Introduction
Crafting an effective penetration testing quote is not merely a formality; it is a crucial step that can significantly shape a client’s cybersecurity strategy. By integrating essential components such as:
- The scope of work
- Objectives
- A transparent cost breakdown
organizations can ensure that their assessments align with specific security goals and regulatory requirements.
However, the challenge lies in customizing these quotes to meet unique client needs while maintaining clarity and transparency. Cybersecurity firms must navigate the delicate balance between comprehensive evaluations and tailored solutions that resonate with their clients’ distinct contexts. How can they achieve this balance effectively?
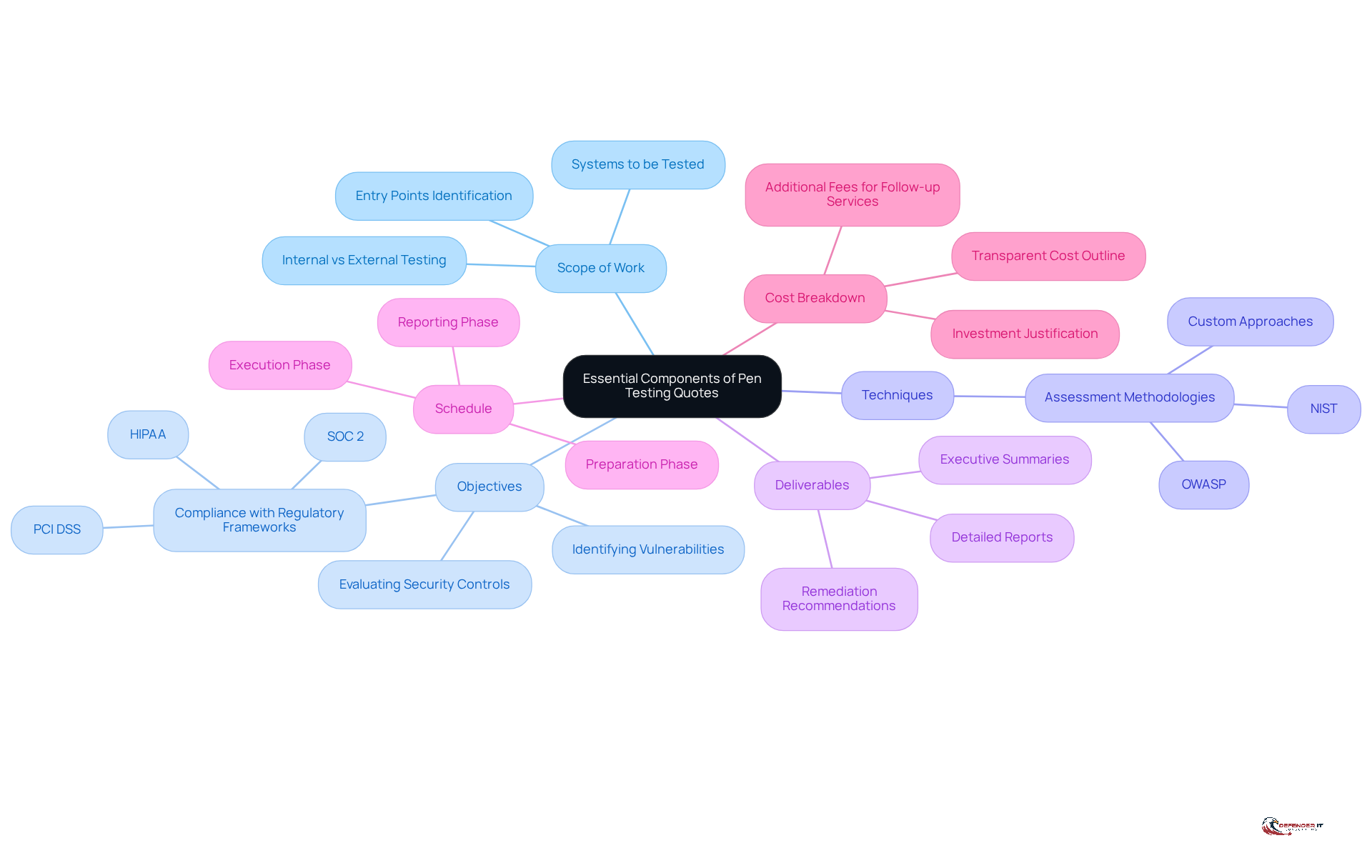
Define Essential Components of Pen Testing Quotes
When crafting a penetration testing quote, several key components must be included to ensure clarity and effectiveness:
- Scope of Work: Clearly outline the systems, applications, or networks to be tested, specifying whether the test is internal, external, or both. This focus helps identify potential entry points and ensures comprehensive coverage.
- Objectives: Define the goals of the penetration assessment, such as identifying vulnerabilities, evaluating security controls, or ensuring compliance with regulatory frameworks like PCI DSS, HIPAA, and SOC 2. These frameworks are tightening, making penetration evaluations a requirement or strong recommendation. Setting clear objectives directs the evaluation process and aligns with organizational needs. As one expert remarked, ‘Begin with crystal-clear objectives’ to guide the entire evaluation effort in the right direction.
- Techniques: Specify the assessment methodologies to be employed, such as OWASP, NIST, or custom approaches tailored to the customer’s environment. This clarity assists clients in comprehending the rigor and relevance of the evaluation process.
- Deliverables: List the expected deliverables, including detailed reports, executive summaries, and remediation recommendations. Clear documentation is crucial for communicating findings to stakeholders and facilitating informed decision-making.
- Schedule: Provide an estimated schedule for the evaluation process, encompassing preparation, execution, and reporting phases. This helps manage expectations and ensures timely delivery of results.
- Cost Breakdown: Include a transparent breakdown of costs related to the evaluation, detailing any additional fees for follow-up services or consultations. A clear financial outline assists customers in comprehending the investment needed and the worth of the services provided. Significantly, the expense of a data breach can greatly surpass the investment in proactive security assessments, making this clarity even more essential.
Incorporating these components not only enhances the clarity of the pen testing quote but also empowers clients to make informed decisions regarding their cybersecurity investments. By outlining the scope of work and objectives, organizations can ensure that security assessments align with their safety goals and regulatory requirements, ultimately minimizing the risk of financial and reputational harm.
Customize Quotes for Client-Specific Needs
To effectively customize penetration testing quotes, it is essential to consider several key strategies:
- Industry-Specific Risks: Assess the unique risks associated with the customer’s industry. For example, financial institutions often require more rigorous evaluations due to stringent regulatory compliance, which can significantly impact the scope and methodology of assessments.
- Business Objectives: Align assessment aims with the customer’s overarching business goals. Understanding the customer’s objectives-whether enhancing security, meeting compliance standards, or protecting sensitive data-can inform a more tailored testing approach that directly supports their strategic initiatives.
- Previous Assessments: Review any prior assessments or tests conducted on the client’s systems. Insights from previous evaluations can highlight areas of vulnerability that need focused attention in the current test, ensuring that resources are allocated effectively.
- Stakeholder Input: Engage with key stakeholders to gather insights on specific concerns or areas of focus. This collaboration fosters a more relevant and efficient evaluation strategy, as it incorporates the viewpoints of those who best understand the operational context.
- Regulatory Compliance: Ensure that the quote addresses specific compliance requirements relevant to the customer’s industry, such as PCI-DSS for payment processors or HIPAA for healthcare organizations. Compliance-driven evaluations can increase expenses by 15% to 30%, but they are crucial for fulfilling legal requirements and preventing potential fines.
By customizing pen testing quotes in this manner, cybersecurity firms can deliver more relevant and effective services, ultimately enhancing the client’s security posture and aligning with their business objectives. Furthermore, it is important to recognize that quality security assessments can yield returns exceeding 12,000% by preventing even a single successful attack. As one specialist noted, “The best method to grasp what your security assessment will cost is to converse with a provider who poses the right questions during scoping.
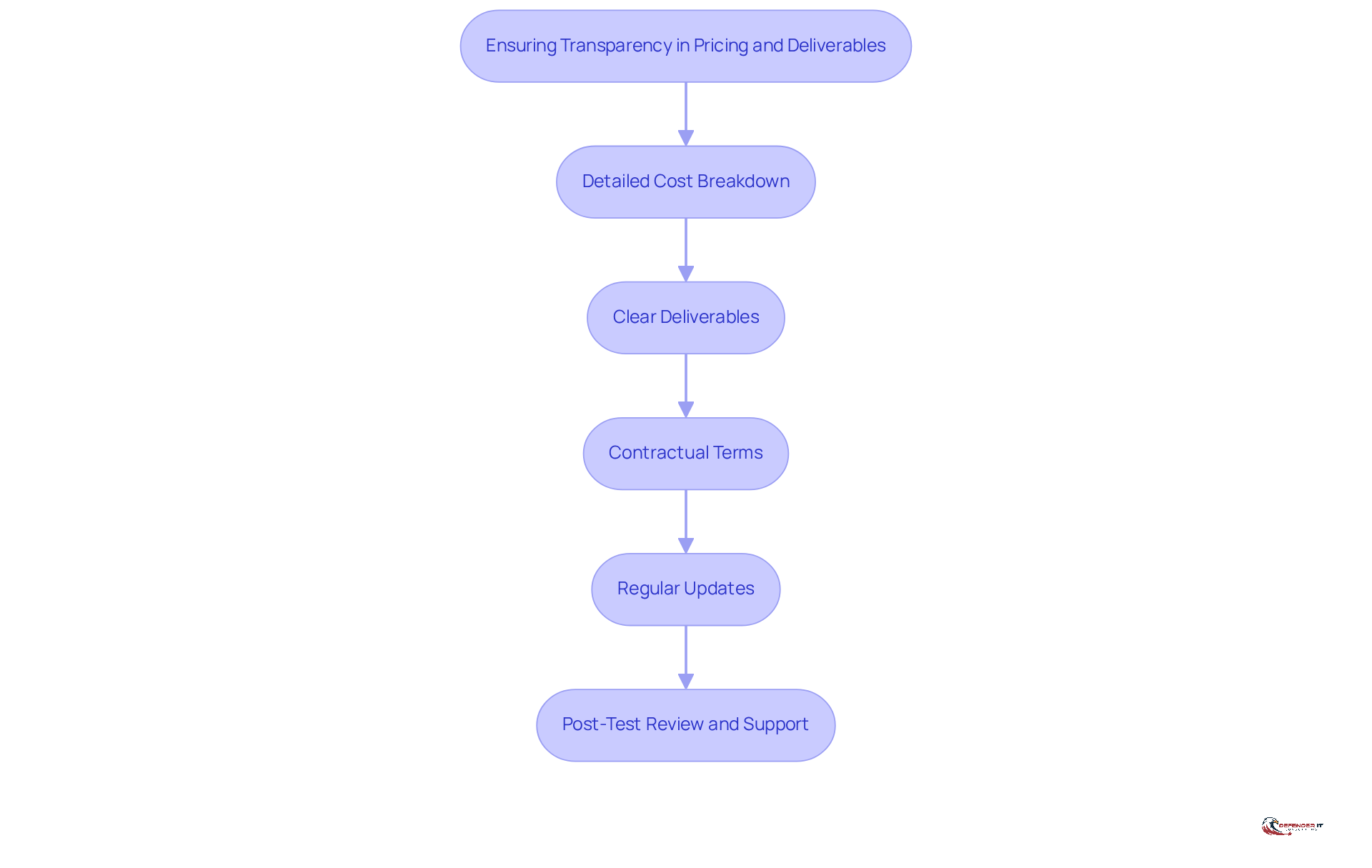
Ensure Transparency in Pricing and Deliverables
To promote transparency in penetration testing quotes, it is essential to implement the following practices:
- Detailed Cost Breakdown: A comprehensive breakdown of costs should be provided, including any potential additional fees for follow-up services or consultations. This clarity assists customers in understanding what they are paying for and ensures they are aware of the investment they are making in their cybersecurity. Compliance standards such as PCI DSS and HIPAA can increase the complexity and cost of penetration assessments, which makes it crucial to include these factors in the pen testing quote.
- Clear Deliverables: It is important to specify what the customer will receive at the conclusion of the evaluation process, such as detailed reports, executive summaries, and remediation plans. This clarity helps customers assess the value of the service and understand the actionable insights they can expect.
- Contractual Terms: Clearly outlining any terms and conditions associated with the evaluation, including confidentiality agreements and liability clauses, is vital. This ensures that both parties are aware of their rights and responsibilities, fostering a secure and professional relationship.
- Regular Updates: Consistent updates throughout the testing process should be provided to keep stakeholders informed of progress and any preliminary findings. This ongoing communication fosters trust and engagement, allowing customers to feel involved in the process.
- Post-Test Review and Support: Conducting a post-test review meeting to discuss findings, recommendations, and next steps is essential. Additionally, emphasizing the importance of post-engagement support, which includes assistance with vulnerability remediation and clarification of findings, strengthens transparency. This collaborative approach allows for customer feedback, ensuring that their concerns are addressed and that they comprehend the implications of the findings.
By ensuring transparency, cybersecurity firms can build stronger relationships with clients, leading to better collaboration and more effective security outcomes. As BreachLock emphasizes, while the cost of a successful attack can be devastating, the cost of prevention is invaluable.
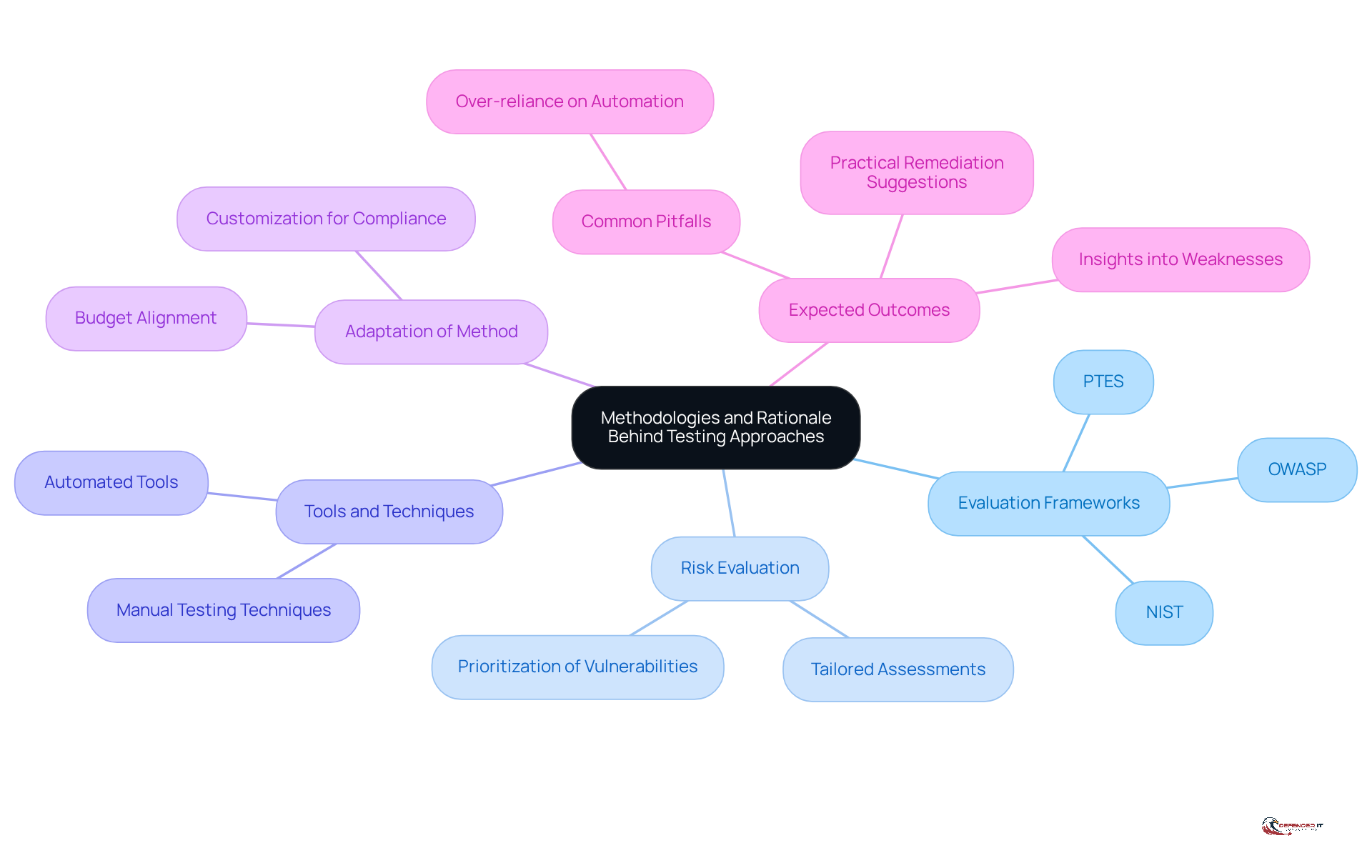
Explain Methodologies and Rationale Behind Testing Approaches
When presenting a penetration testing quote, it is crucial to articulate the methodologies and rationale behind the chosen approaches:
- Evaluation Frameworks: Established frameworks such as OWASP, NIST, or PTES should guide the assessment process. These frameworks ensure comprehensive coverage of potential vulnerabilities, aligning with industry best practices and regulatory requirements. For instance, NIST provides guidelines on information security assessments that help organizations effectively identify and address security weaknesses.
- Risk Evaluation: The evaluation method must assess risks tailored to the customer’s unique environment and threat landscape. This targeted evaluation helps individuals understand the reasoning behind the focus areas of the pen testing quote, ensuring that significant vulnerabilities are prioritized according to their potential impact. As Karan Patel, CEO of Redfox Cybersecurity, emphasizes, “The organizations that invest in regular, high-quality pentesting are the ones that identify weaknesses before adversaries do.”
- Tools and Techniques: Clearly outline the tools and techniques that will be utilized during the evaluation process. Employing advanced tools not only enhances the effectiveness of the evaluation but also fosters trust in the thoroughness of the assessment. For example, automated tools can scan thousands of assets simultaneously, allowing for efficient identification of vulnerabilities.
- Adaptation of Method: Highlight how the evaluation method will be tailored to meet the customer’s distinct needs, including specific compliance mandates or sector benchmarks. This customized approach ensures that the evaluation is relevant and effective in addressing the individual’s particular security challenges. Notably, smaller organizations can expect to spend approximately $5,000 for an external penetration assessment, underscoring the importance of aligning the evaluation scope with budgetary considerations.
- Expected Outcomes: Clarify what customers can anticipate gaining from the assessment process, including insights into weaknesses, their potential effects, and practical suggestions for remediation. This transparency helps customers recognize the value of the assessment and the importance of addressing identified weaknesses. Additionally, it is essential to note common pitfalls in penetration testing, such as over-reliance on automated tools, which can lead to missed vulnerabilities.
By effectively communicating these methodologies and rationales, cybersecurity firms can enhance client understanding and trust, ultimately leading to more successful engagements.
Conclusion
Crafting effective penetration testing quotes is crucial for cybersecurity firms and their clients. A well-structured quote clarifies the assessment’s scope and objectives while aligning the testing with the client’s specific needs, ultimately enhancing their security posture. By focusing on essential components such as clear deliverables, industry-specific risks, and transparent pricing, organizations can ensure that their cybersecurity investments yield significant returns while minimizing vulnerabilities.
This article outlines best practices for creating these quotes, including:
- Defining key components like the scope of work
- Objectives
- Methodologies
- Cost breakdowns
Customization based on client-specific needs, such as regulatory compliance and previous assessments, is vital for delivering relevant and effective services. Furthermore, fostering transparency in pricing and deliverables builds trust and encourages collaboration between cybersecurity firms and their clients.
In an increasingly complex threat landscape, the significance of thorough and tailored penetration testing cannot be overstated. Organizations are urged to adopt these best practices not only to protect their assets but also to foster a proactive approach to cybersecurity. By investing in quality assessments and engaging in open communication, businesses can better prepare themselves against potential breaches, ensuring a safer digital environment for all stakeholders involved.
Frequently Asked Questions
What are the essential components of a penetration testing quote?
The essential components include the scope of work, objectives, techniques, deliverables, schedule, and cost breakdown.
What should be included in the scope of work?
The scope of work should clearly outline the systems, applications, or networks to be tested and specify whether the test is internal, external, or both.
Why are objectives important in a penetration testing quote?
Objectives define the goals of the assessment, such as identifying vulnerabilities or ensuring compliance with regulations. Clear objectives guide the evaluation process and align with organizational needs.
What techniques can be specified in a penetration testing quote?
Techniques may include assessment methodologies like OWASP, NIST, or custom approaches tailored to the customer’s environment.
What deliverables should be listed in a penetration testing quote?
Expected deliverables include detailed reports, executive summaries, and remediation recommendations.
How should the schedule be presented in a penetration testing quote?
The schedule should provide an estimated timeline for the evaluation process, including preparation, execution, and reporting phases.
What is included in the cost breakdown of a penetration testing quote?
The cost breakdown should include a transparent outline of costs related to the evaluation, detailing any additional fees for follow-up services or consultations.
Why is clarity in a penetration testing quote important?
Clarity helps clients understand the investment needed for cybersecurity assessments and ensures that the assessments align with their safety goals and regulatory requirements, minimizing the risk of financial and reputational harm.
List of Sources
- Define Essential Components of Pen Testing Quotes
- The Essential Elements of a Successful Penetration Testing Plan – Shorsec Cyber Security (https://shorsec.io/blog/the-essential-elements-of-a-successful-penetration-testing-plan)
- Why Pen Testing is Essential for 2026 Cybersecurity Strategy (https://mainstream-tech.com/pen-testing-is-essential)
- Components of an Effective Penetration Testing RFP (https://netspi.com/blog/executive-blog/penetration-testing-as-a-service/effective-penetration-testing-rfp-components)
- 2026 GDPR Cybersecurity Requirements & Penetration Testing – Netragard (https://netragard.com/blog/gdpr-cybersecurity-requirements-and-penetration-testing)
- Penetration Testing Requirement: What U.S. Rules Mandate It in 2026? (https://halock.com/penetration-testing-requirement-what-u-s-rules-mandate-it-in-2026)
- Customize Quotes for Client-Specific Needs
- Penetration Testing Cost in 2026: $4K–$100K+ Guide (https://bsg.tech/blog/what-can-you-expect-to-pay-for-penetration-testing)
- Penetration Testing Requirement: What U.S. Rules Mandate It in 2026? (https://halock.com/penetration-testing-requirement-what-u-s-rules-mandate-it-in-2026)
- 5 Things to Look for in a Penetration Testing Company in 2026 – Netragard (https://netragard.com/blog/5-things-look-for-penetration-testing-company)
- Penetration Testing Quote: Complete Cost Breakdown (2026) (https://getastra.com/blog/penetration-testing/quote)
- 83 Penetration Testing Statistics: Key Facts and Figures (https://getastra.com/blog/penetration-testing/statistics)
- Ensure Transparency in Pricing and Deliverables
- Understanding Your Penetration Testing Quote – BreachLock (https://breachlock.com/resources/blog/understanding-your-penetration-testing-quote)
- The 2026 State of Pentesting: How Modern Teams Manage and Deliver Results (https://thehackernews.com/expert-insights/2026/01/the-2026-state-of-pentesting-how-modern.html)
- Penetration Testing Report: Key Information and Deliverables | Penetration Testing (https://penetration-testing.com/legal-and-documentation/penetration-testing-report-key-information-and-deliverables)
- 2026 Managed IT Services Cost: Transparent Price | Dataprise (https://dataprise.com/resources/blog/managed-it-services-cost-2026)
- Explain Methodologies and Rationale Behind Testing Approaches
- What is Penetration Testing? A Complete Guide to Pentesting in 2026 (https://redfoxsec.com/blog/what-is-penetration-testing-a-complete-guide-to-pentesting-in-2026)
- The 2026 State of Pentesting: How Modern Teams Manage and Deliver Results (https://thehackernews.com/expert-insights/2026/01/the-2026-state-of-pentesting-how-modern.html)
- Pentesting Frameworks & Methodologies and Why They’re Important – BreachLock (https://breachlock.com/resources/blog/pentesting-frameworks-methodologies-and-why-they-are-important)
- Hybrid Penetration Testing: What’s New in 2026 (https://brightdefense.com/resources/hybrid-penetration-testing)
- The Complete Guide to External Penetration Testing (2026) – Triaxiom Security (https://triaxiomsecurity.com/blog/the-complete-guide-to-external-penetration-testing-2026)