execution and Privilege Escalation exploits identified in recent studies, highlighting the need for continuous vigilance.
- Protection Auditing: Conducting a thorough examination of protection policies and practices related to each device is essential for ensuring adherence to industry standards. Regular audits are vital for maintaining a robust protection framework, particularly as the healthcare sector faces heightened regulatory scrutiny. As Phil Englert, VP of Medical Device Protection at Health-ISAC, emphasizes, “Healthcare organizations must prioritize cybersecurity measures, implement strong cybersecurity practices, conduct regular risk evaluations, and remain informed about the latest threats and technologies to proactively safeguard against cyber threats.”
- Clinical Workflow Evaluation: Assessing how healthcare tools integrate into clinical processes is critical for identifying potential threats arising from their practical use. Given the interconnected nature of healthcare systems, weaknesses in one component can jeopardize the entire network.
By employing these methodologies, organizations can gain a comprehensive understanding of their healthcare equipment protection stance and identify crucial areas for enhancement through a medical device security assessment. A joint research report has identified 993 vulnerabilities across 966 healthcare products, emphasizing the urgency of implementing these strategies.
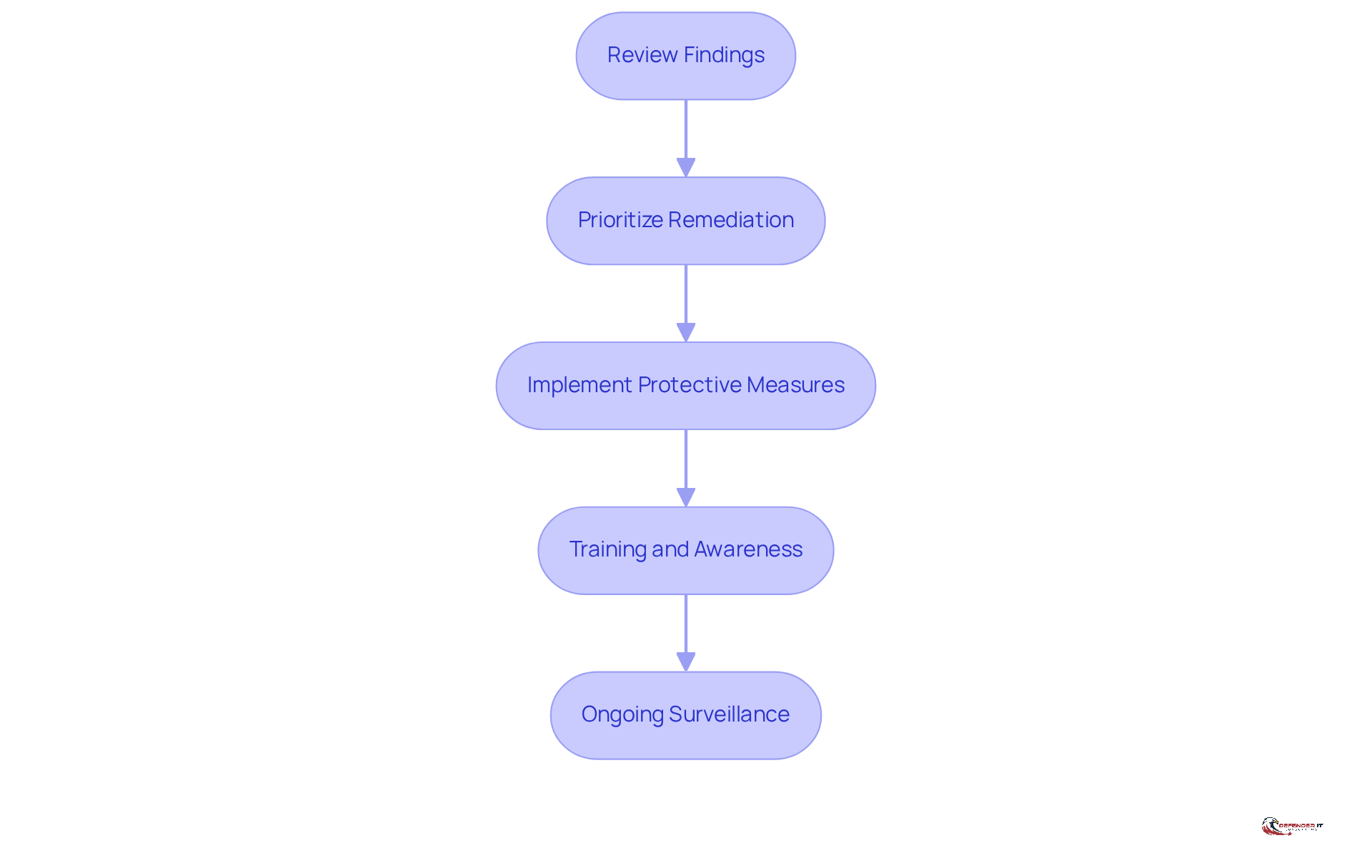
Analyze Results and Implement Recommendations for Improved Security
To enhance medical device safety, conducting a to evaluate outcomes and implement recommendations is essential. The following steps outline an effective approach:
- Review Findings: Begin by compiling and reviewing the assessment results. Categorize vulnerabilities according to their severity and potential impact on patient safety.
- Prioritize Remediation: Develop a remediation plan that prioritizes the most critical vulnerabilities. Consider factors such as risk exposure and regulatory requirements in this process.
- Implement Protective Measures: Apply necessary protective measures, including software updates, access restrictions, and network segmentation, to mitigate identified risks.
- Training and Awareness: Conduct training sessions for staff on new protection protocols, emphasizing the importance of maintaining equipment safety.
- Ongoing Surveillance: Establish an ongoing surveillance program to routinely evaluate the safety status of healthcare equipment and adapt to emerging threats.
By adhering to these steps, organizations can effectively respond to findings from their medical device security assessment and bolster their overall security posture, thereby ensuring the safety and integrity of medical devices.
Conclusion
Conducting a thorough medical device security assessment is essential for safeguarding patient safety and maintaining data integrity within healthcare settings. By systematically evaluating medical devices, organizations can identify vulnerabilities and implement necessary protective measures. This not only ensures compliance with regulatory standards but also builds trust among patients and stakeholders.
This article outlines a four-step approach to mastering medical device security assessments:
- Understanding their importance
- Preparing effectively
- Conducting the assessment using established methodologies
- Analyzing results to implement improvements
Each step emphasizes the necessity of proactive measures, from gathering essential information and engaging stakeholders to utilizing advanced evaluation techniques and prioritizing remediation efforts.
The significance of medical device security assessments is paramount. As cyber threats continue to evolve, healthcare organizations must prioritize these assessments to protect their equipment and patients. By embracing best practices and fostering a culture of continuous improvement, stakeholders can enhance the security posture of medical devices, thereby mitigating risks and ensuring a safer healthcare environment for all.
Frequently Asked Questions
What is the purpose of conducting a medical device security assessment?
The purpose of conducting a medical device security assessment is to evaluate medical equipment for weaknesses that could jeopardize patient safety and data integrity, ensuring that devices function correctly and are secure from cyber threats.
Why is regulatory compliance important in medical device security assessments?
Regulatory compliance is important because it helps organizations adhere to standards established by regulatory bodies, such as the FDA and the revised Quality Management System Regulation effective February 2, 2026, which incorporates ISO 13485. Compliance is essential to avoid penalties and maintain market access.
How do medical device security assessments contribute to risk mitigation?
Medical device security assessments contribute to risk mitigation by proactively identifying and addressing vulnerabilities, preventing exploitation by malicious actors and enhancing overall protection for patients and healthcare providers.
What role does trust and reputation play in medical device security?
Trust and reputation are critical as demonstrating a commitment to safety fosters trust among patients and stakeholders, which is essential for maintaining a positive image in the healthcare sector.
Can you provide an example of a recent cyber incident that highlights the need for medical device security assessments?
A recent example is the cyberattack on Stryker in 2023, which was linked to a hacking group associated with Iran. This incident underscores the urgent need for robust cybersecurity measures in healthcare equipment.
How has the FDA’s new framework affected manufacturer liability and risk exposure?
The FDA’s new framework has significantly increased manufacturer liability and risk exposure, emphasizing the necessity for proactive risk management in medical device security.