Introduction
In an era where cyber threats are increasingly prevalent, organizations are tasked not only with responding to incidents but also with navigating a complex and evolving regulatory landscape. A robust incident response plan serves as a strategic asset, capable of mitigating damage, safeguarding sensitive data, and enhancing overall resilience. Given that the average time to identify a breach has reached nearly 200 days, it is imperative for organizations to effectively prepare for, respond to, and learn from incidents. This proactive approach fosters a culture of continuous improvement and compliance.
Establish a Comprehensive Incident Response Plan
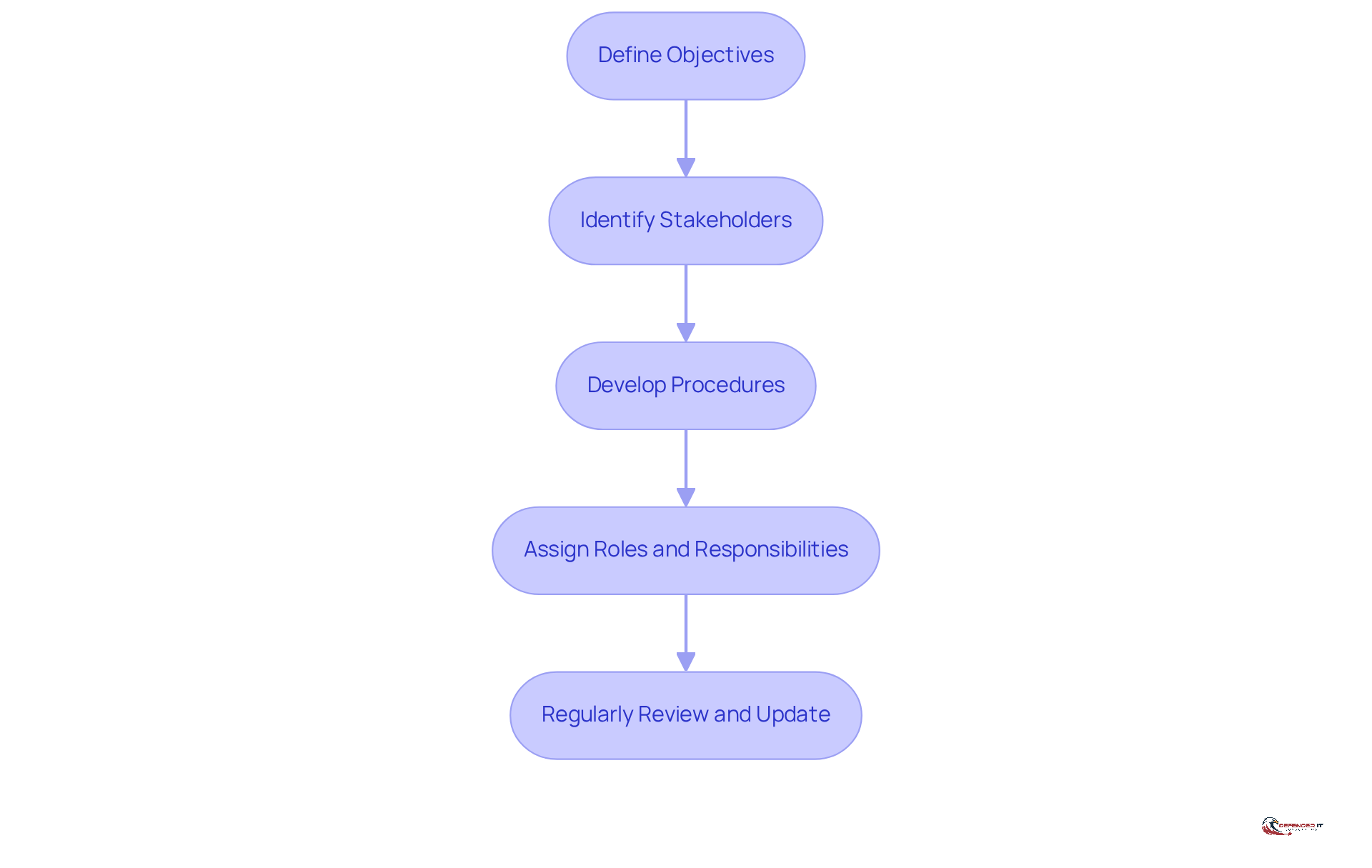
To establish a comprehensive incident response plan, organizations should follow these steps:
- Define Objectives: Clearly outline the goals of the response plan, including minimizing damage, ensuring adherence to regulations, and protecting sensitive data.
- Identify Stakeholders: Involve key personnel from IT, legal, compliance, and management to ensure all perspectives are considered.
- Develop Procedures: The importance of procedures cannot be understated. Focus on creating guidelines for detecting and addressing incidents. This should include communication protocols and escalation paths.
- Assign Responsibilities: Clearly outline who is accountable for each element of the incident management, ensuring responsibility and efficiency.
- Review and Update: The plan should be a living document, reviewed and updated regularly to reflect changes in the threat landscape and organizational structure.
By adhering to these steps, organizations can develop a robust incident response plan that enhances their preparedness and resilience.
Implement Key Phases of Incident Response
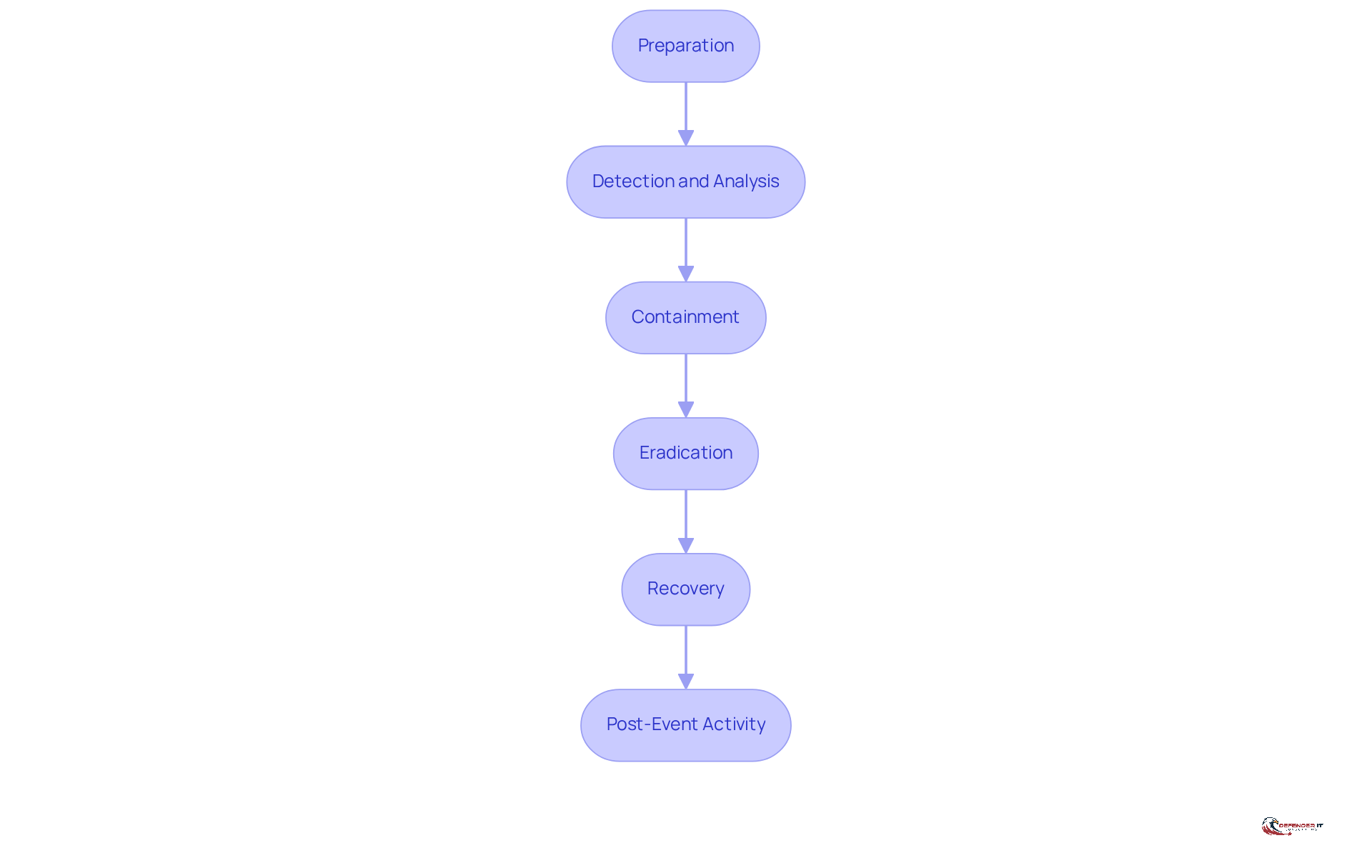
The process comprises several critical phases that organizations must follow to effectively manage incidents:
- Preparation: Establishing a robust foundation is essential. This phase involves ensuring that all necessary tools, resources, and personnel are prepared before an event occurs. Regular training and drills are vital to empower staff with the knowledge and skills needed for effective response. As John C. Maxwell emphasizes, prioritizing preparation is crucial for effective business operations.
- Detection and Analysis: Organizations should implement advanced monitoring tools to swiftly identify anomalies and potential threats. Examining alerts is essential for understanding the nature and extent of the event, with the goal of minimizing impact. Companies utilizing automation and AI in security operations can reduce breach containment time by 40%, underscoring the need for timely detection mechanisms.
- Containment: Rapidly isolating affected systems is critical to prevent further damage. This may involve disconnecting systems from the network or shutting down specific services to limit the impact of the event.
- Eradication: Identifying and removing the threat is essential. This phase may require forensic analysis and applying necessary patches to ensure that the threat is fully addressed.
- Recovery: The focus here is on restoring systems to normal operations while ensuring that all vulnerabilities are resolved. Continuous monitoring is necessary to detect any residual issues that may arise post-recovery.
- Post-Event Activity: Conducting reviews is vital for identifying weaknesses and areas for improvement. Entities that document post-breach discoveries significantly enhance their reaction time and precision, with only 40% currently engaging in this practice. Moreover, organizations that prioritize learning from incidents emphasize the critical importance of learning from events.
By systematically executing these stages, organizations can adopt a comprehensive strategy for incident response and recovery that reduces harm and enhances compliance, ultimately fostering a culture of readiness and resilience against threats.
Conduct Post-Incident Reviews for Continuous Improvement
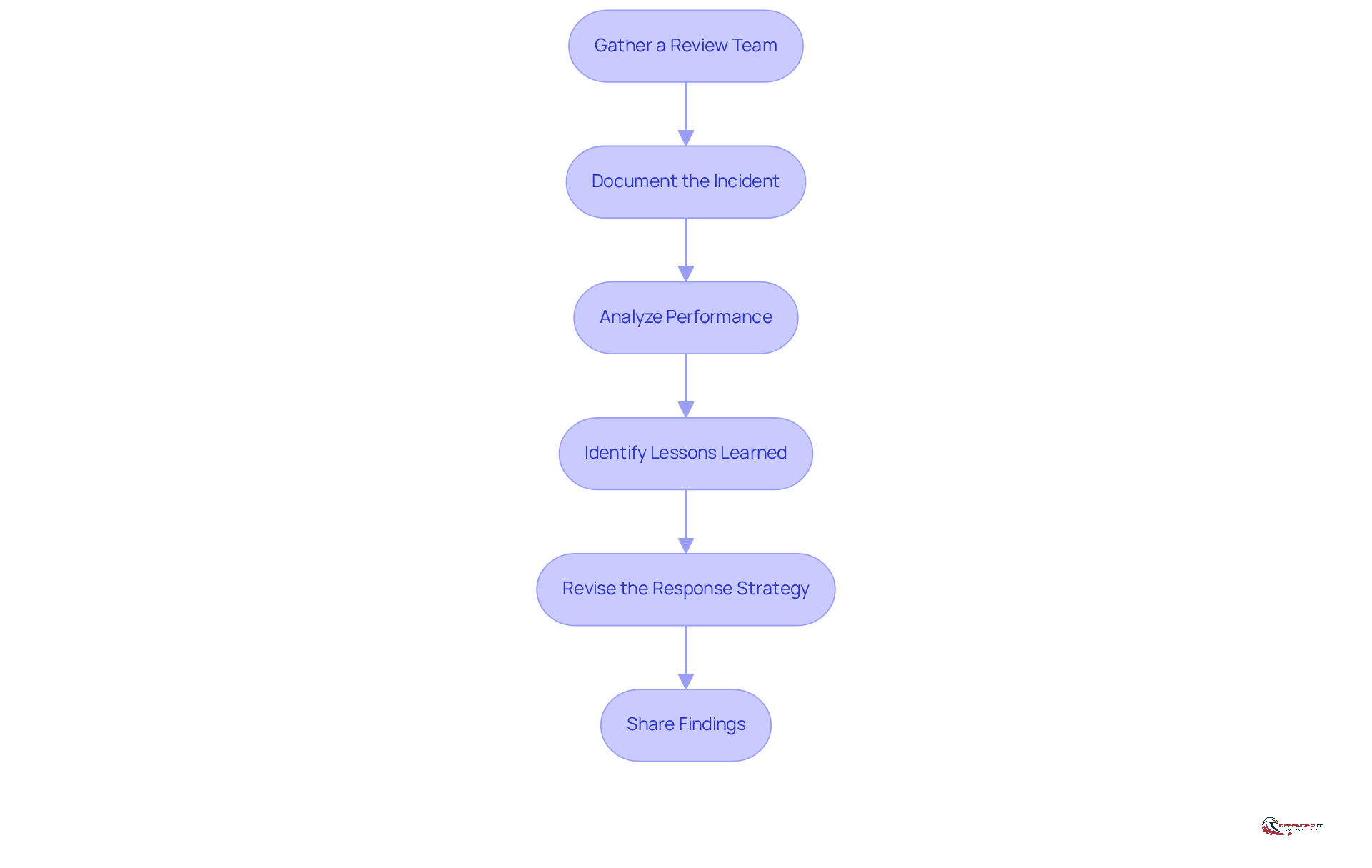
To conduct effective reviews, organizations should adhere to the following best practices:
- Gather a Review Team: Assemble a diverse group of stakeholders involved in incident management, including responders, IT/security leaders, and executives. This diversity ensures a comprehensive analysis of the incident.
- Create a Timeline: Create a detailed timeline of events, capturing detection, actions taken, and recovery efforts. This documentation is crucial for understanding the sequence of events and identifying areas for improvement.
- Analyze Performance: Assess the effectiveness of incident handling against established goals. Evaluate which strategies were successful and where gaps existed, focusing on detection, containment, and clarity of communication.
- Identify Improvements: Discuss key takeaways, emphasizing improvements in processes, tools, and training. This reflective practice transforms incidents into opportunities for resilience and growth.
- Incorporate Lessons: Incorporate lessons learned into the response plan to enhance future readiness. This ensures that organizations are better prepared to manage similar incidents in the future.
- Share Findings: Communicate insights from the review with relevant stakeholders, fostering a culture of learning and awareness within the organization.
By following these steps, companies can effectively transform incidents into learning opportunities, thereby strengthening their response capabilities and enhancing overall resilience. In 2026, it was observed that only 34% of entities are conducting post-event reviews, highlighting the need for a systematic approach to documentation and analysis. As Pritesh Parekh emphasizes, ‘The review process is one of the most valuable tools for improving security management over time.’ Furthermore, conduct reviews within 24-72 hours after addressing an incident to ensure details remain fresh and actionable.
Align Incident Response with Compliance Requirements
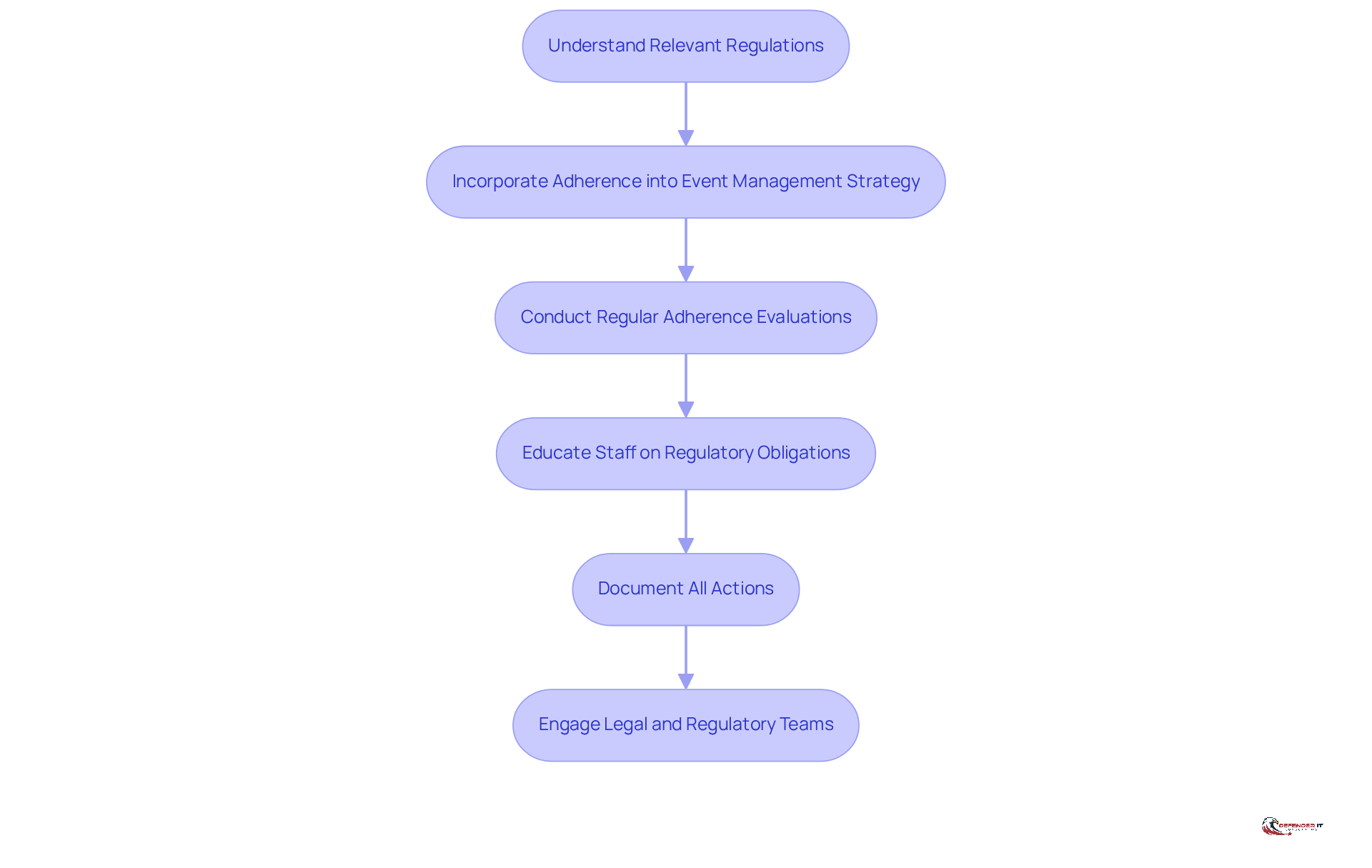
To effectively align incident response with compliance requirements, organizations should take the following steps:
- Understand Relevant Regulations: Familiarize yourself with applicable laws and regulations, such as GDPR, HIPAA, and PCI DSS, which significantly influence crisis management strategies, financial penalties, and reputational damage. For instance, the average fine reached $8.19 million in 2023, underscoring the financial implications of noncompliance.
- Incorporate Adherence into the Event Management Strategy: Ensure that the event management strategy clearly contains procedures for compliance. This integration assists in optimizing reactions during events and guarantees that all requirements are fulfilled.
- Conduct Regular Audits: Frequently assess occurrence management practices to ensure they align with regulatory standards. These audits assist in recognizing gaps and areas for enhancement, ensuring that organizations stay ready for possible events.
- Provide Comprehensive Training: Deliver thorough training to all pertinent personnel concerning regulatory duties and the significance of following them during emergencies. Knowledgeable personnel are crucial for efficient event management and regulation adherence.
- Document All Actions: Maintain comprehensive records of events management actions, decisions made, and communications. This documentation is essential for showcasing adherence during audits and can act as a reference for future events.
- Engage Legal and Regulatory Teams: Involve legal and regulatory teams in the event management process to ensure that all actions taken adhere to regulations. Their expertise can help identify issues and mitigate risks associated with noncompliance. Anna Fitzgerald, a Senior Content Marketing Manager at Secureframe, highlights the significance of converting intricate regulatory structures into useful resources, which can assist companies in grasping their obligations.
By aligning incident response and recovery efforts with compliance requirements, organizations can significantly reduce legal risks and enhance their overall preparedness, ensuring they are well-prepared to handle incidents effectively.
Conclusion
Establishing a robust incident response and recovery framework is essential for organizations aiming to protect sensitive data and comply with regulatory requirements. A comprehensive incident response plan enables organizations to minimize damage during incidents, ensuring preparedness against the evolving landscape of cyber threats. This proactive approach safeguards assets while enhancing compliance and operational resilience.
Key components for a successful incident response strategy include:
- Establishing clear objectives
- Identifying stakeholders
- Implementing critical phases:
- Preparation
- Detection
- Containment
- Eradication
- Recovery
- Post-event analysis
Each phase is vital for equipping organizations to handle incidents efficiently, allowing them to learn from past experiences and improve future responses. Furthermore, aligning incident response efforts with compliance requirements is crucial for avoiding legal repercussions and maintaining organizational integrity.
As cyber threats become increasingly sophisticated, organizations must prioritize their incident response and recovery strategies. By embracing best practices and fostering a culture of continuous improvement, businesses can enhance their security posture and build trust with stakeholders. Taking action today to strengthen incident response capabilities will lead to more resilient organizations, prepared to navigate the challenges of tomorrow.
Frequently Asked Questions
What is the purpose of establishing a comprehensive incident response plan?
The purpose is to minimize damage, ensure adherence to regulations, and protect sensitive data during incidents.
Who should be involved in developing the incident response plan?
Key personnel from IT, legal, compliance, and management should be involved to consider all perspectives.
What are the key steps to develop an incident response plan?
The key steps include defining objectives, identifying stakeholders, developing procedures, assigning roles and responsibilities, and regularly reviewing and updating the plan.
Why is it important to develop procedures for incident response and recovery?
Developing procedures is crucial for effectively detecting and addressing incidents, as well as establishing communication protocols and escalation paths.
How often should the incident response plan be reviewed and updated?
The plan should be regularly reviewed and updated to reflect changes in the threat landscape and organizational structure.
What benefits does a robust incident response plan provide to organizations?
A robust plan enhances organizational preparedness and compliance posture in the face of potential crises.
List of Sources
- Establish a Comprehensive Incident Response Plan
- HHS Stresses Importance of Having an Effective Cybersecurity Incident Response Plan (https://hipaajournal.com/hhs-stresses-importance-of-having-an-effective-cybersecurity-incident-response-plan)
- Incident Response Statistics: How Do You Compare? | FRSecure (https://frsecure.com/blog/incident-response-statistics-how-do-you-compare)
- Incident Response Statistics to Know in 2025 (https://jumpcloud.com/blog/incident-response-statistics)
- The Critical Importance of a Robust Incident Response Plan in 2025 | Sygnia (https://sygnia.co/blog/critical-importance-incident-response-plan)
- The Importance of Having an Incident Response Plan | Travelers Institute (https://institute.travelers.com/cyber-security/cyber-readiness/incident-response)
- Implement Key Phases of Incident Response
- Cyber threats to watch in 2026 – and other cybersecurity news (https://weforum.org/stories/2026/02/2026-cyberthreats-to-watch-and-other-cybersecurity-news)
- Incident Response Statistics: How Do You Compare? | FRSecure (https://frsecure.com/blog/incident-response-statistics-how-do-you-compare)
- Incident Response Statistics to Know in 2025 (https://jumpcloud.com/blog/incident-response-statistics)
- 22 Workplace Safety Quotes From Leaders and Experts – AlertMedia (https://alertmedia.com/blog/workplace-safety-quotes)
- Conduct Post-Incident Reviews for Continuous Improvement
- How to conduct an effective post-incident review (https://csoonline.com/article/4009438/how-to-conduct-an-effective-post-incident-review.html)
- onpage.com (https://onpage.com/onpage-university/guide-to-post-incident-reviews)
- Post-Incident After-Action Reviews Are Critical to Building Organizational Resilience, Says McLean & Company (https://finance.yahoo.com/news/post-incident-action-reviews-critical-193000867.html)
- Building the Perfect Post-Security Incident Review Playbook (https://darkreading.com/cybersecurity-operations/perfect-post-security-incident-review-playbook)
- Post-incident review: Boost Your Cybersecurity Resilience (https://cdg.io/blog/post-incident-review)
- Align Incident Response with Compliance Requirements
- Cyber security compliance statistics for 2026 | CyberArrow (https://cyberarrow.io/blog/cyber-security-compliance-statistics)
- mark43.com (https://mark43.com/press/solutions-review-cybersecurity-awareness-month-quotes-from-industry-experts-in-2024)
- Cybersecurity Facts and Stats as of 2026 (https://preveil.com/blog/cybersecurity-statistics)
- 130+ Compliance Statistics & Trends to Know for 2026 (https://secureframe.com/blog/compliance-statistics)